@MidnightNetwork #night $NIGHT
I've seen in the rapidly evolving blockchain industry, many projects compete for attention through short-term narratives, token speculation, or market hype. Yet the long-term success of a blockchain ecosystem is rarely determined by narrative cycles alone. Instead, it is shaped by deeper structural elements such as infrastructure decentralization, developer accessibility, resource distribution models, and ecosystem integration.
The Mōhalu phase of Midnight Network, expected around mid-2026, represents an important transition in this regard. Rather than focusing solely on application launches, this stage emphasizes community node participation, staking rewards, and the activation of the DUST capacity exchange. These components collectively form the foundation for a more decentralized and builder-friendly privacy infrastructure.
Understanding the significance of Mōhalu requires examining how Midnight approaches distribution architecture, metadata propagation, and developer-oriented resource models.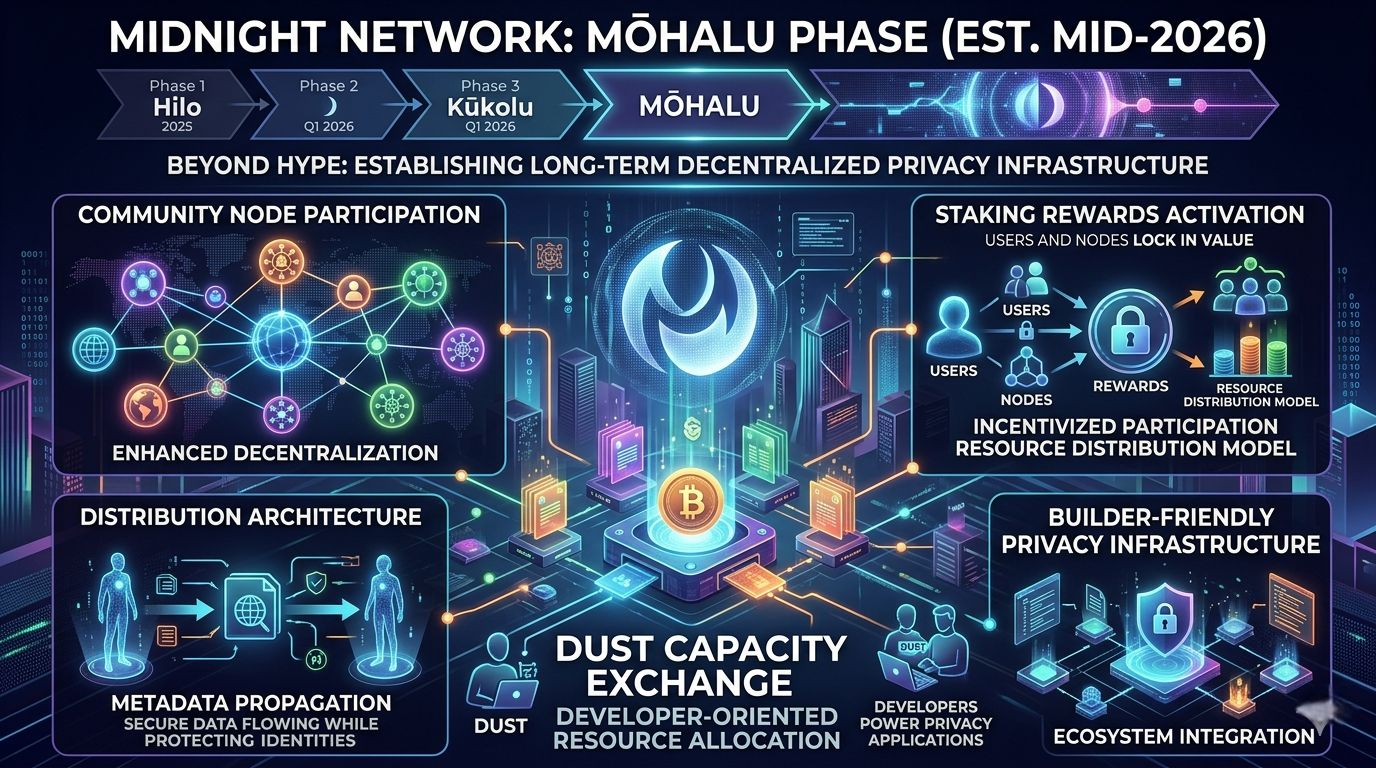
From Federated Infrastructure to Community Nodes
In its early operational stages, Midnight relies on a controlled validator environment to ensure network stability while developers experiment with privacy-preserving smart contracts. This approach is common in emerging blockchain networks because it allows the protocol to mature before exposing the infrastructure to broader participation.
The Mōhalu phase begins the transition toward community-operated nodes. Independent infrastructure providers and validators will be able to participate in block production, contributing to network security and transaction verification.
From a technical perspective, this transition serves several important functions.
First, validator diversity increases the network’s resilience against censorship and centralized failure points. When more independent operators participate in consensus, the network becomes harder to control or disrupt.
Second, a broader validator ecosystem creates a distributed infrastructure layer capable of supporting privacy-focused applications at scale. Builders deploying decentralized applications need reliable node infrastructure that is geographically and organizationally distributed.
By expanding node participation, Midnight aims to establish the kind of decentralized execution environment required for long-term application deployment rather than experimental development.
The Dual-Resource Economic Architecture
One of the most distinctive aspects of Midnight’s design is its two-layer resource model, centered around the tokens NIGHT and DUST.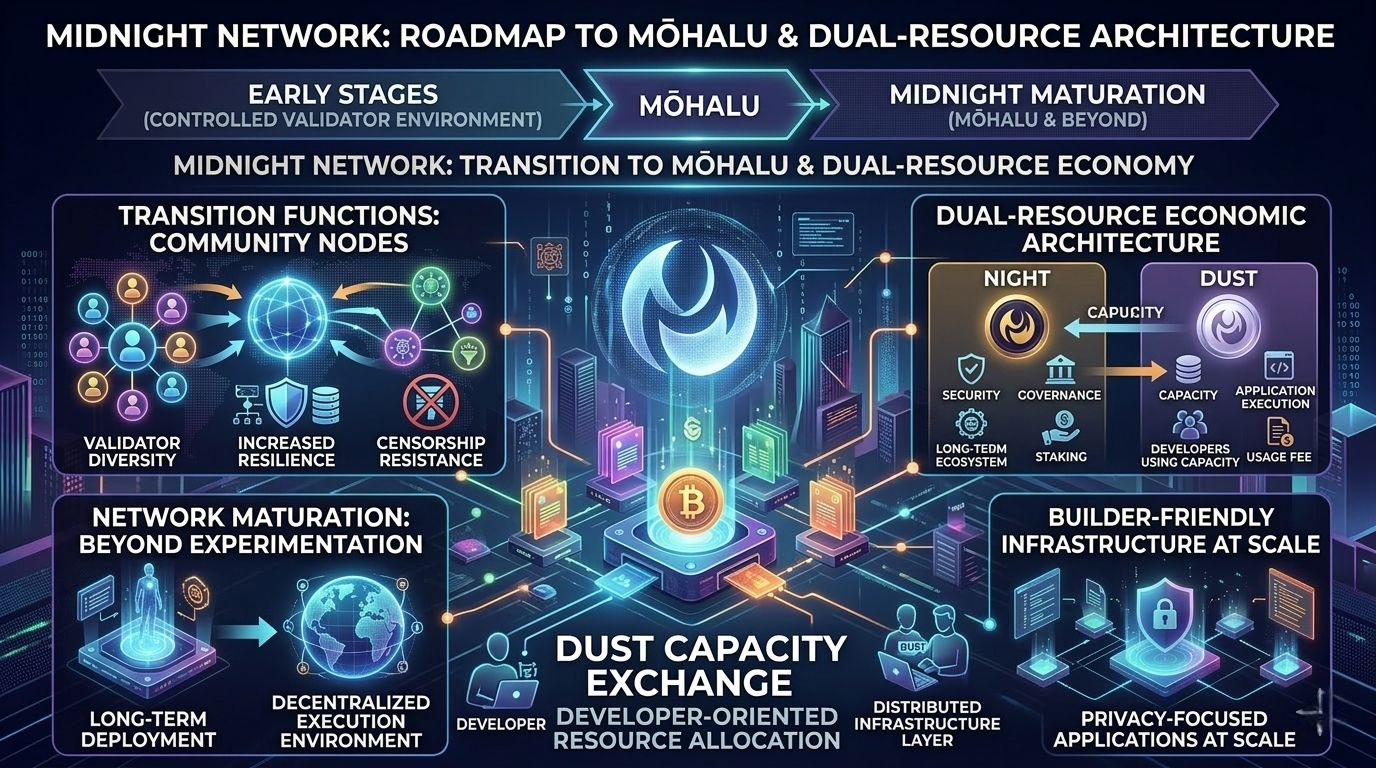
The NIGHT token functions as the security and governance asset of the network. Participants who hold or stake NIGHT help secure the protocol and may receive rewards for contributing to consensus.
However, transaction execution within the network does not rely directly on NIGHT. Instead, Midnight introduces DUST, a shielded network resource used to execute transactions and smart contract operations.
This structure separates two different economic layers:
• Capital layer: represented by NIGHT
• Execution layer: represented by DUST
DUST is generated automatically by holding NIGHT, effectively creating a renewable transaction capacity rather than a purely speculative gas token. When transactions occur, DUST is consumed as a computational resource.
This architecture offers several advantages for developers and application operators.
First, it allows applications to maintain predictable operational costs. Instead of relying on fluctuating gas markets, developers can generate transaction capacity through NIGHT holdings.
Second, the model encourages long-term infrastructure participation, since holding the network asset provides continuous access to execution resources.
In practical terms, this transforms transaction fees into something closer to programmable infrastructure capacity, aligning the network’s economic model with long-term ecosystem growth.
Metadata Propagation and Privacy-Preserving Verification
Privacy-focused blockchains face a fundamental challenge: maintaining confidentiality while still enabling decentralized verification.
Midnight approaches this challenge using zero-knowledge cryptographic systems, which allow a transaction to be validated without revealing the underlying data.
Instead of exposing sensitive information publicly, the network verifies cryptographic proofs of correctness. This allows nodes to confirm that a transaction follows the protocol rules without accessing private inputs.
The deeper architectural significance lies in how metadata is propagated through the network.
Rather than broadcasting full transaction data across all nodes, Midnight separates:
• public consensus metadata, which ensures network security
• shielded transaction data, which remains private
This layered approach enables selective disclosure, where only the necessary information becomes visible for verification while sensitive details remain confidential.
For sectors such as financial services, identity infrastructure, and healthcare data systems, this model offers a potential path toward blockchain adoption without sacrificing data privacy or regulatory compliance.
The DUST Capacity Exchange
Another major component of the Mōhalu phase is the introduction of the DUST Capacity Exchange.
Traditional blockchains rely on gas markets where users compete to pay transaction fees. These systems can lead to unpredictable costs during periods of network congestion.
Midnight’s approach treats transaction execution as a resource allocation problem rather than a bidding market.
Through the DUST exchange, participants can allocate or manage their available transaction capacity derived from NIGHT holdings. This creates a system where execution resources can be distributed across the ecosystem more efficiently.
For developers, the implications are significant.
Applications may choose to cover transaction costs for their users, enabling frictionless onboarding. Infrastructure providers could manage transaction capacity for multiple services, while enterprises deploying private applications may maintain their own execution resources.
In effect, the network introduces a programmable resource economy, which may prove more predictable for large-scale deployments.
Ecosystem Integration and Cross-Chain Potential
Another strategic element of Midnight’s design is its positioning as a privacy infrastructure layer rather than a standalone blockchain competing for liquidity.
Many modern decentralized applications require both transparency and confidentiality. Public blockchains provide verifiable settlement, while privacy layers protect sensitive data.
Midnight aims to bridge these two needs by enabling applications that combine public chain transparency with private computation environments.

If successfully implemented, this model could allow other blockchain ecosystems to integrate Midnight’s privacy functionality as an additional layer rather than migrating entirely to a new network.
For developers, this kind of interoperability significantly expands the potential addressable ecosystem.
The Technical Moat Behind Midnight
While many blockchain projects emphasize single innovations, Midnight’s architecture combines several design elements that together form a stronger competitive moat.
These include:
• Programmable privacy through zero-knowledge smart contracts
• A dual-resource economic model separating capital and execution
• Renewable transaction capacity via DUST generation
• Infrastructure decentralization through community nodes
• Cross-chain compatibility for privacy-enabled applications
Individually, these innovations are notable. Collectively, they create an environment where privacy becomes an integrated infrastructure feature rather than an optional add-on.
