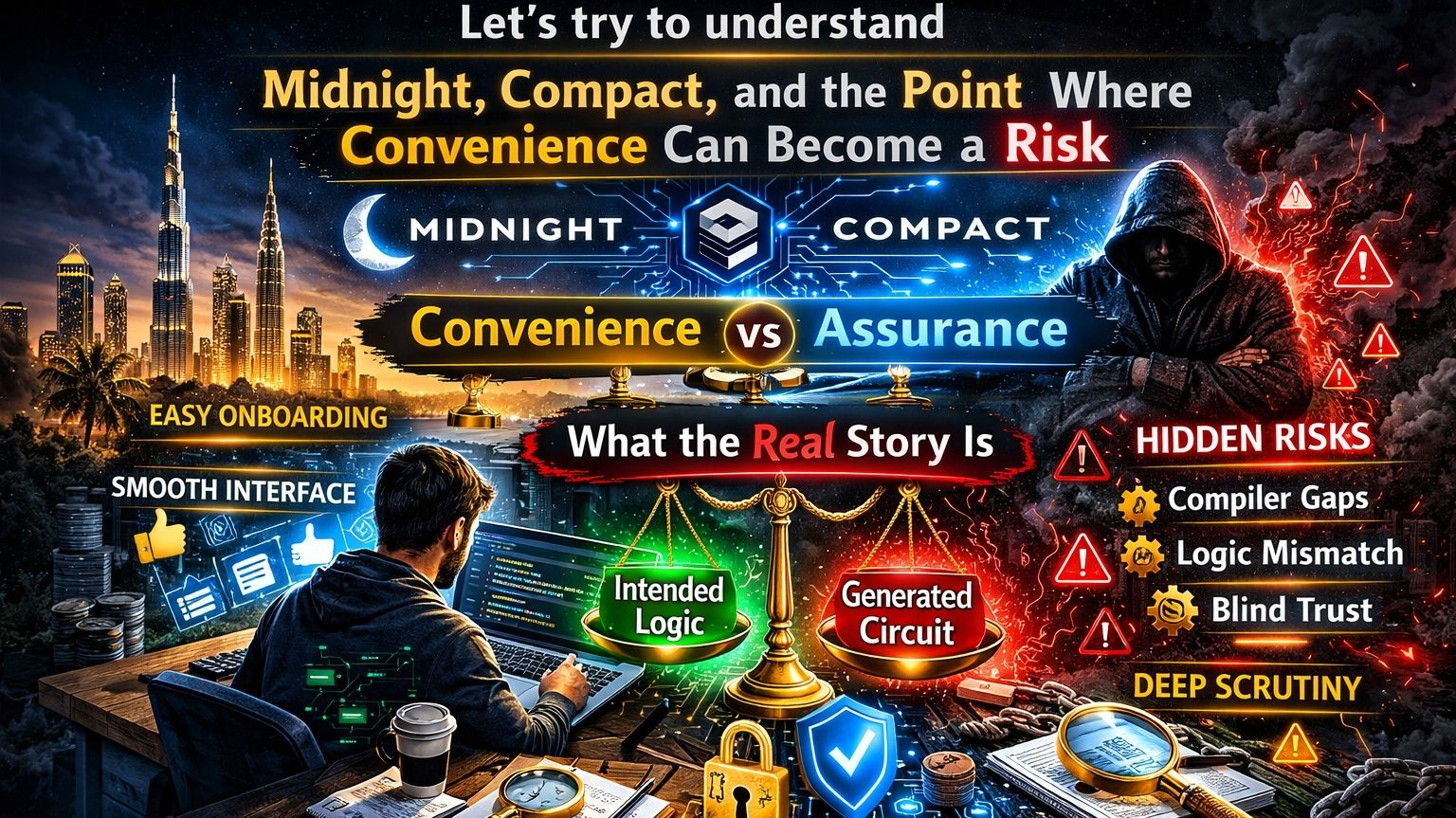
Let’s try to understand what the real story is.Today, I was sitting in my room in Dubai, casually scrolling through my phone and watching random stuff without thinking too deeply about anything. Then a message popped up from a friend of mine. He said, “Come on, brother, let’s go outside for a bit.” When I opened the door, he was already standing there waiting for me. We went out together, and somewhere in the middle of that ordinary moment, my mind drifted back to something I had been thinking about for a while: the things that look easiest on the surface are not always the things we should trust the fastest. And honestly, that is exactly the feeling I get when I hear a platform describe itself as a developer-friendly zero-knowledge platform.
Not because the idea sounds bad, but because it sounds a little too good. In crypto, especially in areas as complex as zero-knowledge technology, it always sounds attractive when a project says it has made things easier, improved onboarding, cleaned up the tooling, and created a smoother path for normal developers. And that is usually the moment when I stop and think more carefully.
Because the truth is, there is logic behind what Midnight is trying to do. If zero-knowledge technology is ever going to move beyond a small circle of cryptography experts, then the developer experience has to improve. It is not realistic to expect every software developer to dive deep into cryptography. Not everyone can be both a software engineer and a mathematical systems expert. That is why something like Compact makes sense. If the goal is wider adoption, the tools must become easier to use. If the goal is to bring private computation to more people, the friction must be reduced. And if the goal is to attract mainstream developers, then the language, tooling, and workflow must feel approachable enough for them to enter without fear.
From that angle, it looks like a smart move. Also, taking it in an open-source direction under the Linux Foundation sends a positive signal. At the very least, it suggests that the project is not just a closed black box. It becomes something people can inspect, test, question, and debate. In crypto, that already matters a lot.
But this is where the real question begins. Making something easier to use is not the same as making it truly trustworthy. And I think this is the point many people ignore too quickly. As zero-knowledge development becomes more accessible, a new problem appears. More people will build systems they do not fully understand. More teams will deploy logic they can read on the surface, but cannot fully reason about at the cryptographic level. More organizations will assume that the compiler, circuit generation, and proof layer are enforcing exactly what they intended. And to me, that is the real risk.
In normal software engineering, errors are painful, but they are often visible. Code breaks, a feature behaves badly, logs appear, a bug can be reproduced, and a patch is released. It is unpleasant, but usually manageable. Cryptographic systems are not that forgiving. If there is a semantic mismatch when developer-friendly code is translated into a cryptographic circuit, if an abstraction hides something important, or if the generated logic is slightly different from what the developer intended, the problem may not be obvious right away.
The code may compile. Proofs may be generated. The system may look valid. Deployment may happen with confidence. And then later, people discover that the system was technically working, but it was doing the wrong thing. That is not a normal bug. That is the kind of failure that looks legitimate at first, and that is exactly why I cannot feel fully comfortable with the idea of simply making ZK “easy.”
I am not against better usability. I do not believe difficulty is a virtue. Bad tooling does not make a project more secure. Complex interfaces are not proof of trustworthiness. And confusing systems are definitely not noble just because they are hard to use. If Midnight is working on accessibility, that is good for the space, because the truth is that better tools are needed.
But there is another truth too: convenience often creates confidence before it creates understanding. And in cryptographic environments, that can be dangerous. When the abstraction is clean, the syntax is familiar, and the developer workflow feels smooth, people quickly start assuming that the underlying system must also be simple, predictable, and trustworthy. But in cryptography, the real danger often lives inside the hidden layer that abstraction covers up.
So for me, the main question is not whether Midnight can attract developers. It probably can. The main question is not even whether Compact can make ZK development easier. It probably can do that too. The real question is something deeper. When most developers interact with zero-knowledge systems through a simplified interface, will they actually be able to verify what is happening underneath? Will they know whether the compiler translated their intent into the correct cryptographic form? Will teams be able to detect mismatches that are invisible on the surface but important for security? And if something fails, will organizations be able to explain that failure clearly, or will they only say, “The system seemed to be working?”
To me, that is the real test for Compact and Midnight. Because if the whole model finally comes down to this — just trust the toolchain — then the basic trust problem has not disappeared. It has only changed shape. Before, people had to trust raw cryptographic construction. Now, they may simply trust the platform that hides the complexity behind a cleaner interface.
Yes, that can still be progress, but only if usability is matched by serious assurance. Because adoption can come quickly. Dependability does not. Dependability requires the kind of work that gets less applause: deep audits, compiler-level scrutiny, circuit verification, hostile edge-case testing, formal reasoning, and the slow kind of trust that grows from repeated technical confidence, not from marketing language.
So the real test is not just TypeScript-style friendliness. The real test is whether the cryptographic enforcement underneath that friendliness is understandable, verifiable, and trustworthy. That is why, when I look at Compact, I do not think the main headline is that Midnight is making zero-knowledge mainstream. Maybe it is. But the more important headline, for me, is this: can Midnight make zero-knowledge mainstream without making people too confident in systems they only partly understand?
Because easy tools are powerful. But in cryptography, easy tools with hidden failure modes are not just convenient. They can become the starting point of very expensive mistakes.