Midnight wasn’t what I expected at first.
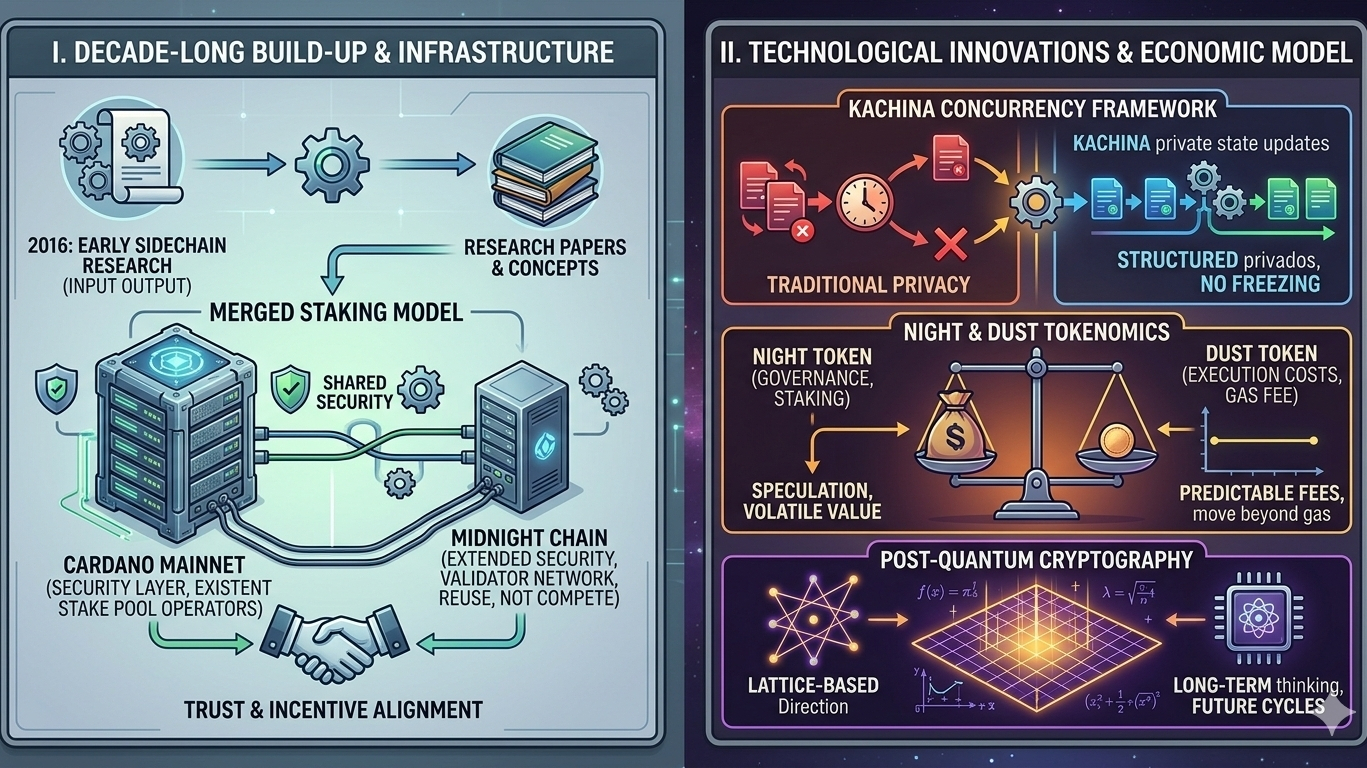
At a glance, it looks like just another privacy-focused chain. Another project trying to deal with data exposure on public ledgers. But the more I dug into it—especially tracing things back to Input Output’s sidechain research from 2016—it started to feel less like a new direction and more like the result of a long build-up.
Because the ideas behind Midnight aren’t new. They’ve been in progress for years.
That early sidechain work introduced a simple but powerful concept: you don’t scale by forcing everything into one chain—you scale by extending it. And that idea clearly shaped how Midnight is designed today.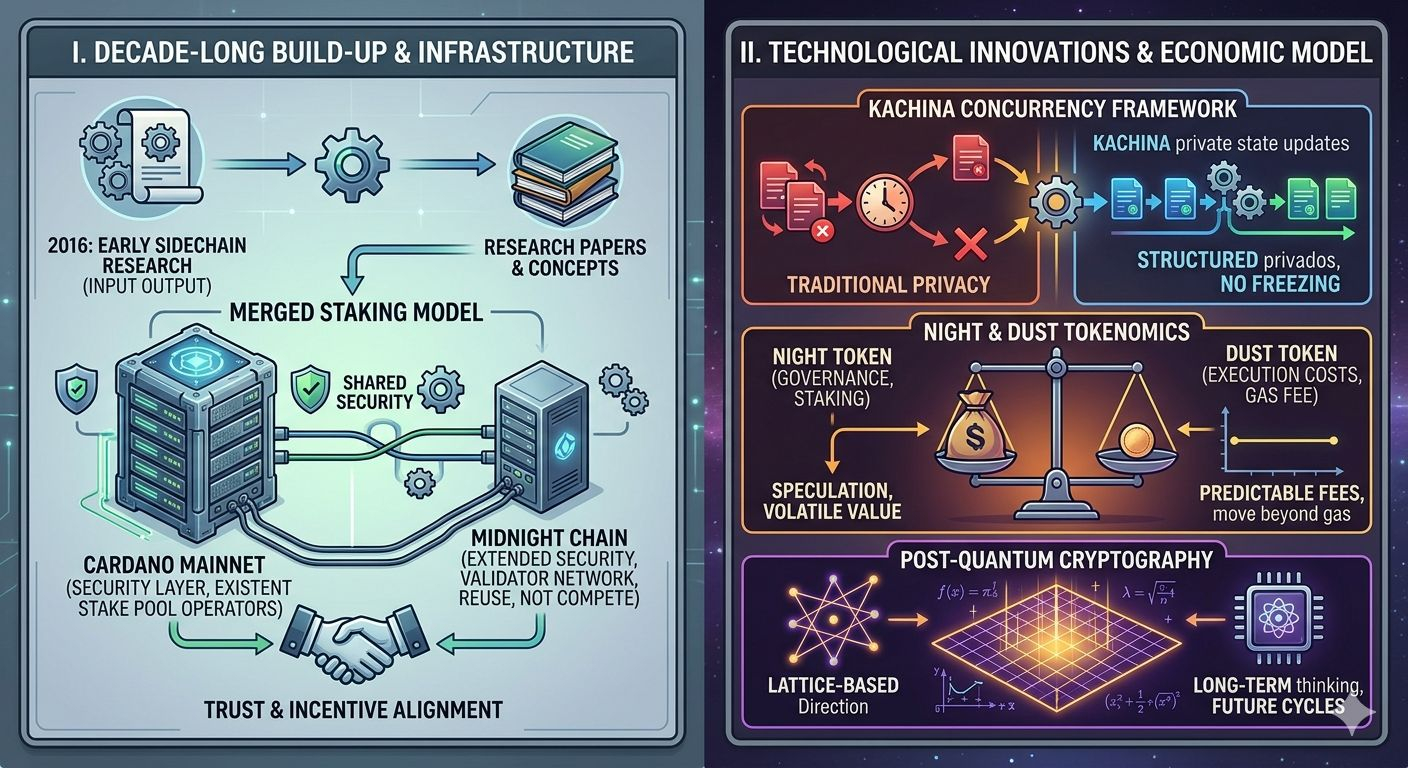
What really made things click for me was how this connects to merged staking.
Instead of building a validator network from zero, Midnight leans on Cardano’s existing stake pool operators. Same base infrastructure, same security layer—just extended into a new system. It doesn’t compete for security like most chains do. It reuses it. And honestly, that solves a problem many new projects quietly ignore.
Then comes Kachina—and this is where it gets interesting.
Concurrency has always been a weak point in privacy systems. Hiding transactions is one thing, but handling multiple users interacting with private states at the same time? That’s where things usually break—proofs conflict, execution slows down, systems stall.
Kachina doesn’t eliminate that challenge, but it organizes it.
From what I understood through the Midnight Summit discussions, it introduces a structured way to handle private state updates without freezing the network. It accepts trade-offs instead of pretending they don’t exist—and that’s a very real-world approach.
That’s when a pattern started to emerge for me.
Midnight isn’t chasing perfection—it’s working within constraints.
And that changes how you think about privacy. It’s not about hiding everything. It’s about controlling what gets revealed, when, and for what reason.
That’s how real systems operate anyway—whether it’s finance, identity, or everyday interactions. You don’t expose everything, just what’s necessary. Midnight seems to be built around that idea, assuming users will act strategically. That’s a subtle but powerful design choice.
The economic model adds another layer to this.
The split between NIGHT and DUST might look simple, but it solves a deeper issue. Most networks tie execution costs to a speculative token, which makes fees unpredictable—and sometimes unusable.
Midnight separates that.
DUST is generated, not traded. Which means execution costs become more stable, more predictable. Something you can actually plan around. When I first came across this idea around AFT ’24, it felt like one of the few serious attempts to move beyond the traditional gas model—not tweak it, but rethink it entirely.
And then there’s the part that most people overlook: post-quantum direction.
The mention of lattice-based cryptography stood out to me. Not because it’s immediately necessary, but because it shows long-term thinking. This isn’t just about the current market cycle—it’s about building something that can survive future ones.
That’s rare.
Stepping back, Midnight doesn’t feel like a product chasing hype. It feels like years of research finally aligning at the right time.
Sidechains.
Concurrency.
Economic design.
Privacy as a strategy.
Everything connects.
And that’s probably the biggest shift in perspective for me—
Midnight isn’t trying to reinvent everything.
It’s trying to fix what never really worked in the first place.