The thing that made me reevaluate the situation was the understanding that the most difficult issue of privacy that Midnight faces is not the proven transaction.
It is the little time that the evidence is anywhere.
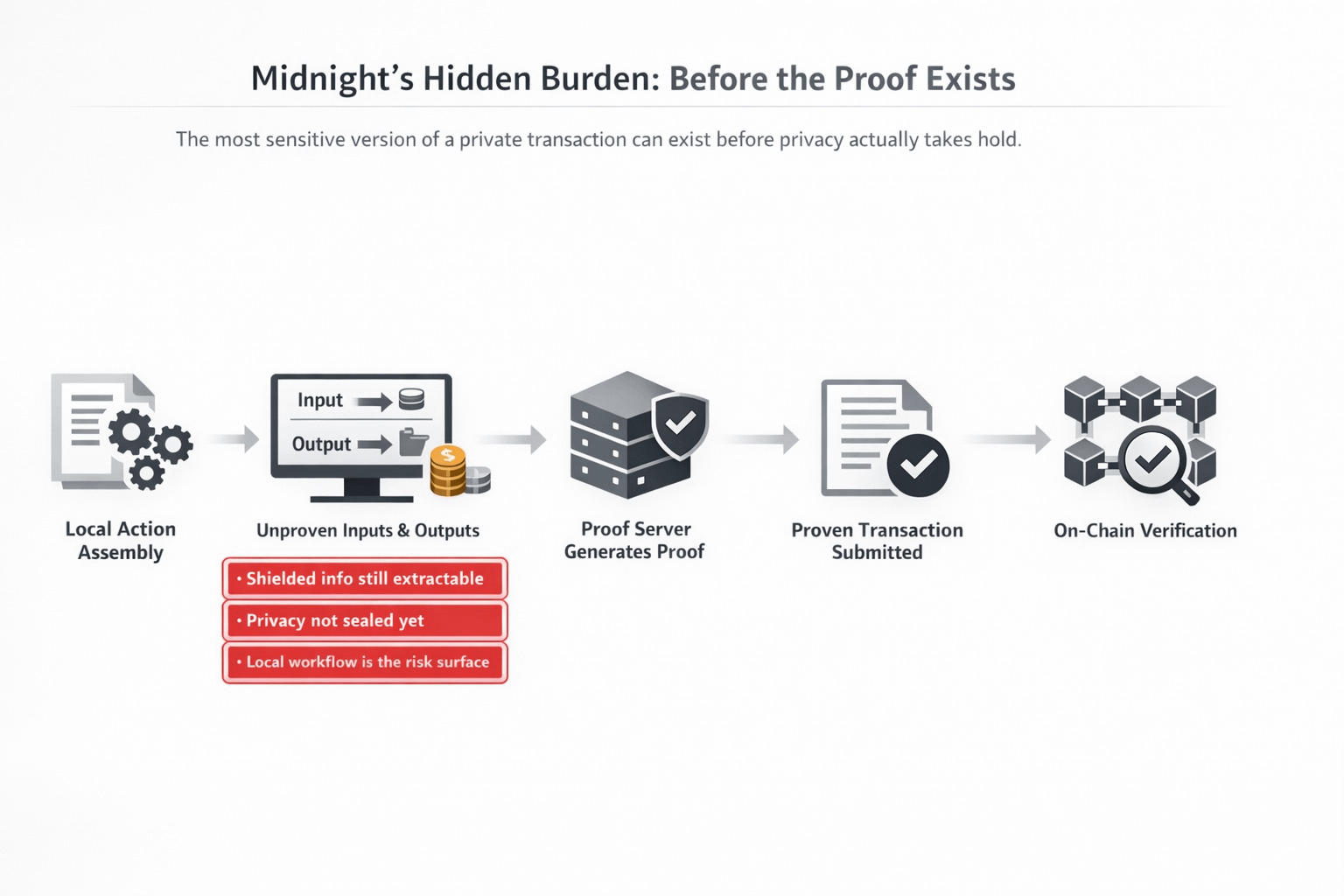
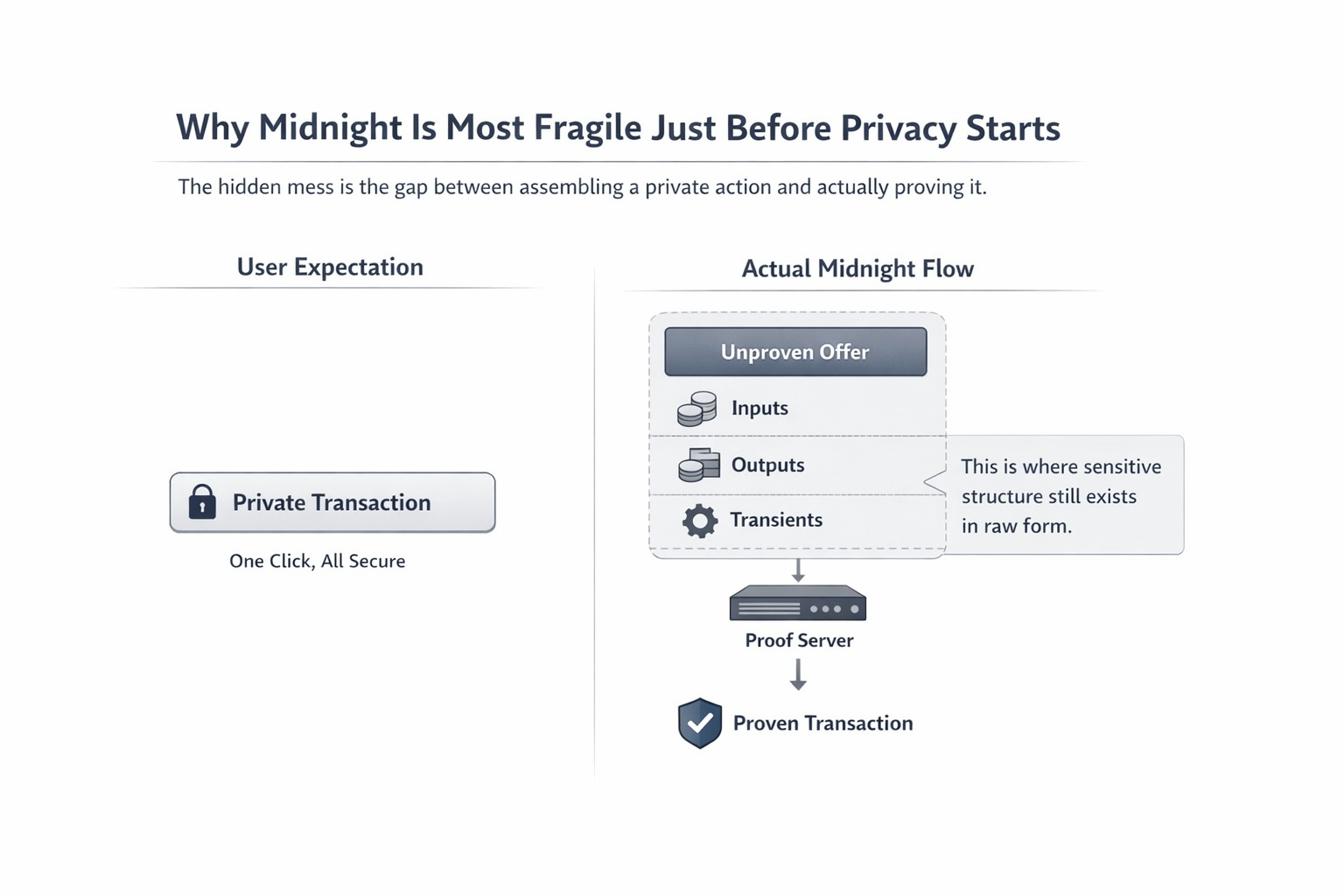
It was at that point that the project ceased to become a clean story about privacy to me and began to look like a far more serious workflow problem. The transaction model of midnight is based on proof-based verification and transactions frequently used by real activity incorporate a cryptographic proof rather than the signature-based public flow as usual. However, prior to such a given proof being attached the system must still assemble the action in an unproven state.
That is the dirty part I believe people miss.
Midnight has an overt proof-stage model. Components of transactions start as UnprovenX, may be fully proven X on the proof server, and may also be converted into a ProofErasedX form to be tested. The warning is even more sharp in the Zswing layer: even an UnprovenOffer has not been proven yet, and at this point all the shielded information in the offer can still be recovered. It implies that the privacy tale is not created at the time of input. It gets born when the secret making stage has really concluded.
This becomes uncomfortable at the visible workflow.
I build the action locally. Inputs are selected. Outputs are shaped. Deltas are known. The transients are even occasionally generated and burned during the same transaction. Then that object then exists there as an awaited transaction or awaited offer when the proof server is yet to do something. Midnight tells the truth about that building. Then the node subsequently checks structure in the pool, and the embedded proof in the case of a block. Until then there is no such evidence, the nimble reason is not yet residing within the seclusion assurance that persons tend to envision when the word Midnight is mentioned.
That altered my perception of the entire project.
Confidential execution is not the only hard problem. It is ensuring that the pre-proof messy stage is not silently transformed to be the weakest part of the system. What is more important about midnight is the angle that it is not merely inquiring whether a personal transacting can confirm properly on-chain. It is also putting the question whether the surrounding which constructs that exchange prior to the generation of proof is disciplined enough to warrant the privacy result in the subsequent future. The proof server is precisely there to make that conversion of unproven to proven step.
The native evidence to the project is as you see in the object model.
It is not a Midnight transaction that is simply an opaque blob. The ledger flow identifies guaranteed and fallible segments, Zswap receipts and payments, and even transients that are created and burnt between the same transaction. On the Zswap API level, an UnprovenOffer has a well-defined set of inputs, outputs, transients, and balance deltas before proving. This is why I can feel this burden. The system is strong enough to construct complex personal actions, although, what that implies is that the most exposing version of the action can momentarily exist prior to the evidence cementing the action into the form that it is supposed to be perceived in by the network.
That was the turning point to me.
I terminated Midnight because of the lazy marketing sense of privacy by default. I began reading it like it was privacy following discipline. The distinction matters. When constructors, wallets, or local tooling lose track on the pre-proof path, then even the ultimate proof can be mathematically accurate yet the most critical workflow point has already occurred somewhere out of view by the user. This is an essential aspect of midnight since it presents a more difficult question than most privacy initiatives do: where is the boundary between the state of privacy and the state of being displayed to the point that it counts?
Here is where it begins to sound more to me that it is not a generic token paragraph but rather precise design that is being employed by $NIGHT.
NIGHT is positioned above DUST generation and this is what drives execution. However the execution does not begin to have any real meaning until the system is in a position to transfer the crude untrying form of a transaction into the established form accepted by the ledger. To this load the token design is not above. It is placed in the undercarriage of a workflow where capacity, proving, and final submission is only a concern when the sensitive pre-proof phase is approached safely enough that the privacy guarantee has still remained intact when DUST is actually used up.
The question that I keep on returning to the pressure-test is straightforward.
Is it possible that @MidnightNetwork can bring the pre-proof phase to a level where users are not made aware of it, but not so forgettable as to cause harm to builders? Is it possible to make local tooling, wallets, and proving infrastructure good enough that the most sensitive form of a transaction, will never become the weakest point of operation in the entire stack? Since in case the answer is no, the first actual price of privacy will never be reflected in the evidence. It will appear before the evidence, on the one hand when the hidden information is not yet as covered as the final story makes it out.
What stayed with me is this.
On Midnight, the privacy is not created when a user is clicking.
It is conceived when the untested version has finally ceased to exist.
$NIGHT #night
