What made me change my mind was that the privacy model of Midnight is missing one thing that should be made public.
Not the identity. Not the secret. Not the full action.
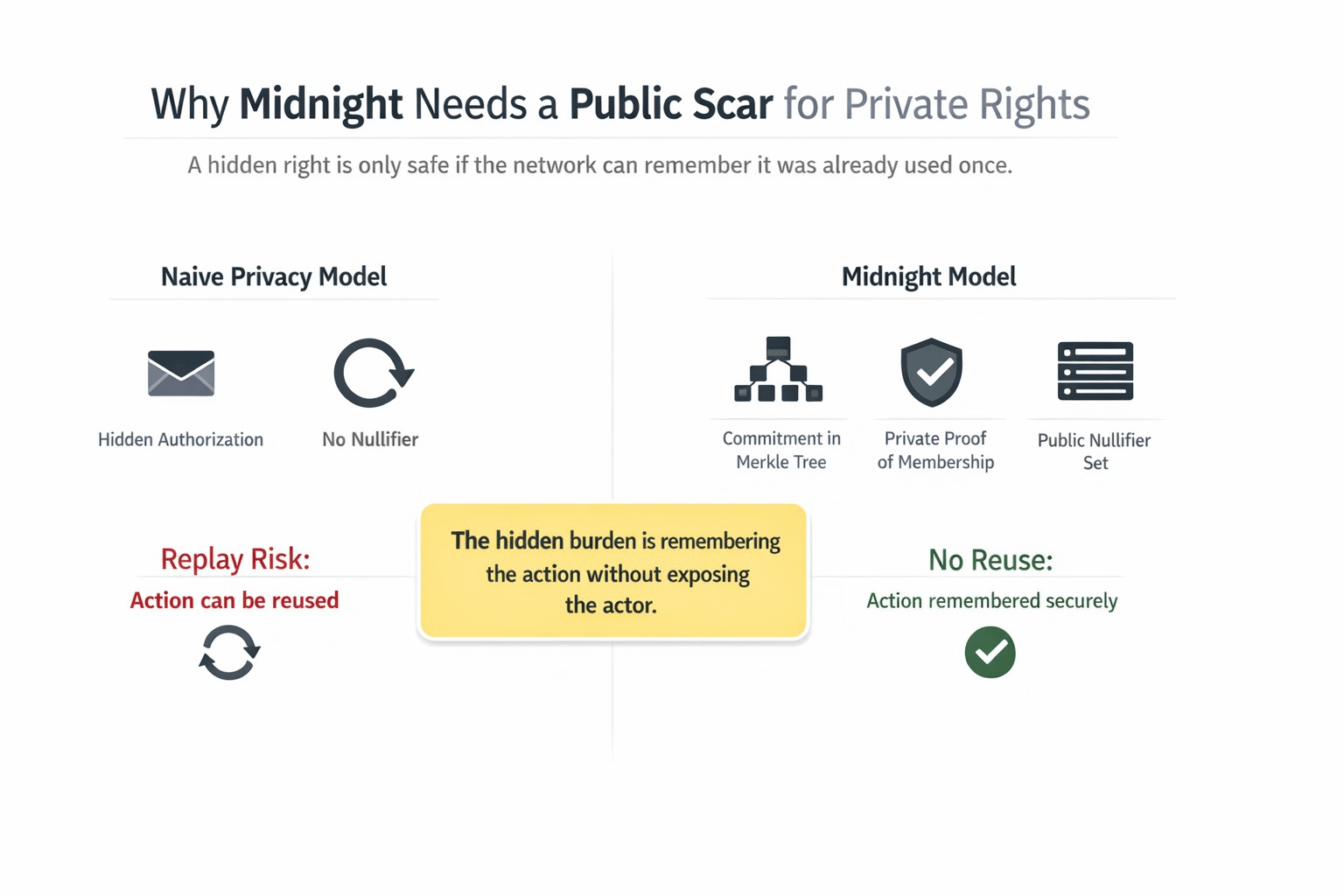
Nothing but the fact that the act is already once accomplished. It was also where I felt that the project ceased being a delightful privacy tale to me and became considerably more serious. The patterns of privacy in midnight constructs on the basis of commitments, Merkle proofs, and nullifiers. The commitment protects the right to act secretly. It is the nullifier that forever sets the mark of the right already used.
This is the invisible baggage that I do not hear discussed by enough people.
Many people read about the idea of private authorization and have a vision of a clean world where all significant things remain hidden. It is even harder than midnight. Privacy is replay, in case a hidden token, credential, or right may be reused. The system must also keep the use in memory without displaying what hidden item was utilized. Midnight does that by maintaining commitments in a Merkle tree and nullifiers in a Set, and then by making the contract show membership privately and also by stating that the associated nullifier has not yet been presented.
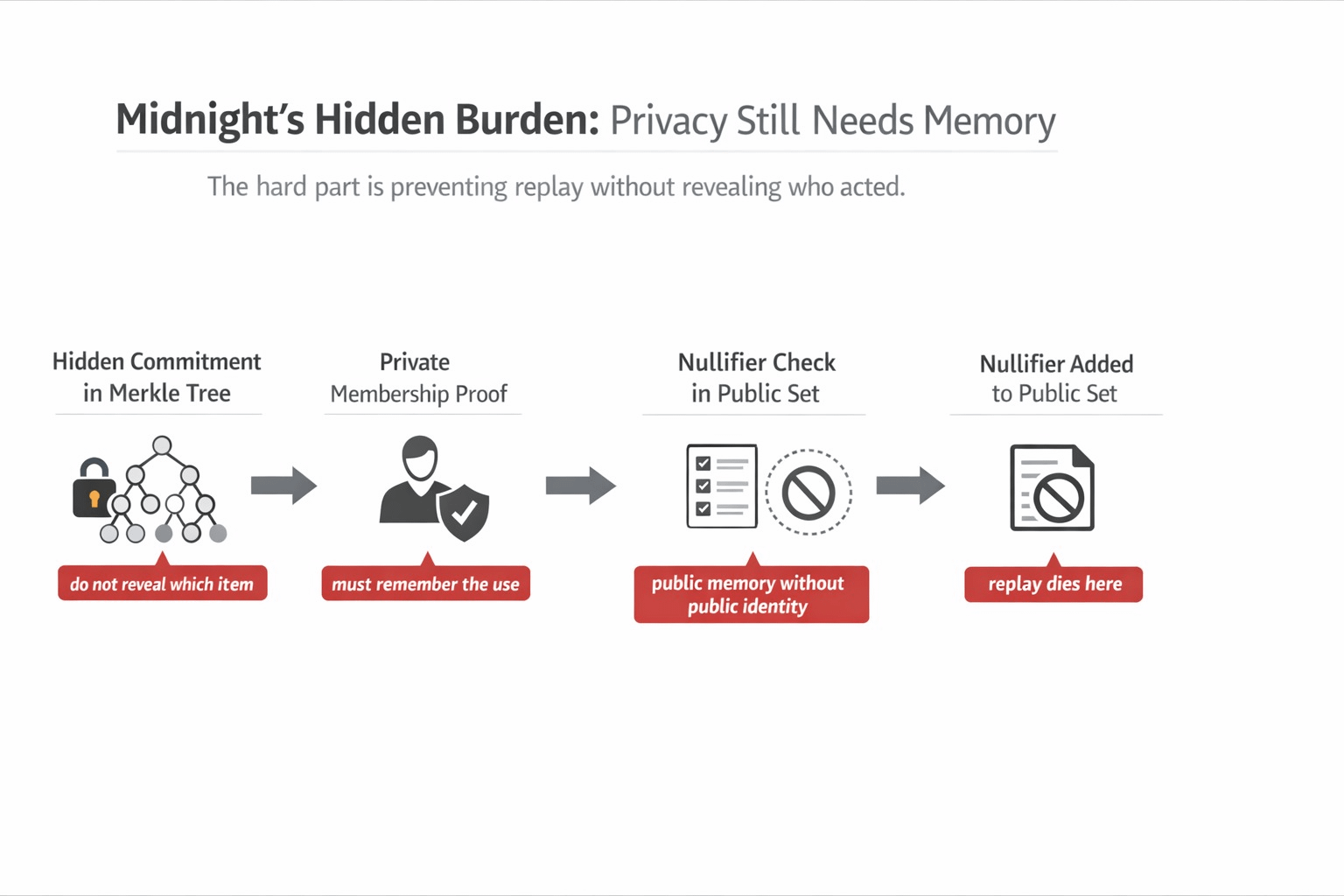
This is the point at which I eventually made the visible workflow.
A user has something to do, and only one time. Maybe redeem a right. Perhaps a personal authorization. Perhaps eat a guarded paper. The app demonstrates that an item in the tree, which is committed, is a part of the authorized set, but does not show what the item is. Such is the graceful side. However, this task is not the most difficult at all: right after it the contract must also introduce a disclosed nullifier into public state in such way that the same hidden item would never be used again. Midnight even makes this the major pattern underlining Zerocash and Zswap. It means that the system is not just concealing the user. It is also creating a one-directional scar on the general consciousness that indicates in some way, that something official was eaten here, and cannot be un-eaten.
It is the reason Midnight began to be more significant to me in this very angle.
The project is more important as I am no longer asking the question whether the project can hide data, but asking the question whether the project can hide data without losing memory. That is a much uglier problem. An exclusive system forgetting excessively is an entitlement to repetition and duplication. A personalized system that has remembered excessively begins to recreate the same face of surveillance upon which it was designed to evade. The nullifier and commitment of Midnight is in the midst of that tension. It allows the contract to recall use without disclosing to it what was the concealed object that formed that memory.
The project-native evidence is acute to the extent that it transformed my way of thinking of privacy design.
Midnight is not merely providing hand builders with an imprecise privacy toolkit. It provides them with very narrow primitives to this very problem. PersistentCommit and persistentHash can be used to create commitments. The proof of membership is possible by using path objects and root checks based on Merkle trees. Then one-time use is implemented using nullifiers which are publicly stored in a Set. Midnight also cautions that commitments and nullifiers cannot have the same domain separators and that creation of a nullifier might necessitate secret knowledge so that even the one who initially authorizes the secret material cannot know that the secret material will be used only afterwards. That is not generic writing on privacy. That is an exact response to the replay issue.
My turning point was not complicated.
I stopped reading Midnight because privacy was all about concealing all the significant things. I began to read it because privacy is a situation where I can choose what the system should never forget. That is a far more difficult requirement. The hidden item stays hidden. The evidence of membership remains confidential. The actual use must become irreversible. As soon as I noticed that, the nullifier ceased to look like the technical issue. It began resembling the actual cost of credible privacy. Midnight is more grave as it acknowledges that the rights of privacy are deadly unless the network will be able to recall publicly that the system has already been used.
And that is where I had begun to feel the clicking of $NIGHT more sharply in the exact design.
Midnight makes partings rather than dissolutions. NIGHT the naked indigenous token. Possession of it produces DUST, which is the resistant, non-transferable commodity applied to fund transaction charges and execute smart contracts. The identical separation instinct manifests themselves here as well. There is ownership or authorization that is hidden in one of the systems. An additional piece draws the smallest public record that is required to prevent reproduction. Then DUST executes the transaction which executes both pieces. In this perspective, it means that $N$NIGHT relevant; because it is located at the upstream relative to a network that is not attempting to turn privacy into a frictionless experience by posing a delusion that memory is not required. It is financing a paradigm in which privacy is only possible because the system remembers the thing it simply must remember.
The question that I continue to struggle with is the pressure-test question of whether Midnight can actually assist builders to maintain this balance when reality applications become messy.
Is the nullifier aggressiveness of teams sufficient to kill replay without leaking additional structure than they require to? Are they able to retain the scar on the forehead of the masses whilst at the same time rendering one-time personal rights credible? When apps become more controlled, more composable, or more user-facing will they maintain that discipline or begin to introduce additional state to make support and product logic less challenging? This issue is still alive within the design making midnight more compelling to me. The slogan of private transactions cannot fully address it.
What stayed with me is this.
The privacy is no more difficult in Midnight, where the secret is concealed.
Most difficult is where the system must recall the use, but not the user.
$NIGHT #night @MidnightNetwork
