The part people miss
I think a lot of crypto still treats verification like a receipt you check after the fact. Something happened, then later someone proves it. Sign Protocol matters to me because it pushes the opposite idea: verification can be the thing that starts the next step. Not just proof of a claim, but a trigger for rights, access, payments, approvals, and distributions. That’s a more interesting design space, and honestly a more useful one off-chain too. Sign’s own docs now frame the protocol as the evidence layer inside a broader S.I.G.N. stack for money, identity, and capital systems, which tells you the team is aiming far beyond a generic attestation tool.
I noticed that shift again today while going through the refreshed docs. The tone is different from the older “attest anything” pitch. It’s more operational now. Less about proving a fact in isolation, more about recording who approved what, under which authority, under which ruleset, and what action should be allowed next. That sounds dry on paper. It isn’t. That’s basically the difference between a nice credential demo and infrastructure that can survive audits, disputes, or messy real-world coordination.
What the protocol actually is for
At the protocol level, Sign organizes data around schemas and attestations. Schemas define the structure of a claim. Attestations are signed records that conform to that structure. The clever part is not just that these records can live on-chain, off-chain, or in hybrid form. It’s that SignScan indexes and queries them across supported environments through REST, GraphQL, and SDK access, which makes them usable by applications instead of trapped as isolated blockchain artifacts. That’s where verification starts becoming workflow infrastructure rather than static proof.
So the practical move is simple: once eligibility, compliance, ownership, or approval is attested in a standard format, another system can consume that fact and act on it. A contract can gate a function call. A distribution engine can release funds. An auditor can replay the history. A registry can accept or reject an update. Sign’s docs are very explicit here. The evidence layer is supposed to answer who approved what, when it happened, what rule version applied, and what settlement reference proves execution. That’s not decorative metadata. That’s executable context. 
Where the workflow angle becomes real
This is why TokenTable fits so naturally beside Sign Protocol. TokenTable handles allocation logic, vesting schedules, claims, clawbacks, and distribution execution, while Sign Protocol handles the evidence and eligibility layer underneath it. In plain terms, verification can decide who gets paid, when they can claim, whether a revocation applies, and whether the final distribution can be audited later. Sign says TokenTable distributed more than $4 billion to over 40 million wallets in 2024, while the protocol processed more than 6 million attestations. Even if you haircut those numbers a bit for caution, the direction is obvious: this system is being used where verification and distribution touch each other directly.
That’s also why some of the older Sign case studies still hold up. OtterSec using attestations for proof of audit is a good example. The attestation is not just a badge saying “audited.” It becomes the authoritative object another party can check before trusting a contract. Same with KYC-gated contract flows, Web2 data onboarding through MPC-TLS plus zk proofs, or developer reputation use cases. The theme is consistent: verification isn’t the end of the process. It’s the condition that allows the next process to happen with less trust leakage.
Governance is less romantic than people think
I don’t think Sign’s governance story is the kind of DAO theater many token holders expect. And that’s probably fine. The official materials lean much harder into operational governance than pure token voting. In the S.I.G.N. governance docs, power is described through roles: sovereign authority, treasury or central bank operator, technical operator, auditor or supervisor. Governance keys approve upgrades, emergency actions, and parameter changes. Issuer keys sign credentials. Audit keys handle lawful access where relevant. The baseline expectation is multisig or HSM-backed controls, plus separation of duties. That’s a very institutional model of power.
The token complicates this a bit. Sign’s official token pages pitch $SIGN for access, staking, and governance, but the MiCA whitepaper is more precise: holders do not automatically get governance rights unless they operate as validators, and rights can evolve through protocol rules and community-led consensus rather than corporate ownership. I actually prefer that kind of bluntness. It avoids the fake decentralization script. Still, the tradeoff is real. If you buy SIGN expecting clean token-holder sovereignty, the present setup looks more like influence through network participation and ecosystem alignment than direct democratic control. 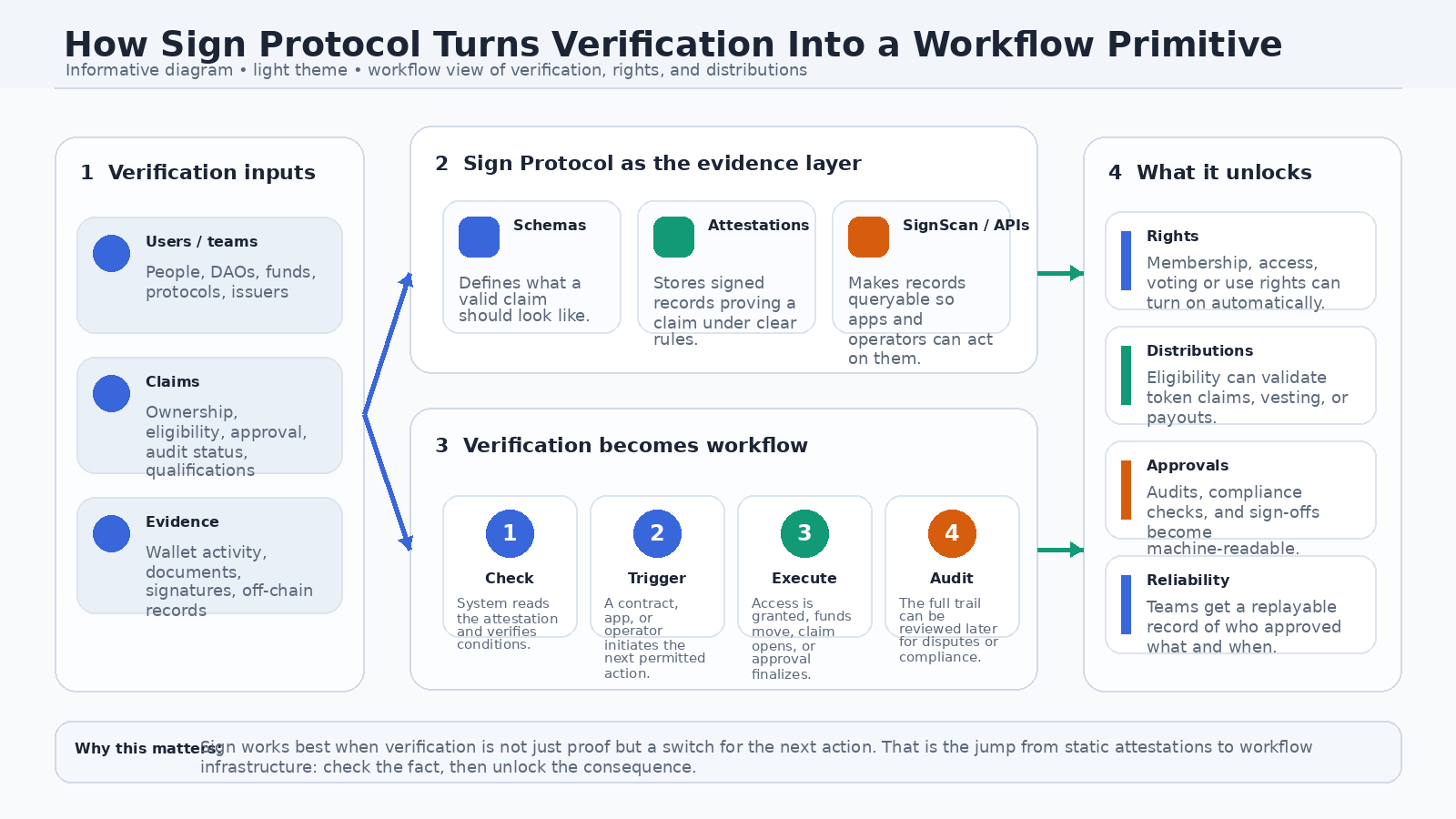
Ecosystem, culture, and why it’s trending now
What people do day to day around Sign is a mix of builder activity and community ritual. Builders use the SDKs, schema tools, explorer, and APIs. Non-coders can create and inspect attestations through SignScan. Token holders get pulled into staking, claiming, and the oddly branded but very intentional Orange Dynasty layer. I got a DM this week from someone who dismissed that whole orange culture as fluff, and I kind of get the instinct. But it does serve a purpose: it turns a very abstract infrastructure product into a recurring participation loop. Show up, stake, claim, use the tools, amplify the ecosystem, stay socially legible inside it.
As for why Sign feels more present right now, I’d point to three things. First, the docs were refreshed in February 2026 around the S.I.G.N. framing, which is a meaningful narrative upgrade from “attestation protocol” to sovereign-grade evidence infrastructure.
Sign was already getting attention before now. It released its token in 2025 and got strong financial support the same year. It reportedly raised $16 million in January 2025 and later raised another $25.5 million in October 2025. The token is still active in the market and people are still trading it. On March 23, 2026, CoinGecko said the token had a maximum supply of 10 billion, about 1.64 billion in circulation, and a market cap close to $533 million. All of this makes the project look active and keeps it in public view.What would change my mind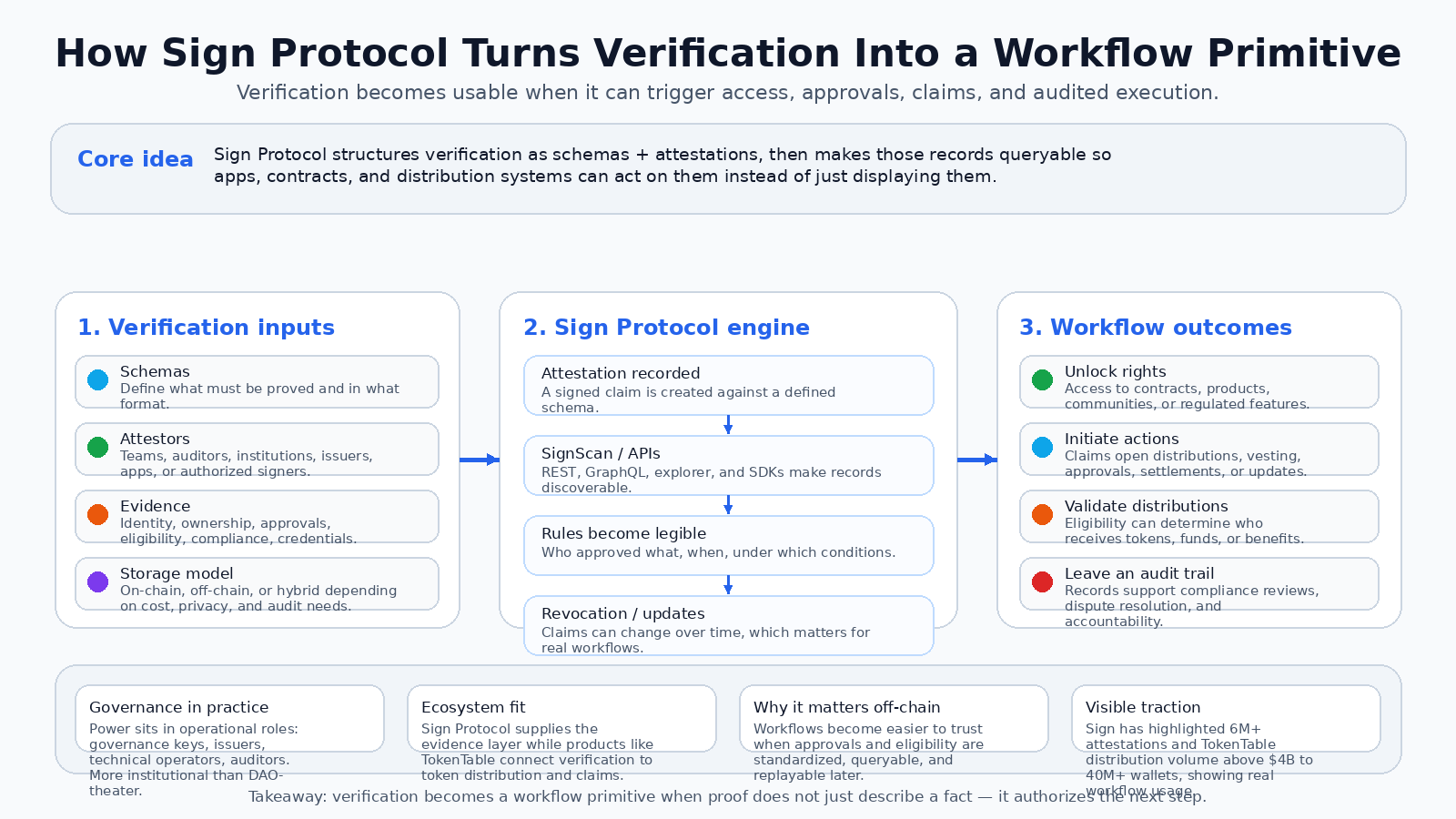
My current view is pretty simple. Sign Protocol is most compelling when verification is tied to consequences. Not identity for identity’s sake. Not credentials as collectibles. Verification that initiates a payment, unlocks a right, validates an allocation, or leaves behind evidence an auditor can actually use. That’s the workflow primitive idea, and Sign has a better shot at it than most because it links schemas and attestations to distribution, querying, and operational governance in one stack.
But I’d change my mind if the system stays better at describing sovereign-scale workflows than proving them in production. The biggest risk here is that the architecture becomes too polished as a narrative and too uneven as a public footprint. I want to see more visible third-party applications where attestations are not merely stored, but clearly driving off-chain decisions and on-chain execution at scale. Until then, my sharp takeaway is this: Sign becomes important the moment verification stops being a certificate and starts acting like a switch. Ttyl
