Crypto has long struggled with identity. Most projects either ignore it completely or swing to the other extreme with heavy KYC requirements. In both cases, privacy ends up compromised—either through absence or overexposure. Neither approach truly solves the problem.
That’s why Sign stands out.
Instead of treating identity as an afterthought, Sign places attestations at the core of its design. By combining encryption, zero-knowledge proofs, and selective disclosure, it offers a system where users can prove something about themselves without revealing everything. It feels less like a workaround—and more like a real attempt at balance.
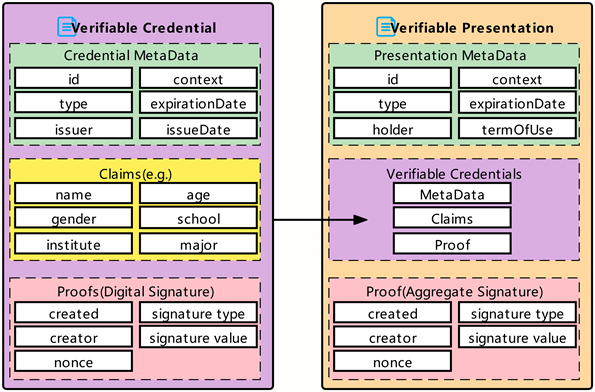
At the heart of this system are schemas and attestations. Think of a schema as a reusable data template—it defines what information exists and how it should be interpreted. An attestation, then, is the completed and signed version of that schema, stored on-chain. It’s a simple concept, but incredibly powerful in practice.
And the growth reflects that. In 2024 alone, schemas expanded to over 400,000, while attestations surpassed 6.8 million. That’s not theoretical adoption—that’s real usage. Developers aren’t just experimenting, they’re actively building.
Where Sign becomes particularly compelling is its privacy layer. With zero-knowledge attestations, you can prove facts—like being over 18 or residing in a specific country—without exposing underlying documents. It’s not data sharing; it’s cryptographic proof.
Equally important is revocability. Identity isn’t static—circumstances change. Sign allows attestations to be revoked, avoiding the risk of outdated or misleading credentials persisting forever. Surprisingly, many systems overlook this.
Then there’s the cross-chain dimension. Sign integrates Trusted Execution Environments (TEEs) and works with Lit Protocol to validate data across chains. Secure enclaves request only the necessary data, verify it, and return a signed result—without exposing the rest. Even specific data points, like a JSON path on Arweave, can be verified in isolation. It’s a precise, minimal-exposure model—but one that still depends on hardware integrity and operator trust.
SignPass adds another layer—an on-chain identity registry where wallets can hold credentials, certifications, and KYC proofs. The key advantage is reuse. Once verified, users don’t need to repeatedly submit personal data across platforms. In a world of constant data breaches, that’s a meaningful shift in user experience.
What’s even more notable is real-world adoption. Countries like Kyrgyzstan and Sierra Leone are already exploring Sign for digital identity systems. Sierra Leone’s vision, in particular, is ambitious: a reusable digital ID across public and private sectors, with programmable services like welfare eligibility verified on-chain—without exposing personal details.
Still, this isn’t a perfect solution.
TEE-based systems introduce new trust assumptions. Secure hardware has failed before, and reliance on developers and schema validators remains a risk. More importantly, without institutional recognition, even the most elegant cryptographic proofs have limited real-world value. Technology can be neutral—but adoption never is.
Even with these challenges, Sign represents a meaningful shift. It’s not about abandoning identity, nor about enforcing surveillance. It’s about enabling identity to move across systems—securely, privately, and selectively.
It may not be the final answer. But for once, it doesn’t feel like empty hype.
#SignDigitalSovereignInfra @SignOfficial