$SIGN #SignDigitalSovereignInfra @SignOfficial

I didn’t really question how broken online trust was until I noticed how much of it depends on screenshots.
Someone says they got whitelisted → screenshot Someone claims they contributed → screenshot Someone says they hold a role → screenshot
And somehow we all agree to trust pixels.
That’s when SIGN started to feel less like a tool… and more like a correction.
Not a better database. Not a cleaner UI. A different assumption entirely.
That claims on the internet shouldn’t be shown. They should be anchored.
What SIGN does quietly is remove the idea that trust lives in platforms.
Right now, trust is always rented.
Your identity sits inside Twitter. Your contributions sit inside Discord. Your achievements sit inside some backend you don’t control.
If the platform changes rules, deletes data, or just disappears your “proof” disappears with it.
And if your proof disappears with a platform it was never really proof.
SIGN flips that.
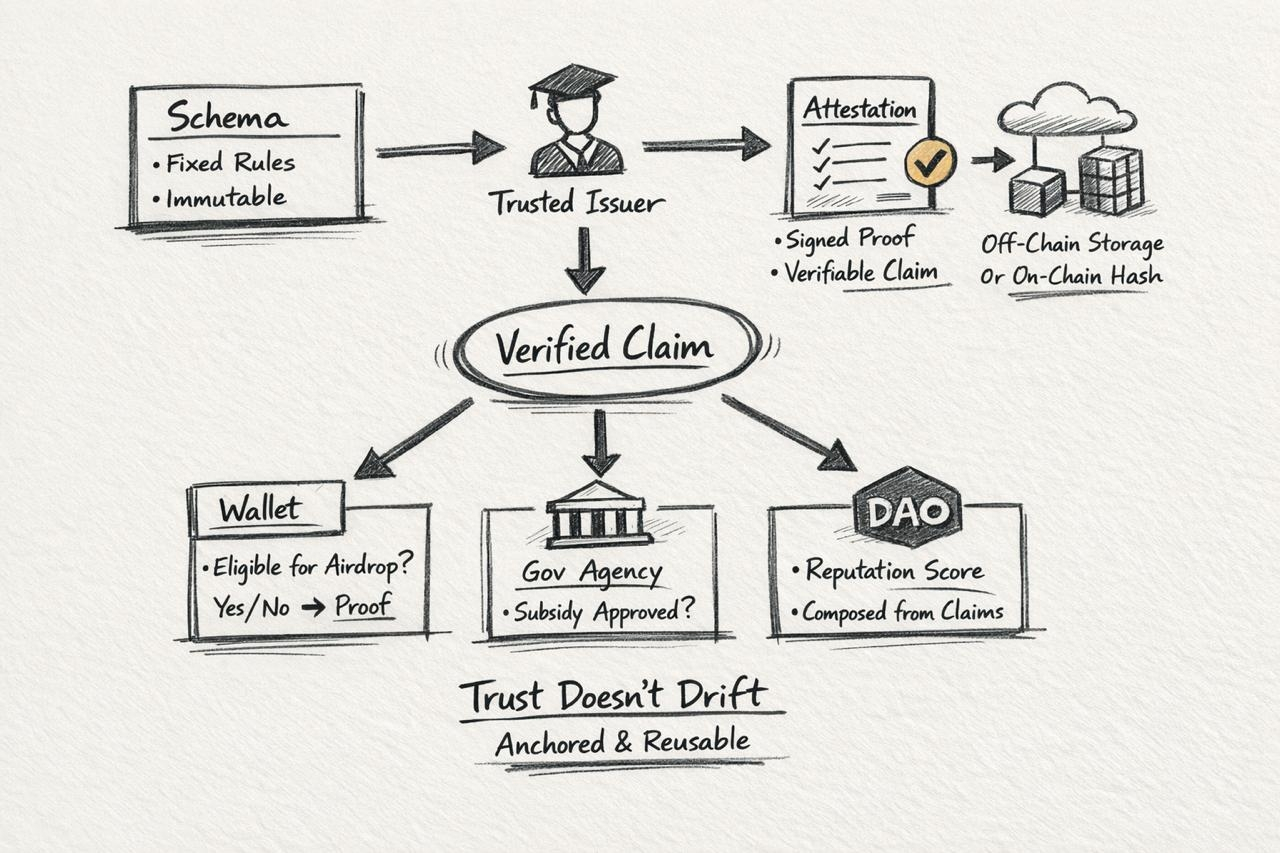
It takes the claim itself this wallet contributed, “this address is verified”, “this person belongs here” and turns it into an attestation.
Not a post. Not a badge. A signed, structured, verifiable claim tied to an issuer.
That sounds simple until you realize what it removes.
It removes interpretation.
Schemas are where the shift really begins.
Most people treat schemas like formatting. Like JSON structure. But in SIGN, schemas are constraints.
One schema = one idea. And that idea is fixed.
You can’t casually change what “verified user” means halfway through. You can’t silently expand what “eligible for benefits” includes.
If you want to change it… you create a new schema.
That feels restrictive at first. Honestly, even annoying.
But then it hits you…
That rigidity is what makes the system trustworthy.
Because the meaning of a claim doesn’t drift over time.
That’s why schemas in SIGN aren’t flexible by design. They force systems to commit to meaning before scale.
In most systems, trust breaks slowly. Definitions change quietly. In SIGN, change is explicit. It leaves a trail.
That’s not just structure.
That’s enforced consistency.
Then comes the part people underestimate: issuers.
An attestation isn’t just data. It’s a relationship.
Someone is staking their identity on a claim.
If a university issues a credential that’s their reputation on the line. If a DAO assigns a role that’s their governance signal. If a government verifies identity that’s institutional weight.
SIGN doesn’t try to replace trust.
It exposes it through an issuer layer the system can read.
Instead of asking “is this true?” You start asking “who said this is true?”
And suddenly trust becomes traceable.
Not socially… structurally.
But where it gets uncomfortable is storage.
Because this is where most systems pretend everything is clean.
On-chain storage sounds perfect until you think about scale. You don’t put national identity systems fully on-chain without turning gas into infrastructure cost.
So SIGN doesn’t force purity.
It allows hybrid models by design.
Data can live off-chain. Hashes anchor it on-chain. Or you push it to something like Arweave for persistence.
But here’s the part most people skip…
Storage choice is not neutral.
It directly shapes the reliability of your attestations.
If your data layer fails the attestation still exists, but verification weakens.
So trust here isn’t just cryptography.
It’s architecture across layers.
Now imagine this in practice.
A government issues an attestation: “this wallet is eligible for a subsidy.”
That claim follows a fixed schema. It’s signed by a known issuer.
Another agency doesn’t ask you to upload documents again. It doesn’t re-run verification from scratch.
It just checks:
Is the attestation valid? Does it match the schema? Is the issuer trusted?
That’s it.
No repetition. No re-validation loops.
That’s not UX improvement.
That’s coordination compression.
And that’s where SIGN starts to dominate.
Because attestations aren’t just proofs… they’re reusable verification primitives across systems.
Then you reach ZK.
This is where things stop being intuitive.
Because now the system is saying:
You don’t need to see the data to trust the claim.
You just need proof that the claim satisfies the rules defined by the schema.
Selective disclosure isn’t just a feature here. It’s enforced at the verification layer.
You can prove eligibility without revealing identity. You can prove ownership without exposing balance. You can prove compliance without exposing full history.
That changes verification completely.
It stops being about revealing truth.
It becomes about proving constraints against a defined system.
That’s a very different model of trust.
And SIGN is building directly into that model.
The deeper shift is this:
Trust stops being an experience and becomes infrastructure.
Right now, trust feels like something you earn socially.
Followers. Reputation. Visibility.
But those are signals. Not proofs.
SIGN moves trust into something machines can verify without context.
No scrolling. No guessing. No “seems legit”.
Just:
Is the claim valid? Who issued it? Does it satisfy the schema?
That’s not a better interface.
That’s a different layer entirely.
But it’s not clean.
Schema rigidity makes upgrades painful. Issuer power can concentrate trust. Storage introduces dependency layers. ZK is still hard for most developers.
SIGN doesn’t remove trade-offs.
It makes them explicit.
And that’s what makes it stronger.
Because systems don’t break from complexity.
They break from hidden assumptions.
The part that changed how I see SIGN isn’t just technical.
It’s behavioral.
If claims become permanent and verifiable…
People stop performing trust.
They start structuring it.
Projects can’t inflate contributions easily. Users can’t fake history without leaving traces. Institutions can’t quietly redefine eligibility inside black boxes.
Because everything is anchored to:
schemas (meaning) issuers (responsibility) attestations (proof)
That triangle is where SIGN holds dominance.
Not as a feature.
As a system boundary.
Most systems today don’t fail at trust because of bad UX.
They fail because their “proof” disappears the moment the platform does.
SIGN removes that fragility.
It defines proof independent of platforms.
And maybe that’s the real shift.
SIGN doesn’t just improve how we trust online.
It defines what counts as proof in the first place.
And once that definition moves on-chain…
Everything built on top starts behaving differently.
Not louder.
Just harder to fake.