The approval was still valid on @SignOfficial . The institution had already stopped meaning it that way.
Great.
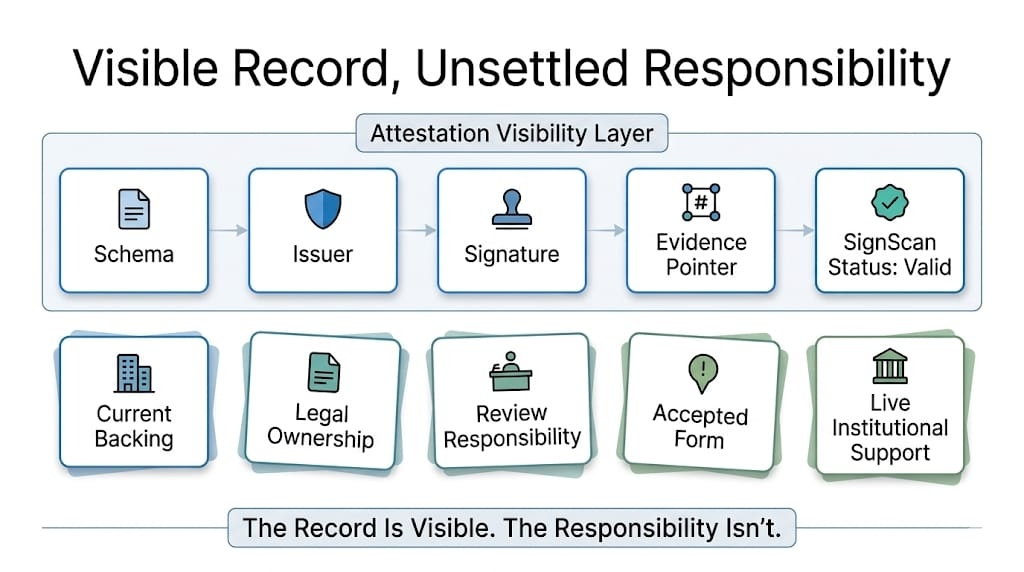
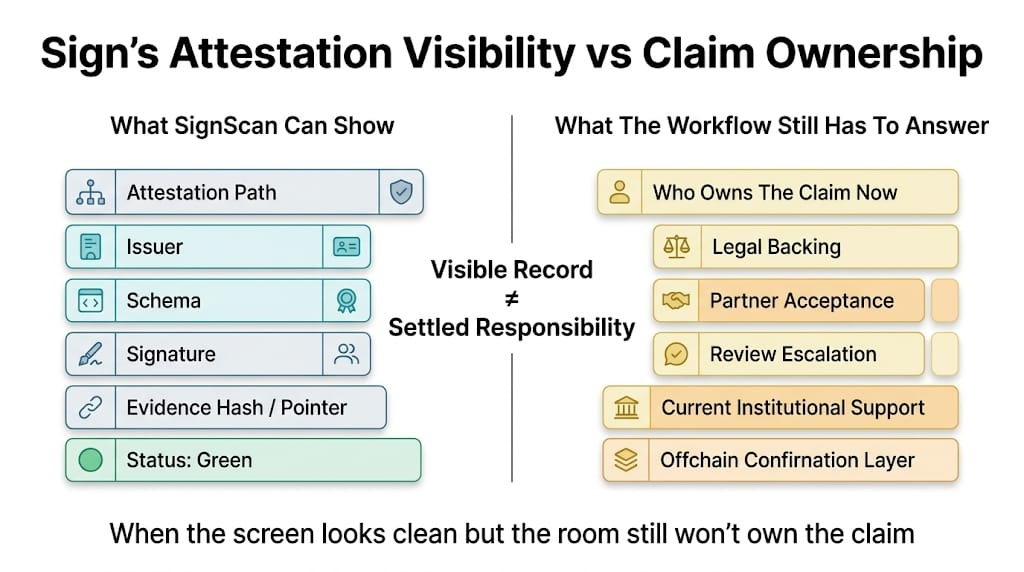
I keep getting stuck on that distinction because institutions are weirdly good at letting something expire socially... before they ever bother expiring it formally. Everyone around the workflow starts acting like the old approval class is legacy, discouraged, basically dead except for cleanup and edge cases and whatever else people say when they want something gone without doing the work of actually killing it. Then the attestation on Sign protocol stays live. The signer path stays live. The record still resolves. SignScan still shows it cleanly. And some downstream system, naturally, keeps acting like valid means welcome.
That is where it starts going bad. Like actually bad.
Not forged records. Not broken signatures. Not even the older signer-still-there problem exactly. This one is meaner in a smaller way. The institution has already stopped wanting the old approval to matter in the full present-tense sense. Ops knows it. Compliance knows it. Program people definitely know it because they are the ones rolling their eyes in meetings and saying “that path is basically sunset” while the path is, technically, still very much alive in the actual system.
Great setup.
So the old Sign approval survives in two different states at once.
Formally live.
Socially stale.
And on Sign, the formal side always looks calmer.
A schema got used for an approval class. Fine. Attestations issued under it. Maybe a lighter route, a launch route, a stopgap review path, some interim approval surface that got a program moving before the institution decided what the grown-up version was supposed to look like. Happens all the time. Then the institution tightens. New route. New control. New expectations. Maybe not even a new schema, which is where people really start lying to themselves. Sometimes the exact same record class just quietly stops being something anyone serious wants to lean on for new action. That is the ugliest version, honestly. Nothing visibly breaks. The trust just drains out of it first.
What expires first in these systems, trust or state.
Usually trust. State is lazy.
Ops starts treating the old approval like legacy baggage. Good enough for renewals maybe. Good enough for a narrow cleanup path. Not the thing you want showing up in the newer distribution leg, or the stricter access route, or anything with extra exposure attached. But if that informal expiry never gets translated into something a downstream system can read, then the record keeps moving with all the old machine-readable dignity it had on day one. Signed. Queryable. Valid enough-looking. Same old story. The institution got less willing. The system did not.
And then somebody downstream reads it literally.
That should not be surprising anymore. It still annoys me anyway.
Because the later system does not get the social memo. It gets the attestation. Maybe TokenTable reads it. Maybe some internal claims logic does. Maybe a partner integration does the usual lazy thing and says valid record under recognized schema, good enough for now. Maybe reporting keeps counting it as current because no one wants an extra column called “approved under a path we no longer really stand behind.”
Nice clean dashboard. Bad read.
Then some export still included it.
Still in the supported list....
green in the dashboard. Good.
Still enough for the claims file.
Not valid versus invalid. Worse. Valid versus still wanted.
And Sign $SIGN keeps the old record clean. Fine. The institution already stopped wanting that clean record to carry this much current weight.
Same schema. Same attestation class. Same clean return. Enough for the next system to stop asking what changed off to the side.
That is how the old class keeps sneaking into new work.
Historical truth is fine. The approval happened. The record should exist. The problem starts when a downstream system cannot tell “this approval still exists” from “we still want it carrying current action here.” Those are not the same thing. Not even the same thing, some weeks.
Maybe the older approval class was never formally sunset because legacy renewals still needed it. Maybe legal never signed off on killing it. Maybe engineering did the usual thing and left it in because removing it cleanly would have touched too many downstream dependencies and nobody wanted that fight before quarter close. Fine. Normal. Miserable, but normal.
Then treasury asks why a wallet cleared under that old path is still showing up in a newer distribution run.
Ops says the attestation is still valid.
Engineering says the schema is still supported.
Program team says nobody was supposed to be using that approval class for new flow anymore.
Compliance says yes, well, that was the informal understanding.
Informal understanding. Great control surface.
Where did that understanding live for the system. Not in the meeting. In the workflow.
Was the older approval class excluded from the payout filter. Was there a route split. Did the partner integration know “legacy valid” was supposed to mean “do not keep building on this.” Did reporting stop collapsing it into current approvals. Or did everybody keep trusting the same clean Sign object because it is much easier to operationalize a live record than a dead vibe around the record.
That is usually the one.
And the record never has to look suspicious for this to hurt. That is what makes it so annoying. It can still resolve correctly. Still verify. Still map back to a real schema and a real signer and a real historical approval. Nothing about the attestation has to be false. The institution just stopped wanting that type of yes to function as a full-strength yes long before it found the energy to encode that change honestly.
Then the old approval class starts doing new work by inertia.
That is when treasury notices.
Maybe access stays open longer than anyone intended. Maybe a later claims leg still reads the old class as enough. Maybe a partner system keeps using it because the response coming back from Sign still looks machine-clean and nobody built in a “socially expired but technically live” state because, obviously, that would require admitting how these systems actually work.
So the approval on Sign infrastructure stays valid.
The institution stops meaning it in the same way.
And by the time someone asks which mattered more, the downstream path has already answered for them.

