$SIGN #SignDigitalSovereignInfra @SignOfficial

The part that bothered me wasn’t that the signer was wrong.
It was that the signer was still right… just not right anymore.
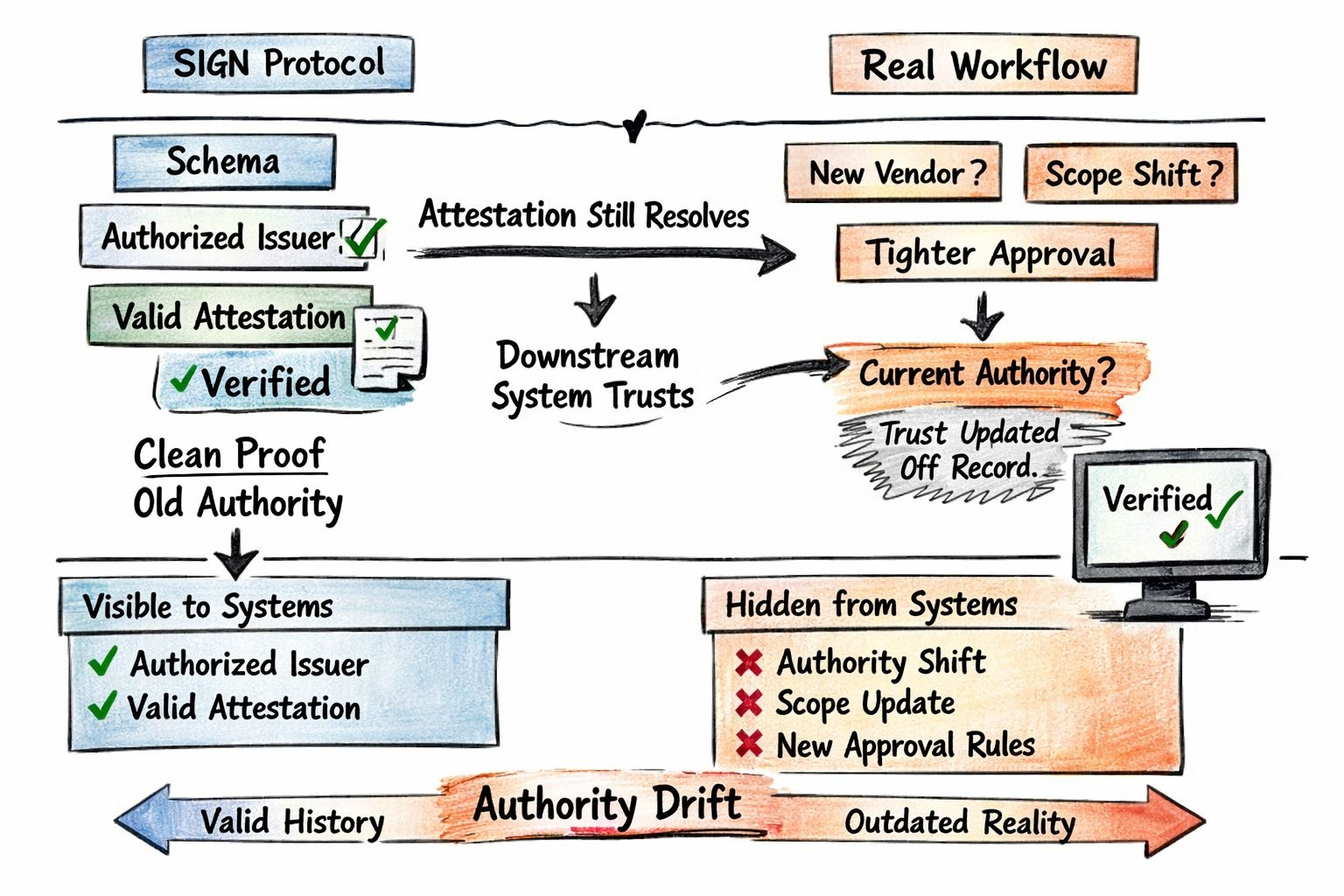
Everything looked clean on Sign Protocol.
Authorized issuer. Valid signature. Schema matched. The attestation resolved exactly how it should.
No errors. No warnings.
And still… the workflow had already moved on.
That’s where SIGN gets interesting and a bit uncomfortable.
Because SIGN guarantees something very specific:
👉 the claim is valid under a schema 👉 the issuer was authorized at the time of signing
That’s it.
It doesn’t guarantee that the institution still stands behind that issuer right now.
And that gap is where things break.
Because in SIGN, the structure is clean:
Schema defines meaning. Issuer is allowed to sign. Attestation binds both into proof.
Verification checks the schema and the signature.
All solid.
But none of that tracks whether authority is still current.
What I’ve seen is this:
Issuer gets registered under a schema. Attestations start flowing.
Then the institution shifts.
New vendor. New approval boundary. Scope gets narrowed.
But the issuer isn’t fully revoked. Or not revoked everywhere.
So now you have:
👉 schema still valid
👉 issuer still resolvable
👉 attestations still verifiable
But authority has already moved somewhere else.
And SIGN will still return that attestation as valid.
Because from its perspective… it is.
That’s not a flaw.
That’s the design.
Most people assume SIGN removes trust. It actually makes mistakes easier to scale if you model authority wrong.
SIGN gives you clean proof. It does not give you correct authority.
So downstream systems do what they’re designed to do.
They verify the attestation.
They don’t question the lifecycle behind it.
Because that lifecycle isn’t encoded unless you explicitly design it.
This is the real mechanism most people miss.
If you don’t define:
issuer revocation rules
scope boundaries
time-based validity
active issuer sets per workflow
then old authority keeps passing new decisions.
And that’s where SIGN becomes powerful if used properly.
Because it lets you move from:
“issuer is trusted” ❌
to:
“issuer is trusted under specific conditions” ✅
Now authority becomes programmable.
Not static.
Not assumed.
Without that, you get what I saw.
Clean issuer trail. Dirty institutional reality.
And the system trusts the clean thing… because that’s all it can read.
So now the question changes.
Not:
“Is this attestation valid?”
But:
“Is this issuer still valid for this exact context, right now?”
SIGN doesn’t break when authority drifts.
It keeps working.
And that’s exactly why the mistake becomes harder to notice.