$SIGN #SignDigitalSovereignInfra @SignOfficial

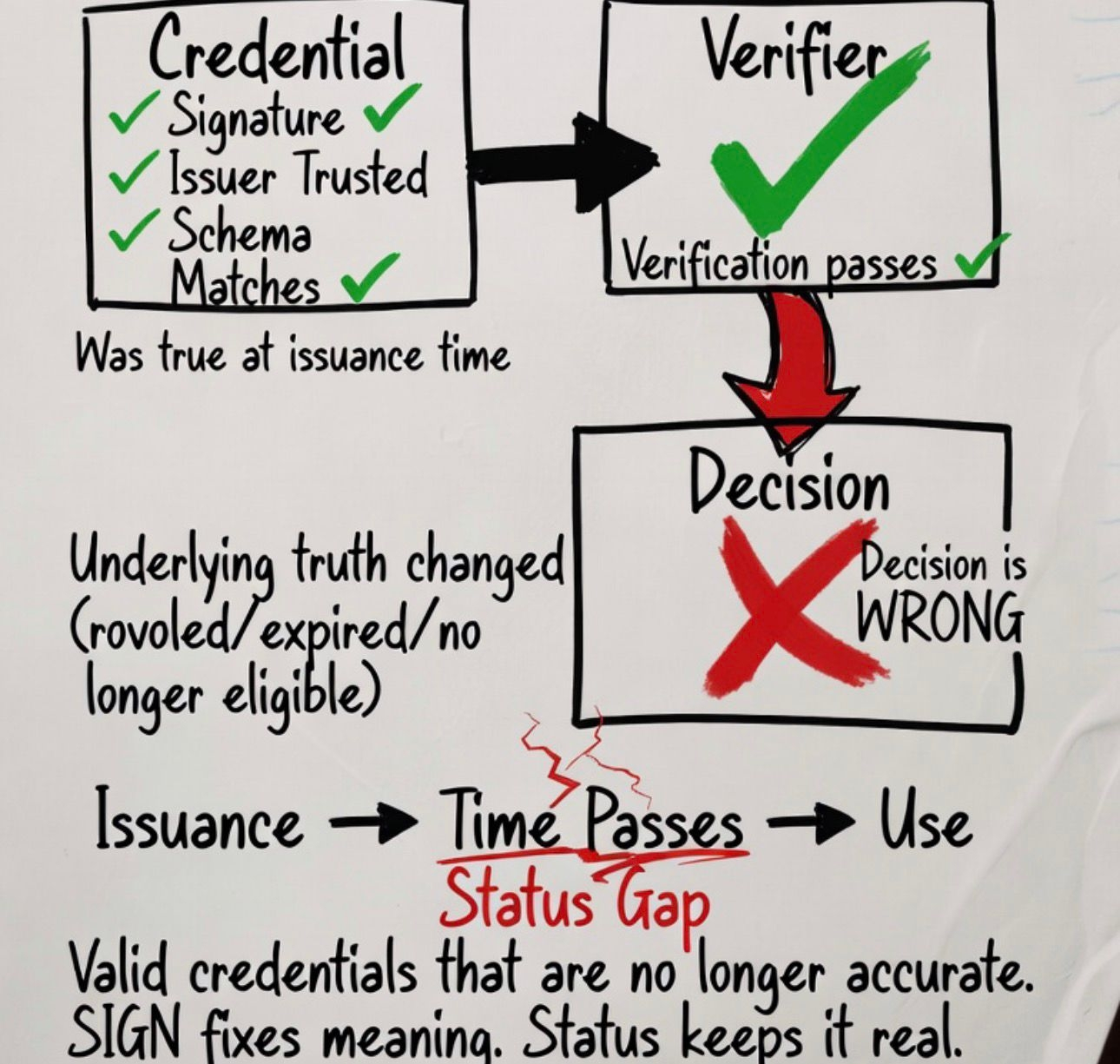
I used to assume that once a credential is issued and verified, the job is done. If the signature checks and the issuer is trusted, the system should accept it.
But that only works if nothing changes after issuance. In most systems, that assumption is already false.
In practice, most claims are not permanent. A license can be revoked. An eligibility status can change. A compliance flag can be removed. The credential itself doesn’t update, but the underlying truth does.
That creates a gap. The system can verify that something was true at a point in time, but it has no guarantee that it is still true when it is used later.
This is where things start to break in a quiet way. The credential looks valid. Verification passes. There is no visible error. But the decision based on it is wrong because the state behind it has already changed.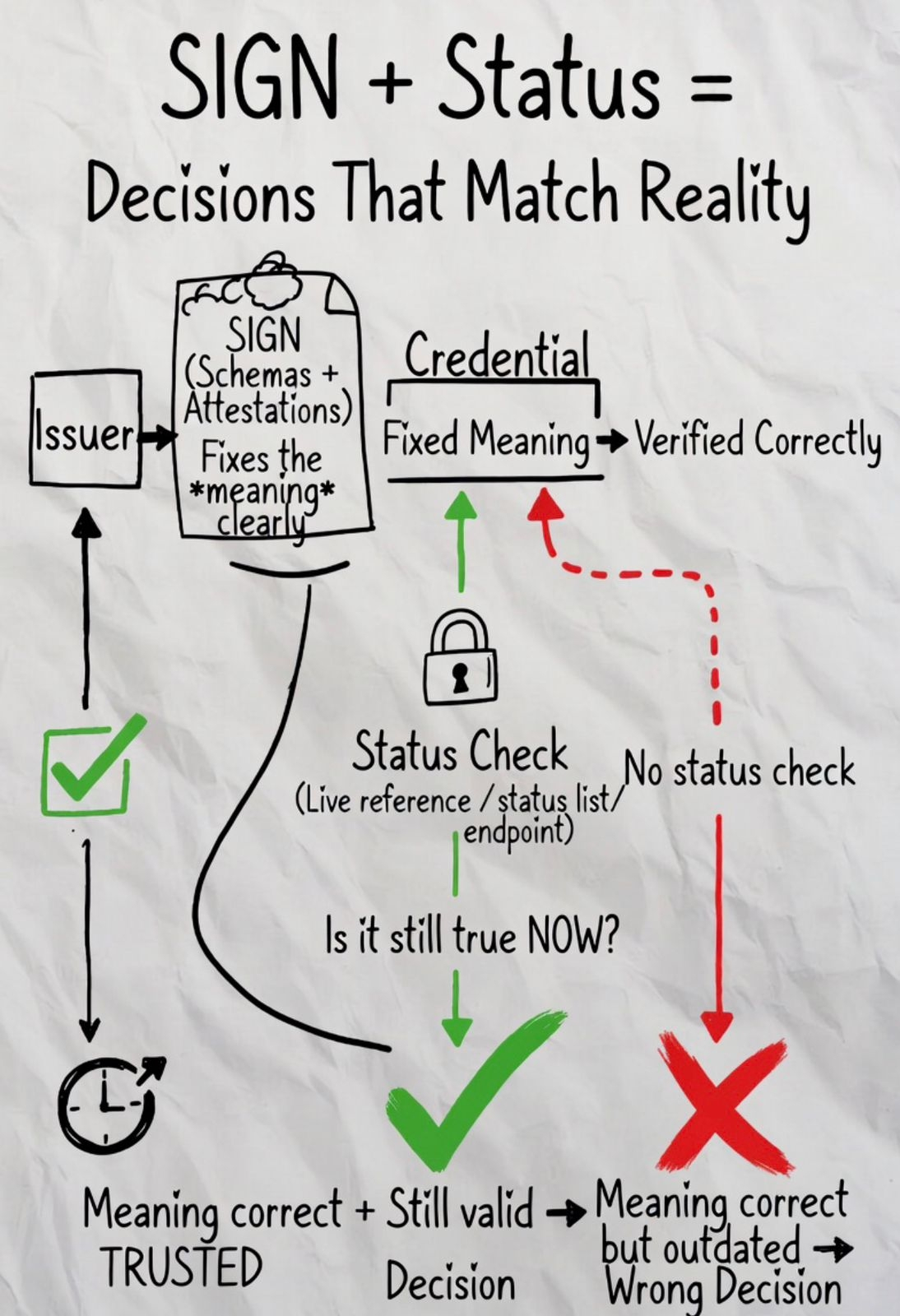
I’ve seen simple flows where an issued credential is reused after its conditions no longer hold. The system accepts it because it has no way to check current status. Nothing fails technically, but the outcome is incorrect.
The problem is not invalid credentials. It’s valid credentials that are no longer accurate.
Revocation and status lists exist to deal with this, but they are often treated as optional features.
In practice, this means attaching a live reference to the credential a status list or endpoint that must be checked at the moment of use. Without that step, the system is relying on a snapshot, not current state.
A status check answers a different question than verification. Verification asks if the credential was issued correctly. Status asks if it should still be accepted now.
Without that layer, systems rely on outdated claims. At small scale, it looks like occasional inconsistency. At larger scale, systems stop trusting each other.
Not because verification fails, but because decisions based on verified data start conflicting across systems.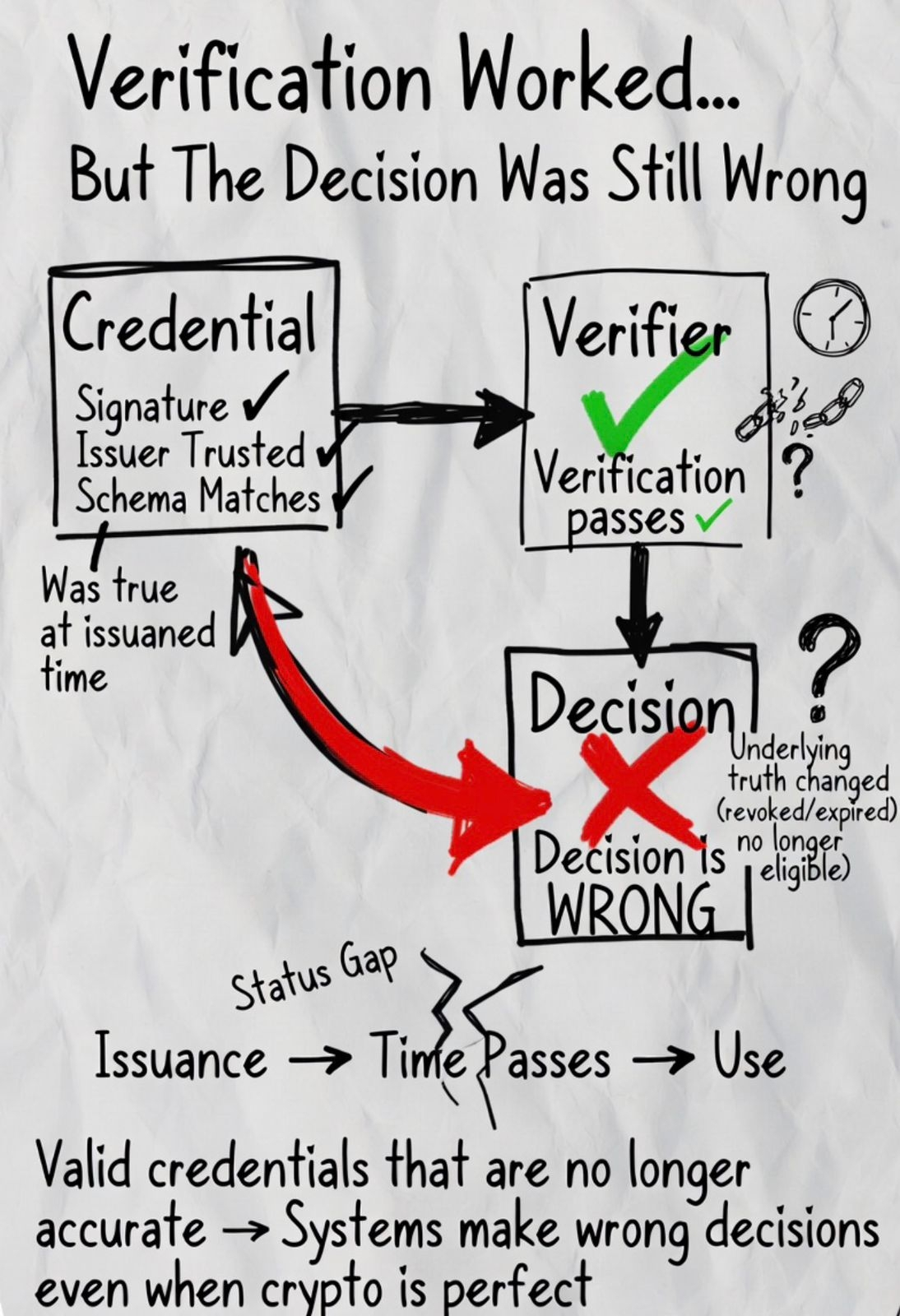
Now bring SIGN into this.
SIGN makes the meaning of a claim clear and consistent through schemas and attestations. It removes ambiguity at issuance and makes verification reliable across systems.
But even with perfect schemas, a system that ignores status will keep accepting claims that should have already expired.
So meaning can be correct, and still mislead.
That’s why this layer matters. Issuance defines what the claim is. SIGN ensures that definition is shared. Status determines whether that claim still holds.
If any one of these is missing, the system doesn’t break immediately. It just keeps making decisions based on outdated information.
That’s harder to detect, and more damaging over time.
The issue is not whether a credential can be verified. It’s whether it is still valid at the moment it is used.
The system is not failing to verify.
It’s failing to keep up with reality.