I had both attestations open in separate tabs and they were being annoyingly polite about the disagreement.
Same issuer. Same recipient. Same program. Same claim, basically. Both verified cleanly. Both came back as valid Sign attestations. No broken signature, no revoked status, no obvious corruption, nothing dramatic enough to make the problem feel honest.
That was the problem.
The first schema was the old one. Back when the team wanted speed more than precision. A narrower structure, fewer required fields, cleaner issuance flow. You could read it and feel exactly what had happened in the room when they designed it: ship now, tighten later. So they did. They issued against it for months. Hundreds of credentials, maybe more. All of them living on just fine inside the Sign workflow because Sign does not care whether a schema is old or new in some emotional sense. It cares whether the attestation matches the schema it references, whether the issuer signed it, whether the record still stands.
Then the program matured and the schema changed.
Of course it changed.
A field was added because the old one was too vague. A status definition got tightened because people were reading too much into a loose label. One boolean turned into something more precise. A missing qualifier finally got pulled into the structure because someone, somewhere, had already used the older version in a way it was never supposed to carry.
All normal. All responsible. All the boring language teams use when they are cleaning up the consequences of earlier confidence.
So they published the new schema version in Sign Protocol and started issuing under that instead.
Which sounds orderly until you are the one staring at a live system still carrying the old attestations forward like nothing happened.
That is what versioning hides so well at first. People talk about it like it is registry hygiene. Developer maintenance. Just keeping structures current. But once those structures are tied to live attestations, schema versioning stops being maintenance and starts becoming memory management for institutional judgment.
Because the older credentials do not evaporate out of courtesy.
They remain signed. Remain structured. Remain technically valid under the schema that existed when they were issued. And if your downstream logic is not careful — if your verifier, eligibility screen, or risk workflow is still happy enough with “valid attestation exists” — those old credentials keep moving through new rules with their old shape intact.
That is how I ended up with two histories for the same subject that were both defensible.
The earlier credential was not fake.
The later credential was not correcting fraud.
The system had simply learned to describe the same kind of claim with more precision than it used to.
And now I had to decide what the machine should do with that.
Trust the latest version because the program knows more now?
Trust the earlier one because it was valid when issued and maybe still legally or operationally relevant?
Treat them as equivalent because they both verify?
That last option is where people start lying to themselves. Verification only tells me each attestation is internally sound against its own schema. It does not tell me they mean the same thing at runtime. It definitely does not tell me which one should carry more weight once a live workflow has to collapse them into a single answer.
That part is not solved by cryptography.
That part is governance wearing a technical mask.
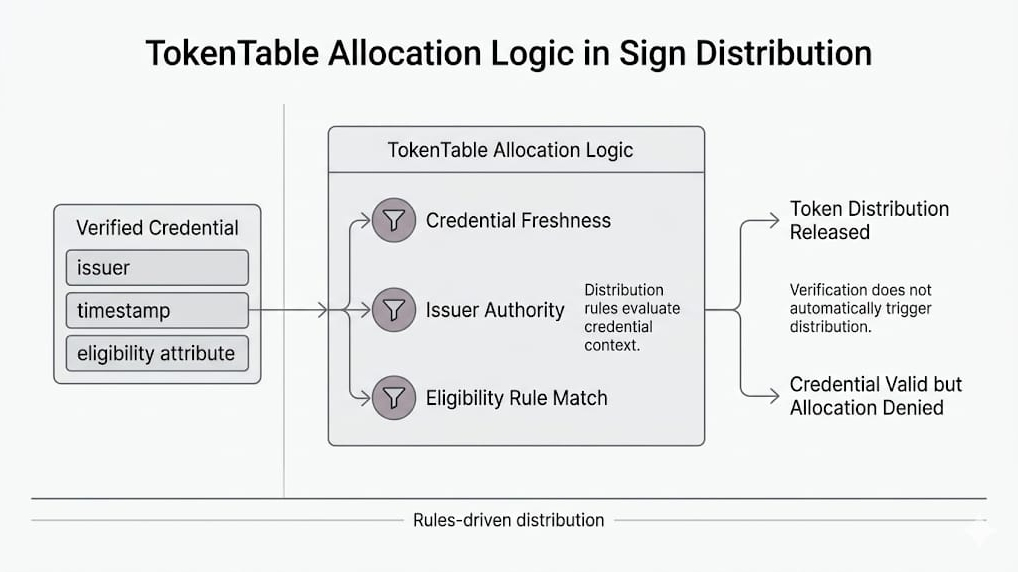
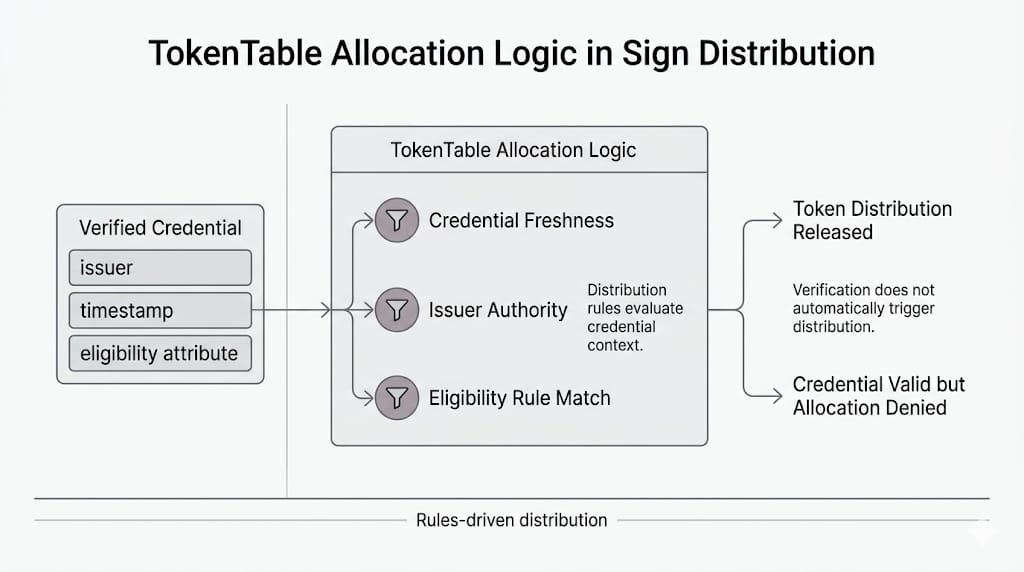
And Sign makes the discomfort sharper, not softer, because the protocol is so explicit about the schema-attestation relationship. The attestation is not free-floating truth. It is truth as structured by a particular schema at a particular moment in the life of a program. Change the schema and you have not just updated a template. You have changed the shape of what the system is prepared to recognize.
The dangerous part is that both generations can still sit there looking equally official.
Same green checks.
Same issuer name.
Same verification path.
Different historical assumptions frozen inside each one.
So I kept both tabs open longer than I needed to, like one of them might confess first.
Neither did.
They just sat there, both valid, both legible, both ready to be used downstream by whatever system was impatient enough to pretend validity and priority were the same thing.