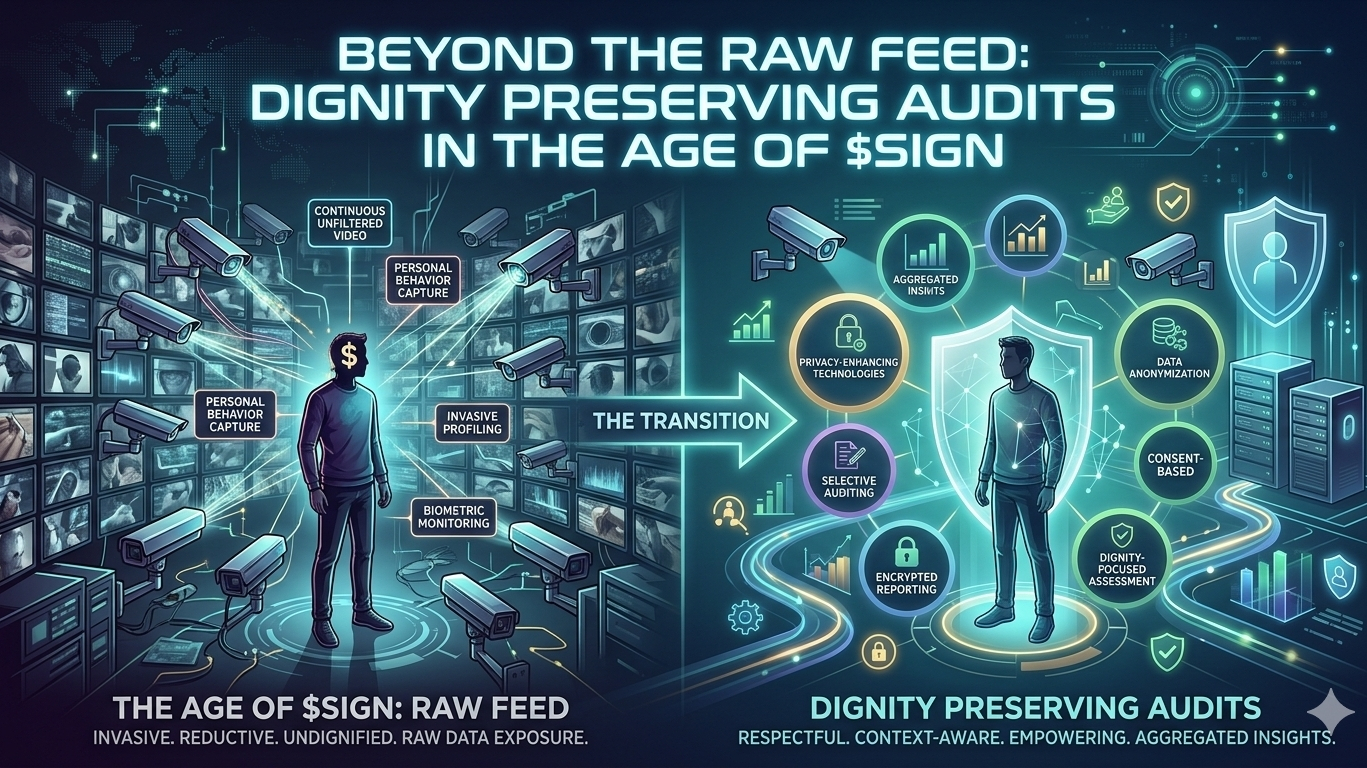
Government welfare programs face a recurring paradox. To ensure public funds are used correctly to prevent fraud and waste auditors often demand "total visibility." But in practice, total visibility quickly morphs into excessive exposure. The auditor’s true mission is actually quite narrow, they need to confirm that disbursement followed the established rules and that there is no evidence of misappropriation or error. However, many audit processes ultimately turn into a demand for the "raw feed" identity details, family income, exact addresses and sensitive demographic markers that have nothing to do with rule execution.
For the beneficiary, this turns a moment of support into a moment of vulnerability. Especially in regions where social trust is a delicate resource, the requirement to "lay bare" one's life can be a dealbreaker. Many people would rather forgo the aid they are entitled to than have their private details circulate among multiple systems and strangers. This psychological resistance is real, when the audit process lacks boundaries, the feeling of being scrutinized by the entire system directly impacts the willingness to apply.
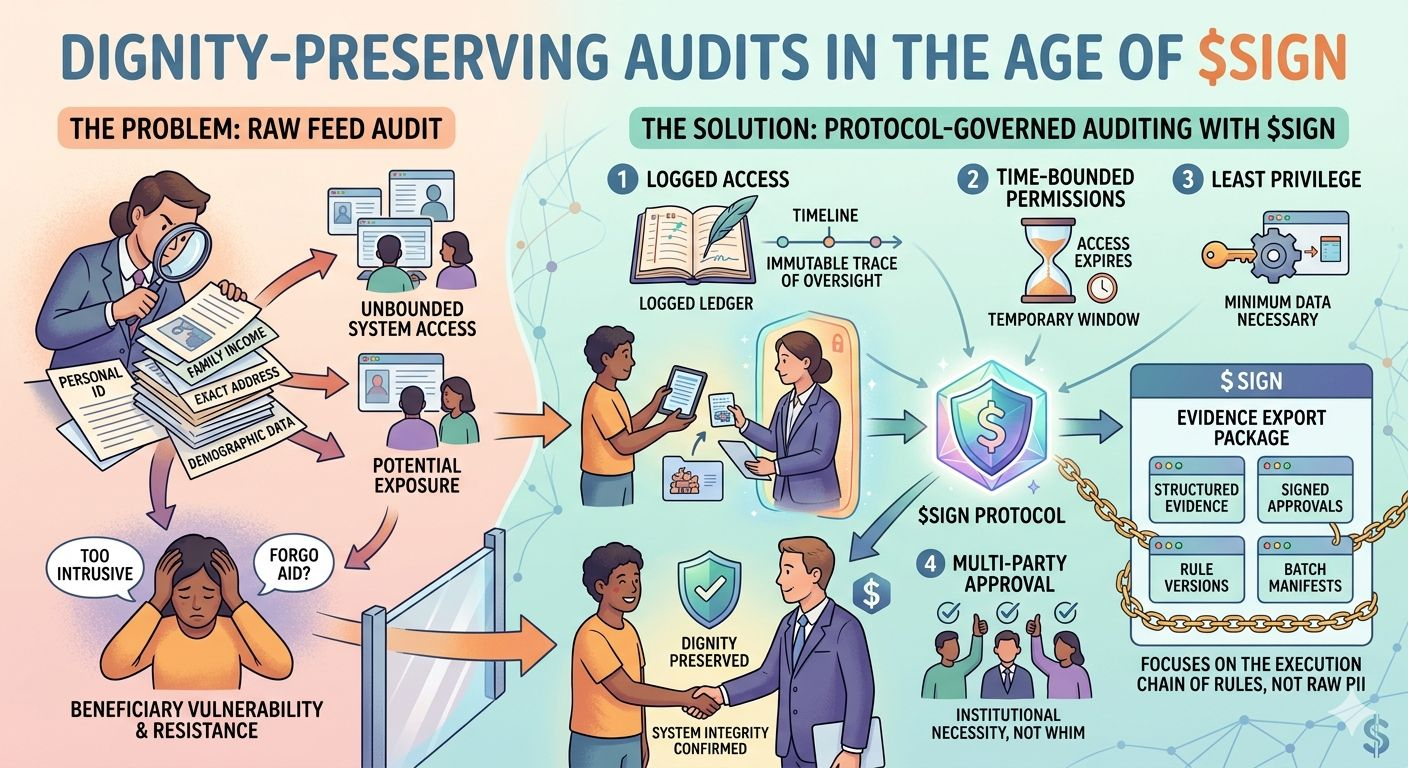
The approach outlined by @SignOfficial offers a "healing" resolution to this friction. It reframes auditing from an all access pass into a strictly governed protocol through four realistic requirements.
✨First, every access is Logged, the audit itself must leave an immutable trace of who looked and what they saw, ensuring the oversight process doesn’t become its own black box.
✨Second, permissions are Time bounded. Access is not a permanent backdoor but a temporary window that automatically expires, preventing "emergency access" from lingering for months.
The most vital principle is Least privilege. 🔥This ensures that auditors receive only the minimum data necessary to complete their task. It recognizes that an audit requires judgment, not prying. By supplementing this with Multi party approval, the system moves the decision to access sensitive data away from personal whim and into the realm of institutional necessity.
This philosophy is made practical through the Evidence Export Package. Instead of exporting raw PII, the system provides structured evidence, signed approvals, rule versions, batch manifests and settlement references. This approach is fundamentally correct because it focuses on the execution chain of the rules. If the rule versions and approval records match, the auditor has confirmed the integrity of the program without ever needing to see the beneficiary’s private background.
The value of $SIGN is found in this boundary. Auditing is not an occasional choice, it is a mandatory and periodic requirement of the regulatory environment. 🔥🔥Every fiscal year, every project and every anomaly triggers these operations. 🚀
By turning every authorization, log and evidence package into a protocol call, Sign ensures that transparency does not come at the cost of dignity. It allows the system to see what must be seen, without touching what should remain private.
@SignOfficial #signdigitalsovereigninfra $SIGN #SignDigitalSovereignInfra