The signature was still perfect. That was the problem.
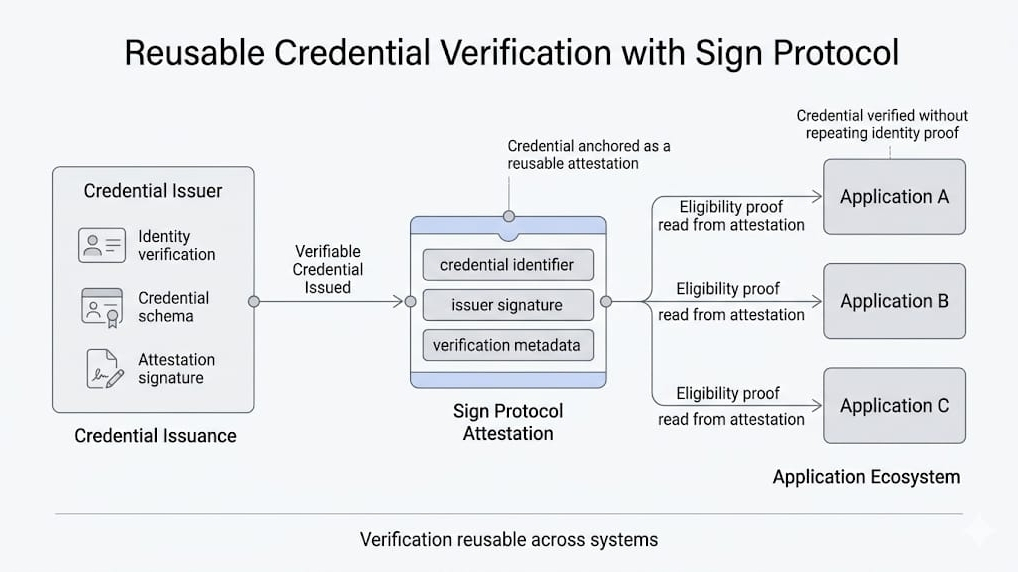
I had the attestation open in one tab, the current program checklist in another, and a compliance thread slowly getting meaner in the corner of the screen. The record verified cleanly. Schema matched. Signature checked out. Status looked fine. No revocation, no obvious dispute marker, no broken chain of custody. In Sign terms, it still behaved like a real attestation is supposed to behave: a signed structured statement that can be verified later, relative to its schema, signer, authority, status, and supporting evidence.
Which should have made the decision easy.
Instead it made it worse, because now the argument was no longer about whether the statement was authentic. It obviously was. The argument was about whether authenticity was still carrying the same meaning it had on the day the issuer signed it
That is a much uglier question.
The issuer had been legitimate at issuance. No drama there. They had the authority then. The attestation was produced under a valid workflow then. The evidence behind it made sense then. But “then” had started doing too much work. The program had changed since. Oversight changed. Risk tolerance changed. Half the internal language around acceptable proof had quietly drifted. Nobody had revoked the old attestation because, technically, nothing inside the record had become false in the neat machine-readable way people like. The statement still existed. The issuer still existed. The signature still verified. Sign had preserved exactly what it was built to preserve: an attributable claim you can inspect later.
Later just turned out to be the dangerous part.
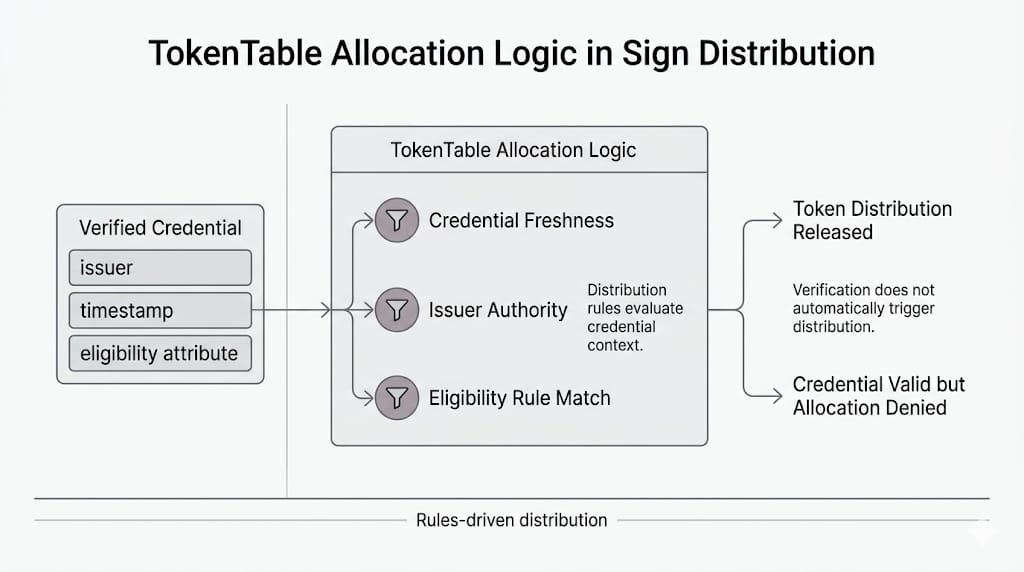
I think people talk themselves into the wrong mental model here because “verifiable later” sounds stronger than it is. It sounds like the system solved time. Like the hard part was binding a claim to an issuer in a durable way and now the future can just consult the record and move on. But Sign does not actually say that. The docs are calmer than that. They are annoyingly precise. Verification is a stack: schema, signature, authority, status, evidence. Not one clean yes or no. And that last part matters because authority is not some eternal glow left behind by a signature. It is part of context. Status is part of context. Evidence policy is part of context.
So there I was, staring at something that was still valid enough to pass the protocol checks and still awkward enough to make a human hesitate.
That hesitation is where Sign gets interesting in a very specific way.
Because Sign is excellent at preserving attribution. It is excellent at making a statement durable, inspectable, portable, queryable later. That durability is the feature. But durability does not freeze the institution around the statement. It does not freeze what counted as acceptable authority in the room where the attestation was first issued. It does not freeze how much weight downstream teams are willing to place on that issuer six months, twelve months, eighteen months later. The record remains crisp. The surrounding assumptions go soft.
I could feel the team trying to force a simpler category onto it.
If it verifies, accept it.
If it’s outdated, reject it.
Nice clean options. Very satisfying. Also not honest.
Because nothing here had actually crossed the clean rejection line. In Sign, attestations are generally treated as append-only records. Systems handle change by revoking, superseding, or attaching corrections and disputes, not by pretending the old record never existed. The old statement was still there doing what old statements do best: insisting that it was, in fact, once said by someone who really was allowed to say it.
And maybe that is the real pressure point.
Not whether the attestation is authentic. It is.
Not whether the issuer was real. They were.
The pressure comes later, when a perfectly authentic Sign attestation arrives in a workflow that has aged into a different idea of what that issuer now means. The signature survives the context that made it comfortable.
The cryptography keeps its shape.
The institution doesn’t.