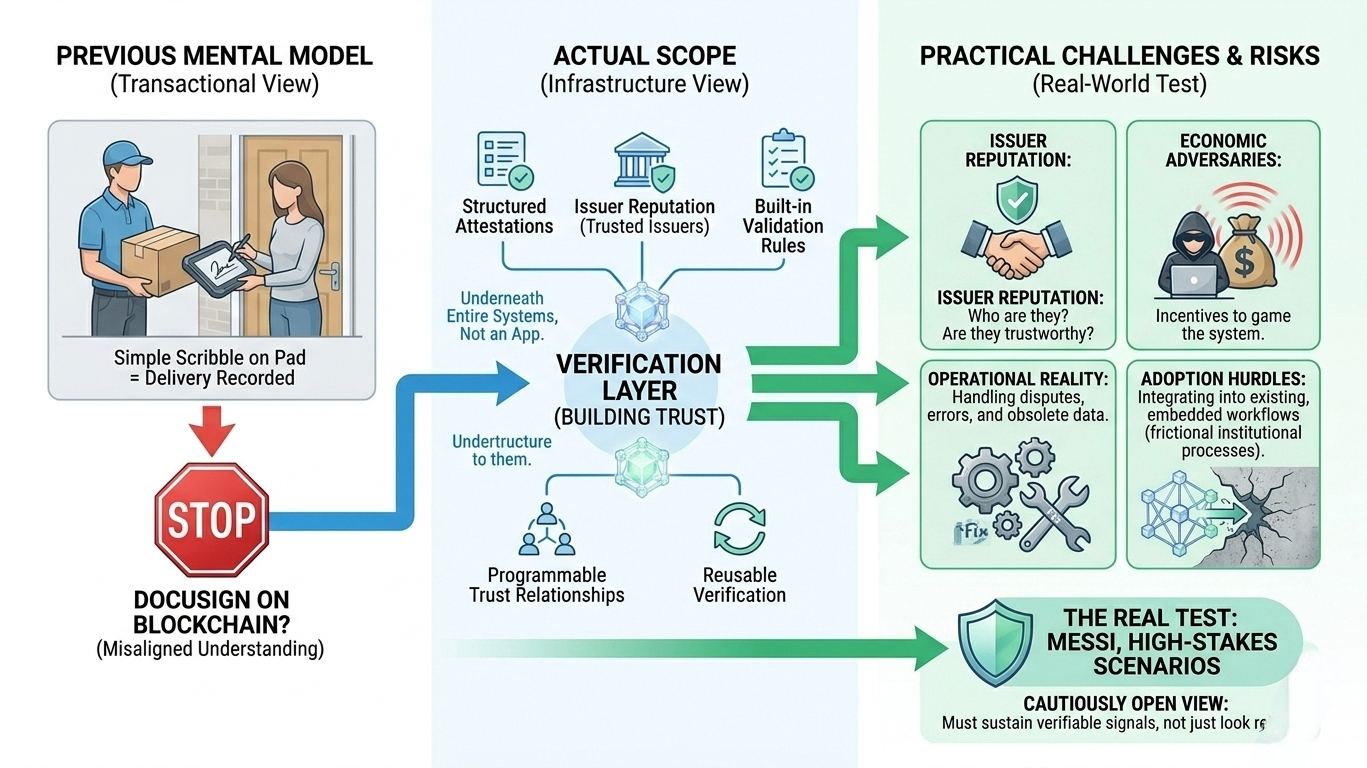
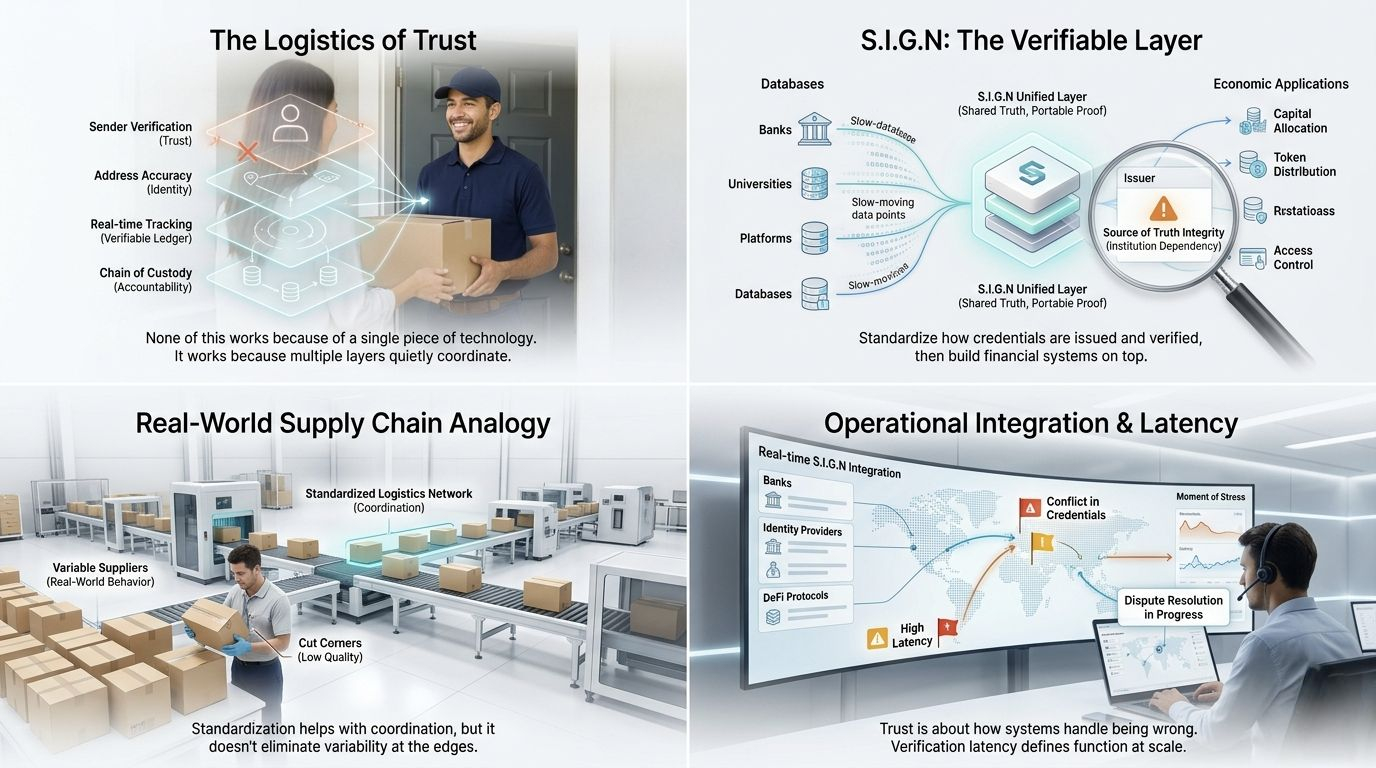
I used to think of digital signatures the way I think about signing for a package at the door. The courier hands over a device, I scribble something that vaguely resembles my name, and the system marks the delivery as complete. It’s simple, transactional, and mostly about recording that a moment happened. The real trust isn’t in the signature itself—it’s in the logistics network behind it, the tracking system, the reputation of the courier, and the expectation that if something goes wrong, there’s a process to resolve it.
That’s roughly the mental model I had when I first came across Sign. I assumed it was just a blockchain version of something like DocuSign—a tool to formalize agreements, make them tamper-resistant, and move on. A better signature layer, maybe more transparent, maybe more portable, but still fundamentally a tool for marking consent or approval.
But the more I’ve looked into it, the less that framing holds up.
What Sign is trying to do feels less like digitizing signatures and more like building a verification layer that sits underneath entire systems. It’s closer to infrastructure than to an app. Instead of asking “who signed this document,” it asks “what can be trusted about this entity, and how do we prove it in a way that others can reuse?” That shift sounds subtle, but it changes the scope entirely. Now you’re not just recording actions—you’re shaping how trust itself is constructed and transferred across contexts.
That’s where the complexity starts to surface.
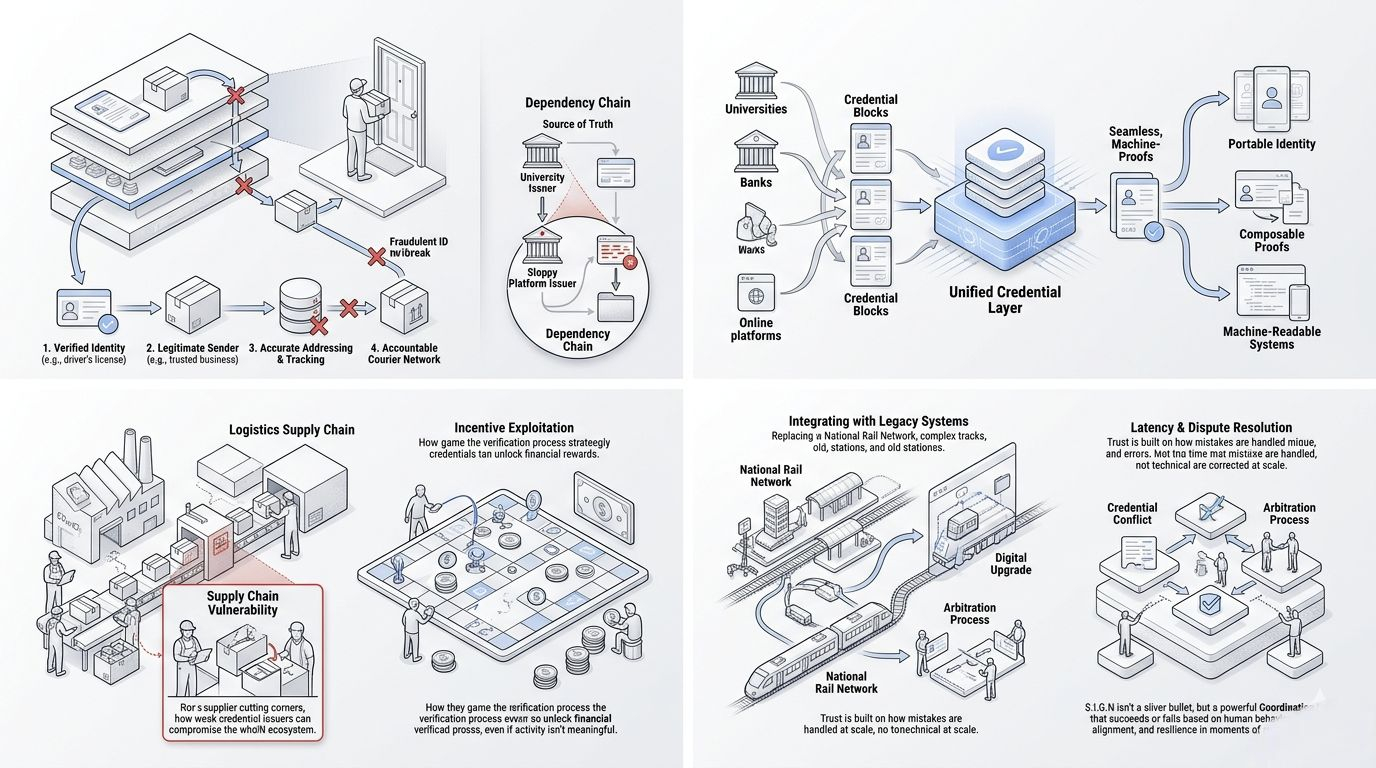
In real-world systems, trust is rarely a single step. In logistics, for example, a delivered package depends on coordinated checkpoints: scanning, routing, custody transfers, and exception handling. Each step has incentives, failure modes, and verification mechanisms. If one part is weak, the whole system becomes unreliable. The same applies here. A credential is only as strong as the issuer behind it, the process used to verify it, and the incentives that govern both.
This raises a practical question: who are these issuers, and why should anyone trust them? It’s easy to create a system where credentials exist; it’s much harder to ensure those credentials actually mean something under pressure. If value starts to flow through these attestations—access to capital, identity verification, eligibility—then the incentive to game them increases. At that point, the system isn’t just technical; it becomes economic and adversarial.

Another layer of difficulty is operational. Real systems don’t just work in ideal conditions; they have to handle disputes, delays, and edge cases. What happens when a credential is wrong? Or outdated? Or issued based on incomplete information? Traditional institutions have slow, sometimes messy processes for resolving these issues, but they exist. A blockchain-based system has to replicate that reliability without relying on centralized authority, which is easier said than done.
There’s also the question of adoption. Infrastructure only matters if people actually use it. And usage doesn’t come from theoretical elegance—it comes from integration into workflows that already exist. Businesses don’t adopt new systems because they’re interesting; they adopt them because they reduce cost, risk, or friction in a measurable way. If Sign is positioning itself as a foundational layer, it has to compete not just with other blockchain projects, but with entrenched institutional processes that, while imperfect, are deeply embedded.

What I find interesting is that Sign seems to acknowledge some of these challenges through built-in constraints—things like verification rules, issuer checks, and structured attestations. These aren’t just features; they’re attempts to shape behavior in advance. But rules alone don’t guarantee outcomes. In many cases, they create new trade-offs. Tight controls can improve reliability but reduce flexibility. Loose controls can increase adoption but weaken trust. Balancing those forces is an ongoing process, not a one-time design decision.
So the more I think about it, the less I see Sign as a “blockchain DocuSign” and the more I see it as an attempt to formalize trust relationships in a programmable way. That’s a much bigger ambition, and it comes with a different set of risks. It’s not just about whether the technology works—it’s about whether the surrounding ecosystem can sustain meaningful, verifiable signals without collapsing under incentives to exploit them.
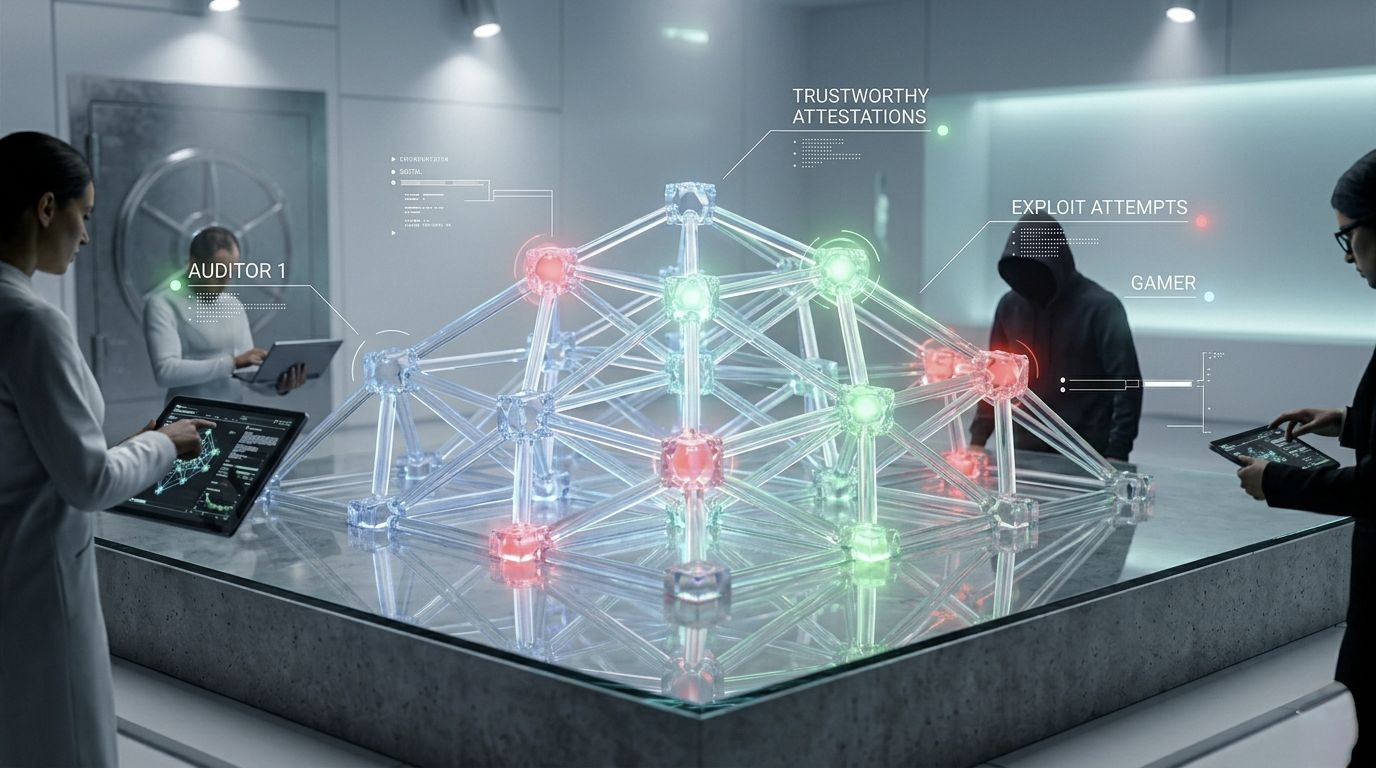
My view, at least for now, is cautiously open. I don’t think the initial comparison to DocuSign does it justice, but I also don’t think the broader vision is proven yet. The real test won’t be in clean demos or early integrations—it will be in messy, high-stakes scenarios where incentives are misaligned and the system still has to hold up. If it can do that, then it’s something closer to infrastructure. If not, it risks becoming just another layer that looks reliable until it’s actually used.
If Sign can survive that pressure, it won’t just be useful—it will become invisible infrastructure.
@SignOfficial #SignDigitalSovereignInfra $SIGN