When I hear “security innovations” in a Layer-1 pitch, my first instinct isn’t confidence — it’s caution. Not because security isn’t improving, but because the industry has trained users to equate more mechanisms with more safety, when in reality most breaches happen at the seams between systems, not inside the cryptography itself. The uncomfortable truth is that a chain can be mathematically sound and still feel unsafe in practice.
That’s why the interesting question isn’t whether Fogo adds new safeguards. It’s where responsibility for safety is being repositioned across the stack.
In the old model, security is treated as the user’s burden. You manage private keys, double-check addresses, interpret wallet prompts, and hope the contract you’re signing hasn’t buried a malicious permission. If something goes wrong, the post-mortem usually concludes that the user “should have verified.” This framing protects protocols but leaves people navigating a threat landscape they’re not equipped to understand. Security becomes a ritual rather than a property of the system.
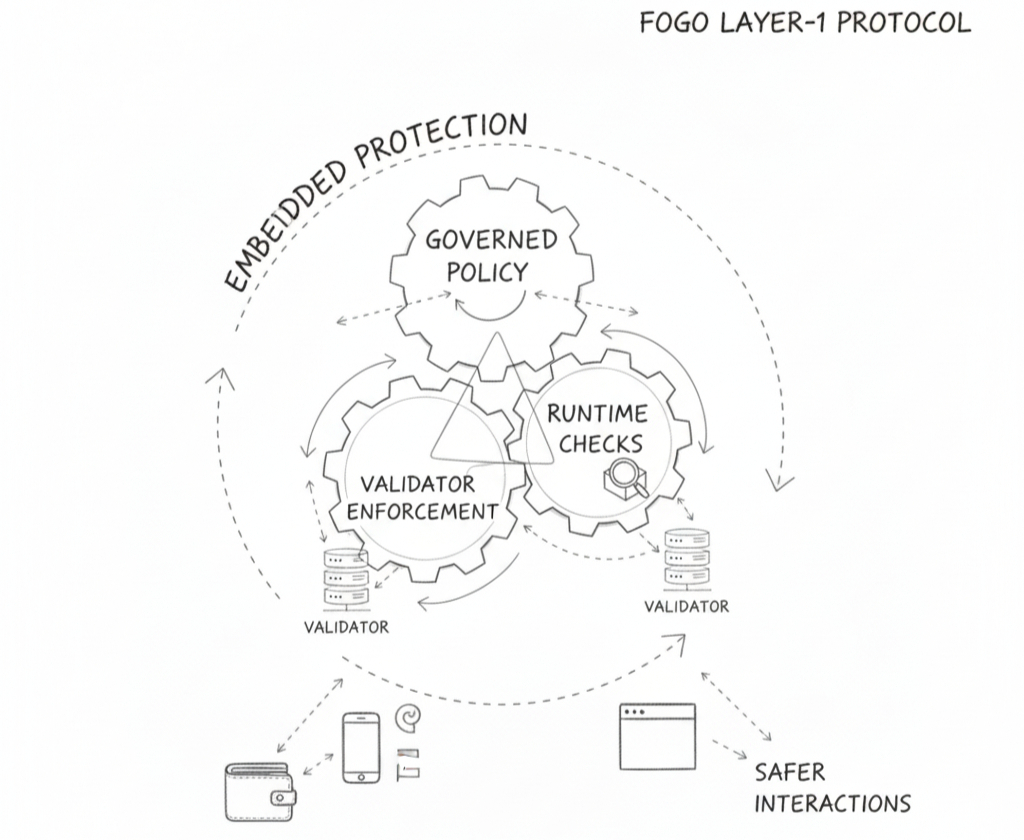
Fogo’s approach signals a shift away from ritual toward embedded protection. By designing the protocol around predictable execution, constrained permissions, and clearer transaction intent, the chain reduces the number of ambiguous states where users can be misled. That doesn’t eliminate risk, but it narrows the attack surface from “anything you sign could be dangerous” to “actions behave within defined boundaries.”
Of course, constraints don’t appear by magic. They’re enforced through execution rules validator coordination and runtime check that determine what a transaction is allowed to do before it reaches finality. Deterministic execution paths matter here. When outcomes are predictable and state transitions are tightly scoped, it becomes far harder for malicious contract to exploit undefined behavior or edge case ordering.
But the deeper shift isn’t technical — it’s architectural. When a protocol enforces clearer intent and bounded permissions, it moves part of the security model from the wallet into the network itself. Instead of every wallet vendor inventing its own warning heuristics, the chain establishes guardrails that all participants inherit. This reduces fragmentation in how risk is presented and interpreted.
That’s where the market structure begins to change. In fragmented ecosystems, security is uneven: sophisticated users rely on hardware wallets and simulation tools, while everyone else relies on luck. With protocol level safeguards, safety becomes more uniform. Infrastructure providers wallet developers and application teams can build on shared assumptions about execution behavior rather than patching around inconsistencies.
Uniformity, however comes with tradeoffs. The more the protocol standardizes safe behavior, the more it defines what “normal” looks like. This can concentrate influence over which transaction patterns are considered acceptable and which are flagged, delayed, or rejected. Security policy becomes part of governance, whether explicit or implicit.
Failure modes evolve accordingly. In loosely defined systems exploits often arise from unpredictable interactions. In tightly constrained systems, risk shifts toward policy errors and coordination failures. A validator misconfiguration, an overly restrictive rule or delayed propagation of security parameters can halt legitimate activity just as effectively as an attack. Users don’t see the nuance — they experience a transaction that should work but doesn’t.
This doesn’t mean tighter security is a mistake. In many ways, it’s overdue. But it does mean trust migrates upward. Users are no longer trusting only cryptography; they’re trusting that validators enforce rules consistently, that runtime checks are correctly specified, and that governance processes adjust safeguards without introducing instability. The promise shifts from “don’t make mistakes” to “the system won’t let small mistakes become catastrophic.”
There’s another subtle consequence: smoother, safer interactions encourage longer session lifetimes and fewer confirmation prompts. While this reduces phishing exposure and signature fatigue, it also increases the importance of session boundaries and delegated permissions. If authority persists longer, the cost of a compromised session rises. Security becomes less about single clicks and more about lifecycle management.
From a product perspective, this changes accountability. Applications built on Fogo inherit a more opinionated security baseline. They can no longer blame ambiguous protocol behavior for unsafe outcomes. If users are misled, it’s likely a front-end design failure, a permission request that overreaches, or inadequate disclosure of what an action entails. Security becomes part of product design, not just protocol design.
That, in turn, creates a new competitive axis. Apps won’t just differentiate on features; they’ll differentiate on how safely those features are delivered. How clearly are permissions scoped? How often do transactions behave exactly as previewed? How resilient is the experience under congestion or validator churn? In a system with stronger defaults, deviations become more visible — and less forgivable.
The strategic implication is that security is evolving from a personal responsibility into shared infrastructure. Specialists — validators, runtime engineers, wallet providers — increasingly define the guardrails within which everyone else operates. The long-term value of this model depends on whether those guardrails remain transparent, adaptable, and resilient under stress rather than rigid or opaque.
Because in calm conditions, almost any security model appears sufficient. It’s during volatility, rapid upgrades, and adversarial pressure that the true design reveals itself. Do safeguards fail open or fail safe? Do policies adapt quickly without fragmenting the network? Do users remain protected without being locked out of legitimate activity?
So the real question isn’t whether Fogo introduces better security mechanisms. It’s who defines the boundaries of safe behavior, how those boundaries are enforced across the validator set, and what happens when the system is forced to choose between usability and protection under imperfect conditions.