The room feels too clean for a problem this messy. One person. One chair that squeaks when you shift your weight. A dashboard on the main screen that the team jokes about in daylight and secretly depends on at night. You keep telling yourself the numbers are fine, and then your eyes land on the same place again. A small mismatch. Not dramatic. Not a siren. Just enough to turn your stomach into a tight knot that won’t let you sleep.
You rub your face, scroll back, scroll forward. You want it to be rounding. You want it to be a slow indexer. You want it to be anything that comes with an easy sentence. Because easy sentences mean you don’t have to wake anyone up. Easy sentences mean you don’t have to write the kind of report that ends up living forever in a folder titled “Lessons.” But the mismatch keeps sitting there like a coin balanced on its edge. It shouldn’t be possible, and yet it is.
This is the moment where all the slogans stop being useful. They work when money is still just a chart, when risk is still abstract, when people are still impressed by the word “decentralized.” But the adult world shows up quietly. Payroll. Contracts. Clients who aren’t here for ideology. Clients who have their own obligations and deadlines and lawyers. You can’t hand them a slogan. You have to hand them a record.
There’s a tab labeled “public view.” You click it out of habit, like touching a bruise to see if it still hurts. The public view looks calm. It always does. Public feeds do that—they tell a story that feels complete because it’s visible. But visibility is not proof. “Public” isn’t the same as “provable.” Public is broadcast. Provable is when you can show what matters in a way that survives doubt, without forcing you to expose everything else that has nothing to do with the question.
And doubt is not an attitude. It’s an occupation. Auditors are paid to doubt you. Regulators are required to doubt you. Clients learn to doubt you the first time something doesn’t reconcile on their side. If your system can’t answer doubt with evidence, someone else will answer it for you, and they won’t be gentle.
This is where privacy stops being a preference and becomes a duty. It’s easy to talk about privacy like it’s a luxury until you’re holding real client data in your hands. Until you remember there are laws, contracts, NDAs, competitive positioning, market conduct rules, and plain human dignity. You don’t get to treat all details like they belong to the public just because you can. You are responsible for what your transparency exposes.
The sealed folder metaphor comes back because it sounds like something from an old office, but it fits. In an audit room, you don’t dump every internal detail onto the table and call it integrity. You bring what is relevant. You keep the rest contained. The folder is sealed not because it’s shameful, but because it’s sensitive. You can open it—just not in the hallway, not for everyone, not without record and purpose. Authorized parties, under process: auditors, regulators, compliance. Sometimes the client, when it’s their right. Sometimes a court. The point isn’t to hide. The point is to disclose correctly.
Selective disclosure is how you stay honest without being reckless.
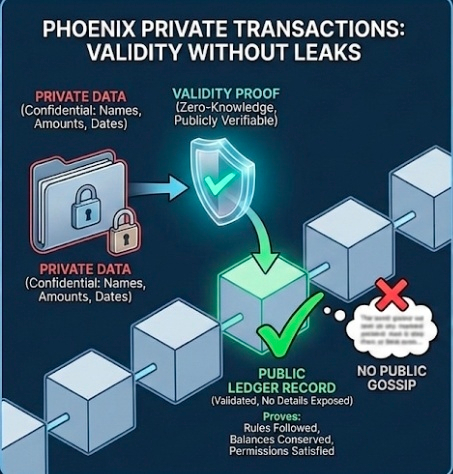
That’s why Phoenix private transactions matter in a very practical way. Not because “privacy is cool,” but because confidentiality needs enforcement. You want the chain to be able to say, with certainty, “this is valid,” without saying, “and here are the private details that will get someone hurt.” Validity proofs without leaking the contents. Rules were followed. Balances were conserved. Permissions were satisfied. The system can prove those things without turning the transaction into public gossip.
Because public gossip has consequences.
If a client’s positioning becomes visible, you don’t just embarrass them. You give competitors and opportunists a map. If salary payments become patterns, you expose people who didn’t consent to being part of a public dataset. If trading intent becomes readable before settlement, you invite copying, front-running, accusations, and a whole set of market conduct problems that show up as real investigations with real names on the paperwork. If every treasury move becomes a signal, you turn routine operations into something the market trades against. That’s not “transparency.” That’s harm, dressed up as virtue.
You go back to the discrepancy. You do what you always do when you’re scared and trying not to show it: you get specific. You pull logs. You compare execution receipts against settlement confirmations. You check time windows. You check for out-of-order messages. You look for the boring culprit—some delay, some retry, some seam between layers that was never meant to be exciting.
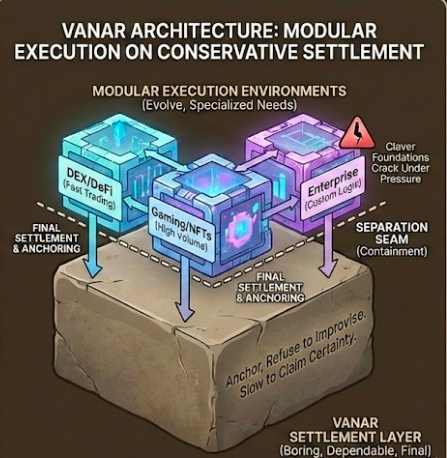
This is where Vanar’s architecture feels less like a diagram and more like a decision someone made for nights exactly like this. Modular execution environments on top of a conservative settlement layer. Let execution move. Let it evolve. Let it handle specialized needs. But keep the settlement layer boring. Dependable. Slow to claim certainty. The foundation should not be clever. Clever foundations crack under pressure. Settlement should finalize, anchor, and refuse to improvise.
Separation is containment. Containment is survival.
But separation also creates seams. And seams are where people make their most expensive mistakes, especially when they’re tired. Cross-chain readiness is basically learning to live with seams without letting them tear. Bridges and migrations aren’t “just infrastructure.” They’re coordination under risk. Multiple representations of the same asset living in different ecosystems. ERC-20 and BEP-20 representations that people already use because that’s where the tools and habits are. Then a migration to native. New assumptions. New address patterns. New ways for a single human slip to become a chain-level mess.
Key management sits in the middle of it all like a quiet threat. Most incidents don’t start with a genius attacker. They start with an ordinary person doing an ordinary thing slightly wrong. An approval made too quickly. A wrong contract address pinned. A signer who goes offline without a clean backup plan. A checklist that was “basically done.” This is the part people don’t like to say out loud: trust doesn’t degrade politely. It snaps. It breaks in one clean moment, and then everyone’s asking what controls existed, what permissions were in place, what could be revoked, what could be recovered, and whether you can prove it.
That’s also why EVM compatibility matters in the most unromantic way possible. Fewer surprises. Familiar tooling. Familiar assumptions. Less accidental complexity. Not a promise that nothing will go wrong—just fewer ways for “I thought it worked like this” to become an outage.
And keeping $VANRY central, in this adult framing, isn’t about talking it up. It’s about placing responsibility somewhere real. If staking is treated as a bond, it becomes a kind of accountability deposit. You’re not just “involved.” You’re on the hook. You’ve got something at stake in the plain meaning of the word. That matters when systems are under stress, because you need participants who don’t vanish when it stops being fun.
After a while, the discrepancy finally makes sense. It’s not a monster. It’s a delayed settlement finalization after a cross-environment handoff, plus a monitoring state that makes “pending” look like “done” if you glance too quickly. Two clocks telling the truth at different speeds. The gap is explainable, but that doesn’t make it acceptable. Explainable problems become repeatable problems if you leave them alone.
So you write the report the way you wish other people wrote reports: clear, plain, and honest about the human parts. You recommend tighter reconciliation gates. Clearer state labels. Alerts that don’t just scream, but point. You add process steps that will annoy someone later, and you accept that annoyance is cheaper than client harm. You note the sharp edges: bridges, migrations, key custody, fatigue, missed checklists. You spell out what can be revoked and how recovery works. You make the controls feel real.
In the end, the work always collapses into the same two rooms. The audit room, where someone will ask for proof and the sealed folder will be opened under rules, not vibes. And the other room, quieter and heavier, where someone signs under risk—knowing that permissions, controls, revocation, recovery, and compliance obligations are not optional. They’re what separates a system people can rely on from a system people only want to believe in.
It’s almost when you finally lean back. The discrepancy is still there, but now it has a name, a cause, and a plan. That doesn’t feel like victory. It feels like adulthood.

