I had a conversation with someone who said, "Don't worry, this is private." But then they showed me a block explorer, and I was able to figure out the pattern in just a few seconds. I wasn't able to see the actual amounts or messages, but I could see the trail, the path that the transactions took. And that's a problem, because the trail can be just as revealing as the actual information. Midnight Network is one of the few systems that understands this, and it's designed to protect against that kind of threat. It's not just about keeping the messages or amounts secret, it's about keeping the entire trail hidden.
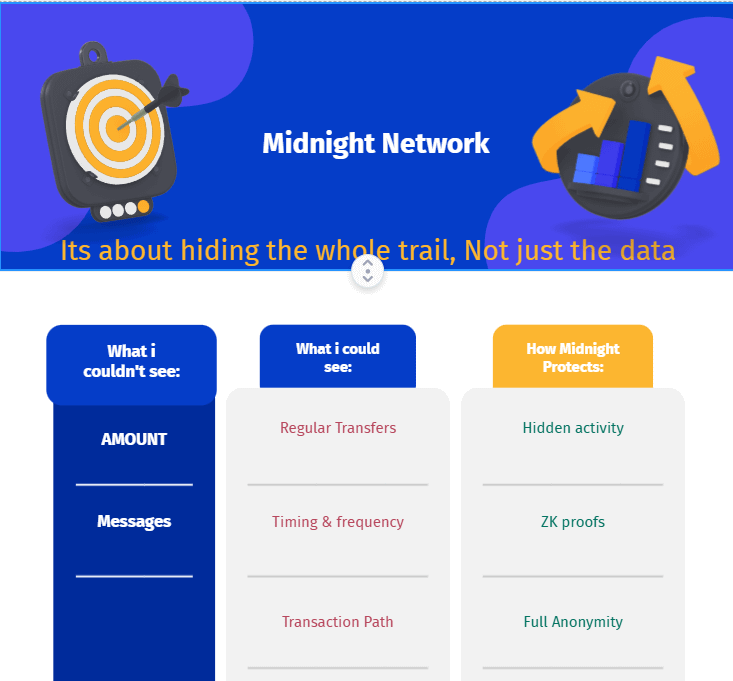
When people think of a "privacy chain", they usually assume it's all about keeping transaction amounts and details secret. But the truth is, there's a bigger issue at play. Even if you can't see the actual transactions, the metadata can still give away a lot of information - like who's involved, when it happened, and how often it's happening. That's why Midnight Network stands out to me. Instead of treating this as a minor problem, they're tackling it head-on. Their approach is to protect not just the data, but also the metadata, and they see privacy as a way to control how your data is used, rather than just keeping it completely secret.
Even with encryption, patterns can still be detected. When the same parties interact repeatedly, it can create noticeable patterns, like bursts of activity at certain times of day or frequent contract calls. Additionally, round-number payments and address clustering can also give away sensitive information. This can essentially reveal a map of "who interacted with whom" - a major concern for businesses. It's not just the leak of data itself that's the problem, but also the leak of relationships between parties, which can be just as damaging.
The approach of Midnight Network is basically: shield what creates the graph, then selectively reveal only what is required. ZK proofs let an app prove compliance or correctness without exposing the underlying sensitive details. The key is that disclosure becomes a policy decision. You can keep interactions shielded while still enabling controlled, programmatic disclosure when needed.
Imagine a mid-size supplier network paying 12 contractors weekly. That is 48 payments per month. Even if amounts are hidden, a public chain still reveals the recurring cadence, the counterparties, and the peaks around payroll days. A competitor does not need your invoice data. They just need the metadata to infer who your suppliers are and when cash stress hits.
So, what if we turn things around? Let's say it's midnight Network and the app is working its magic. It can keep the whole interaction private, like a shield, and still give us a proof that everything is okay. This proof would be like a statement that says, "Hey, all 48 payments were authorized and followed the rules, no problems here." And the best part is, it can do all this without sharing the whole interaction with everyone, just keeping it between the people who need to know.
Compared side by side, a public L1 is transparent by default, so metadata becomes an analytics buffet, while a classic privacy coin can hide a lot but often feels like all-or-nothing secrecy, which creates friction for regulated or enterprise workflows. Midnight tries to sit in the middle by making privacy flexible and verifiable, because disclosure can be controlled through programming instead of forced into full transparency or full blackout.
I think the next “killer apps” won’t be defined by who has the best encryption. They’ll be defined by who can reduce metadata leakage without killing auditability. Midnight Network’s bet is that programmable data protection becomes infrastructure, not a niche feature.
It isn’t just the details about your data that are out in the open, but the way your company works is also out in the open.
The question is, will people using online platforms continue to accept that their personal information is visible, just because they're using a public system, or will developers start making sure that users' data is protected from the beginning, as a standard feature for any serious online application?

@MidnightNetwork #night $NIGHT
