honestly? I've been thinking about the zero knowledge proof layer in Midnight for weeks now and I don't think people fully understand what it means for application developers trying to build on it 😂
let me start with the thing that actually surprised me.
most people when they hear zero knowledge proofs think about privacy in the simple sense. you can prove something is true without revealing the underlying data. that's the headline. that's what gets written about in crypto media. and it's real — that capability is genuinely there and genuinely valuable.
but what nobody talks about is what it actually costs to generate those proofs at the application level and what that cost means for the developer experience on Midnight specifically.
ZK proof generation is computationally expensive. not expensive in a theoretical way. expensive in a this-affects-your-application-architecture way. every shielded transaction a user makes requires a proof to be generated somewhere. that somewhere is either happening on the user's device or it's being offloaded to a prover service that someone is running and someone is paying for.
and here's where it gets interesting.
if the proof generation happens on the user's device — which is the pure decentralized version of this — then you're depending on that device having enough computational capacity to generate the proof in a reasonable amount of time. on a modern laptop that might be fine. on a mid-range smartphone in 2024 that might be a three second wait. on an older device in an emerging market where Midnight's privacy guarantees are arguably most needed — that wait gets longer. potentially much longer.
user experience research is pretty unambiguous about wait times. three seconds feels long. five seconds feels broken. anything beyond that and a meaningful percentage of users abandon the interaction entirely.
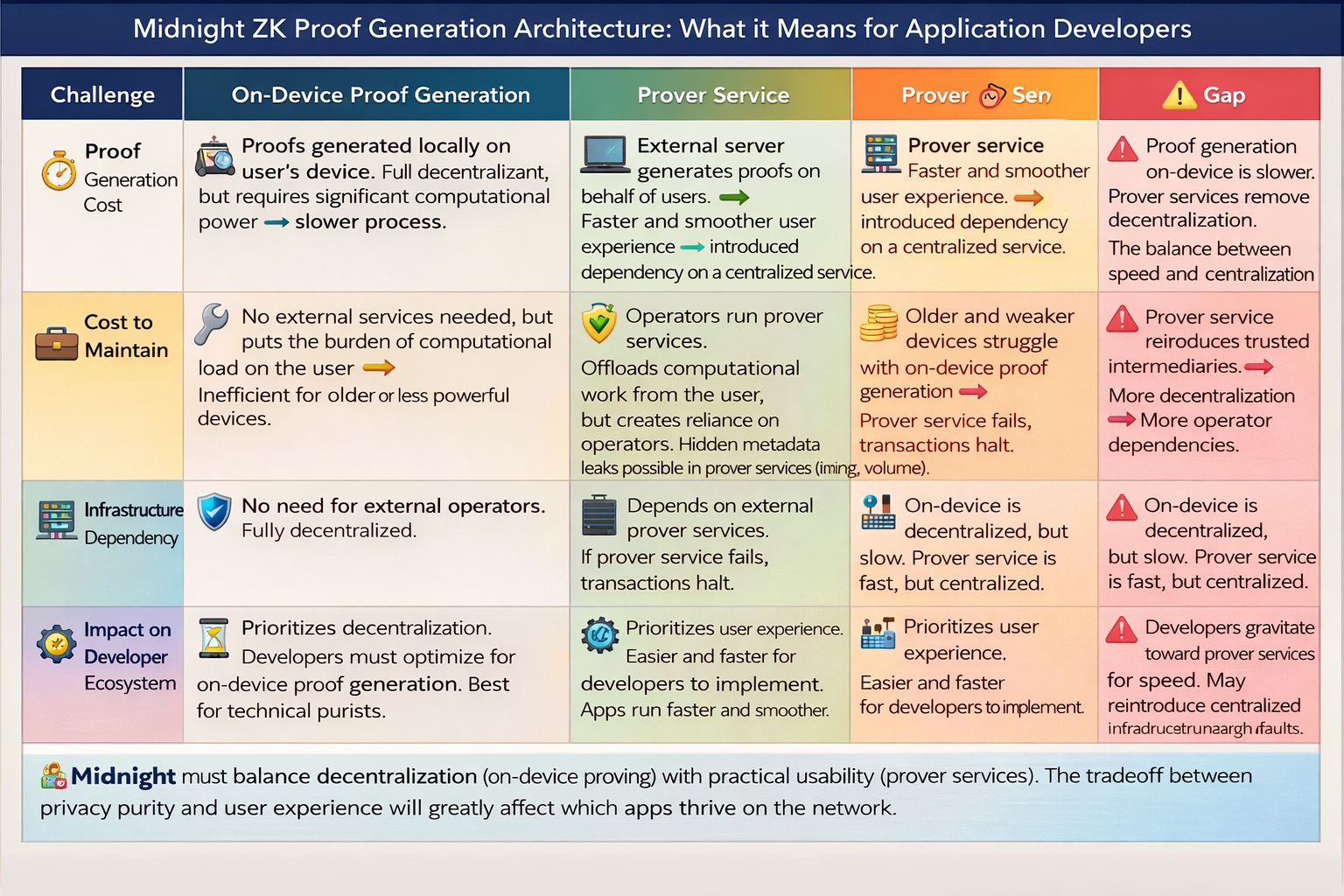
so the pure on-device proof generation model — the one that preserves the most decentralization — creates a user experience that degrades in exactly the populations where the privacy application is most valuable.
the alternative is a prover service. an external server that handles proof generation on behalf of users, returns the proof to the client, and lets the transaction proceed without taxing the user's device.
that works. it actually works really well from a pure user experience perspective. proof generation gets fast. the experience feels smooth. the app feels like a normal app.
but now you've reintroduced a server into a system that was supposed to remove the need for trusted intermediaries.
the prover service knows what proofs it's generating. it knows the timing. it knows the volume. it knows which applications are generating which kinds of transactions. it doesn't know the contents of the shielded data — the ZK guarantee holds at the cryptographic level. but metadata is real and metadata leaks information in ways that pure cryptographic analysis sometimes undersells.
and there's the dependency problem again. if your application relies on a prover service and that prover service goes down, your users lose access. not to their funds necessarily — but to the ability to transact through your application. same category of single point of failure as the sponsee model just at a different layer of the stack.
what I find genuinely fascinating about this tension is that it's not unique to Midnight. it shows up in every ZK application stack that's tried to go beyond the purely technical demo phase into something real people use on real devices in real conditions.
the teams that have navigated it best are the ones that treated it as a product problem rather than purely a cryptography problem. they built progressive proving systems that try on-device first, fall back to a prover service when device capacity is insufficient, and give users visibility into which mode they're operating in.
that's a reasonable engineering answer. it's not perfect but it preserves user experience across device capability ranges while being honest about the tradeoffs.
what I don't know — and what I haven't seen clearly addressed in Midnight's documentation yet — is which direction the default is going to go for application developers building on the network.
because that default matters enormously.
most developers don't deeply interrogate the proof generation architecture of the platform they're building on. they use the SDK. they follow the documentation. they build toward whatever the default path is because optimizing the proof generation layer is not where they want to spend their time — they want to spend their time building the actual application.
if the default path leads toward prover services the network is going to end up with a lot of applications that have reintroduced centralized infrastructure through the back door without any of the developers fully realizing it happened.
if the default path leads toward on-device proving the network is going to end up with a lot of applications that feel slow on the devices most commonly used by the people who need privacy applications most.
neither default is obviously right. both defaults have real consequences that compound across every application built on the network.
and here's the thing that keeps bringing me back to this.
Midnight's entire value proposition rests on the idea that privacy can be practical. not just cryptographically sound in a whitepaper but actually usable by real people in real situations where privacy genuinely matters for their safety and autonomy.
the ZK proof generation architecture is one of the places where that value proposition either holds in practice or quietly collapses into a compromise that technically preserves the guarantees but functionally reintroduces the dependencies it was supposed to eliminate.
I'm not saying the team hasn't thought about this. I genuinely believe they have. the people building Midnight are not naive about the gap between ZK theory and ZK practice.
but I think the developer community building on top of Midnight needs to be asking these questions explicitly and early. not after the application ecosystem has grown up around a default that nobody examined carefully enough.
because the proof is in the proving. literally. 🤔