Zero-knowledge isn’t magic—it just feels like it at first. Once you break it down, it’s actually a very practical piece of technology solving a very real problem: how to prove something is true without exposing the details behind it.
Right now, data breaches are everywhere. Whether it’s individuals or companies, sensitive information keeps getting leaked. That’s where zero-knowledge (ZK) technology starts to make sense. Instead of handing over your data to prove something, you prove it without ever revealing the data itself.
Midnight is built around this idea. It gives developers tools to create applications where privacy isn’t an afterthought—it’s built in from the start. The goal is simple: let people interact, transact, and build without constantly risking their personal information, while still staying compliant with regulations.
At its core, zero-knowledge works through two roles: a prover and a verifier. The prover has some private information. The verifier needs confirmation that a statement about that information is true. Instead of sharing the data, the prover generates a proof—called a zero-knowledge proof (ZKP)—that convinces the verifier without exposing anything sensitive.
A simple way to think about it: imagine needing to prove you have a medical condition for insurance. Normally, you’d have to hand over your records. With ZK, you can prove the condition exists without revealing your full medical history. The insurer gets certainty, and you keep your privacy.
There are different types of ZK systems, but two of the most well-known are ZK-SNARKs and ZK-STARKs. Midnight uses ZK-SNARKs because they strike a strong balance between efficiency and security. They produce small proofs that are quick to verify, which makes them practical for real-world applications.
How do they actually work? In simple terms, the process starts with a setup phase where certain parameters and keys are created. Then, the problem you want to prove is translated into a kind of mathematical “circuit.” The prover uses their secret (called a witness) along with this circuit to generate a compact proof. Finally, the verifier checks that proof using the public parameters—without ever seeing the underlying data.
What makes this powerful is how many ways it can be used.
For data protection, it allows validation without exposure—your identity and information stay private. In payments and smart contracts, it enables confidential transactions while still enforcing rules. In voting, it can prove eligibility without revealing identity, reducing manipulation risks. For scalability, it helps reduce the amount of data stored and processed on-chain. And for interoperability, it allows different blockchains to interact securely without needing full transparency.
Midnight applies this through its own systems like Zswap and Kachina, which focus on secure, private transactions and smart contract execution. The idea is to make privacy usable not just theoretical.
In the end, zero-knowledge isn’t about hiding everything. It’s about sharing only what’s necessary .
@MidnightNetwork #night $NIGHT 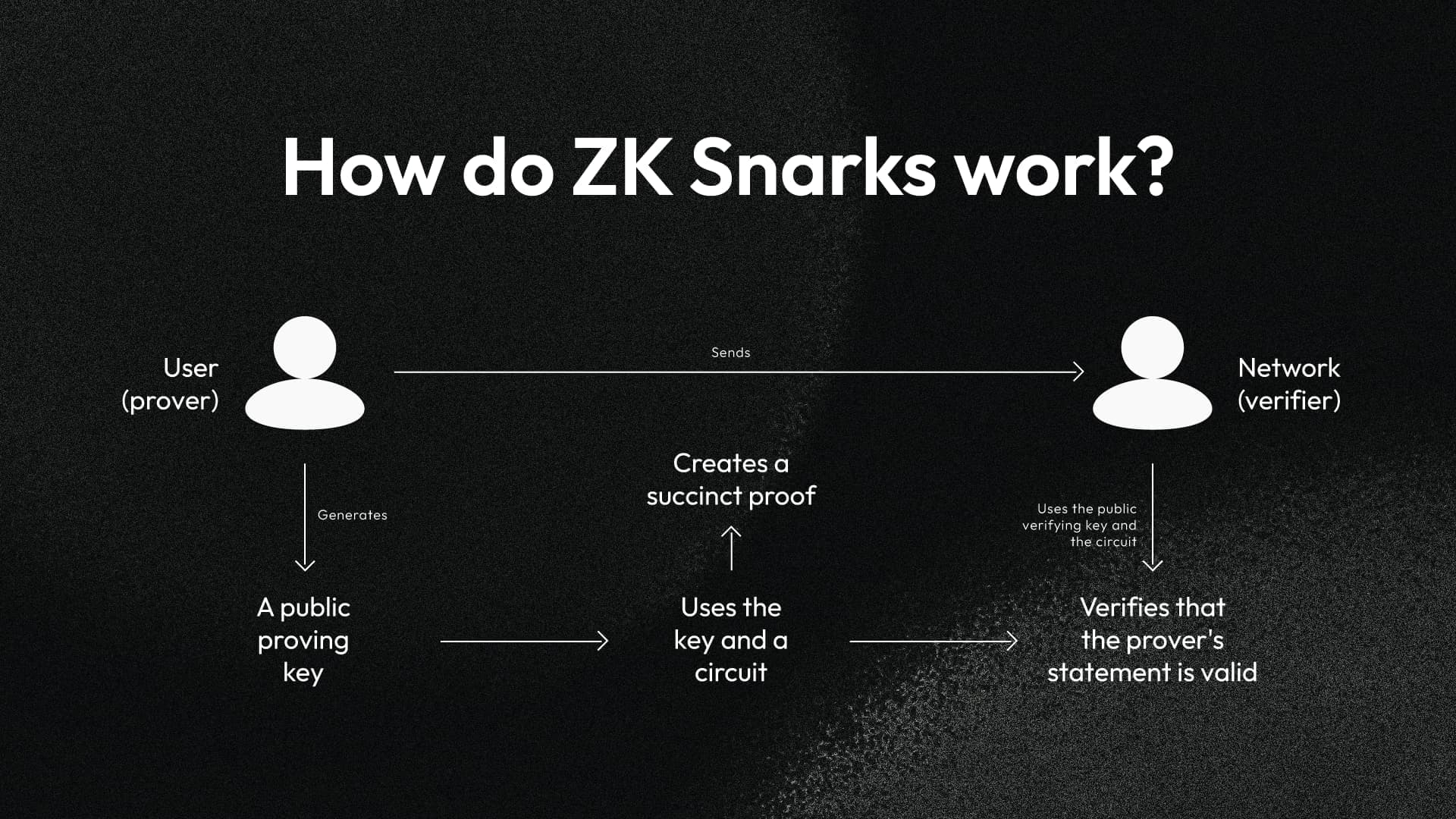 and nothing more.
and nothing more.