There was a time when “verification” in crypto meant something almost laughably simple. You signed a message with your wallet, maybe connected to a dApp, and that was enough. Ownership was visible. Identity didn’t matter. That worked until it didn’t.
What eventually became the Sign ecosystem didn’t emerge out of ambition as much as friction. Too many things that mattered in the real world degrees, contracts, salaries, eligibility had no clean way to exist on-chain without either exposing too much or requiring someone to manually check everything off-chain. The promise of decentralization kept running into the same wall: trust still had to be rebuilt, one spreadsheet, one email, one verification call at a time.
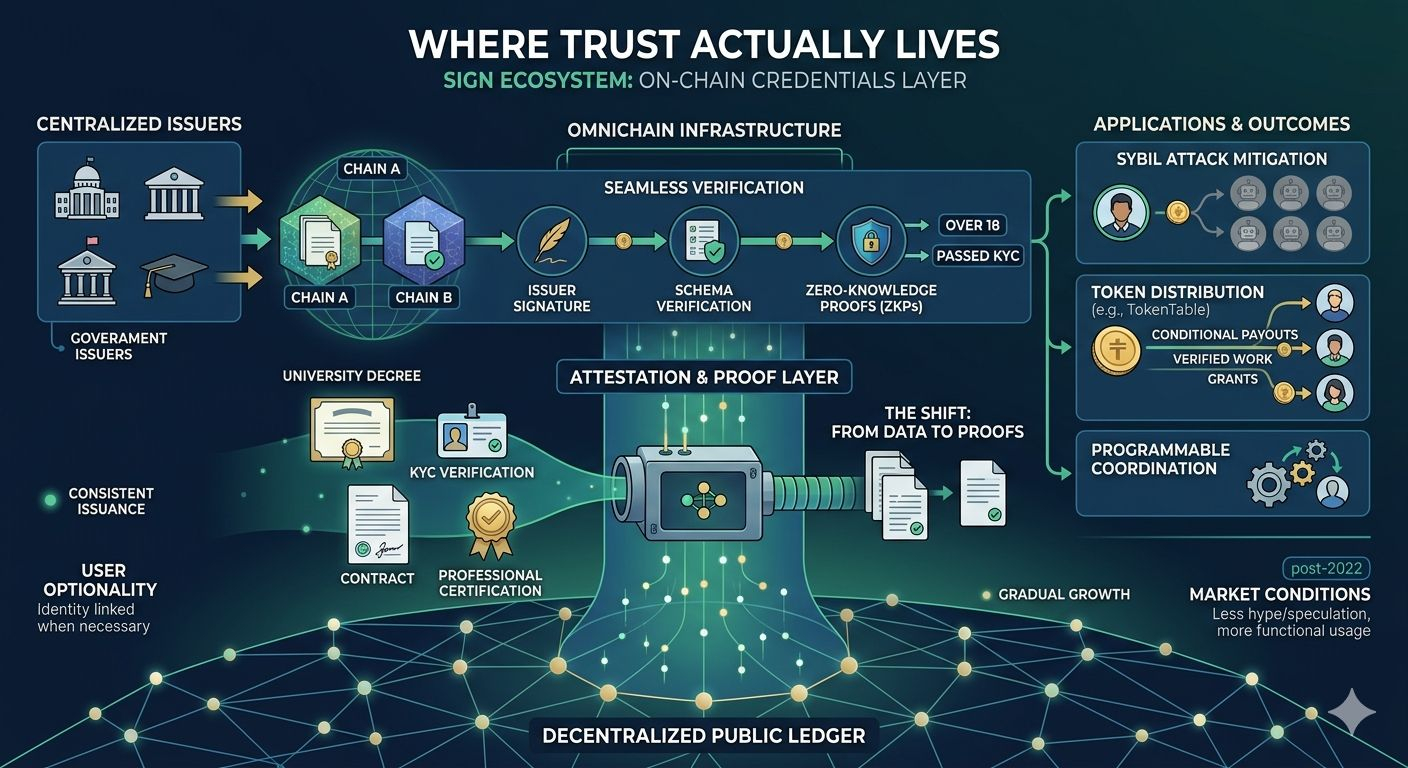
Early versions of credential systems tried to solve this by just putting documents on-chain. That failed quickly. It was expensive, messy, and in some cases outright dangerous from a privacy standpoint. No one wants their passport or medical history sitting permanently on a public ledger. What Sign Protocol and similar systems did differently was subtle but important. They stopped thinking about storing data, and started thinking about proving statements.
That shift from data to attestations sounds small, but it changes everything.
The first real moment where this idea gained attention wasn’t some polished launch. It was during the period when airdrops started getting abused at scale. Sybil attacks became a kind of sport. People weren’t just farming rewards they were industrializing it. Thousands of wallets, scripted interactions, entire ecosystems distorted by actors who had no real stake in anything they touched. Projects tried to fight back with increasingly complex heuristics, but it always felt reactive.
That’s when verifiable credentials started to look less like an experiment and more like a missing layer. If you could prove, in a cryptographic way, that a wallet belonged to a unique human, or to someone who had completed a specific action in the real world, you could change how value was distributed. Not perfectly, but meaningfully.
Still, theory is easy. The stress came when these systems had to operate under real conditions.
One of the earliest challenges was fragmentation. Different chains, different standards, different assumptions about identity. A credential issued in one environment was often useless in another. The idea of “omnichain” attestations sounded good, but implementing it meant dealing with inconsistent infrastructure and, more importantly, inconsistent trust assumptions.
What held up better than expected was the simplicity of the attestation model itself. An issuer signs a statement. That statement follows a schema. Anyone can verify the signature against a known public key. It’s not revolutionary cryptography. It’s just applied correctly. And because it’s simple, it’s portable.
The verification layer, especially when combined with zero-knowledge proofs, ended up being more than just a privacy feature. It became a kind of filter. Instead of exposing raw data, users could reveal only what was necessary for a specific interaction. Not their age, but the fact that they are over 18. Not their full identity, but the fact that they passed KYC with a recognized provider. This reduced friction in places where compliance and privacy usually clash.
But the real test wasn’t technical elegance. It was whether any of this translated into actual usage.
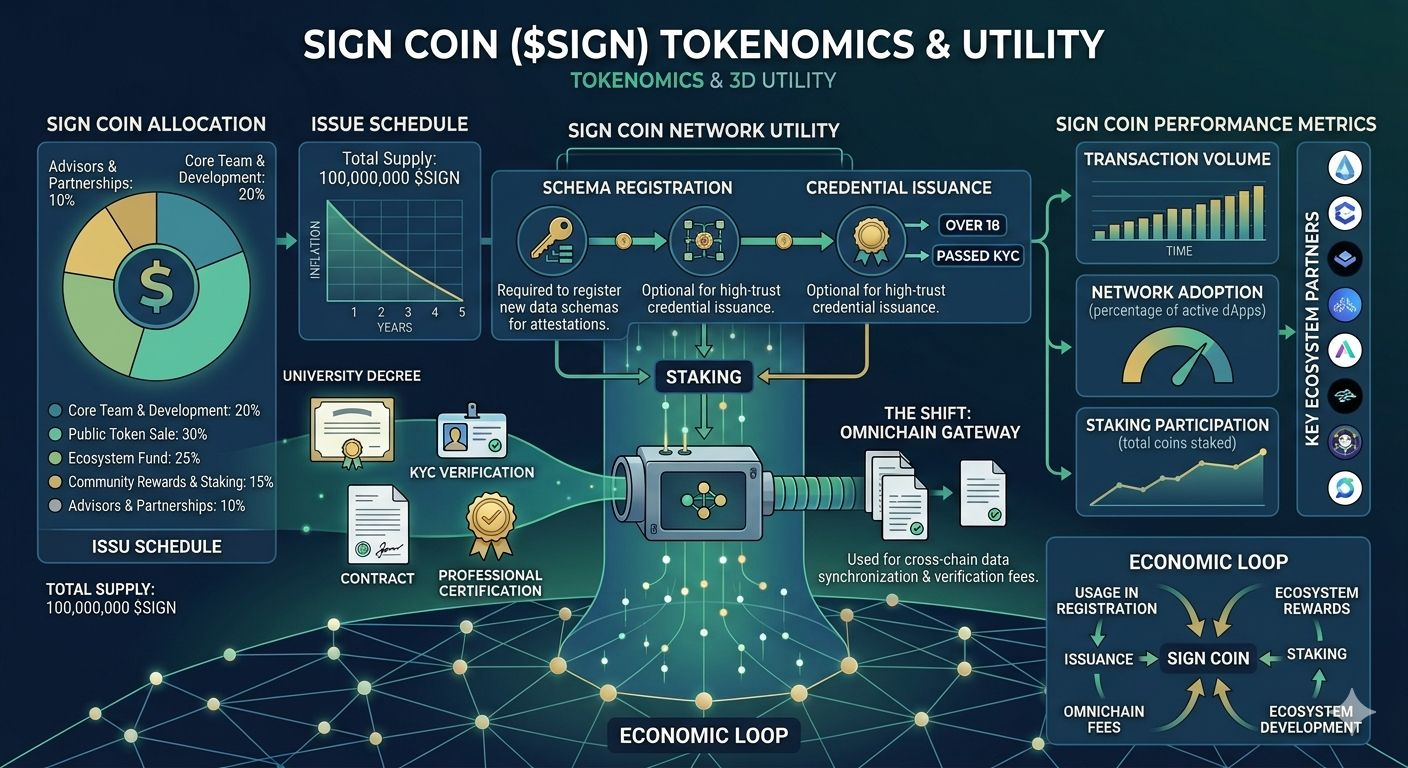
TokenTable, or similar distribution systems tied into this stack, became an interesting signal. At first, it looked like just another airdrop tool. But over time, the patterns shifted. Instead of broad, indiscriminate distributions, you started seeing more targeted flows payments tied to verified work, grants tied to verified participation, allocations that required some form of proof beyond wallet activity.
This is where the economic layer starts to matter. Tokens stop being just speculative assets and start behaving, at least partially, like conditional payouts. If a credential is verified and a condition is met, something happens. Funds move. Access is granted. Rights are exercised. It’s not fully autonomous, but it’s closer to programmable coordination than most earlier systems managed.
The identity layer, often the most controversial part, evolved more slowly. Linking real-world identity to a wallet has always been uncomfortable in crypto. There’s a reason anonymity was valued so highly in the first place. Systems like SignPass had to walk a narrow line. Too strict, and they feel like traditional KYC wrapped in new branding. Too loose, and they fail to provide meaningful guarantees.
What seems to have worked, at least in certain contexts, is optionality. Identity isn’t required everywhere. But where it is required—government programs, regulated finance, certain employment flows—it can be provided in a way that doesn’t fully expose the user. This doesn’t eliminate trust issues, but it localizes them.
Market conditions forced this ecosystem to mature faster than it probably would have otherwise. The post-2022 environment, with tighter liquidity and less tolerance for speculative excess, made it harder for purely narrative-driven projects to survive. Infrastructure had to justify itself through usage, not just potential.
In that environment, credential systems found a quieter kind of relevance. Not explosive growth, but steady integration. Governments experimenting with digital IDs. Financial institutions exploring tokenized assets that require verified participants. Platforms needing a way to distinguish between real users and automated behavior.
On-chain activity reflects this in a subtle way. You don’t see massive spikes that correlate with hype cycles. Instead, you see consistent issuance of attestations, gradual growth in verification calls, and token flows that align with specific events rather than broad speculation. It’s not the kind of data that attracts attention, but it’s the kind that suggests something is actually being used.
That said, skepticism is still warranted.
One unresolved issue is centralization at the edges. While the protocol layers may be decentralized, the entities issuing high-value attestations—governments, universities, large institutions—are inherently centralized. If they control the inputs, they indirectly shape the system. This isn’t necessarily a flaw, but it limits how “permissionless” the ecosystem can truly be.
Another concern is interoperability in practice versus theory. Omnichain capability exists, but real-world implementations often rely on bridges, wrappers, or intermediaries that introduce new risks. The ideal of seamless verification across environments is still, in many cases, aspirational.
There’s also the question of incentives. The token tied to this ecosystem doesn’t always have a clear, direct relationship with usage. In some cases, it functions more as a coordination or governance layer than a core economic driver. That can be fine, but it creates a gap between on-chain activity and token value that markets don’t always price accurately.
And then there’s user behavior, which rarely aligns with design assumptions. People reuse credentials in ways that weren’t anticipated. They cluster around certain issuers. They look for shortcuts. Any system that tries to formalize trust will eventually run into the messy reality of how humans actually behave.
Despite all of that, there’s something structurally interesting here that keeps it relevant.
It doesn’t try to replace existing institutions. It doesn’t assume a fully decentralized future where governments and corporations disappear. Instead, it creates a layer where their assertions can be translated into something programmable and verifiable. That’s a more modest goal, but also a more achievable one.
Over time, that kind of infrastructure tends to fade into the background. It stops being a “project” and starts being part of how things work. You don’t think about the protocol when you receive a payment tied to a verified task, or when your credentials are accepted across platforms without repeated checks. You just notice that something which used to be slow and uncertain now happens quickly and quietly.
Maybe that’s the real shift. Not that trust has been eliminated, but that it’s been compressed. Reduced to something smaller, more precise, and easier to move across systems.
And if that continues, the most important part of this entire stack won’t be the tokens, or even the protocols themselves. It will be the fact that, for the first time, proving something about yourself and acting on that proof doesn’t require starting from zero every single time.
@SignOfficial #SignDigitalSovereignInfra $SIGN
