@SignOfficial I think what makes Sign’s privacy model so interesting is that it avoids the usual all-or-nothing argument. It is not pushing for a world where everything is public in the name of trust, and it is not pretending everything should be hidden in the name of privacy either. What it offers instead feels narrower and more serious. It is private to the public and auditable to lawful authorities. In Sign’s own security material that means ordinary people should not be able to casually trace identities balances benefit flows or sensitive eligibility details while authorized oversight bodies can still verify that rules were followed and approvals existed and budgets matched results.
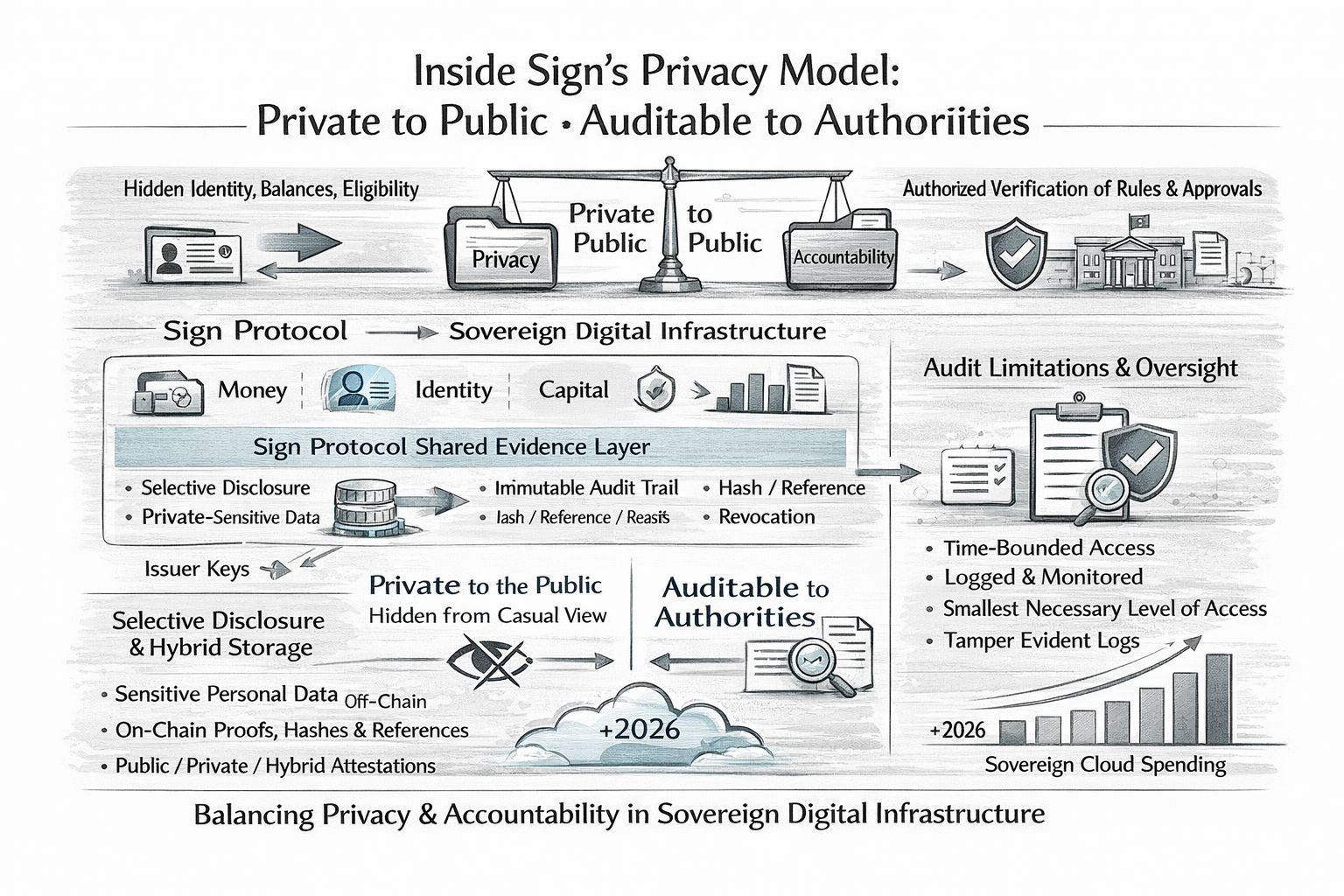
When I read that it feels less like a crypto slogan and more like an effort to design for real government pressure. Sign’s documentation presents S.I.G.N. as a sovereign digital infrastructure stack for money identity and capital with Sign Protocol working as the shared evidence layer. The protocol supports public private and hybrid attestations along with selective disclosure privacy preserving proofs and immutable audit references. In simple terms the system is trying to help institutions prove that something happened without pushing every sensitive detail into open view.
What makes the model stand out to me is its practical restraint. The docs say personal information should stay off chain by default while on chain records should mostly hold proofs hashes references revocation links and rule versions. That feels far more sensible than the older habit of treating blockchains like giant public filing cabinets. Sign also describes hybrid storage as the preferred path when open verification matters but payload privacy still has to be protected. To me that balance feels more mature than the all public reflex that shaped a lot of earlier web3 thinking.
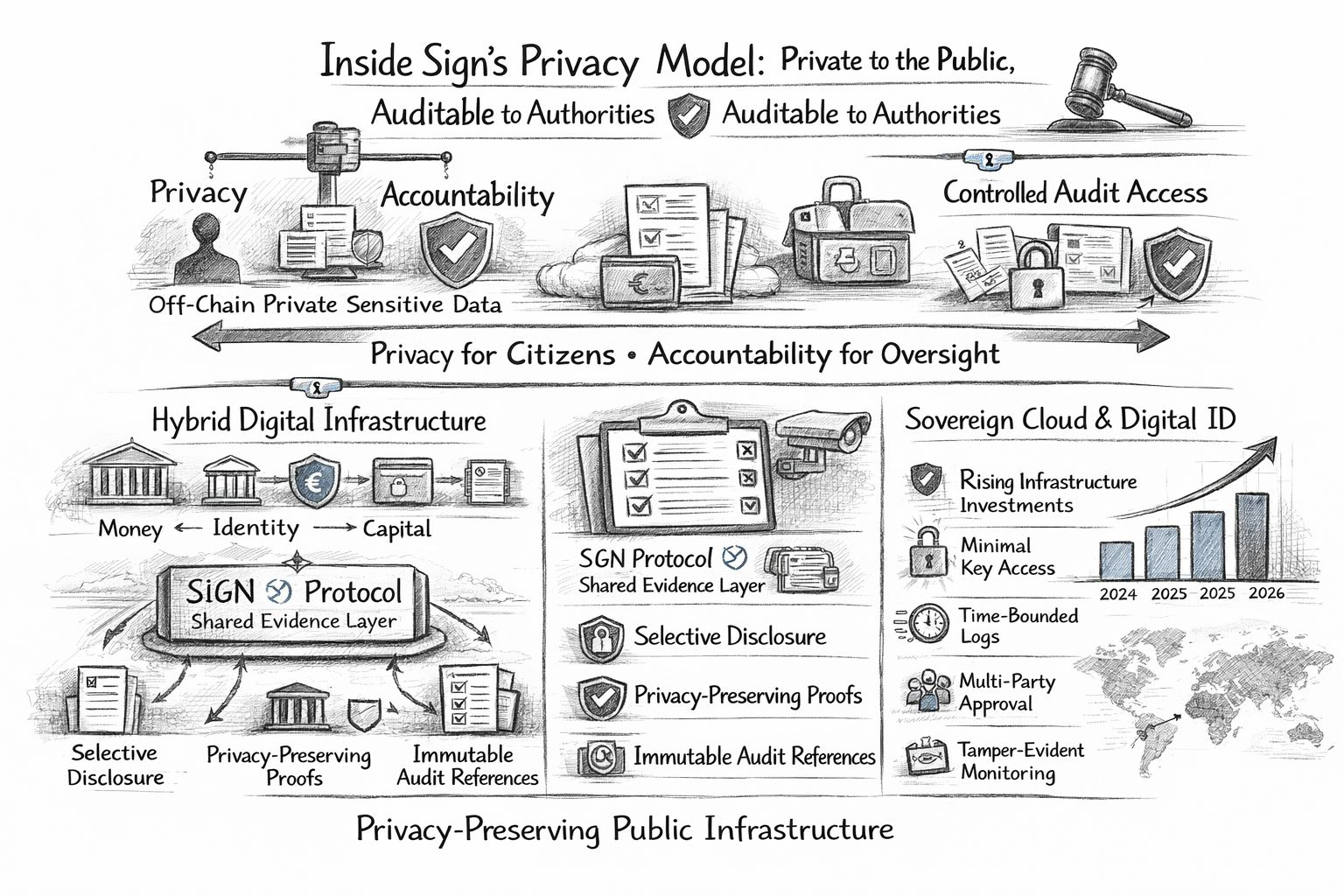
I also think the strongest part of the design is not the cryptography by itself but the way governance is built around it. Sign’s privacy material says audit access should be logged time bounded and limited to the smallest level of access needed and in some cases it should require approval from more than one party. It also separates issuer keys from operator keys and calls for tamper evident logs monitoring and tested recovery processes. That matters because privacy failures in public systems do not usually come from one dramatic breach alone. They often come from weak internal controls and poor oversight and vague lines of responsibility. A system is only as private as the people who are allowed to touch it.
Why is this getting attention now? I think the moment is bigger than Sign itself. We are in a period where governments and heavily regulated industries are becoming much more serious about where data is stored and who gets to access it. That is why the wider conversation around sovereign cloud has picked up so much speed in 2026. That wider shift helps explain why Sign is drawing attention now. It sits in a space where identity payments infrastructure and oversight are starting to merge into the same conversation and where privacy is no longer being treated as a side feature.
There is also real movement behind the theory. Sign’s recent material links the stack to government style use cases such as identity payment evidence regulatory approvals audits border control and voting. Reporting on Sierra Leone also points to a memorandum focused on national digital identity wallets and blockchain powered payment systems which suggests that this is moving beyond abstract product language and into actual state level experimentation. I would still be careful not to oversell the maturity of it. The architecture is getting clearer and the partnerships are visible but durable national scale proof is still something that has to be earned over time. My honest view is that Sign’s model is compelling because it accepts a hard truth. Public infrastructure needs privacy and accountability at the same time and neither one holds for long without the other. The real test will come when political pressure rises and audits expand and lawful access stops sounding theoretical and starts becoming a daily operating reality.
