The more I looked at SIGN’s design, the more one small detail kept pulling my attention back.
At first, the bridge felt like the least important part of the whole system. Just infrastructure. A route for moving value between two environments. CBDC to stablecoin. Stablecoin back to CBDC. Atomic swaps. Limits. Controls. It all sounded technical and straightforward, almost like background machinery.
That was how I read it the first time.
Then I noticed the line saying AML/CFT checks are applied to bridge transactions.
Once I saw that, I could not really look at the bridge the same way again.
Because that means it is not just there to move value from one side to the other. It is also the place where that movement gets examined, filtered, and approved. And the moment that becomes clear, the entire architecture starts to feel different.
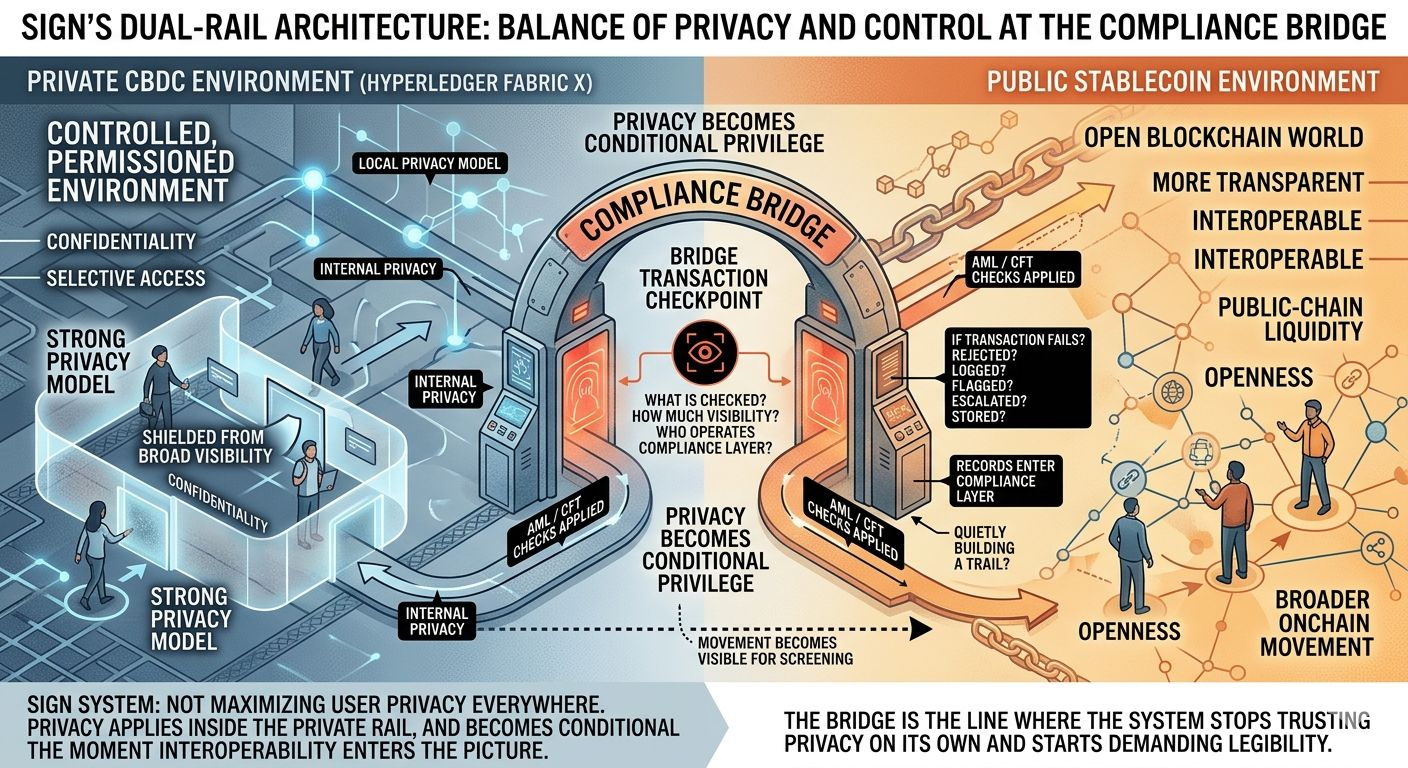
What SIGN is building makes more sense when you stop thinking of it as one smooth system and start thinking of it as two very different worlds joined together.
On one side, there is the private CBDC environment built on Hyperledger Fabric X. That is the controlled, permissioned side. The side wrapped in the language of privacy, selective access, and protection for retail activity. It is designed to feel contained.
On the other side, there is the public stablecoin environment. That side feels much closer to the open blockchain world — more transparent, more interoperable, more connected to public-chain liquidity and broader onchain movement.
Between those two worlds sits the bridge.
At first that sounds simple enough. It just connects them.
But the more I think about it, the less simple it feels.
If every crossing through that bridge triggers a compliance check, then the bridge is not just a connector. It is a checkpoint. And once you understand it that way, it becomes one of the most important parts of the whole design.
Inside the private CBDC system, the privacy model sounds strong. Retail transactions are framed in a way that makes it seem like ordinary activity is shielded from broad visibility. That creates a clear impression that this side of the system is meant to preserve a real degree of financial privacy.
And maybe it does.
But the moment someone wants to move value out of that private environment and into the public one, the bridge steps in and the rules change.
Now the transfer is no longer just movement. It becomes something that has to pass through a compliance layer.
That is where the tension starts to show.
Privacy inside a closed environment is one thing. Privacy at the exact point where a system needs to inspect, evaluate, approve, or reject your movement into a public environment is something else entirely. You cannot really say a transfer remains private in the same way if it has to become visible enough for AML/CFT screening the moment it reaches the boundary.
That does not mean the privacy claims are fake.
It does mean they have limits.
And those limits matter more than they first appear to.
The more I sit with it, the more the bridge feels like the place where the system reveals what it actually is.
A lot of people will probably read the privacy section and come away thinking the system is privacy-preserving. Others will look at the stablecoin side and see openness, interoperability, and utility. But neither of those views captures the full picture on its own.
The real story is in the transition.
Because that is where the user’s options stop being theoretical and start being tested by policy.
The private side may offer confidentiality. The public side may offer openness. But the bridge decides whether a person can actually move between those two conditions.
That is why it feels so important.
It is not just handling conversion. It is deciding what kind of movement is allowed, under what rules, with what level of scrutiny, and with what kind of record left behind.
That is much more than plumbing.
That is control.
What makes this harder to ignore is how little the document really says about the checkpoint itself. It tells you that AML/CFT checks are applied to bridge transactions, but it does not really unpack what that means in practice. And that leaves a lot hanging in the air.
What exactly is being checked?
How much visibility does the bridge have into the transaction?
Who is actually operating that compliance layer?
What happens if a transaction fails?
Does it simply get rejected, or does it get logged, flagged, escalated, and stored?
How long are those records kept?
Who gets access to them later?
Those are not minor implementation details. Those are the details that determine whether the bridge is a proportionate regulatory boundary or something much heavier than that.
Because once compliance enters the picture, records usually enter with it.
And once records enter with it, privacy becomes about more than whether the public can see your payment. It becomes about whether the system itself is quietly building a trail at the exact point where users try to step outside the private zone.
That is where the design starts to feel less like privacy infrastructure and more like privacy with conditions attached.
I do not think that automatically makes the system broken. And I do not think it means the entire privacy model is meaningless.
If a sovereign system wants to connect a private domestic monetary environment with a more open public blockchain environment, some kind of compliance boundary is not surprising. In a lot of ways, it is expected.
The issue is not that the checkpoint exists.
The issue is what that checkpoint means for the broader promise being made.
Because a user reading about retail privacy may imagine something more complete than what the architecture actually offers. They may assume privacy follows the asset naturally. But what this setup seems to suggest is something narrower.
Privacy applies inside the private rail, and then becomes conditional the moment interoperability enters the picture.
That is a very different promise.
Not privacy everywhere.
Privacy until the boundary.
And that boundary may be the most honest way to understand the whole system.
The private environment is allowed to be private.
The public environment is allowed to be open.
But the passage between them is supervised.
That tells you almost everything.
It tells you this is not really a system trying to maximize user privacy in every direction. It is trying to balance privacy with control, and it does that by placing the strongest scrutiny at the exact moment value leaves the protected environment.
In that sense, the bridge is not just infrastructure.
It is the line where the system stops trusting privacy on its own and starts demanding legibility.
Maybe that is the right design for the kind of system SIGN wants to build. Maybe a sovereign dual-rail model was always going to work like this.
But if that is the model, it should be described more plainly.
Because right now the privacy story sounds broad, while the actual point where privacy gives way to compliance feels narrower, heavier, and far more important than the document first makes it seem.
That is the part I keep coming back to.
Not that the bridge exists.
But that the bridge is where privacy stops being a clean principle and starts becoming a conditional privilege.
Once I saw that, the whole architecture read differently.
#SignDigitalSovereignInfra @SignOfficial $SIGN