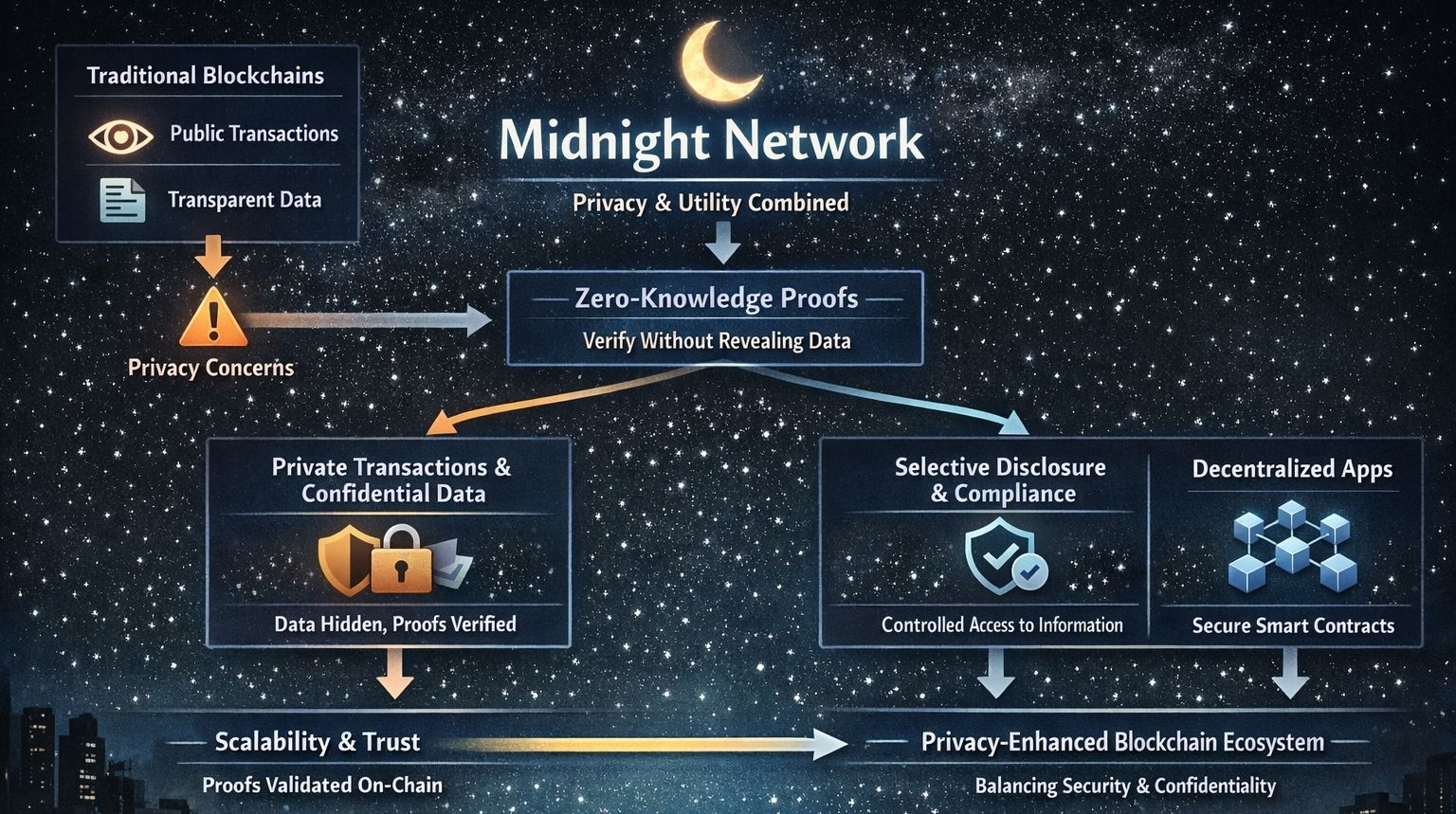
If you’ve spent any time exploring blockchain technology, you’ve probably noticed a recurring tension: transparency versus privacy. Most public blockchains are designed to be open and verifiable, which is great for trust, but not always ideal when sensitive data is involved. This is the space where Midnight Network is trying to carve out a meaningful role—by using zero-knowledge (ZK) proofs to balance privacy with functionality in a way that feels practical rather than theoretical.
At its core, Midnight Network is built around a simple idea: people and organizations should be able to use blockchain technology without exposing more information than necessary. Traditional blockchains like Bitcoin or Ethereum make transaction data visible to anyone who cares to look. While addresses are pseudonymous, patterns can still reveal identities or behaviors over time. For many use cases—finance, identity, healthcare, enterprise workflows—this level of exposure isn’t just uncomfortable, it’s unacceptable. Midnight attempts to address this by embedding privacy directly into the protocol, rather than treating it as an optional add-on.
The technology behind this approach relies heavily on zero-knowledge proofs. In simple terms, ZK proofs allow one party to prove that something is true without revealing the underlying information. For example, you could prove you meet certain criteria—like being over 18 or having sufficient funds—without sharing your actual age or account balance. Midnight uses this concept to enable transactions and computations that are verifiable by the network but opaque to outside observers. This means users can interact with smart contracts and decentralized applications while keeping their data confidential.
What makes Midnight particularly interesting is that it doesn’t aim to be a “completely private” black box system. Instead, it tries to strike a balance between privacy and compliance. In the real world, especially in regulated industries, absolute anonymity can be a barrier rather than a feature. Midnight’s design acknowledges that some level of selective disclosure is often necessary. The idea is that users should have control over what they reveal and to whom, rather than having everything exposed by default or hidden beyond recovery. This approach opens the door to use cases where privacy and regulation need to coexist, such as financial services or enterprise data sharing.
Architecturally, Midnight is designed as a network that can handle both private and public data flows. It separates the execution of transactions from the verification of their correctness, using ZK proofs as the bridge between the two. This allows computations to happen off-chain or in a privacy-preserving environment, while still producing proofs that can be validated on-chain. The result is a system that doesn’t overload the blockchain with sensitive data, yet maintains the integrity and trust that decentralized systems rely on.
Another key aspect is its focus on programmability. Midnight isn’t just about private transactions; it’s about enabling developers to build applications that can operate with fine-grained control over data visibility. This could include decentralized identity systems, confidential financial instruments, or supply chain applications where certain details need to remain hidden while others are shared. By giving developers tools to define what is public and what is private, the network becomes more flexible and adaptable to real-world needs.
In terms of ecosystem, Midnight is positioning itself as part of a broader movement toward privacy-enhanced Web3 infrastructure. Rather than competing directly with general-purpose blockchains, it complements them by providing capabilities that are difficult to implement natively in fully transparent systems. This could lead to integrations where public chains handle open interactions and settlement, while Midnight manages sensitive computations behind the scenes. Over time, this kind of layered approach might become more common as the industry matures.
The problem Midnight is trying to solve isn’t new, but it remains unresolved: how do you build systems that are both trustworthy and respectful of user privacy? Centralized systems handle privacy by controlling access, but they require trust in a single authority. Traditional blockchains remove that central authority but often sacrifice privacy in the process. Midnight’s bet is that zero-knowledge technology can bridge this gap, offering a way to verify truth without exposing the underlying data.
Of course, there are challenges. ZK technology, while powerful, is still relatively complex and can be computationally intensive. Making it accessible to developers and efficient at scale is not trivial. There’s also the question of adoption—whether users and organizations will be willing to adopt a new network, and how it will integrate with existing tools and ecosystems. These are not small hurdles, but they are shared by many projects pushing the boundaries of what blockchain can do.
What makes Midnight worth paying attention to is not that it promises to solve everything, but that it approaches a real limitation of current systems with a thoughtful design philosophy. It recognizes that privacy is not just a feature—it’s a requirement for many meaningful applications of blockchain technology. By focusing on controlled disclosure, practical programmability, and verifiable privacy, Midnight is exploring a direction that could make decentralized systems more usable in everyday contexts.
In the broader crypto landscape, where experimentation is constant and narratives shift quickly, projects like Midnight serve as a reminder that some of the most important work happens quietly, at the level of infrastructure. If blockchain is to move beyond niche use cases and into mainstream adoption, solutions that address privacy without compromising trust will likely play a central role. Midnight Network is one attempt to move in that direction, grounded in technology that is still evolving but increasingly hard to ignore.