Governance Capture via Credential Engineering
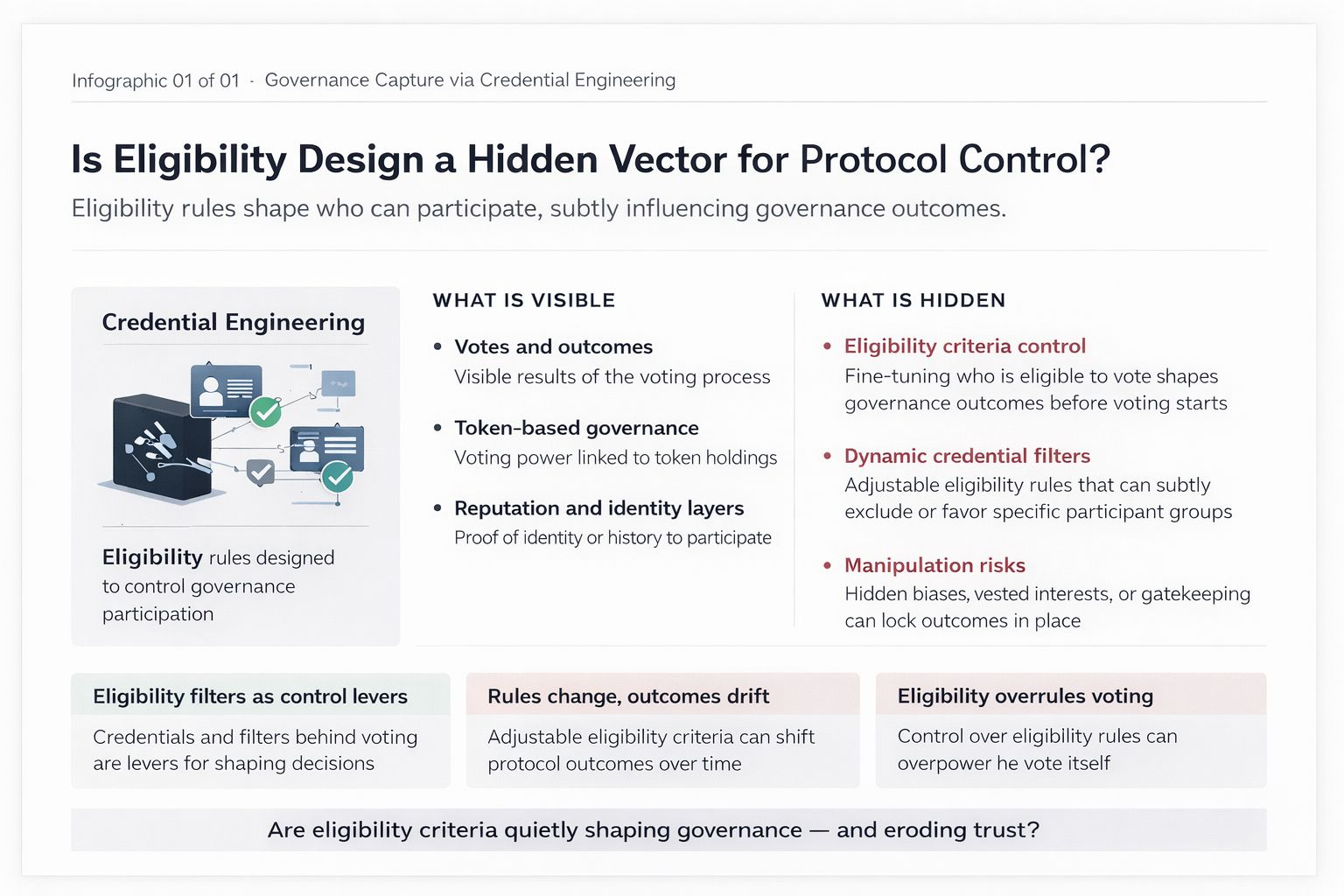
→ Designing eligibility rules to subtly control protocol outcomes
There’s a weird thing I’ve started noticing in governance systems: people think they’re voting on outcomes, but most of the time, the outcome was already decided before the vote even opened.
Not in a conspiracy way. More subtle than that.
It’s in the eligibility…
Who gets to vote. Who qualifies. Who even shows up on the list in the first place. That’s where things get shaped. And once you see it, it’s hard to unsee.
Think about it like a college entrance exam. Everyone talks about merit, scores, fairness. But if the syllabus itself quietly favors students from certain backgrounds, the result is already biased before anyone writes the exam. The “competition” is just theater.
That’s the core problem most governance systems pretend doesn’t exist.
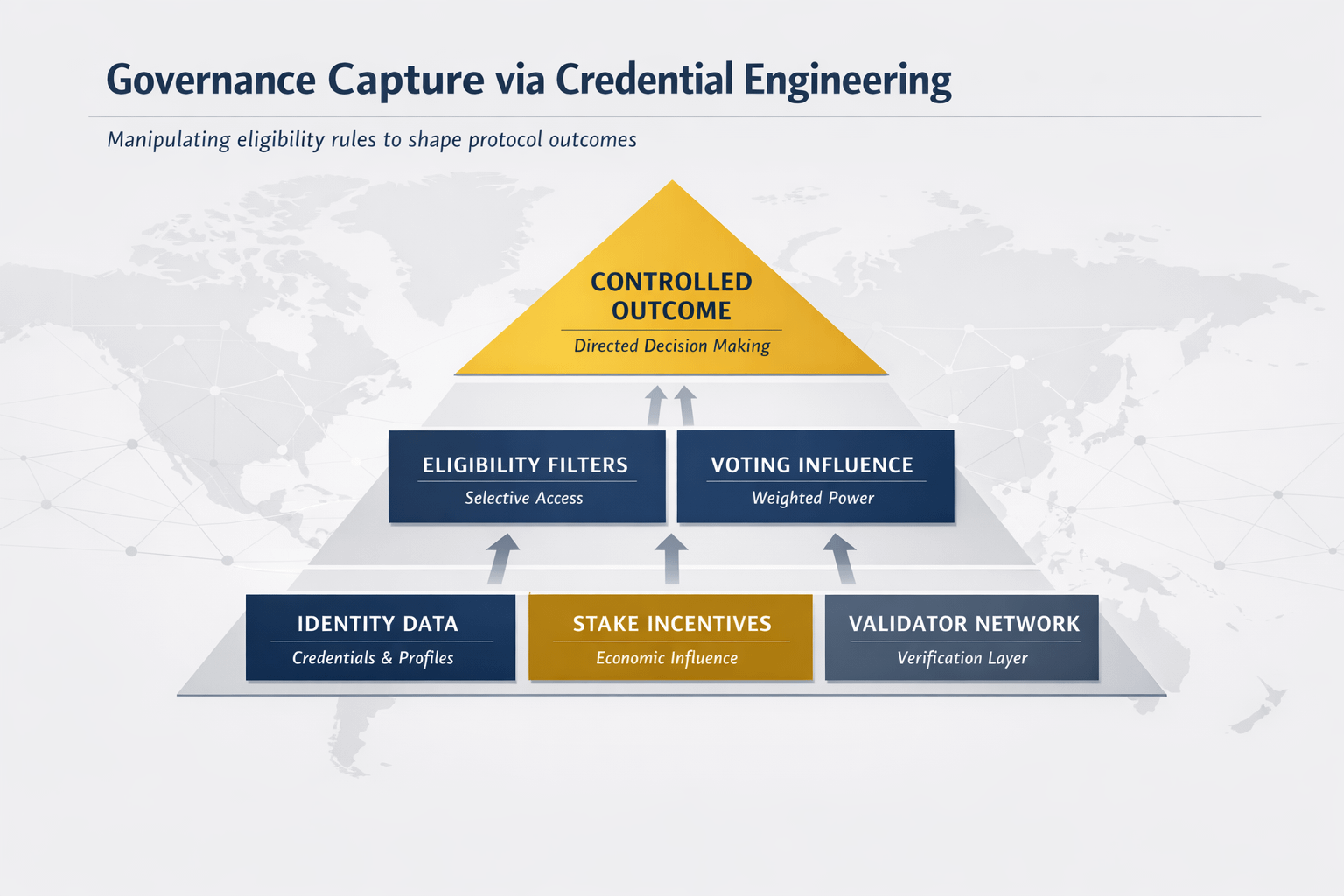
Token-based voting made it worse. Wealth = influence. Then came attempts to fix it: reputation systems, identity layers, quadratic voting. Each one tries to rebalance power, but they all run into the same issue someone still defines the rules of participation.
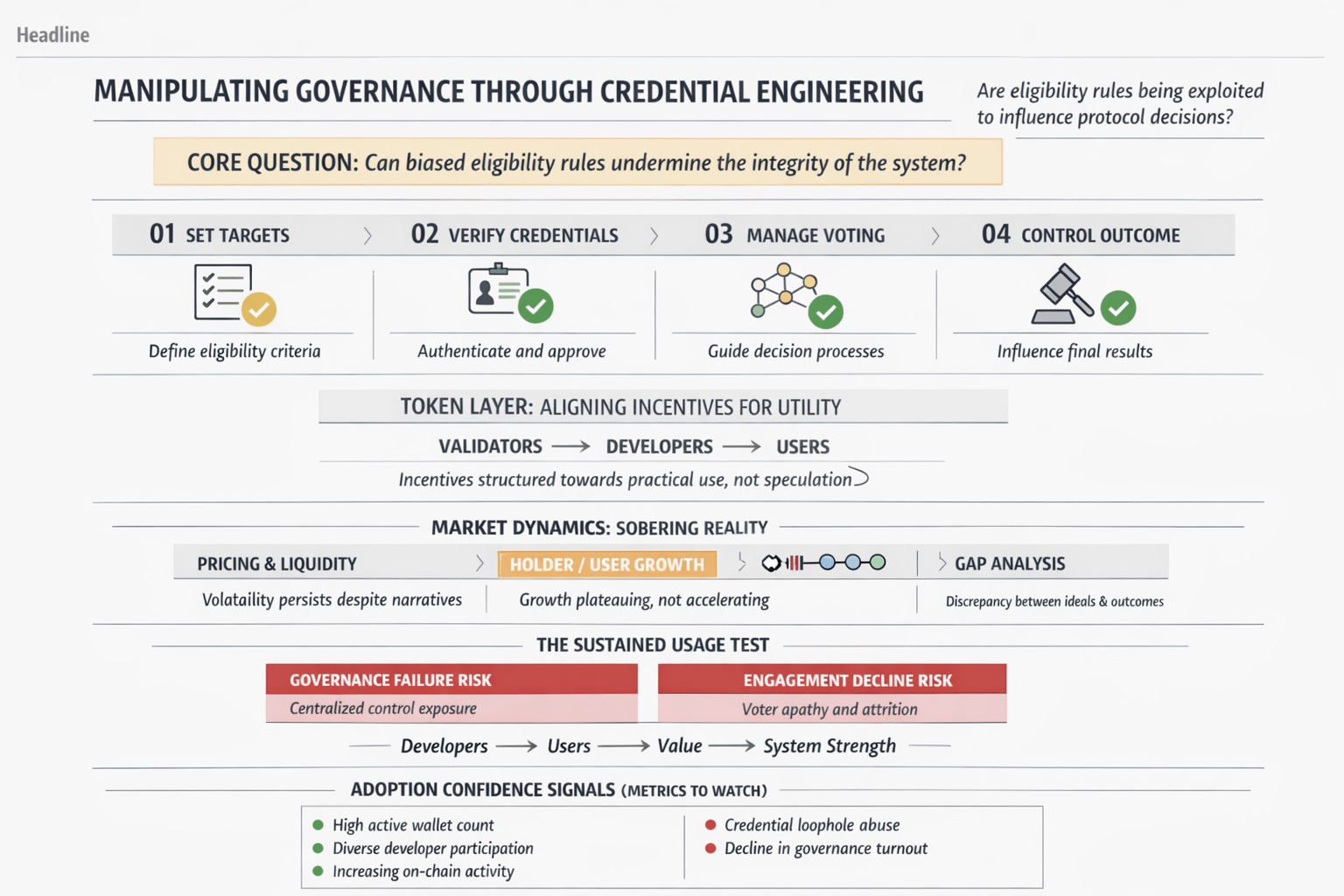
And that’s where credential engineering enters.
With something like $SIGN , the interesting shift isn’t just identity or attestations ,, it’s how credentials become programmable gates. Not just “are you human?” but “what kind of human are you, according to this system?”
Two mechanisms stand out.
First, attestations as composable signals. Instead of a flat identity, you accumulate credentials maybe proof of contribution, participation in past votes, holding certain assets, completing tasks. These aren’t just badges; they’re filters. Governance proposals can define eligibility based on combinations of these signals.
Second, dynamic eligibility rules. This is where it gets sharp. A proposal doesn’t have to be voted on by “all users.” It can be restricted to wallets with specific attestations say, contributors with 3+ verified actions in the last 90 days, or users who interacted with a protocol before a certain block.
On paper, this sounds fair. Even smart. You’re letting “relevant” participants decide.
But here’s where it gets interesting.
Who defines what “relevant” means?
Because once you can design the filter, you can shape the crowd. And once you shape the crowd, you shape the outcome without ever touching the votes themselves.
It’s like hosting a debate but quietly choosing who gets invited. You don’t need to rig the microphones if you’ve already curated the room.
This is the part people underestimate. Credential systems don’t just measure reality ,, they construct it.
And sometimes, it’s not even malicious. A team might genuinely believe that long-term contributors should have more say. So they design eligibility around contribution attestations. Fair enough.
But then edge cases creep in.
What counts as a contribution? Who verifies it? Can it be gamed? Are early insiders overrepresented? Are newer users permanently sidelined?
The system starts to solidify around its own history.
There’s also a feedback loop here that’s easy to miss. If governance power depends on certain credentials, users will optimize to acquire those credentials. Not necessarily to contribute meaningfully, but to qualify.
So behavior shifts. You don’t get organic participation ,,you get strategic participation.
It reminds me of how social media changed once people realized the algorithm rewards certain behaviors. Suddenly, everyone’s “authenticity” looks the same.
Now imagine that dynamic, but tied to governance power.
And there’s another layer. Credential opacity.
In theory, everything is transparent. On-chain, verifiable. But in practice, the logic behind eligibility can get complex fast. Nested conditions, multiple attestations, time-based filters. Most users won’t fully understand why they’re eligible or not.
So you end up with a system that feels neutral but is actually highly opinionated.
That’s not necessarily bad. Every system has opinions baked into it.
The real question is whether those opinions are visible.
Because governance capture doesn’t always look like domination. Sometimes it looks like well-designed rules that quietly favor a certain type of participant.
$SIGN doesn’t create this problem it exposes it. It gives tools to formalize what was previously informal.
And that’s the uncomfortable part.
We like to believe that decentralization means no one’s in control. But in systems like this, control just moves upstream from voting to rule design.
So maybe the real governance layer isn’t the vote at all.
It’s the moment someone decides what qualifies you to be in the room.#SignDigitalSovereignInfra @SignOfficial

