I used to think better identity systems were just a matter of stronger cryptography and clearer standards. If we could prove who someone was securely, adoption would follow. It felt like a technical problem waiting for a technical solution.
But over time, that assumption started to feel incomplete. I noticed that most systems, even the advanced ones, still depended on being asked. Every interaction began with a request. “Show me who you are.” And every response revealed more than it needed to.
At first, this felt normal. But upon reflection, it became clear that this model creates quiet friction.
When I looked closer, the issues weren’t just technical. They were structural. Identity systems still relied on hidden central points, issuers, registries, intermediaries. Even when labeled decentralized, verification often required reaching back to a source. That dependency didn’t disappear. It just moved.
More importantly, I noticed something harder to ignore: people weren’t using these systems repeatedly.
The ideas sounded important, privacy, ownership, verifiability, but they didn’t translate into daily behavior. Identity remained an occasional task, not embedded infrastructure. It was something you dealt with when required, not something that worked quietly in the background.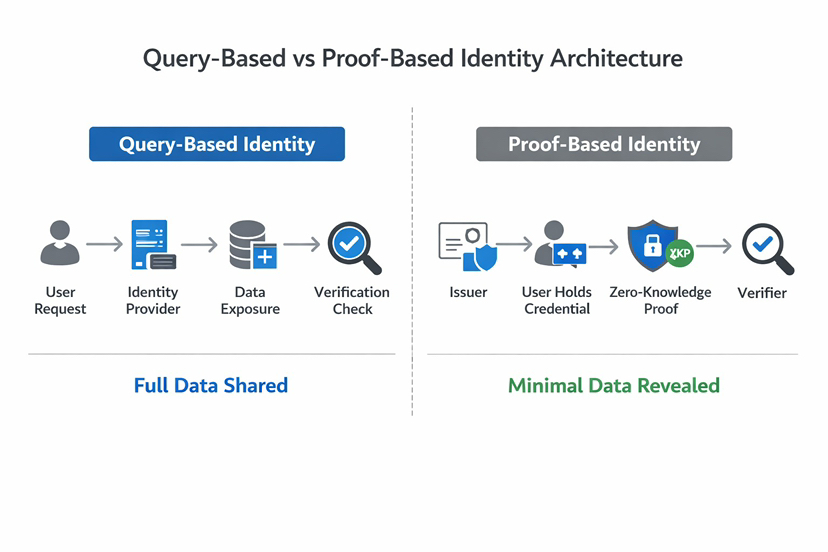
That gap started to change how I evaluated these systems. I stopped focusing on what they promised and started observing how they were used.
I moved from asking whether something was conceptually correct to asking whether it reduced friction in practice. Systems, I realized, only scale when they stop demanding attention.
They need to disappear.
It was around this shift that I began looking more closely at @SignOfficial and the role of $SIGN Token in its design.
At first, this felt like another iteration of familiar ideas, verifiable credentials, decentralized identifiers, selective disclosure. But what stood out wasn’t the components. It was the assumption being challenged:
Does identity need to be queried at all?
Or can it be presented, selectively, privately, and verifiably, without requiring a system to ask for it?
That question reframes identity entirely.
Instead of treating identity as a database to be accessed, #SignDigitalSovereignInfra approaches it as a system of attestations. Credentials are issued once, held by the user, and presented when needed. Verification doesn’t require constant communication with the issuer. It relies on validating proofs.
This changes how interaction happens.
Instead of exposing full identity data, users reveal only what is necessary, a condition, a qualification, a status. Not everything. Just enough.
It reminded me of how payment systems evolved. Transactions once required layers of direct verification. Today, they rely on tokenized confirmation. You don’t expose your financial history, you present a valid signal.
Identity, in this model, begins to function the same way.
A simple example made this clearer to me. Instead of reconnecting wallets and exposing full activity histories for access, a user could present a single attestation, proof of prior participation, compliance status, or reputation, to unlock services. The interaction becomes lighter. More precise. Reusable across contexts.
The role of validators becomes critical here. They aren’t just confirming data, they’re maintaining the integrity of attestations over time. The presence of the Sign Token introduces an incentive layer that supports this coordination. Validators, issuers, and verifiers remain aligned because reliability itself becomes economically reinforced.
What stood out to me wasn’t the token as an asset but as a mechanism for sustaining trust.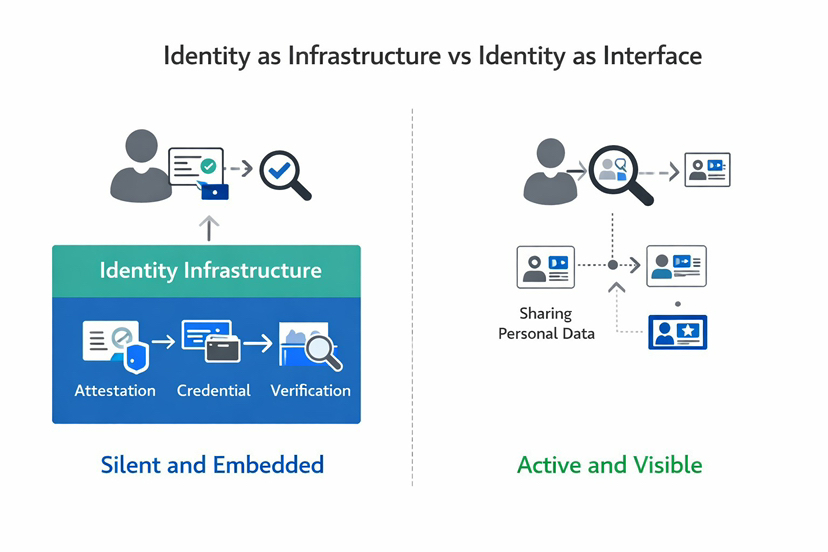
And this design direction reflects broader shifts.
Trust online isn’t disappearing, but it is becoming conditional. People are more selective about what they share. At the same time, institutions require more verification, identity, compliance, eligibility.
This creates a tension: systems need more proof, while users tolerate less exposure.
In emerging digital ecosystems, across regions like the Middle East and South Asia, this tension is even more visible. Systems are being built with fewer legacy constraints, creating space to rethink identity not as storage, but as flow.
But opportunity doesn’t guarantee adoption.
Markets often respond to narratives before systems prove themselves. Identity is a strong narrative. It sounds necessary. But attention doesn’t equal usage.
And usage is what matters.
If identity systems are only used during onboarding, they remain peripheral. If developers treat them as optional features, they don’t become infrastructure. And if users don’t interact with them repeatedly, they don’t build habits.
This is the real constraint.
The usage threshold problem.
A system must cross a point of repeated, unavoidable interaction before it becomes necessary. Below that threshold, it remains an idea, useful, but not essential.
Crossing that threshold requires coordination. Builders must integrate identity into core workflows. Institutions must issue credentials that matter. Users must encounter these systems often enough that they stop noticing them.
That’s not easy.
And there are reasons to remain cautious.
At first, this model felt clean, privacy preserving, user-controlled, interoperable. But upon reflection, it became clear that complexity doesn’t disappear. It shifts. Managing attestations, ensuring issuer credibility, handling revocation, these introduce new layers of responsibility.
There’s also a coordination challenge. For attestations to carry meaning across systems, there must be shared understanding. Standards can guide this, but adoption depends on alignment.
Still, what kept my attention wasn’t simplicity. It was direction.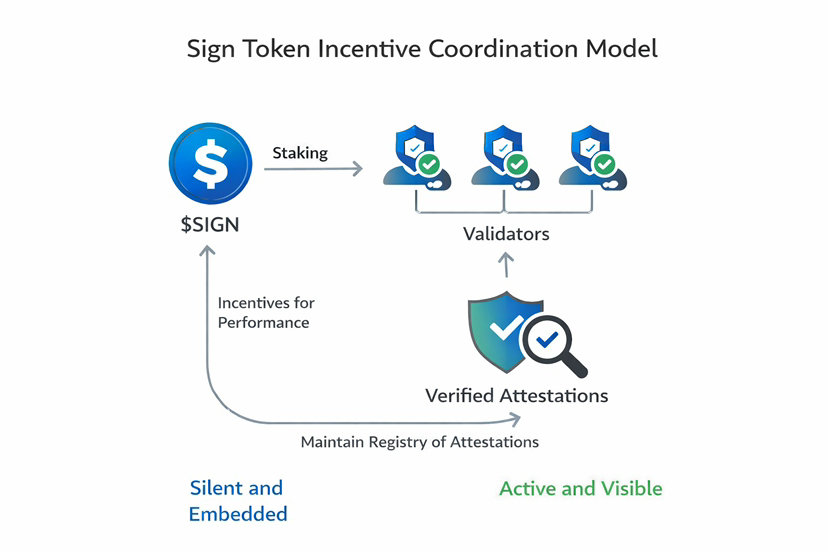
Moving away from “query my identity” toward proof based systems aligns more closely with how people actually behave. It reduces unnecessary exposure. It allows identity to become something you carry, not something constantly requested.
There’s a deeper layer to this.
Technology often tries to formalize trust. But trust itself is built through repetition, through consistent signals over time. Systems don’t create trust. They enable it.
What builds conviction for me now is not how well a system is explained, but how often it is used.
Are there applications where identity is required, not optional? Are attestations reused across contexts? Are validators active because verification demand persists?
These signals are quieter. But they are harder to fake.
Because the difference between an idea that sounds necessary and infrastructure that becomes necessary is repetition, and repetition only happens when systems become invisible.