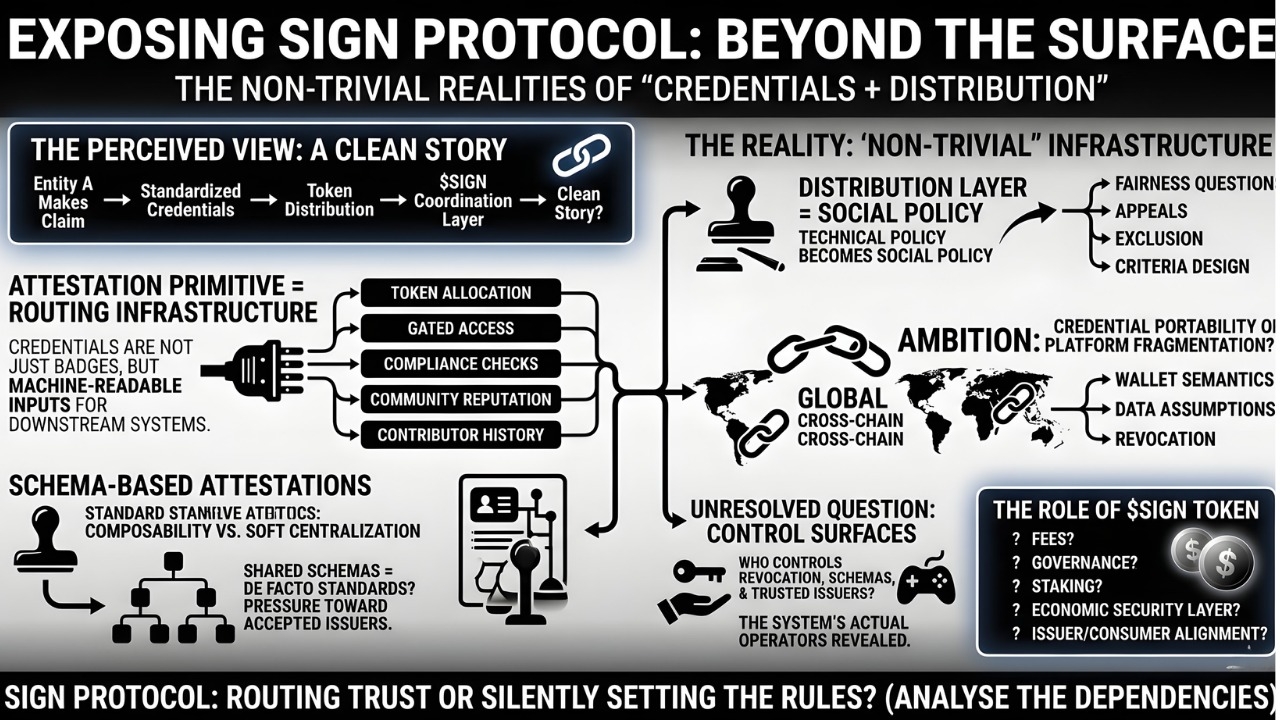
I was poking through SIGN’s litepaper / product docs again, mostly because i kept seeing it framed in a very tidy way: credential verification, token distribution, and a token layer on top to coordinate the network. clean story. almost too clean. whenever something in Web3 sounds that simple, i usually assume the interesting part is hiding one layer lower.
i think most people look at SIGN and see a familiar pattern. okay, it’s an attestation protocol. issuers make claims, users receive credentials, apps verify them, and then projects use that to run airdrops, grants, access lists, or other distribution logic. plus $SIGN sits there as the economic/governance piece. not wrong, exactly. just incomplete.
but that’s not the full picture.
the first thing that seems deceptively small is the attestation primitive itself. on paper it’s just “entity A makes a signed claim about entity B.” kind of boring. but if those claims are standardized enough to be machine-readable and portable, they start behaving like infrastructure rather than metadata. a credential isn’t just a badge — it becomes an input into downstream systems: token allocation, gated access, compliance checks, community reputation, contributor history, maybe even offchain-to-onchain eligibility bridges. and that’s where it gets interesting, because now the protocol is not merely recording trust, it’s routing decisions based on trust.
one core mechanism here is schema-based attestations. that sounds like backend plumbing, but it matters a lot. shared schemas mean different applications can interpret credentials consistently instead of each project inventing a custom format for “verified user,” “event attendee,” or “grant recipient.” that gives you some chance at composability. but it also creates pressure toward standard-setting, and maybe soft centralization. if only a few schemas become widely recognized, and only a few issuers are accepted as credible, then the openness of the protocol matters less than the social trust graph around it.
the second mechanism is the distribution layer, which i honestly think is more operationally important than the identity framing. lots of teams can define who *should* get tokens. fewer can actually execute that distribution in a way that’s resistant to farming, understandable to users, and not a support nightmare. SIGN seems to be trying to connect verification directly to distribution rails, so the same stack that validates eligibility can also drive claims or allocations. useful idea. but here’s the thing: the minute a protocol touches token distribution, it inherits every messy question around fairness, appeals, exclusion, and criteria design. technical policy becomes social policy very fast.
third is the “global infrastructure” ambition. the promise seems to be that credentials and eligibility shouldn’t be stuck inside one chain, one app, or one local trust domain. in principle, that makes sense. in practice, cross-chain credential portability is where elegance usually starts to break. different chains have different wallet semantics, different data assumptions, and different security models. plus revocation, privacy, and issuer trust don’t magically simplify when you add more networks. so i can see the shape of the architecture, but i’m not fully convinced yet that “global” will mean shared standards more than just broad product distribution.
some of the stack is clearly live now, which i appreciate. SIGN is not only a whitepaper object. attestation issuance exists, token distribution tooling exists, and there are real production use cases already. that part feels grounded. what feels more open-ended is the role of $SIGN over time. maybe it becomes necessary for fees, governance, staking, or some verification/economic security layer. maybe it helps align issuers and consumers of credentials. or maybe the protocol and products are useful independent of the token, which is a very normal outcome in infra systems even if nobody says it that way.
my unresolved question is around control surfaces. who gets to revoke a credential, update a schema, or define a trusted issuer set? because if SIGN becomes a real dependency for distribution and verification, those are not side details. they’re the system. and i’m not even saying that as criticism, more like… this is where “decentralized infra” often ends up revealing its actual operators.
watching:
- whether attestations become portable across apps, not just reusable within SIGN’s own ecosystem
- how issuer trust, revocation, and disputes are handled when something goes wrong
- whether distribution tooling drives adoption more than credential verification by itself
- what $SIGN is actually needed for in production usage
- whether “global infrastructure” turns into open standards, or just a successful integrated platform
$SIGN @SignOfficial #signdigitalsovereigninfra