What kept bothering me was not gas. It was authorship.
I keep coming back to one exact incident. A user reaches a light UX step in an eligibility flow. The app prepares an attestation payload in the background. The user gives a delegation signature for that exact payload. A relayer submits it on the user’s behalf. Later, support reopens the case because the user disputes the outcome, and the whole decision now rests on whether that record really captures what the user approved.
That is why SIGN’s delegated attestation flow stood out to me. In Sign Protocol, delegated attestation is not “the backend handles it for you” in some loose sense. The payload has to be defined. The user has to approve that exact attestation through a delegation signature. Only then can a third party upload it. That order matters. The relayer can carry my attestation. It cannot author it for me.
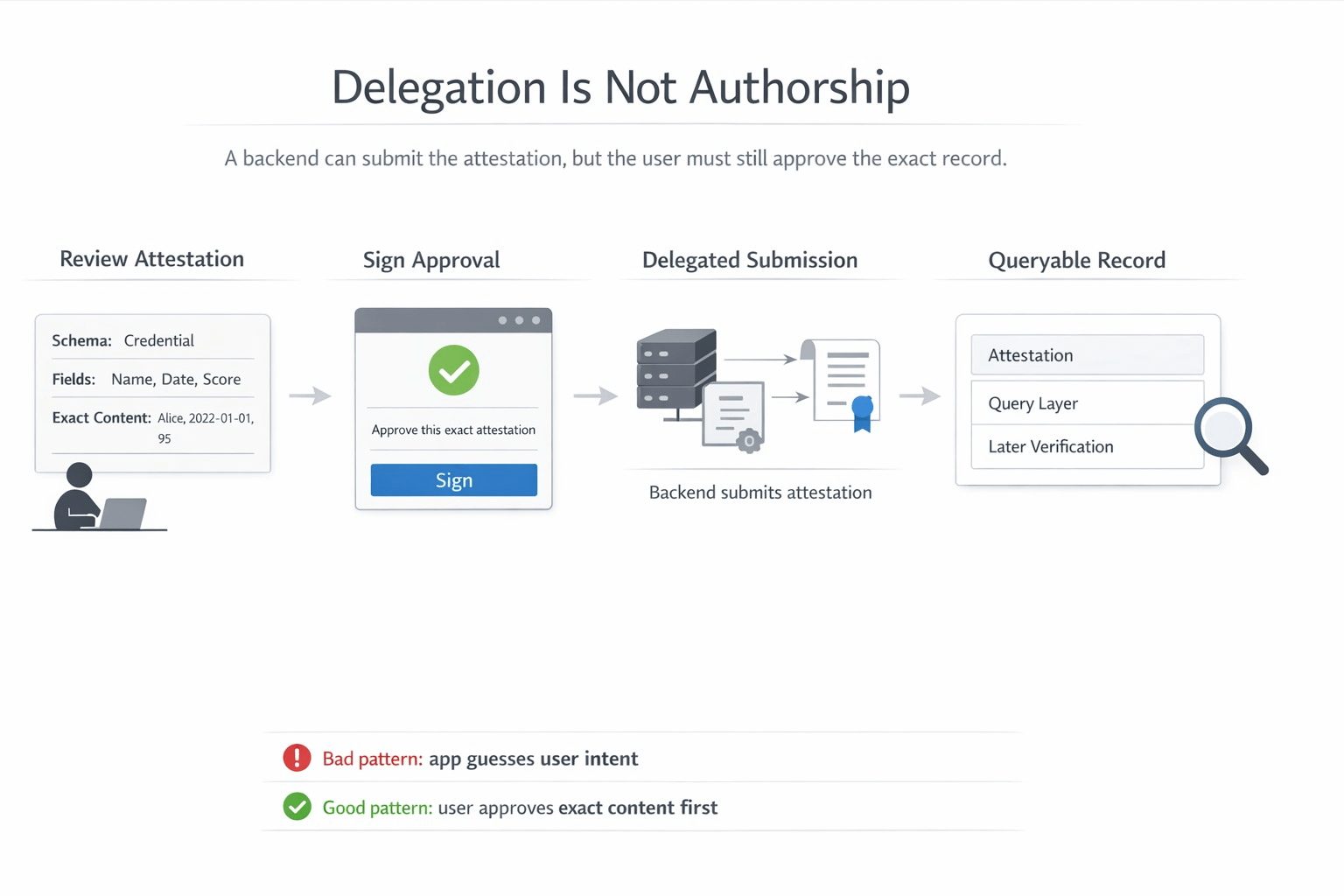
That boundary is the whole point of the flow. If the system stays strict, convenience helps with submission without touching authorship. If the system gets sloppy, the user still sees a wallet, the flow still completes, and the record still looks valid, but the authorship line has already moved. The attestation no longer means “I approved this exact claim.” It starts meaning “the app assembled something close enough and pushed it through.”
The reason I think this matters so much in SIGN is what happens next. The attestation does not vanish after submission. The schema fixes the structure and meaning of the data. The attestation binds that data to the issuer and subject. Then SignScan and the broader query layer make the record searchable, retrievable, and reusable across supported chains and storage paths. So the problem is not one messy UX moment. The problem is that a later operator may reopen a clean-looking record and treat it as ground truth.
That later handoff is where the risk becomes real to me. A support reviewer sees a valid schema, a valid attestation, and a normal history. Maybe the record was used to determine eligibility. Maybe it affected access. Maybe it fed some later decision the user is now challenging. Everything on the surface looks neat. But the actual question is narrower and harsher: was this the exact payload the user approved, or is the platform now defending something the app inferred before the relayer submitted it? If the answer is unclear, the system is no longer proving user intent. It is proving that its own pipeline can produce a believable record.
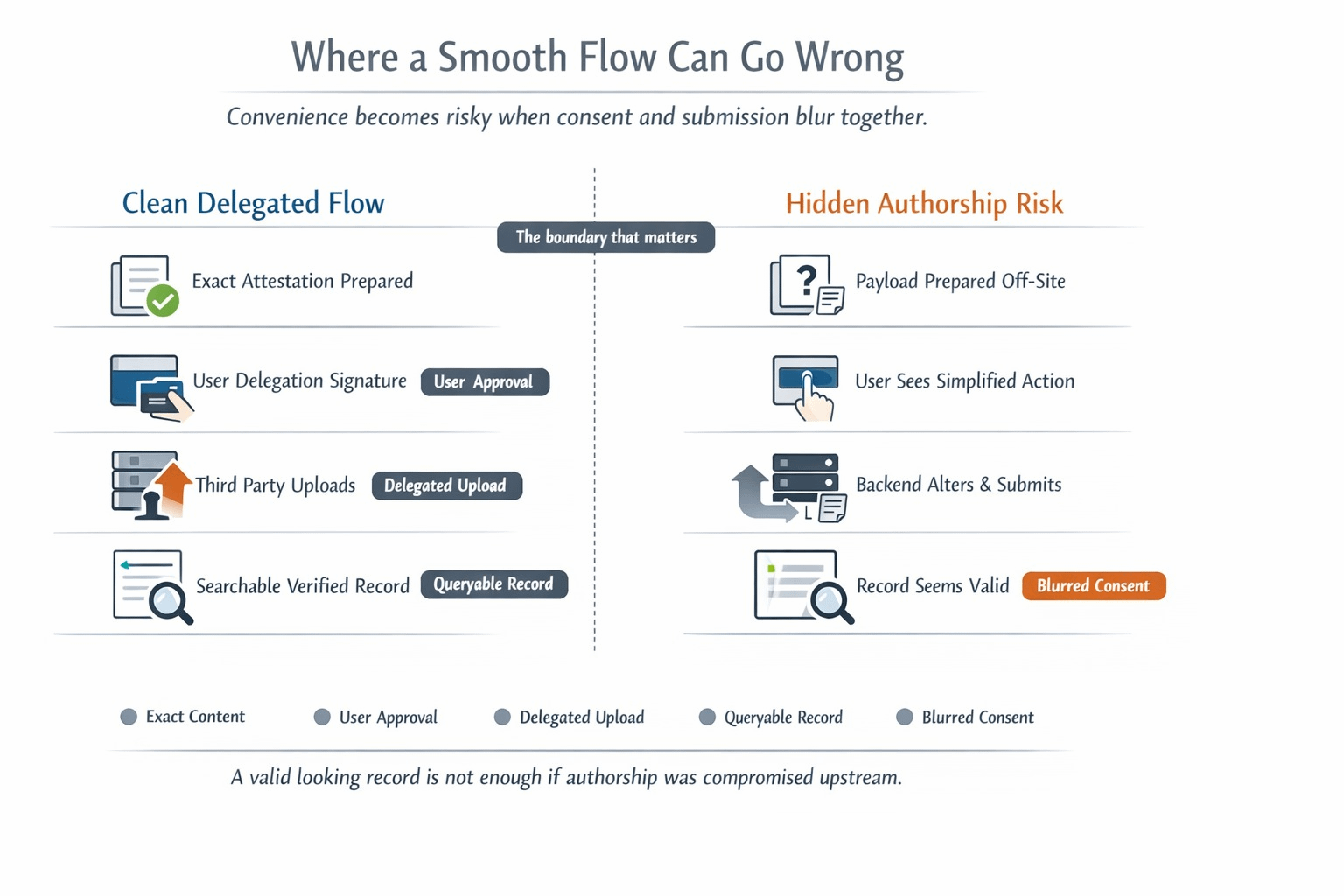
That is why I do not read delegated attestation as a convenience feature first. I read it as an authorship control. A third party can move the submission. It cannot fill in the truth for me. That boundary is what keeps the later query, review, and reuse layers honest. Without it, every downstream surface becomes more confident than it should be. The explorer still looks clean. The attestation still parses. The record is still reusable. But the human approval underneath it has already gone thin.
That is also where $SIGN feels native to me instead of decorative. If SIGN wants to underwrite real attestations, real querying, and real operational reuse, then delegated creation has to stay smooth without ever letting convenience draft the record for the user. Otherwise the system may keep producing verifiable records while quietly weakening the thing those records are supposed to preserve.
I do not think the hard test for SIGN is whether it can make attestations easier to create. I think the hard test is whether, when a disputed record gets reopened later, the system can still prove that convenience carried the user’s statement instead of writing it.
