I have sat in enough review rooms to know how these stories usually begin. A dashboard turns green, throughput climbs, latency falls, and somebody mistakes motion for control. The room relaxes too early. A risk committee signs off because the system looks fast, the users look satisfied, and no one wants to be the person asking why the authority model still feels loose. Then, weeks later, a phone vibrates at 2 a.m. An alert fires. A permissions trail that looked acceptable in daylight now reads like a confession. What failed was not the block time. What failed was judgment, exposure, and the old human habit of granting too much authority to a signature that was supposed to do one small thing.
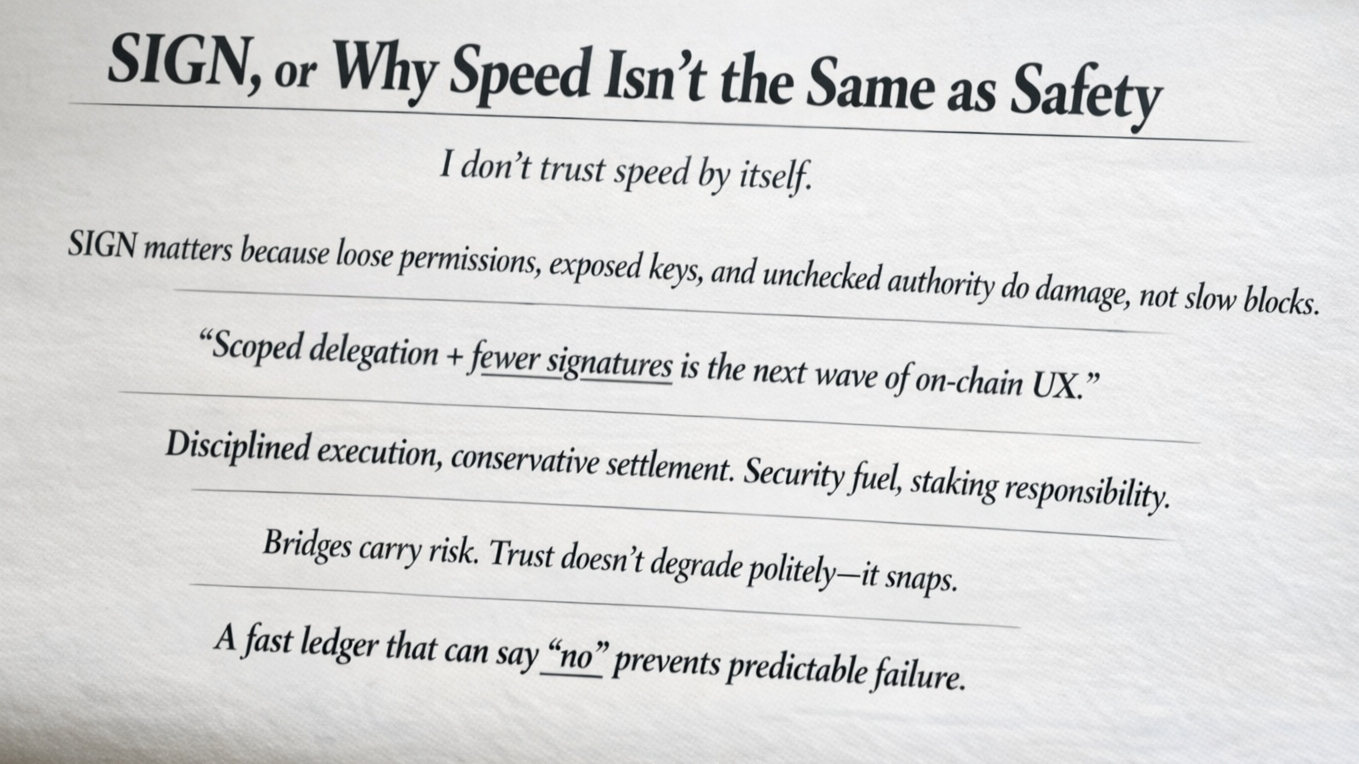
That is where i would begin with SIGN, because speed and safety have been incorrectly grouped together for too long. The market still talks as if performance is the central test of seriousness, as if the main question is how many transactions can fit through the pipe before the next benchmark screenshot gets posted. But real systems do not usually collapse because they were a little too slow. They collapse because permissions were broad, keys were exposed, approvals became muscle memory, and the architecture allowed a local mistake to become a system-wide event. Slow blocks can frustrate people. Bad authority models ruin them.
SIGN matters because it appears to understand that distinction. It is an SVM-based high-performance L1, but the interesting part is not the speed claim by itself. The interesting part is the guardrails. That is the word adults look for after enough incidents, enough audits, enough strained calls with security and legal and operations while everyone tries to explain why something that worked in testing failed in the real world. A fast system without constraints is just a more efficient way to spread damage. A fast system with enforced limits begins to look like infrastructure rather than appetite.
That difference becomes clear in SIGN Sessions. The design is not merely about making the wallet experience smoother, though it does that. It is about replacing vague trust with enforced, time-bound, scope-bound delegation. That sounds procedural until you have lived through the alternative. Then it sounds like the line between a contained event and a public one. A user should not have to hand over broad, lingering authority just to complete a narrow task. A session should do what it was meant to do, for as long as it was meant to do it, and then expire without negotiation. That is not cosmetic design. That is risk discipline written directly into user flow.
“Scoped delegation + fewer signatures is the next wave of on-chain UX.”
The sentence lands because both halves matter. Fewer signatures matter because users are not reliable intrusion detection systems. If a product trains them to approve constantly, then the signature loses meaning. It becomes ritual rather than consent. Scoped delegation matters because it gives meaning back to authority. It says this key can act here, not there; now, not later; for this purpose, not every purpose someone might rationalize after the fact. It narrows the blast radius. It makes auditing less theatrical and more factual. It gives compliance something firmer than optimism to work with.
Anyone who has sat through wallet approval debates knows how quickly the conversation stops being abstract. Product wants less friction. Security wants less standing authority. Compliance wants specific consent, evidence, and revocability. Audit wants logs that can survive review after an incident, not just diagrams that looked clean before one. Risk committees do not stay awake at night because a chain might be a little slower than a rival. They stay awake because a compromised key does not care about your benchmark numbers. They stay awake because one over-permissioned flow can undo a year of disciplined work. They stay awake because exposure travels faster than reassurance.
This is why the TPS obsession feels increasingly unserious. It is not that performance does not matter. It does. But the industry has spent too much time treating throughput as maturity when it is really only one property, and not the one most likely to destroy trust. The ugliest failures do not come from lack of raw speed. They come from excessive permissions, silent key risk, and systems that cannot distinguish between a valid request and an overreach until after the damage is visible. In that sense, the benchmark race has often been a way to avoid the more uncomfortable discussion, which is that authority design is harder, less glamorous, and far more important.
SIGN’s architecture points toward a better hierarchy of concerns. Modular execution above a conservative settlement layer is not just a performance choice. It is a statement about where flexibility belongs and where caution must remain non-negotiable. Execution can move fast, adapt, and absorb application-level demands. Settlement can remain disciplined, slower to trust, harder to fool. That separation matters because mature infrastructure does not ask every layer to be equally aggressive. It lets one layer optimize for speed and another insist on final verification. Anyone who has seen a rushed internal exception become a permanent external weakness will understand the instinct immediately.
EVM compatibility fits into this story, but only in the modest role it deserves. It reduces tooling friction. It helps developers bring over workflows, integrations, and habits without rebuilding everything from scratch. That is useful. But it is not the core safety argument, and it should not be mistaken for one. Familiar tooling can migrate familiar mistakes just as easily as it migrates productivity. The real question is whether the system forces power to stay narrow, observable, and temporary even when convenience pushes in the opposite direction.
There is also no serious way to discuss any modern chain without admitting the problem at the edges. Bridges remain one of the clearest examples of how confidence gets overextended. They are useful, sometimes necessary, and consistently dangerous in ways the market prefers to discuss only after the fact. Every additional dependency imports another trust model, another coordination surface, another place where assumptions harden faster than controls do. “Trust doesn’t degrade politely—it snaps.” That is not rhetoric. That is the operating history of too many ecosystems that believed complexity would remain cooperative simply because the slide deck looked coherent.
The native token has a place here, but not as decoration. It is security fuel. And staking, viewed without promotional fog, is responsibility. It is a declaration that participants securing the network are not merely collecting upside; they are helping bear the burden of the network’s integrity. That framing matters because systems become childish when they talk about incentives without talking about obligations. Infrastructure is always moral in that plain, operational sense. Someone carries the cost of keeping it honest.
What i find most credible in SIGN, then, is not that it can move quickly. Plenty of systems can move quickly. What matters is whether speed is subordinated to control rather than confused with it. Whether the chain can let applications feel lighter without making authority sloppier. Whether sessions can grant enough access to be useful and still expire before usefulness turns into liability. Whether guardrails are actual enforcement rather than language pasted over optimism. Whether the settlement layer remains conservative enough to catch what execution alone would wave through.
Every internal incident report, if written honestly enough, becomes philosophical by the end. It begins with timestamps and alerts and approval chains and forensic detail. Then, slowly, it arrives at the same conclusion: safety is not the absence of motion. It is the presence of limits that hold when people are tired, distracted, hurried, or wrong. The systems that endure are not the ones that say yes most quickly. They are the ones that make every yes narrower, every delegation shorter, and every failure harder to scale.@SignOfficial #SignDigialSovereignInfra $SIGN