 SIGN is one of those projects that immediately makes me pause—not because it’s flashy, but because it’s trying to address a problem I’ve seen quietly derail otherwise solid systems.
SIGN is one of those projects that immediately makes me pause—not because it’s flashy, but because it’s trying to address a problem I’ve seen quietly derail otherwise solid systems.
Identity looks solved from a distance. You authenticate, you get access, things move forward. Simple. But that simplicity is mostly an illusion. Underneath, a lot of these systems are held together by assumptions that no one revisits until something breaks.
And when it breaks, it’s rarely graceful.
I’ve worked on systems where everything checked out operationally. Users onboarded. Permissions aligned. Transactions cleared. Then an audit came in. Or a dispute. Suddenly, basic questions turned into long investigations. Who approved this? What data was used? Was it valid at the time?
No one had clean answers. Just fragments.
That’s the gap SIGN is trying to close. Not by making identity faster or smoother, but by making it explainable. That’s a different goal entirely.
Instead of treating identity as a fixed record, it treats it as something that needs to be proven repeatedly, in context. Every claim becomes something that can be verified independently. Not assumed because it came from a trusted system, but validated because there’s evidence attached to it.
That shift sounds obvious when you say it out loud. It’s not how most systems are built.
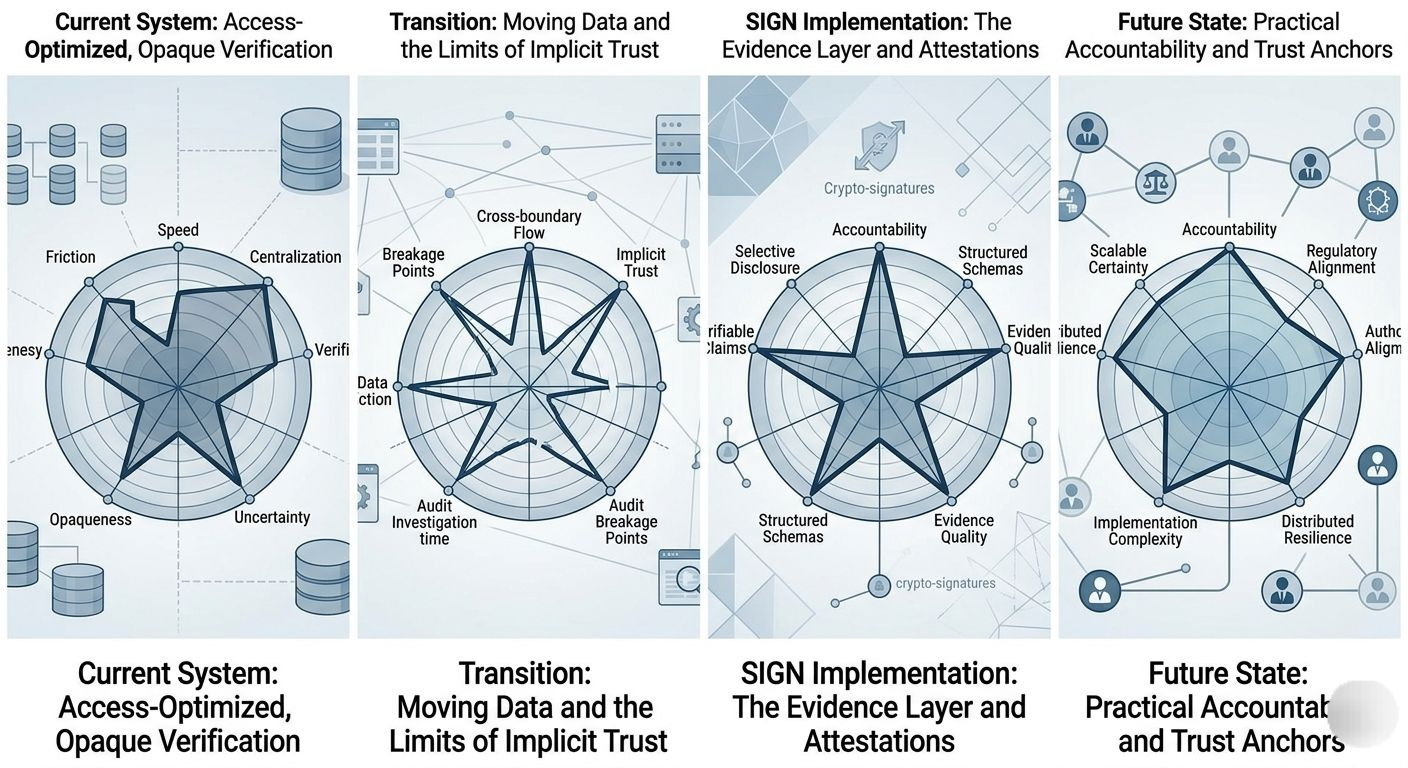
Most systems optimize for flow. Get the user through. Minimize friction. Store just enough to keep things running. Verification is usually implicit—buried inside the system rather than exposed as something reusable.
That works until you need to step outside that system.
The moment data has to move across boundaries—between services, organizations, or even jurisdictions—those assumptions start to fall apart. What was “trusted” in one context becomes questionable in another.
SIGN’s model, built around attestations and structured schemas, is trying to make those boundaries less painful. Instead of passing around raw data or relying on API-level trust, it passes verifiable statements. Small, specific, and cryptographically signed.
It’s a cleaner abstraction. Not perfect, but cleaner.
And honestly, it’s overdue.
What I find more interesting is how this approach changes the role of identity itself. It stops being a gatekeeper and starts acting more like a layer of evidence. Less about access control, more about accountability.
That’s a subtle but important shift.
Because access is temporary. Evidence sticks around.
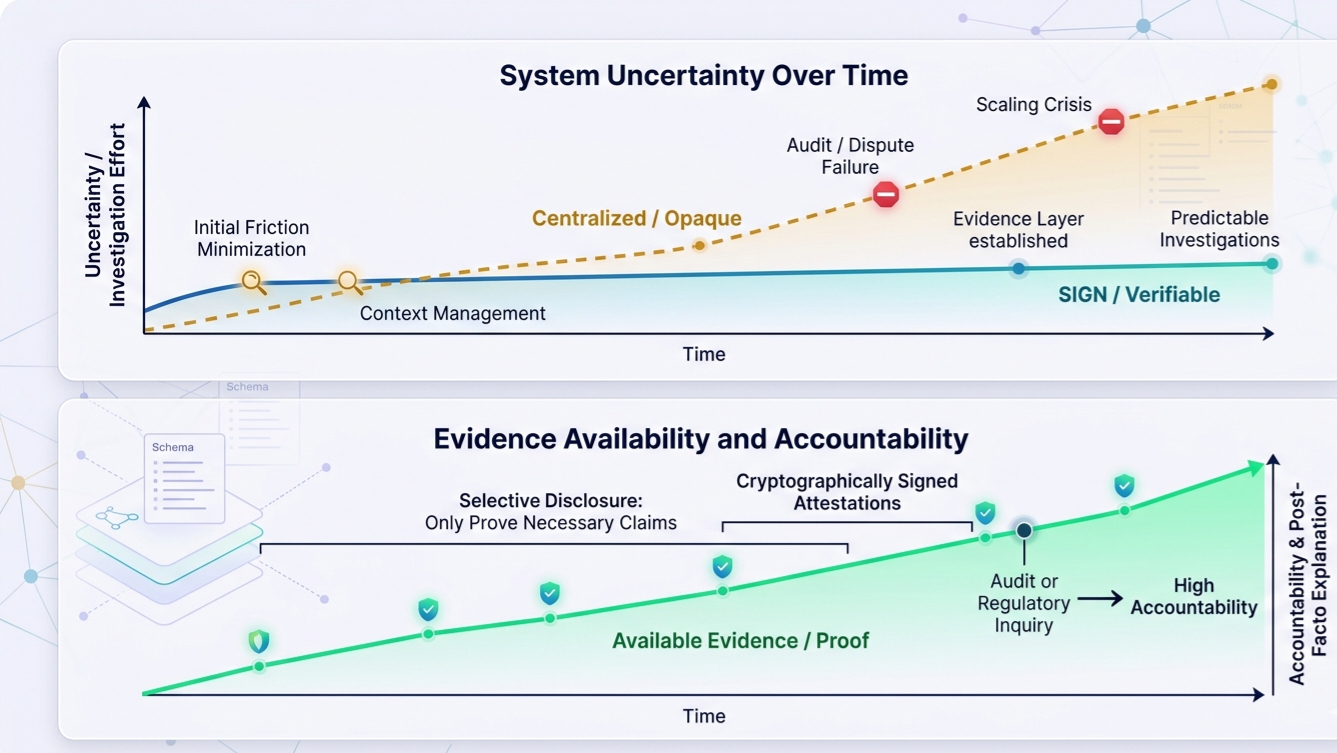
If a system can’t explain why access was granted after the fact, it doesn’t matter how smooth the experience was at the time. You’re left with uncertainty, and uncertainty doesn’t scale well—especially in financial or regulatory environments.
Of course, none of this exists in a vacuum.
Identity systems are always tied to authority. Someone issues credentials. Someone defines the rules. Someone has the power to revoke or invalidate. You can distribute infrastructure, but control still has to live somewhere.
That’s where things tend to get complicated.
SIGN introduces structure—schemas, issuers, verification layers—but structure alone doesn’t guarantee alignment. Different issuers can have different standards. Trust doesn’t automatically transfer. And when systems disagree, things can get messy fast.
I’ve seen integrations fail for less.
Then there’s privacy, which is usually where good intentions go to die. Most systems claim to minimize data exposure, but end up collecting more than they need because it’s easier than designing around constraints.
SIGN’s selective disclosure approach is the right direction. Prove only what’s necessary. Don’t overshare. Keep the payload tight. That’s how identity should work.
But I’d be lying if I said implementation is straightforward. It rarely is. Edge cases pile up. Context leaks. And suddenly you’re back to managing complexity you thought you avoided.
Still, I’d take that over the alternative.
Because the current model—centralized identity, opaque verification, heavy reliance on trust—isn’t holding up well. Too many breaches. Too many inconsistencies. Too many systems that work until they’re questioned.
SIGN doesn’t magically fix that. No system does.
What it offers is a better starting point. One where verification is built in, not patched on. Where identity isn’t just asserted, but supported. Where systems have a chance to explain themselves without scrambling.
That alone makes it worth paying attention to.
Not because it’s revolutionary. Because it’s practical.
And right now, practical is exactly what this space needs. 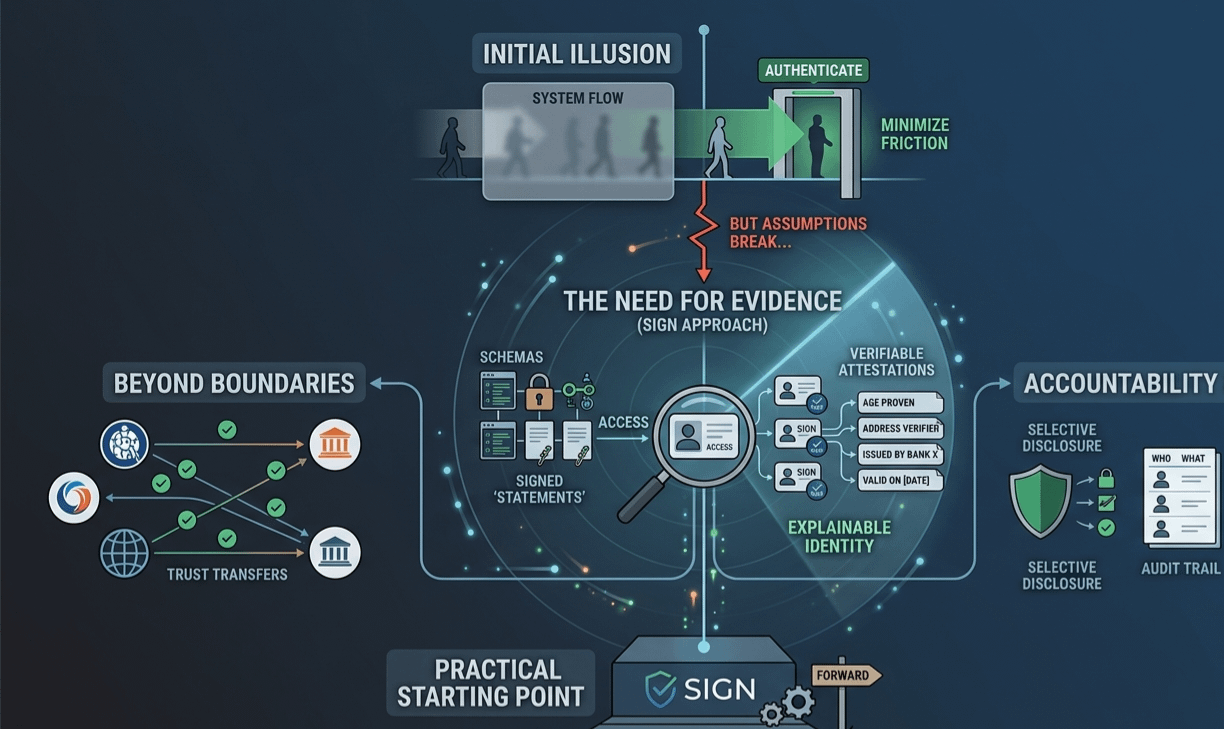
@SignOfficial #signdigitalsovereigninfra $SIGN