I’ve spent a considerable amount of time exploring blockchain technologies, but very few systems have made me rethink digital trust the way the SIGN Protocol has. At first glance, it may appear to be just another infrastructure layer built on blockchain, but once you begin to understand its design, it becomes clear that it represents something much deeper a shift toward programmable trust and automated compliance in a rapidly evolving digital world.
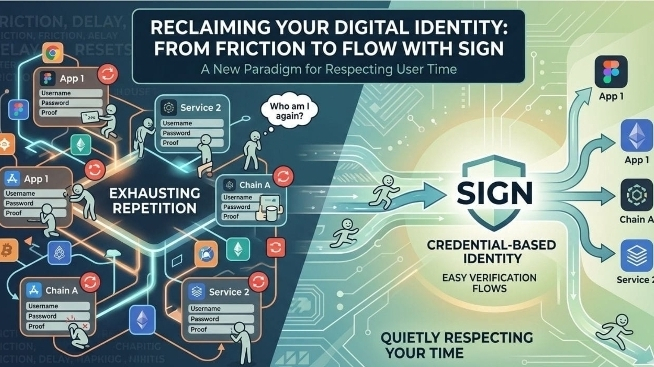
The core idea behind the SIGN Protocol is simple yet powerful: create a global infrastructure where credential verification and token distribution are not only transparent but also reliable, secure, and compliant by default. In traditional systems, trust often depends on intermediaries banks, institutions, or centralized authorities. These entities verify identities, enforce rules, and approve transactions. However, they also introduce inefficiencies, delays, and sometimes even bias or corruption. SIGN Protocol attempts to remove these limitations by embedding trust directly into code.

Through the use of the $SIGN token, I’ve been able to interact with a system where rules are not just guidelines they are enforced automatically through smart contracts. This means that every transaction I make follows a predefined set of conditions. Whether it’s a cooldown period to prevent rapid resale, buyer verification to ensure eligibility, or country-based restrictions to comply with regulations, everything is handled seamlessly in the background.
What makes this particularly valuable is how it reduces human error and manipulation. Instead of relying on manual checks or external approvals, the system executes rules consistently and transparently. This level of automation brings a new kind of confidence, especially when dealing with high-value transactions or sensitive digital assets.
One of the most compelling aspects of the SIGN Protocol is its ability to bridge the gap between compliance and privacy. In many systems today, compliance comes at the cost of exposing personal data. Users are often required to submit sensitive information, which is then stored in centralized databases—making it vulnerable to breaches or misuse. SIGN Protocol approaches this differently by leveraging advanced cryptographic methods, such as zero-knowledge proofs, to verify eligibility without revealing unnecessary details.
From my experience, this creates a much more balanced system. I can prove that I meet certain requirements such as being eligible to participate in a token distribution without exposing my full identity or personal data. This not only enhances privacy but also builds trust in the system, as users feel more secure in how their information is handled.
Another area where I’ve found SIGN Protocol to be particularly effective is in digital property transfers and token distribution. These processes are often complex, involving multiple steps, verifications, and approvals. With SIGN, much of this complexity is simplified. The infrastructure ensures that only verified participants can engage, and that all transactions follow the required rules.
For example, when distributing tokens, the system can automatically check whether a user meets specific criteria such as holding a certain credential or belonging to a particular region. If the conditions are met, the transaction proceeds. If not, it is blocked. This level of precision is difficult to achieve in traditional systems without significant overhead.
My personal approach to using the SIGN Protocol has been cautious and methodical. Rather than jumping straight into large transactions, I started with small test cases. These initial interactions allowed me to observe how the system behaves, how rules are enforced, and how verification processes work in real time. This hands-on experience has been invaluable in building my confidence.
As I became more comfortable with the system, I gradually began to scale my usage. The consistency and reliability of the protocol made it easier to trust larger transactions, knowing that the same rules and safeguards would apply. This step-by-step approach not only minimized risk but also provided a deeper understanding of the infrastructure.
Beyond individual use cases, I believe the broader implications of SIGN Protocol are even more significant. It has the potential to transform how governments, organizations, and communities manage digital identity, distribute resources, and enforce regulations. Imagine a world where aid distribution is transparent and fraud-resistant, where digital credentials are universally recognized, and where compliance is automatic rather than enforced after the fact.
Of course, no system is without challenges. As powerful as programmable compliance can be, it also raises important questions about governance and control. Who defines the rules? How are they updated? And how do we ensure that the system remains fair and inclusive? These are critical considerations that will shape the future of such technologies.
Despite these challenges, my overall experience with SIGN Protocol has been overwhelmingly positive. It offers a glimpse into a future where trust is not dependent on intermediaries but is instead built into the very fabric of digital interactions.
In a world where trust is increasingly difficult to establish, systems like SIGN Protocol provide a refreshing alternative. By combining transparency, automation, and privacy, it creates a foundation for a more secure and efficient digital economy. For me, it’s not just a tool it’s a step toward redefining how we think about trust, compliance, and ownership in the digital age.