i ran into this while double checking a transaction history that looked perfectly clean on chain but didn’t match what actually happened off chain. nothing malicious, nothing broken, just a mismatch between what was recorded and what it really represented.
and yeah, that felt weird.
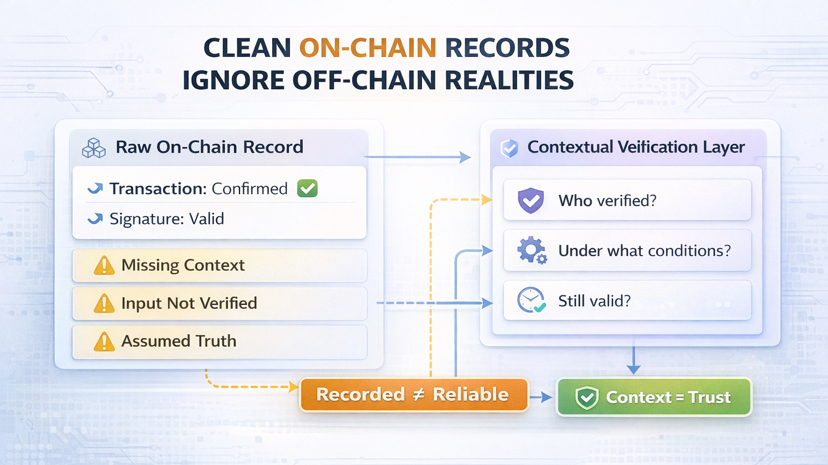
because we tend to assume that once something is on chain, it’s automatically reliable. it’s signed, it’s stored, it can’t be changed. so the natural conclusion is that it must be true.
but that’s not always the case.
what the chain really proves is that something was submitted and confirmed. it doesn’t prove whether the underlying information was correct in the first place. if the input is wrong, the record is still permanent.
that difference is easy to overlook.
i started thinking about how often this happens in practical situations. take something simple like a claim or a verification tied to a wallet. once it’s recorded, other systems might treat it as fact without questioning how that claim was created or whether the conditions behind it were valid at the time.
so you end up with something that is technically valid but contextually questionable.
not fake, not broken, just incomplete.
and that’s where things get tricky. because once that record exists, it becomes a reference point. other decisions can depend on it, even if the original input wasn’t fully reliable.
this is where the approach behind @SignOfficial started to make more sense to me. instead of relying only on the existence of a record, it focuses on attaching verifiable context to that record.
so it’s not just “this happened,” but also “this was checked under these conditions.”
that extra layer changes how information is interpreted.
because now you’re not blindly trusting the record itself. you’re looking at how it was created, who verified it, and under what circumstances it should be considered valid.
i tried to picture how this plays out in a real scenario. imagine a wallet presenting some form of verification to access a service. without context, the system just sees a record and accepts it. with additional context, the system can evaluate whether that verification actually applies to the current situation.
that reduces blind trust.
it doesn’t remove the need for verification, but it makes the verification more meaningful.
$SIGN fits into this flow by supporting how these contextual checks are maintained and referenced. instead of treating every on chain record as equally reliable, it helps systems differentiate between raw data and validated information.
and that distinction matters more than it seems.
because as more systems rely on shared data, the risk isn’t just incorrect information. it’s incorrectly trusted information.
once something is accepted as true, it influences everything that comes after it.
what stood out to me is how subtle this issue is. nothing crashes, nothing throws an error. the system keeps running, but it might be running on assumptions that were never fully verified.
and over time, those assumptions stack up.
you don’t notice it immediately, but the gap between what is recorded and what is actually true can grow if nothing checks it properly.
that’s why just storing data on chain isn’t enough.
it needs context.
it needs a way to understand not just that something exists, but why it should be trusted.
@SignOfficial approaches this by making verification part of the data itself instead of something handled separately. that keeps decisions closer to reality instead of relying on raw records alone.
it’s not a dramatic change, but it shifts how systems interpret information.
and once you start thinking about it, it’s hard to ignore the difference between something being recorded and something being genuinely reliable.
because those two things aren’t always the same.