$SIGN @SignOfficial #SignDigitalSovereignInfra
The line that bothered me was “Exception: 14.”
Not fourteen people. Not fourteen rows. Just fourteen, sitting there in the reporting pack like the category itself was supposed to do all the explaining.
Everything else looked beautifully behaved. Beneficiaries. Totals. Release schedule. Claimed. Pending. Completed. A neat little system of columns doing their best impression of control. Which, to be fair, is part of the whole point of TokenTable inside Sign. It is built to run rules-driven distributions, produce deterministic outputs, and give programs an audit trail that can actually be inspected later instead of reconstructed from spreadsheets and panic. The docs say that pretty plainly. Allocation tables define beneficiaries, amounts, schedules, claim conditions; once finalized they are versioned and immutable, and the system is meant to support public or restricted audit trails around the program.
Fine.
That all looked great from ten feet away.
Then I clicked into the fourteen.
This is where the reporting pack stopped feeling like transparency and started feeling like compression. Because “exception” was carrying three different kinds of pain at once. One row was a late eligibility dispute. One was a wallet mapping problem that had been manually held. Another had technically passed the credential side but was frozen because settlement timing slipped into the wrong window. Same bucket. Same label. Same clean report.
Which is such a TokenTable problem once a capital program matures a little.
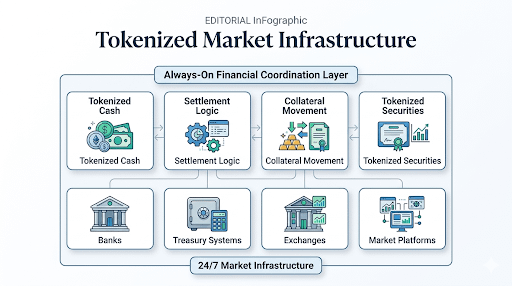
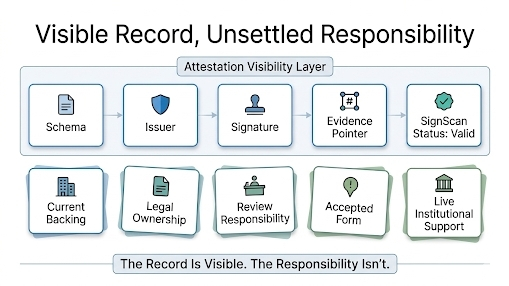
From the outside, standardized reporting makes the distribution legible. That is why people want it. Capital programs need schedules, outputs, reconciliation, evidence. Sign’s own architecture leans hard into that operational discipline: TokenTable handles the allocation and execution side, while Sign Protocol serves as the shared evidence layer for structured claims and linked records that can be queried later through indexers and APIs. Governance pages in the docs are equally blunt that sovereign-style deployments need audit exports, reconciled outputs, and investigation paths for exceptions and disputes.
But the category started flattening the program the second anyone tried to use the pack as understanding instead of overview.
That was the part getting under my skin.
Because the report was not lying. The rows really were exceptions. It just wasn’t telling you what kind of exceptions they were in a way that preserved the original stress of the workflow. A manual hold and a disputed identity binding do not mean the same thing. A clawback review and a delayed claim do not mean the same thing. An operator override and an unresolved credential mismatch definitely do not mean the same thing. But once they fall upward into reporting language, they start becoming administratively equivalent.
That is the quiet trade.
The reporting pack gets easier for treasury, auditors, supervisors, whoever is reviewing the program from a distance. Totals line up. Statuses aggregate. The distribution looks governable. Maybe it is. But the more standardized the categories get, the more the ugly local meanings disappear into tidy headings that travel better than the real story does.
So the pack comes out crisp. The program looks legible. And the hard part is that the people farthest from the workflow now feel best informed, while the only place the actual nuance still exists is buried down in the Sign evidence trail and the operator notes nobody wants to read unless something has already gone wrong.