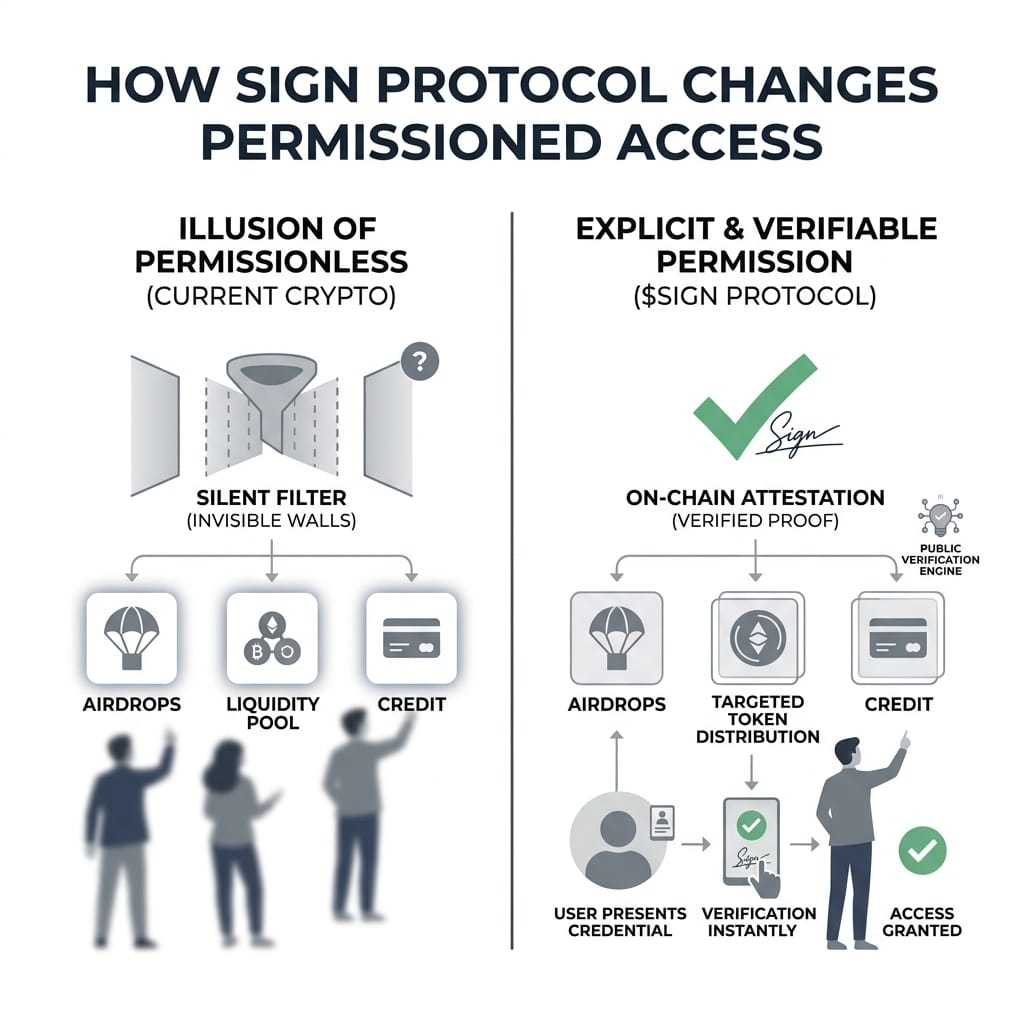
We were told crypto is permissionless.
But try getting into a real airdrop. Try accessing early liquidity. Try getting uncollateralized credit.
You’ll hit a wall.
Not a visible one.
A silent filter.
Someone, somewhere, is deciding if you qualify.
I don’t think crypto removed permission.
It just buried it under wallets and smart contracts so it felt open.
And that illusion worked… until you needed access.
What Sign Protocol does is uncomfortable at first. It doesn’t pretend permission doesn’t exist. It makes it explicit.
Every system runs on permission.
Permission runs on trust.
Trust runs on proof.
Most of crypto still handles this off-chain. Private databases. Internal scoring. Hidden logic. You don’t see it, but it controls everything.
Sign flips that.
Instead of asking, you present proof.
Instead of trusting a backend, you verify a signature.
I started seeing the shift when I looked at how Sign handles attestations.
An attestation is simple in idea. Someone signs a statement about you.
Not “this wallet exists” but “this wallet did something meaningful.”
Completed KYC.
Used a protocol early.
Did not Sybil farm.
That signature lives on-chain.
Now your wallet is no longer just a balance.
It becomes a history of verified claims.
And that changes access.
Airdrops stop being random.
Token distribution becomes targeted.
Communities gate based on proof, not guesswork.
What stands out to me is how little backend trust is required.
There’s no central API deciding eligibility.
No hidden scoring engine.
Just public keys and signatures.
If an issuer signs a credential, anyone can verify it.
If they don’t trust the issuer, they ignore it.
This creates a strange but powerful dynamic.
Trust shifts from platforms… to attestors.
Not all credentials are equal.
And that’s intentional.
You don’t trust the system blindly.
You choose which issuers matter.
Selective disclosure is where it gets more real.
You don’t need to expose everything.
You only show what is required.
Prove you’re KYC’d without sharing identity.
Prove eligibility without revealing behavior history.
That’s a very different model from current systems that over-collect data.
Here, proof becomes modular.
And that feels closer to how permission should actually work.
But I don’t think this is solved yet.
There are real questions.
What stops low-quality issuers from flooding the system with meaningless credentials?
What defines a “trusted” attestor over time?
If reputation becomes tokenized through credentials, it can also be gamed.
Sybil resistance improves, yes.
But it shifts the attack surface.
Now the focus is not fake wallets.
It’s weak attestations.
Designing good credentials becomes critical.
And that’s harder than it looks.
What most people are missing right now is the timing.
The issuer ecosystem is quietly expanding.
We’re starting to see real use cases.
KYC attestations.
Targeted token distribution.
Access control without centralized lists.
This doesn’t feel like a product launch phase.
It feels like infrastructure being positioned before demand explodes.
By the time people notice, the rules of access may already be rewritten.
I keep coming back to one thought.
Maybe the goal was never to remove permission.
Maybe that was always unrealistic.
Maybe the real goal is to make permission fair.
Transparent.
Verifiable.
That’s where Sign is heading.
In the next version of crypto,
you won’t ask for access.
You’ll prove you deserve it.
And the system won’t decide quietly.
It will show you exactly why.
The question is:
what kind of credentials will actually matter?