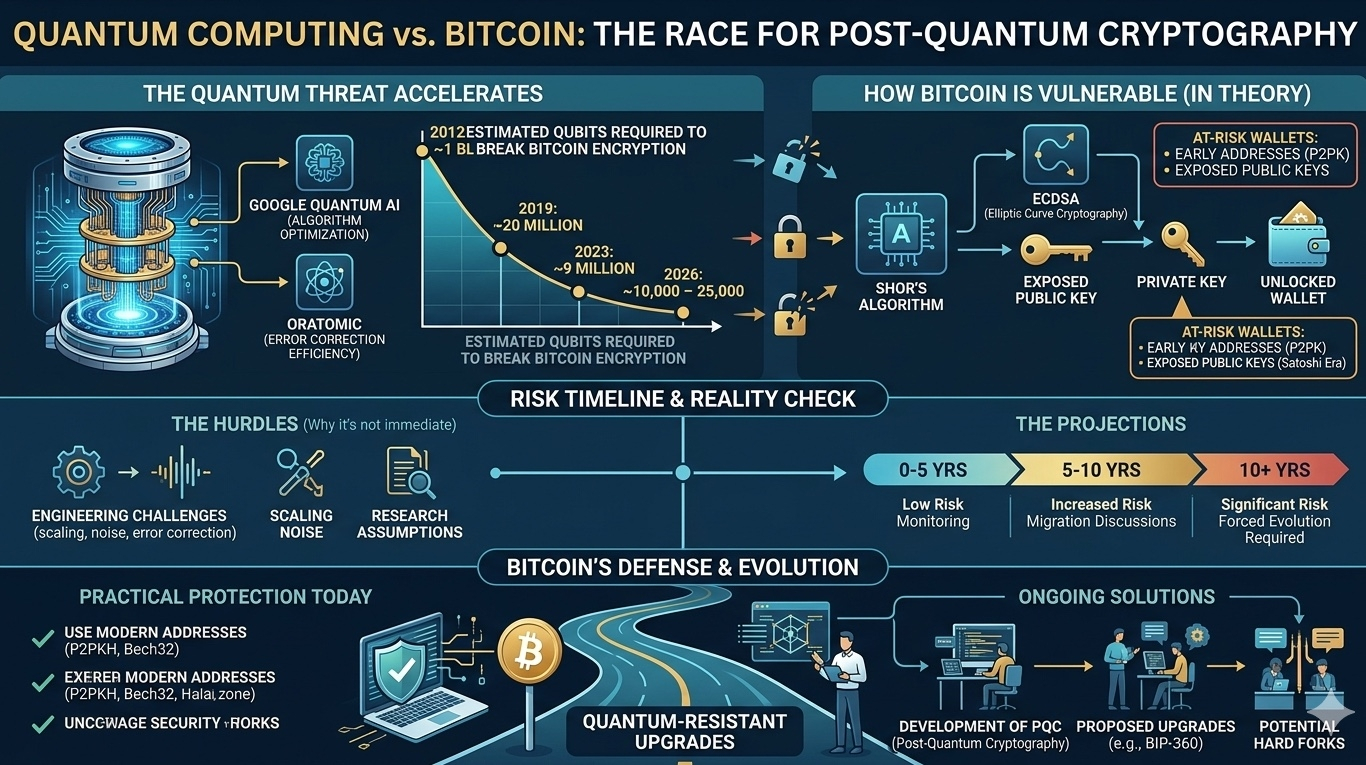
The idea that quantum computing could one day break Bitcoin’s cryptographic security has long been discussed—but recent developments from Google Quantum AI and Oratomic have brought this concern closer to reality.
This article breaks down what’s happening, what it means for Bitcoin, and how serious the threat actually is.
🔬 What Changed? A “Multiplicative Breakthrough”
Two major research papers triggered the latest concerns:
One from Google Quantum AI focused on optimizing quantum algorithms.
Another from Oratomic improved quantum error correction efficiency.
📉 Key Shift:
The estimated hardware required to break Bitcoin encryption dropped dramatically:
2012: ~1 billion qubits
2019: ~20 million
2023: ~9 million
2026: ~10,000 – 25,000 qubits
This isn’t just incremental progress—it’s exponential compression, making theoretical attacks far more feasible.
🔐 How Quantum Computers Could Break Bitcoin
Bitcoin relies on elliptic curve cryptography (ECC), specifically the ECDSA algorithm.
Quantum computers could exploit this using Shor's Algorithm, which can:
Reverse-engineer private keys from public keys
Potentially unlock wallets if public keys are exposed
🚨 Who Is Most at Risk?
Early Bitcoin wallets (including Satoshi-era holdings)
Addresses using pay-to-public-key (P2PK) format
Any wallet that has already revealed its public key on-chain
Estimates suggest millions of BTC could be vulnerable under future quantum conditions.
⏳ Timeline: How Urgent Is the Threat?
Previously, experts believed this risk was decades away. Now, projections are tightening:
Some researchers (like Justin Drake) estimate a 10% probability by 2032
Internal timelines suggest migration may be needed before 2029
Governments (like National Institute of Standards and Technology) are targeting full transition by 2035
👉 The key takeaway:
The threat is no longer theoretical—but it’s not immediate either.
🧠 Important Reality Check
Despite the hype, several limitations remain:
⚙️ Engineering Challenges
Current quantum computers are far below required scale
Error correction systems are still experimental
Combining different quantum architectures (Google vs Oratomic) is complex
⚠️ Research Assumptions
Some results are based on unproven large-scale implementations
Commercial and funding incentives may bias projections
👉 Bottom line:
We are closer—but not yet close enough for real-world attacks.
🛡️ How Bitcoin Is Preparing
The crypto ecosystem is not ignoring this risk.
🔄 Ongoing Solutions:
Development of post-quantum cryptography
Proposed upgrades like BIP-360
Potential hard forks to introduce quantum-resistant signatures
🔐 Practical Protection Today:
Modern Bitcoin addresses (like P2PKH, Bech32) already reduce exposure
Funds can be moved to safer address formats before quantum risk materializes
📊 Final Analysis: Should Investors Be Worried?
🟢 Short-Term (0–5 years)
No immediate threat
Bitcoin remains secure
🟡 Medium-Term (5–10 years)
Monitoring phase
Upgrade discussions will intensify
🔴 Long-Term (10+ years)
Real risk if no migration occurs
Quantum-resistant transition becomes essential
🧭 Conclusion
Quantum computing is advancing faster than expected—but so is the response from the crypto industry.
Rather than a “Bitcoin killer,” this is shaping up to be a forced evolution moment.
Just as the internet upgraded its security over time, Bitcoin is likely to adapt—and survive.
📌 Key Takeaways:
▪ Quantum breakthroughs are accelerating
▪ Bitcoin is vulnerable in theory, not yet in practice
▪ Migration to quantum-safe cryptography is inevitable
▪ The next decade will be critical
#Bitcoin #QuantumComputing #CryptoSecurity #CryptoEducation #ArifAlpha