@SignOfficial #SignDigitalSovereignInfra $SIGN
The part I kept staring at in the docs was not the eligibility logic. It was the handoff.
Because the identity side sounds clean when you first read it. The New ID System gives you the respectable ingredients: verifiable credentials, DIDs, selective disclosure, revocation, trust registries, cross-agency verification. Basically a way to prove that a specific person or entity qualifies without turning the whole process into raw-document chaos. Then TokenTable comes in later and does the capital part: who gets what, when, under which rules. It supports beneficiary identifiers like DIDs, addresses, or internal references, and it also supports direct distribution, beneficiary-initiated claiming, delegated claiming, and operator-led execution. Delegation can involve custodians, agencies, or service providers, and the docs say that delegation is policy-controlled and logged.
All of that reads very orderly until you stop reading it like architecture and start reading it like a person who has to explain where the money actually went.
Because this is where the stack gets emotionally messier than the diagrams want to admit.
The beneficiary qualifies through identity and eligibility evidence. Fine. That part is the clean part. The system can prove who met the conditions. But then the claim path itself may not be the same “surface” as the original subject who qualified. The docs never present that as a bug. Quite the opposite, TokenTable explicitly supports delegated claiming and operational delegation, while the New ID side is built around portable identity and verifiable credentials rather than some naive one-wallet-equals-one-person model. So the architecture is already telling you, very calmly, that “the qualified subject” and “the actor who executes or receives on their behalf” do not always have to collapse into the same thing.
And honestly that is the part I can’t stop turning over.
Because convenience sounds harmless until it becomes representation.
A custodian claims for a beneficiary. A service provider handles submission. A government sub-program operator executes on behalf of the person who qualified. A payout rail uses an address, account, or internal reference that is operationally useful but psychologically very different from the original identity proof. The docs support that flexibility because real systems need it. National-scale distribution would be much uglier if every entitled person had to personally operate every claim surface in exactly the same way.
But the second you accept that flexibility, the risk shifts.
Not away from the system. Just sideways.
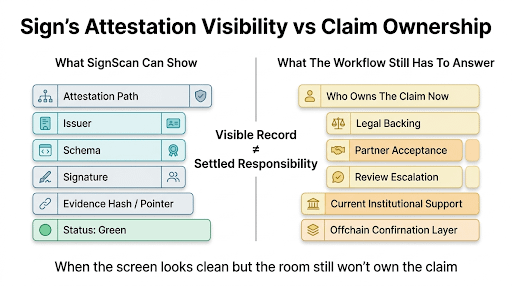
Now the hard question is no longer “did this person qualify?” The hard question becomes “who is allowed to act for that person, through which surface, under what policy, and with what audit trail if the acting surface and the qualifying subject are no longer the same thing?” That part is partly an inference from how the docs divide responsibilities, but it follows directly from the fact that Sign's New ID handles identity and eligibility while TokenTable separately handles claiming, delegation, and settlement. Once those are distinct layers, the seam between them becomes a real governance problem.
That is why this theme feels so natively Sign to me.
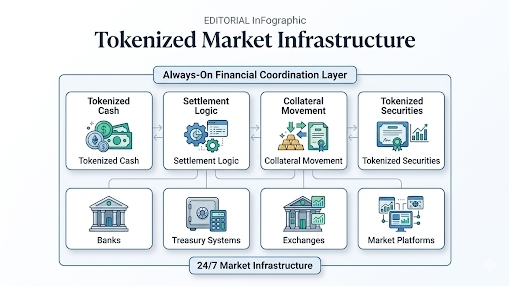
It is not generic “someone else claimed the funds” drama. It is the much more institutional problem that the stack is very good at preserving evidence that a subject qualified, while also being designed to permit delegated action and policy-controlled operators later in the flow. The docs even place TokenTable between New ID, New Money, and Sign Protocol itself: identity establishes who is eligible, Sign anchors the evidence, TokenTable executes the distribution, and the payment rail settles value. Which means the clean identity proof is only the beginning of the story, not the end of it.
So yeah, after reading it all, the thing that stays with me is this:
the stack is excellent at proving who qualified.
It gets much less emotionally clean once the system has to answer who is allowed to stand in for that person, which wallet or account is allowed to become the payout surface, and whether the convenience layer quietly turned into the place where the real distribution risk now lives.