i am writing this after the second alert.
02:13 a.m., the kind that arrives without drama but carries weight—an anomaly in wallet behavior, approvals fanning out faster than expected, nothing broken yet, but something leaning in the wrong direction. the dashboards didn’t scream. they rarely do. risk rarely announces itself; it accumulates quietly in permissions, in assumptions, in the distance between what a user thinks they signed and what the system actually allows.
the committee will review it in the morning. they always do. audit trails, session logs, scope boundaries. someone will ask if this was a throughput issue. it won’t be. it almost never is.
PIXEL doesn’t fail because it’s slow. it would fail, if it ever does, because something was allowed that should not have been.
there’s a persistent myth in this space: that speed is safety. that higher TPS, lower latency, faster confirmations somehow insulate systems from harm. i have yet to see evidence of that. fast systems amplify intent—good or bad. they reduce friction, but they also reduce the time available to notice when something is wrong.
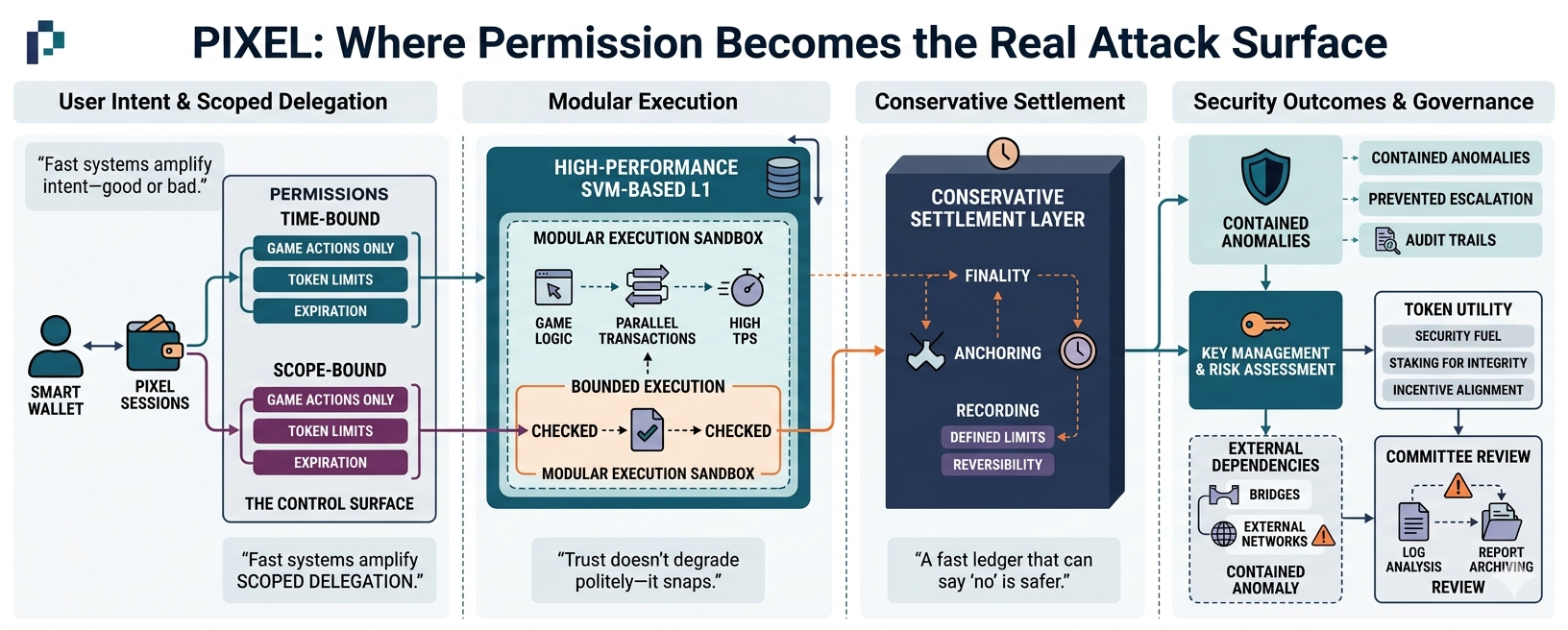
PIXEL is built differently, or at least it tries to be. it operates as a high-performance SVM-based L1, yes, but that descriptor hides the more important design choice: guardrails are not optional features, they are first-class constraints. execution is fast because it needs to be—games demand it—but execution is also bounded, scoped, and reversible within defined limits.
that distinction matters more than raw speed.
the architecture separates concerns in a way that most users will never see. modular execution sits above a conservative settlement layer. the settlement layer does not rush. it finalizes, records, anchors. above it, execution environments can move quickly, process interactions, handle game logic, but they do so within constraints that are explicitly defined and enforced. speed lives in the sandbox; finality lives elsewhere.
this is where most systems get uncomfortable. constraints slow down design. they introduce friction in development, in UX discussions, in product timelines. i’ve sat in those meetings—the wallet approval debates that stretch longer than they should. someone always argues for fewer prompts, fewer confirmations, less “user annoyance.” they’re not wrong, but they’re not complete either.
because every removed prompt is a removed checkpoint.
PIXEL Sessions exist precisely because of that tension. they are not a convenience feature; they are a control surface. time-bound, scope-bound delegation replaces the blunt instrument of persistent wallet approvals. instead of granting indefinite authority, users grant temporary, limited permissions that expire, that can be audited, that can be reasoned about.
“Scoped delegation + fewer signatures is the next wave of on-chain UX.”
it sounds like a product line, but it’s really a risk statement. fewer signatures do not mean less security if those signatures are better defined. a single, well-scoped delegation is safer than a dozen vague approvals scattered across contracts.
the logs from last night reflected that. the anomaly was contained not because the system was fast, but because the permissions were narrow. the session expired before the behavior could escalate. no assets were drained. no irreversible action occurred. the system didn’t need to react heroically—it simply enforced the boundaries that were already there.
this is the part that doesn’t make headlines.
when audits are conducted, they rarely focus on throughput metrics. they examine key management, permission models, upgrade paths, and failure modes. where can authority accumulate? where can it leak? who can sign what, and for how long? these questions are slower, less glamorous, but they are where systems actually break.
key exposure is still the most predictable failure in this industry. not block speed. not congestion. keys, and the permissions attached to them.
PIXEL’s native token appears in these discussions only briefly, almost incidentally. it functions as security fuel, yes, and staking ties participants to the system’s integrity. but staking is not a yield mechanism in this context—it’s a responsibility. it aligns incentives, but it does not replace discipline. no token model can compensate for poor permission design.
bridges complicate this further. they always do. assets crossing domains introduce external dependencies, and external dependencies introduce uncertainty. every bridge expands the attack surface beyond the system’s immediate control. this is not a flaw unique to PIXEL; it is a structural reality of interconnected networks.
and the truth that emerges, again and again, is simple:
“Trust doesn’t degrade politely—it snaps.”
there is no gradual erosion when a bridge fails, when a key is compromised, when an approval is abused. there is a before and an after. committees are formed after the fact, reports are written, lessons are extracted, but the event itself is binary.
this is why the obsession with TPS feels misplaced. speed is measurable, marketable, easy to compare. safety is quieter. it lives in constraints, in refusals, in systems that decline to execute when something falls outside defined bounds.
PIXEL, at its best, is not trying to be the fastest system in isolation. it is trying to be a system where speed operates within clearly enforced limits. where execution is modular, but settlement is conservative. where user experience improves not by removing safeguards, but by refining them into something more precise.
i expect the committee will close the alert by midday. the report will note that no funds were lost, that session constraints behaved as intended, that no escalation path was found. it will be categorized as a contained anomaly.
and then it will be archived.
but the real takeaway won’t be written explicitly. it rarely is. it sits between the lines, in the architecture itself:
a fast ledger that can say “no” is not slower.
it is safer.
and in systems like this, safety is the only performance metric that matters when everything else goes wrong.