I remember a time when every project promising privacy in crypto instantly caught traders’ attention. The idea sounded powerful—transactions hidden from the public eye, financial activity protected from surveillance, and a system where users could finally control their own data. Back then I assumed privacy itself was the innovation. If a network could hide information, it must be valuable. But after watching several projects fade, I started realizing something different. Many of them solved the privacy problem but created another one at the same time: verification. When data becomes invisible, it can also become harder to trust. That experience changed the way I evaluate privacy-focused networks. Now I pay less attention to the narrative and more attention to how a system proves that rules are still being followed.That mindset is exactly why the conversation around Midnight Network started catching my attention recently. Not because privacy is a new narrative in crypto—it definitely isn’t. But because the project raises a more interesting question. Can a blockchain keep data private while still proving that everything happening on the network is valid? That question sits at the center of Midnight’s design.
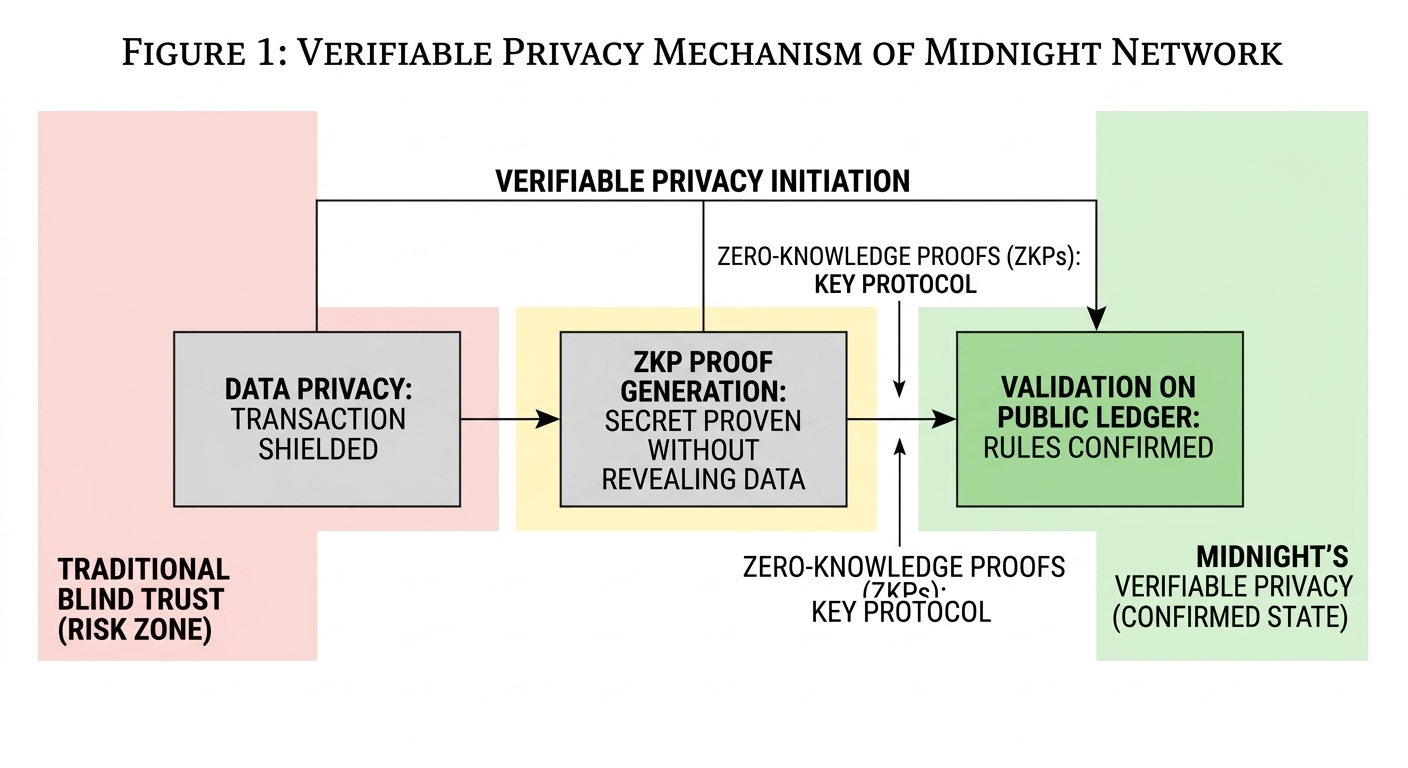
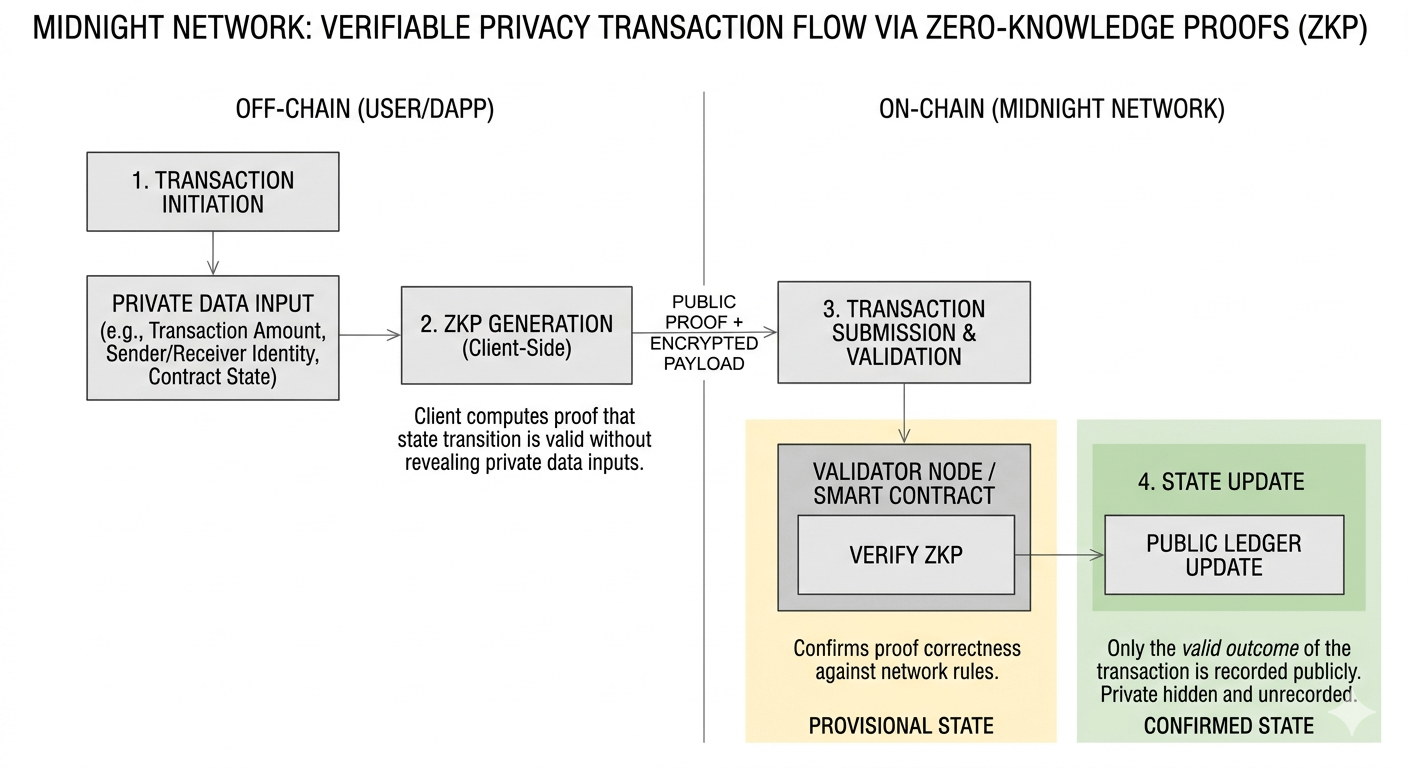
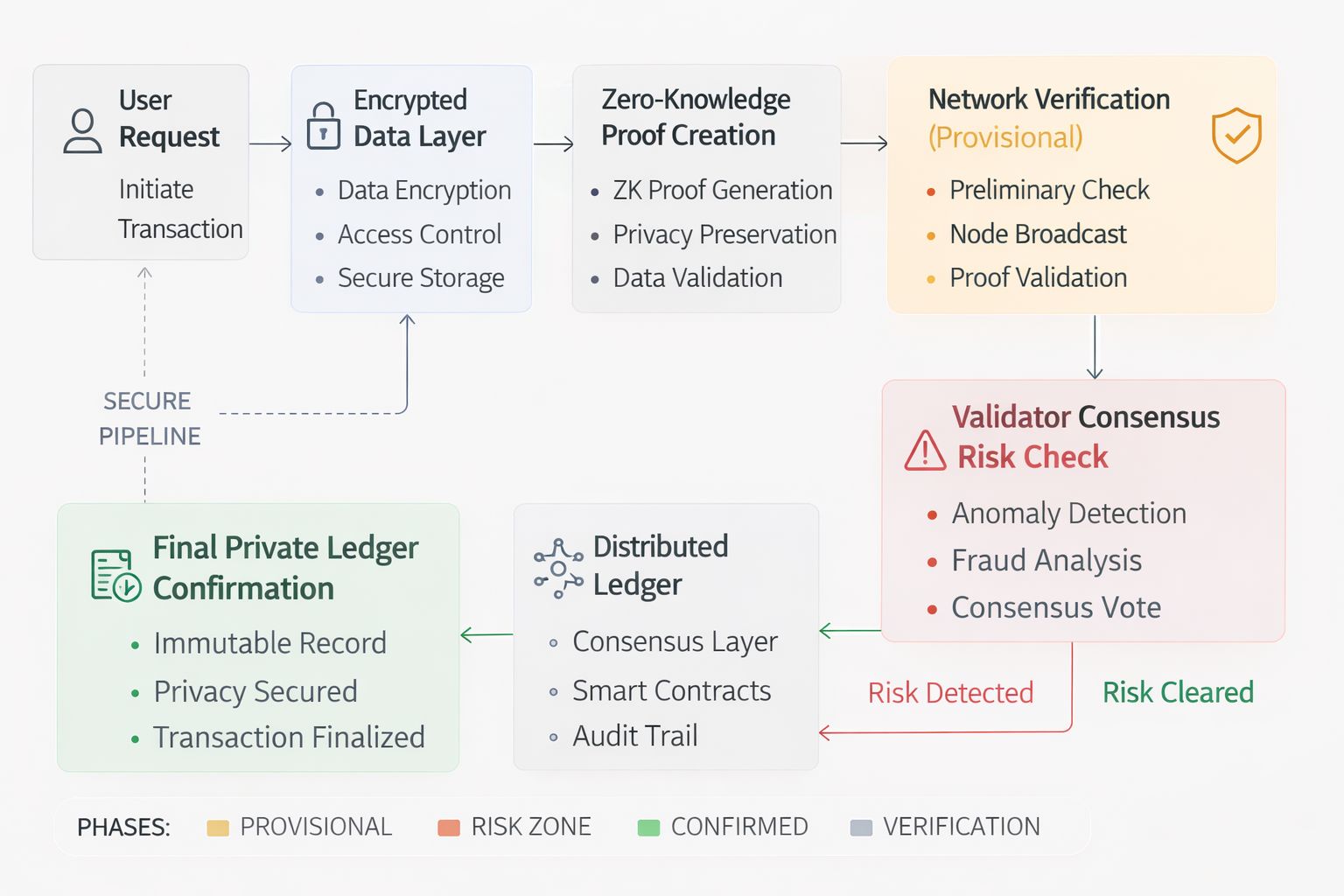
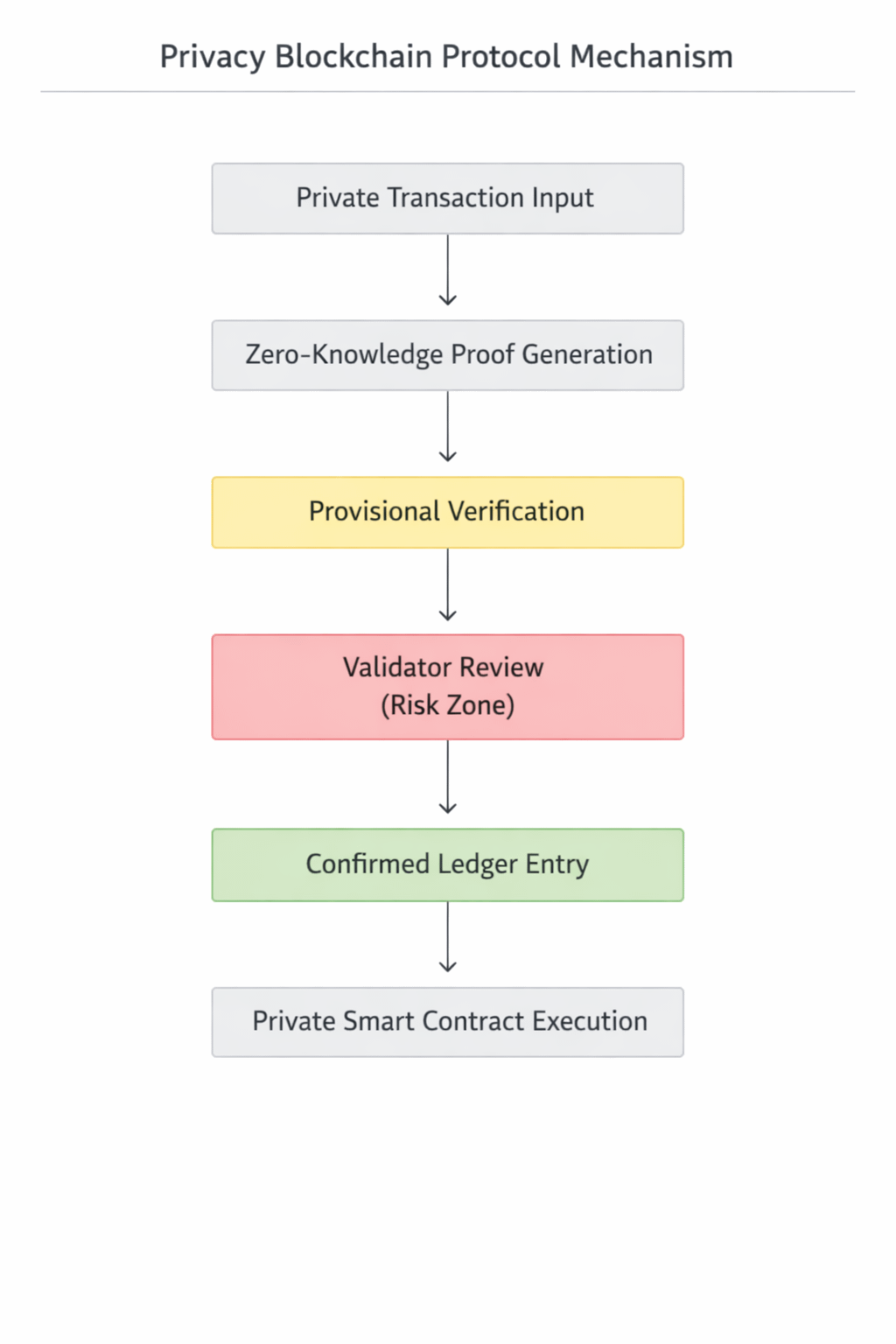
Instead of framing privacy as secrecy, the network focuses on something closer to verifiable privacy. The system is designed so sensitive information can remain hidden while the blockchain still confirms that transactions and smart contract actions follow the correct rules. If that balance works, it could solve one of the longest-running tensions in blockchain design.According to the project’s documentation, Midnight operates as a privacy-oriented blockchain environment that works alongside other ecosystems rather than competing directly with them. The protocol relies on cryptographic techniques known as zero‑knowledge proofs. While the mathematics behind them can be complex, the concept is surprisingly straightforward. A zero‑knowledge proof allows one party to prove that a statement is true without revealing the information behind that statement. Imagine proving that you have enough funds to complete a trade without revealing your exact balance. The system confirms the condition was satisfied, but the underlying data remains private.Midnight applies that idea to decentralized applications and smart contracts. Instead of forcing every piece of application data onto a transparent ledger, the network can verify outcomes while shielding sensitive details.This opens the door for applications where privacy actually matters—things like identity verification, financial processing, or enterprise systems where companies cannot publicly expose internal data.The network also separates its economic roles through two different resources.
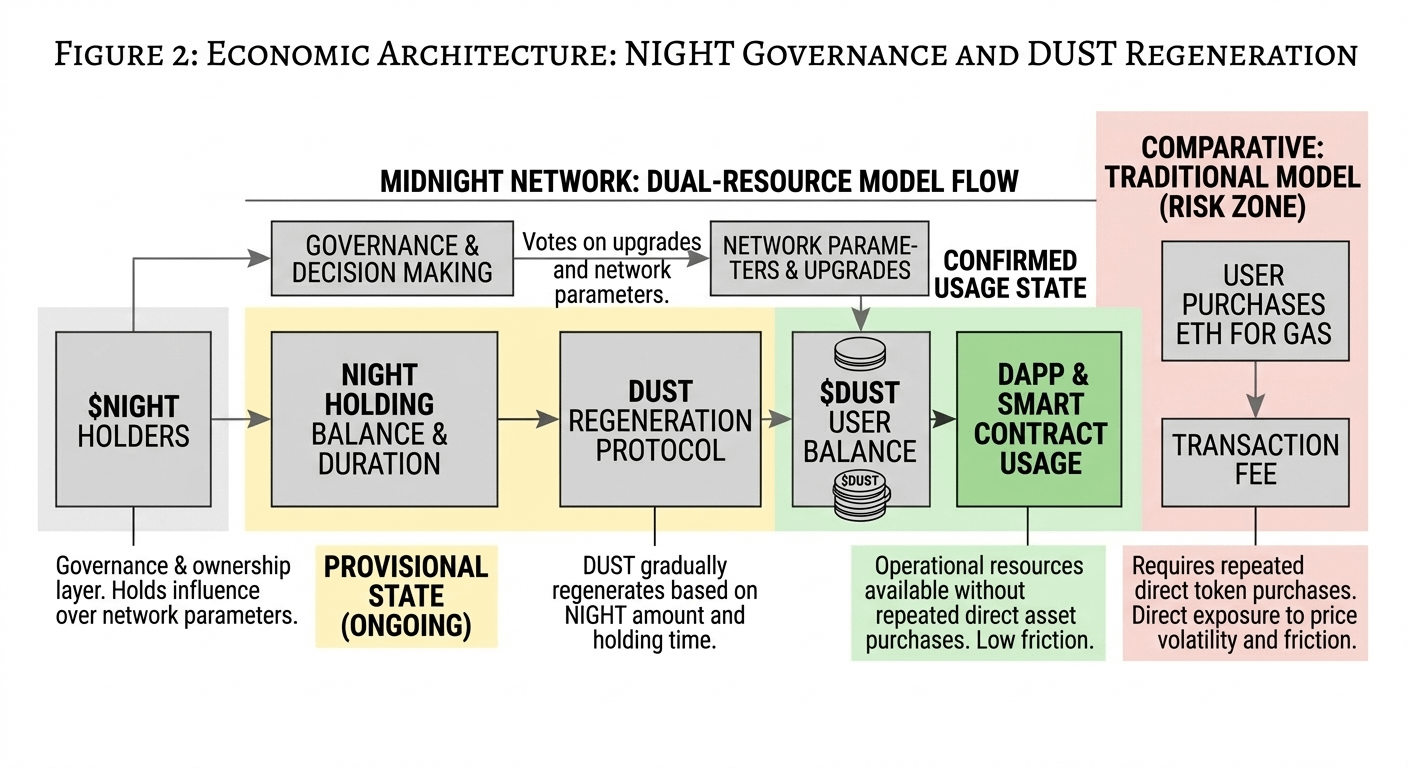
The main token, NIGHT, functions as the governance and ownership layer of the system. Holding it provides influence over network decisions and long‑term participation. Alongside it exists another resource called DUST, which is used to pay for transactions and computational operations within the network. DUST gradually regenerates based on the amount of NIGHT a participant holds. In practical terms, that means developers or applications can accumulate operational resources over time instead of forcing every user interaction to require a new token purchase. If the design works as intended, it could make decentralized applications feel closer to normal web services from a user experience perspective.The market has already started paying attention to this structure. As of early 2026, the NIGHT token trades in the lower cent range with active daily trading volume across several exchanges. Circulating supply remains relatively large compared with price, which is common for infrastructure tokens that are still early in their development cycle. Liquidity levels suggest that traders are already watching the project closely, while the ecosystem continues moving through staged development phases leading toward its mainnet rollout. Activity metrics have also shown gradual growth in developer participation and network addresses interacting with the system.Numbers like these usually tell me that a narrative has entered what traders often call the “discovery phase.” Liquidity and interest exist, but the long‑term valuation is still forming because the network’s real utility has not fully appeared yet.
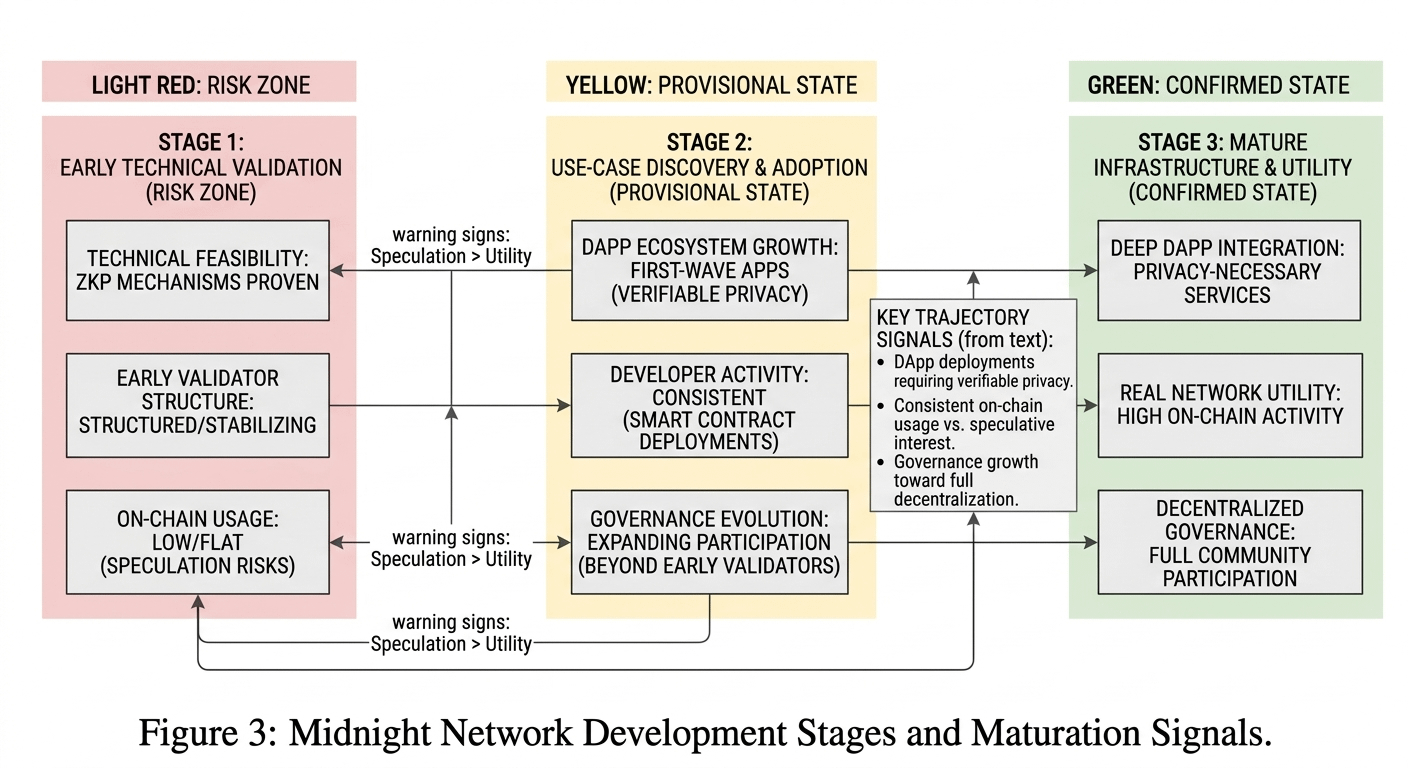
In other words, the market is trying to price the idea before the infrastructure has completely matured.But this is also where the real challenge begins to appear. The biggest test for Midnight isn’t whether privacy technology works. Cryptography has already proven that secure and private systems are possible. The real variable is adoption. Privacy alone does not automatically create demand for a blockchain network. Developers still need reasons to build applications that depend on selective data protection, and users need reasons to interact with those applications regularly.If those applications fail to appear, the network risks becoming another technically impressive platform that struggles to attract real usage. On the other hand, if developers start building services where privacy is not just helpful but necessary, the system could gain strong long‑term relevance. That’s the difference between infrastructure that survives and infrastructure that remains theoretical.Another part of the equation involves governance. Midnight is designed to move through stages before becoming fully decentralized. Early phases involve more structured validator arrangements intended to stabilize the system before governance expands to broader participation. That gradual approach can reduce early instability, but it also means the long‑term decentralization test will happen later. Traders watching the project will likely pay close attention to how governance evolves and whether community participation grows over time.
So what would make me more confident about Midnight’s trajectory? The first signal would be developer activity building applications that actually require verifiable privacy. The second would be consistent growth in smart contract deployments and real network usage rather than temporary spikes of speculative interest. A third signal would come from governance participation expanding beyond the early validator structure as the network matures.At the same time, there are warning signs that would make me more cautious. If trading activity continues rising but on‑chain application usage stays flat, that would suggest speculation is outpacing utility. Another concern would be if developer growth slows down before the ecosystem has produced meaningful applications that demonstrate why the network exists in the first place.So if you’re watching Midnight, it probably makes sense to look beyond short‑term price movements. In markets like this, the difference between narrative excitement and real infrastructure value often comes down to something simple: whether people keep building and using the system once the early attention fades.Crypto history has shown that narratives can appear quickly and disappear just as fast. What lasts longer are networks that solve problems developers and users repeatedly encounter. Midnight’s vision suggests a future where data can stay private without sacrificing trust in the system verifying it. The next phase of the project will reveal whether that balance becomes a practical tool for Web3 applications—or simply another interesting idea waiting for the right moment.
$AGT $NIGHT $G #night #LearnWithFatima #creatorpad @MidnightNetwork

