Introduction
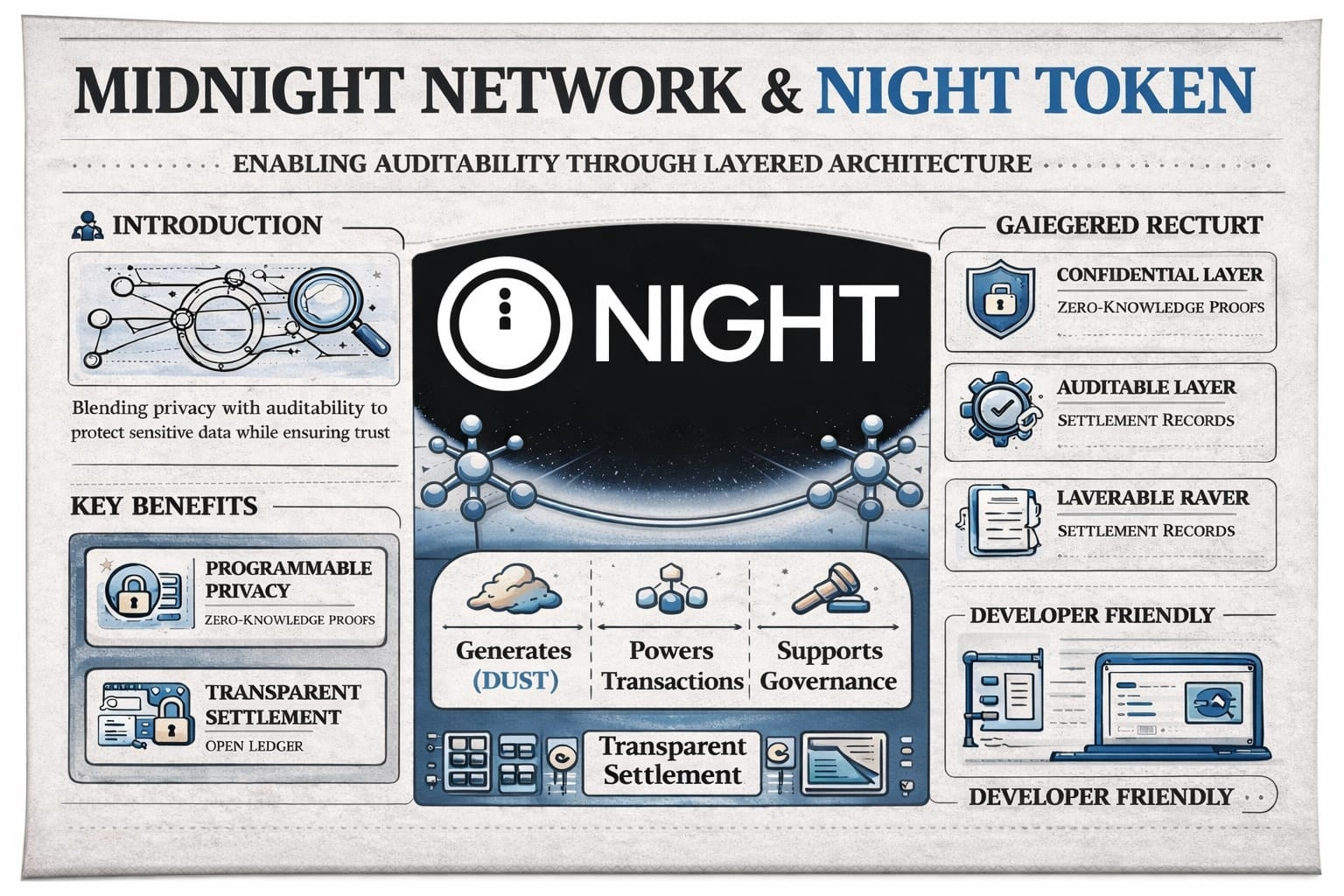
Blockchain has always wrestled with a core puzzle how do you let people check transactions without putting sensitive data on display?Open ledgers bring trust,but also risk exposing more than you want.Midnight Network tackles this by drawing a hard line between what’s private and what’s public.Right at the center is the NIGHT Token,keeping the system running and holding everything together.
Key Technology:Separating Confidentiality and Auditability
Midnight’s architecture splits the network into two layers:one that safeguards data,and another that looks after financial settlement.That clean split means you get privacy but don't lose trust.
On the confidential side,you find zero knowledge proofs protecting transaction data.The system can confirm what it needs to,while keeping the details hidden.Metadata like transaction specifics and DUST usage?That stays private,too.You get validation without exposure.
Meanwhile, on the auditable layer,the network keeps a public record.Here’s where the consensus engine runs and settlements get logged.Instead of storing raw data for anyone to see,this layer tracks results so anyone can check the outcome,but no one peeks behind the curtain.This design means Midnight can give privacy and auditability equal footing,not force you to pick between them.
Role and Utility of the NIGHT Token
NIGHT is the backbone of the Midnight Network. Its main job revolves around resource generation:hold NIGHT,and you generate DUST.DUST pays for transaction execution and smart contract calls.
This model breaks away from the usual fee systems in most networks.You don’t have to send tokens every time you interact with the system.Instead,you rely on resources you generate by holding NIGHT,making costs easier to predict and manage.
But NIGHT does more than just pay the bills.It helps coordinate the network,keeps incentives lined up,and supports governance making sure operations stay secure and efficient.
Ecosystem Overview
Midnight was built for developers who need both privacy and verifiability.You keep sensitive data safe,but still let others check real world outcomes.So whether you’re handling confidential transactions,secure computing,or trying to coordinate across different parties,Midnight gives you the tools.Programmable privacy isn’t just a buzzword here it lets decentralized applications go where they couldn’t before,especially when data protection really counts.
By combining privacy for data and openness in settlement,Midnight provides a playground for innovation.Developers don’t have to sacrifice clarity or secrecy they have space for both.
Conclusion
Midnight Network steps up to one of blockchain's toughest problems with a clean and thoughtful solution.By separating private data from public checks,the network is both auditable and confidential.The NIGHT Token is central driving operations,handling coordination,and making the resource model work.
As blockchain technology keeps moving forward,designs like Midnight’s might shape what comes next:systems where privacy and trust aren’t at odds,but actually work hand in hand.
For example, a decentralized oracle network like Pyth uses this structure to ensure that data providers are rewarded for accurate data (incentives) and that token holders manage the network's evolution