In Web3, privacy is one of those topics everyone agrees is important, yet very few projects approach it in a way that feels complete.
Most conversations stop at one idea: hiding data.
But realworld systems are rarely that simple.
Privacy is not just about secrecy anymore. It is about control.
Privacy Is Evolving Beyond Secrecy
Early blockchain systems were built on radical transparency. Every transaction, every interaction, every detail visible by design. This created trust, but it also introduced a new kind of exposure.

Over time, the industry tried to correct this by introducing privacyfocused solutions. But many of those solutions leaned too far in the opposite direction, treating privacy as complete invisibility.
The result is a false choice:
either everything is visible
or everything is hidden
That binary approach does not work for real users or real businesses.
This is where Midnight Network starts to feel different.
A More Practical View of Privacy
Midnight does not treat privacy as a layer added on top. It treats it as part of the system’s architecture.
Instead of asking users to hide everything, it asks a better question:
What actually needs to be hidden, and what still needs to be proven?
This is where zeroknowledge technology becomes important.
Through zeroknowledge proofs, information can remain private while still allowing verification. Something can be confirmed as true without revealing all the underlying data.
That changes the conversation completely.
It moves privacy from secrecy to selective disclosure.
Control Instead of Darkness
Midnight’s design reflects a more mature understanding of how Web3 should work.
Users and builders should not have to choose between:
full transparency that exposes everything
or total darkness that breaks usability
Instead, Midnight creates a balance between:
confidentiality protecting sensitive information
verifiability proving what actually matters
This balance is what makes the system feel usable beyond theory.
Where This Model Starts to Matter
The real strength of Midnight becomes clearer when you look at practical use cases.
Not abstract ideas but real scenarios where privacy and proof both matter.
Private identity
People can prove who they are without exposing unnecessary personal data.
Sensitive payments
Transactions can remain confidential while still being valid and auditable.
Business logic
Companies can run processes onchain without revealing internal strategies or data.
Smart contracts
Logic can execute transparently, while inputs remain protected.
Protected on-chain activity
Users interact with blockchain systems without turning their entire history into public records.
These are not edge cases. These are everyday needs if blockchain is meant to support real-world systems.
Rethinking Trust
A common misconception is that privacy reduces trust.
Midnight challenges that idea.
It does not remove trust it changes how trust is created.
Instead of relying on full exposure, trust is built through proof.
You do not need to see everything.
You only need assurance that what matters is true.
This approach feels closer to how trust works in the real world: we rarely reveal everything, but we still prove enough.
A Thoughtful Network Economy
Another interesting aspect of Midnight is how it approaches its network economy.
Rather than tying everything to a single token role, the design separates:
the core token function
and the private resource used to power network activity
This is a subtle but important decision.
It suggests that the system is being built with utility in mind, not just speculation. By separating these roles, Midnight creates space for:
more predictable usage models
better alignment between cost and function
reduced pressure on the system to behave like a purely financial asset
It feels like an attempt to support longterm use rather than shortterm attention.
Built for Builders, Not Just Narratives
There is a noticeable difference in how Midnight presents itself.
It does not feel like a concept chasing trends.
It feels like infrastructure being prepared for builders.
The focus appears to be on:
ecosystem readiness
practical tooling
real deployment scenarios
Privacy is not treated as a headline feature. It is embedded into how the system works.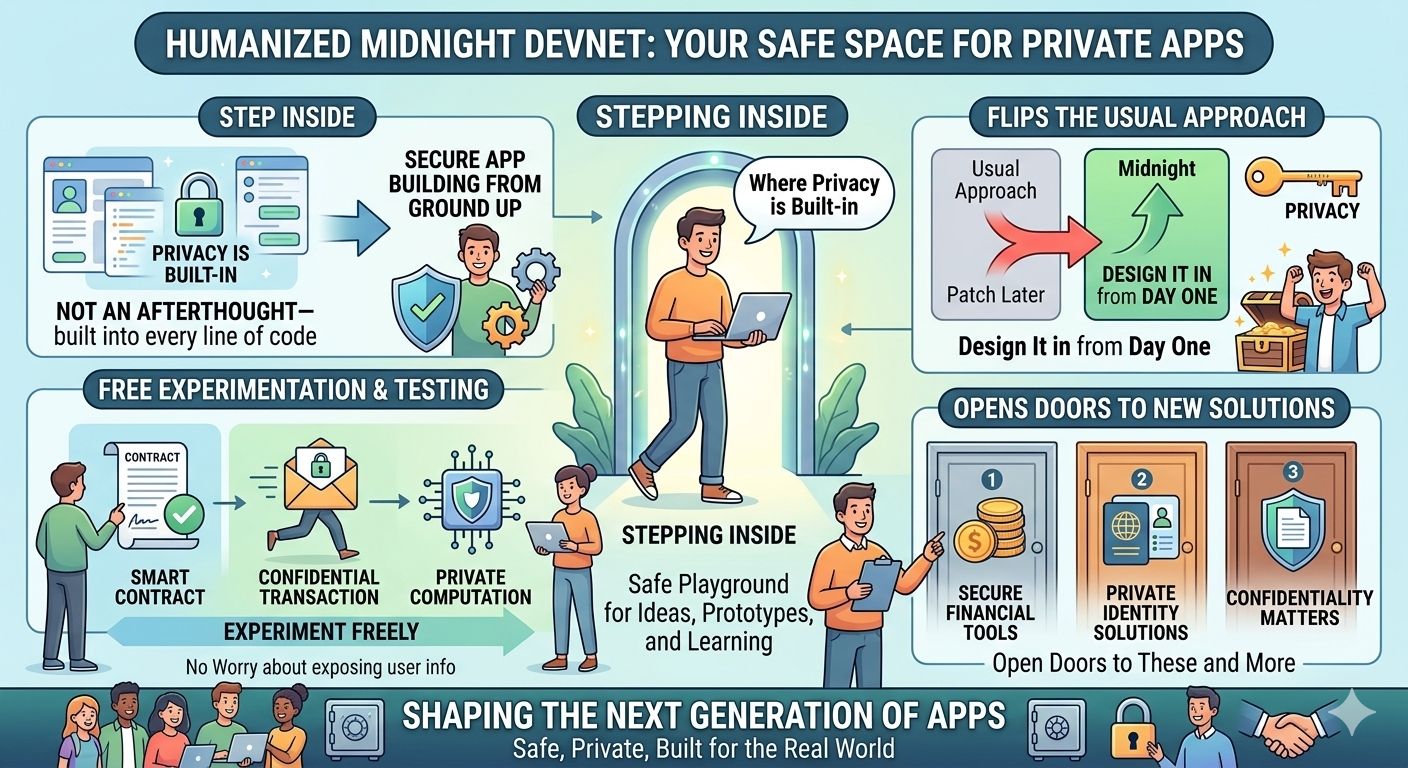
That distinction matters.
Why This Idea Connects on a Human Level
Beyond all the technical language, the reason this approach resonates is simple.
People want control.
People want ownership of their data
People want privacy without losing access or functionality
Builders want tools that protect users without breaking systems
Midnight aligns with these needs without forcing trade-offs that feel unrealistic.
A More Mature Direction for Web3
Midnight gives the impression of a network designed for where Web3 is going, not where it started.
It acknowledges that:
transparency alone is not enough
privacy alone is not enough
the future lies somewhere in between
By combining confidentiality with verifiability, it offers a model that feels closer to realworld requirements.
Final Thoughts
Strong ideas are important, but they are never enough on their own. Execution, adoption, and ecosystem growth will ultimately determine whether Midnight succeeds.
Still, what makes Midnight stand out is not hype or narrative repetition.
It is the fact that it is building around a real structural need in crypto: how to protect information without breaking trust.
That is a problem many prefer not to address directly.Midnight does.