
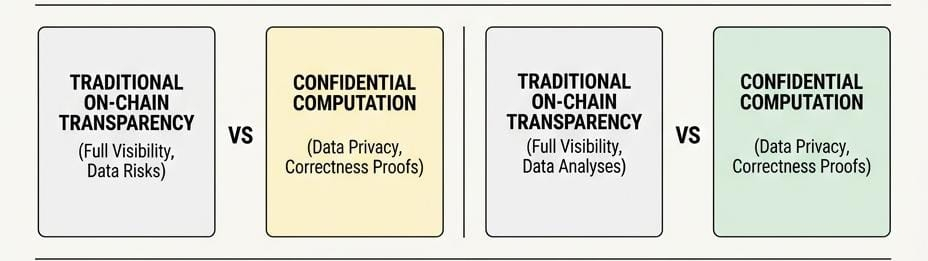
I remember a period when I relied heavily on on-chain transparency to guide my decisions. I would track wallets, follow large transfers, and assume that visibility meant safety. The logic felt solid at the time. If everything was open, then risks should be easier to detect.
Over time, that belief started to weaken. I noticed that transparency often created noise instead of clarity. Wallet movements could be interpreted in multiple ways, and sometimes the most important information was not visible at all. At the same time, I began to realize how exposed users actually were. Every action left a trace that could be analyzed, profiled, and even exploited.
That shift forced me to rethink what trust really means in crypto systems. It is not just about seeing everything. It is about being able to verify what matters without exposing what should remain private. That is the lens I now use when evaluating new projects, and it is exactly what led me to take a closer look at Midnight.
That experience is why Midnight caught my attention, although not for the reasons that usually drive market excitement. Privacy as a narrative is not new, and many projects have approached it in ways that limit usability or reduce transparency to a point where trust becomes difficult.
What makes Midnight more interesting is the question it raises rather than the claim it makes. Instead of asking how to hide data, it asks whether data can remain private while still being provably correct. This is a more demanding problem because it requires both confidentiality and verification to coexist without weakening each other.
The real question then becomes whether this system can move beyond theory and operate in environments where both properties are required at the same time. If it can, it introduces a different model for how blockchain systems handle sensitive information. If it cannot, it risks becoming another example of technology that works in isolation but struggles in real use.
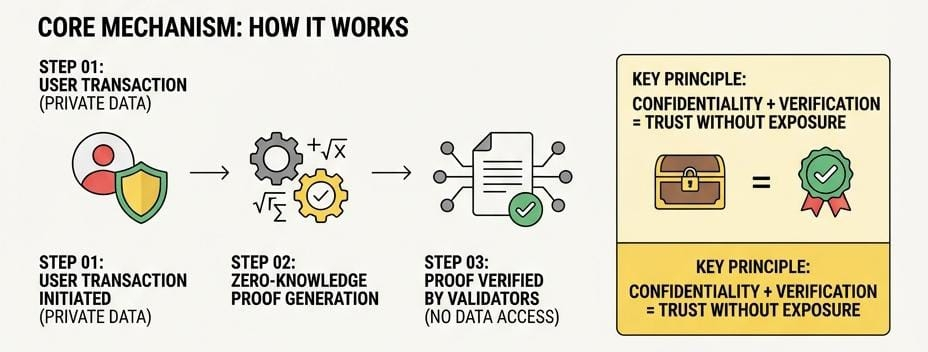
Midnight is built around the idea of confidential computation, where the execution of logic does not require public exposure of the underlying data. This is achieved through zero knowledge based cryptographic methods that allow a participant to prove that a statement is valid without revealing the inputs behind it.
In practical terms, a transaction or computation on Midnight produces two outputs. One remains private and contains the actual data, while the other is a proof that confirms the operation followed the correct rules. Validators in the network do not need access to the private data itself. They only need to verify the proof, which is designed to be mathematically sound and resistant to manipulation.
This design changes the role of validation. Instead of re executing visible data, the network verifies correctness through proofs. That reduces the need for full transparency while maintaining trust in the system. It also allows applications to handle sensitive information such as financial records, identity attributes, or proprietary data without exposing them on a public ledger.
A useful way to think about this is to compare it with traditional financial auditing. A company does not publish every internal transaction publicly, yet it can provide audited statements that prove compliance and accuracy. Midnight attempts to bring a similar structure on chain, where verification does not require full disclosure.
The token within this system supports the economic layer that keeps it functioning. It is used to pay for computation, incentivize validators who verify proofs, and align participants who contribute to network security. Over time, its role becomes tied to how much meaningful activity the network processes rather than how much attention it receives.
What makes this approach significant is that it expands the type of applications that can exist on a blockchain. Systems that require confidentiality are often forced off chain or into hybrid models. Midnight is attempting to bring those use cases fully on chain without sacrificing privacy.
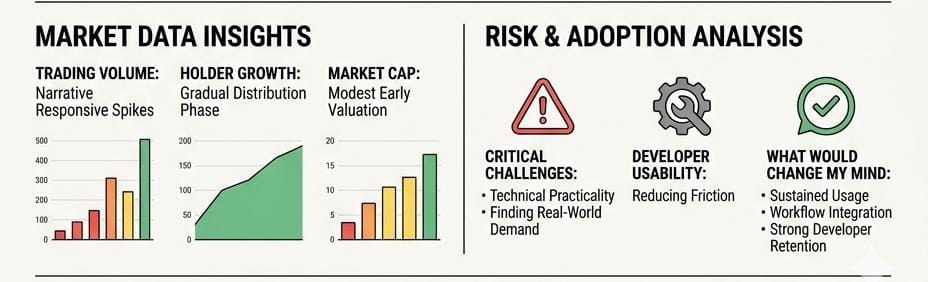
Market behavior around Midnight reflects an early stage of recognition rather than full conviction. The token associated with the network has experienced periods of increased activity, often aligned with ecosystem developments and broader discussions around privacy infrastructure.
Trading volume has shown the ability to expand during key moments, which suggests that the market is responsive to new information. At the same time, this activity has not yet stabilized into a consistent pattern, indicating that participation is still influenced by narrative cycles rather than steady usage.
Holder growth appears gradual, which can be interpreted as a slow distribution phase rather than rapid speculative concentration. This type of pattern is often seen in projects that are still forming their identity in the market. Market capitalization remains relatively modest compared to more established networks, reinforcing the idea that Midnight is still being evaluated rather than fully priced.
Taken together, these signals suggest that the market is aware of the concept but has not yet reached a clear conclusion about its long term value. That uncertainty creates both opportunity and risk, depending on how the underlying system develops.
The central challenge for Midnight is not the validity of its cryptographic approach but the practicality of its adoption. Privacy preserving systems often face a gap between technical capability and real world usage. The difficulty lies in turning a strong concept into something that people repeatedly rely on.
For Midnight, the key variable is whether developers build applications that genuinely require confidential computation. Without that layer, the network risks becoming a solution in search of a problem. Privacy on its own does not create demand. It becomes valuable only when it solves constraints that users cannot address elsewhere.
There is also a subtle tradeoff between usability and complexity. Systems that rely on advanced cryptography can introduce friction for developers and users. If building on the network requires significantly more effort than alternatives, adoption may slow despite the advantages it offers.
Another factor is economic alignment. Validators and participants must find the incentives attractive enough to remain active over time. If network activity does not grow in a way that supports these incentives, the system can struggle to maintain stability.
If Midnight succeeds in overcoming these challenges, it could position itself as infrastructure for a category of applications that cannot function properly on fully transparent systems. If it fails, it may remain technically impressive but underutilized.
My confidence in Midnight would increase if I begin to see clear evidence of sustained usage rather than isolated spikes of activity. This would include applications that are not only deployed but actively used in ways that demonstrate the necessity of privacy features.
I would also pay close attention to how developers interact with the system. If the tools and environment allow builders to create without excessive friction, it increases the likelihood of long term ecosystem growth. Developer retention often reveals more about a protocol than short term market performance.
Another important signal would be integration into workflows where confidentiality is not optional. If businesses or platforms begin to rely on Midnight for operations that require both privacy and verification, it would validate the core thesis behind the project.
On the other hand, I would become more cautious if activity remains largely driven by speculation or if developer engagement starts to decline. Those patterns usually indicate that the underlying value proposition has not translated into consistent demand.
If there is one thing I have learned from watching emerging infrastructure, it is that early narratives rarely determine long term outcomes. What matters is whether a system becomes useful enough that people return to it without being prompted.
With Midnight, the focus should not be on how advanced the technology sounds but on whether it becomes part of real workflows where privacy and verification are both required.
In this space, the line between potential and reality is often defined by usage. The projects that endure are not the ones that introduce new ideas, but the ones that make those ideas necessary.
@MidnightNetwork #night $NIGHT
