In the early days of blockchain, the dream was total transparency. The public ledger was hailed as the ultimate antidote to the black box of traditional finance. However, as the industry matured, a stark reality emerged: total transparency is often incompatible with the needs of the real world. Businesses cannot expose their trade secrets, individuals cannot broadcast their entire financial histories, and regulated institutions cannot ignore data protection laws.
Enter the Midnight Network, a fourth generation blockchain designed to solve this privacy trilemma through the lens of Rational Privacy. By leveraging zero knowledge proofs (zk-SNARKs) and selective disclosure, Midnight allows for a world where you can prove the truth without exposing the data. But a protocol this powerful cannot be governed by a single entity. The journey of @MidnightNetwork is not just a technical one; it is a meticulously planned transition toward a global, open utility, stewarded by the Midnight Foundation.
🔰 The Midnight Foundation: Guardians of an Open Utility.
At the heart of the network’s ecosystem sits the Midnight Foundation. Unlike a traditional corporate board, the Foundation is designed as an independent steward whose primary mandate is to ensure the network remains a neutral, accessible resource for the world. Its role is to bridge the gap between the initial research driven development by Input Output Global (IOG) and a future where the community is the sole driver of the protocol.
The Foundation’s mission is built on three pillars: stewardship, stability, and democratization. By managing the network’s treasury and ecosystem grants, the Foundation incentivizes developers to build on Midnight, specifically targeting high utility applications in DeFi, identity, and supply chain. More importantly, the Foundation acts as a buffer against centralization. By guiding the initial governance parameters, it ensures that no single stakeholder not even its creators can monopolize the architecture of freedom.
🔰 Stability Through Innovation: The NIGHT and DUST Tokenomics.
To ensure Midnight remains a reliable utility for enterprises and developers, the network employs a sophisticated dual token model. This system is designed to solve one of the greatest barriers to blockchain adoption: cost volatility.

A. NIGHT: The Engine of Governance.
The NIGHT token is the unshielded, native utility token of the network with a fixed supply of 24 billion. It represents the capital and governance weight of the ecosystem. Holders of $NIGHT are more than just investors; they are the security providers and decision makers. NIGHT is used for consensus, rewarding block producers (including Cardano Stake Pool Operators), and voting on critical protocol upgrades.
B. DUST: The Renewable Fuel.
However, unlike most blockchains where you spend your core asset to pay for fees, Midnight introduces DUST. Holding NIGHT automatically and continuously generates DUST, a non-transferable, shielded resource used to pay for transaction execution and smart contract interactions.
This token resource model is revolutionary for long term stability. Because DUST is generated passively by NIGHT, a business can calculate exactly how much NIGHT it needs to hold to run its operations for free in perpetuity. This decouples the operational cost from the market price of the governance token, protecting dApp developers from the gas wars and price spikes that plague other Layer 1s. This ensures Midnight remains an open utility as predictable as electricity or water.
🔰The Roadmap: Four Phases to Decentralization.
The path to full decentralization is not a sprint; it is a series of gates designed to ensure the protocol is battle tested at every stage. Midnight follows a Hawaiian themed roadmap Hilo, Kūkolu, Mōhalu, and Hua, each representing a shift in power from a centralized core to a distributed community.
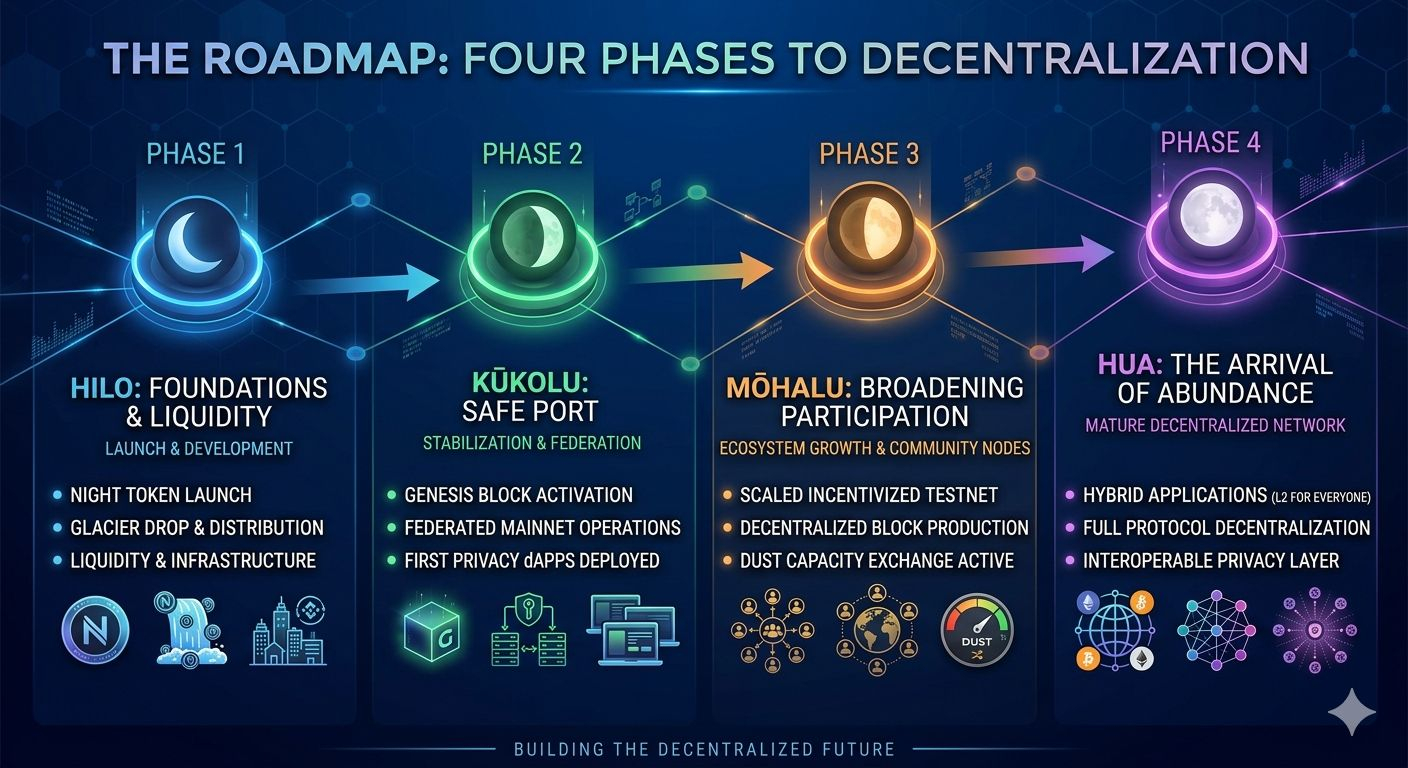
🔸Hilo (The New Moon): This initial phase focused on the launch of the NIGHT token and establishing liquidity. It brought together the first wave of community members through the Glacier Drop, one of the largest and most inclusive token distributions in history, ensuring that the ownership of #night was broad and decentralized from day one.
🔸Kūkolu (The Waxing Crescent): In this stage, the network moves to a federated mainnet. Here, early privacy enhanced dApps go live. The network is operated by a mix of IOG and external enterprise partners (including Fortune 500 participants), providing a stable environment for builders to stress test their Compact (TypeScript based) smart contracts.
🔸Mōhalu (The First Quarter): This is the decentralization trigger. During Mōhalu, the network transitions from a federated model to an incentivized testnet, onboarding Cardano’s vast network of Stake Pool Operators (SPOs). The DUST Capacity Exchange is also activated here, allowing users who have excess DUST to provide it to those who need it, creating a self sustaining internal economy.
🔸Hua (The Full Moon): The final destination. Midnight reaches its Full Moon by hard forking into its final consensus protocol. At this point, all block production is handled by the community, the bridge infrastructure is fully operational, and Midnight becomes a multichain privacy layer. It stops being a standalone chain and starts functioning as a Privacy L2 for everyone bringing rational privacy to Ethereum, Solana, and beyond.
🔰 Conclusion: A Future Built on Trust, Not Exposure
The Midnight Foundation’s long term vision is to create a world where privacy is the default, not a luxury. By separating the value of the network (NIGHT) from the cost of using it (DUST), and by following a disciplined path toward full decentralization, Midnight is building more than just a blockchain; it is building the infrastructure for a more honest digital age.
As the network matures through the Hua phase, the Foundation’s role will eventually recede, leaving behind a truly decentralized, self governing utility. In this future, the architecture of freedom will belong to the people, ensuring that our commerce, associations, and expressions remain our own protected by the power of zero-knowledge and the stability of a community driven network.