Most of crypto talks about moving value.
Very little of it knows how to prove anything.
That gap is starting to matter more than people want to admit.
Crypto has spent years obsessing over execution speed, modular stacks, new virtual machines, and the latest performance theater disguised as innovation. Meanwhile, one of the more basic problems has remained strangely unresolved: how do you prove that something is true, in a way that is portable, verifiable, and not trapped inside a centralized database?
This sounds abstract until it stops being abstract. A user wants to prove they belong to a community without exposing their full identity. A builder wants to verify that a wallet completed KYC somewhere else without rebuilding the same compliance flow. A protocol wants to reward real contributors instead of sybil farms. An institution wants credentials and approvals that can survive across chains and applications. In each case, the same friction appears: crypto moves assets well enough, but it still struggles to carry trust in a usable form.
That weakness has practical consequences. Users repeat the same verification steps across platforms because nothing is portable. Builders keep stitching together identity and reputation systems with custom logic because there is no common layer that everyone actually uses. Projects want “onchain reputation,” but often end up with crude snapshots, leaderboards, and spreadsheets wearing a decentralized costume. The result is predictable: more fragmentation, more duplicated effort, and more trust pushed back into private databases and backend dashboards.
There is a common belief in crypto that if something matters enough, the market will naturally produce a decentralized solution for it. That belief has always been a little too convenient. In reality, markets often optimize for what is easy to speculate on, not for what is structurally important. Tokens appear faster than standards. Liquidity arrives before legitimacy. Infrastructure for proof, identity, and attestation tends to be ignored until the system starts demanding it.
That is the more interesting lens for looking at SIGN.
SIGN is not really about another app, another chain, or another attempt to financialize attention. It is better understood as an effort to build a trust layer for the internet and for crypto specifically: a way to create, store, and verify attestations across different environments. Not trust in the sentimental sense. Trust in the operational sense. Proof that a statement, credential, or claim came from a known issuer and can be verified without relying entirely on one company's server.
That matters because the internet has no native memory for credibility. It has content, accounts, and databases, but very little in the way of portable proof. Crypto improved ownership. It did not fully solve verification. SIGN seems to be built around that gap.
In simple terms, an attestation is a signed claim. It can say a wallet belongs to a certain user, that someone completed an action, that a credential was issued, that a contribution happened, that an entity is approved, or that a relationship exists. The point is not the wording. The point is that the claim can be checked.
At a high level, SIGN works like this:
It lets issuers create attestations, which are signed records tied to a person, wallet, or entity.
These attestations can be structured using schemas, so different applications can understand and verify the same type of claim.
They can be stored in ways that balance cost, accessibility, and privacy, rather than forcing everything into one rigid model.
Applications can read and use those attestations across ecosystems, which makes proof more portable than the usual platform-specific badge system.
The $SIGN token appears to sit around network incentives, participation, and ecosystem coordination rather than pretending to be something mystical.
That is the basic shape of it. Not magical. Just useful, if it works and if enough people decide they need it.
There is a more uncomfortable point here. Crypto has always claimed to reduce reliance on trust, but what it really does is rearrange where trust lives. Instead of trusting banks, users trust wallet software. Instead of trusting institutions, they trust multisigs, signers, frontends, and protocol teams. Instead of eliminating social trust, crypto often hides it beneath technical language.
Attestations expose this contradiction. A system can be cryptographically clean and still socially ambiguous. You can verify a signature and still not know whether the issuer deserves confidence. You can create decentralized identity rails and still end up reproducing old power structures under new branding. The machinery of proof does not remove politics, status, or incentives. It just makes them more legible.
That is why projects like SIGN are worth watching, but also why they should be viewed carefully. The optimistic version is straightforward: attestations become a common primitive for identity, credentials, community membership, reputation, and compliance. Users carry proof across applications. Builders stop reinventing the same verification layer. Crypto becomes slightly less clumsy when it interacts with the real world.
The less optimistic version is also plausible. Attestations become another fragmented standard. Adoption remains narrow. Competing systems dilute network effects. Issuers become the new gatekeepers. Privacy trade-offs become harder than the pitch suggests. And the token, like so many infrastructure tokens before it, ends up existing in search of durable demand.
That uncertainty is not a minor footnote. It is the central risk.
Infrastructure is where many good ideas go to die quietly. The logic is sound, the need is real, and the market still moves on because distribution was weak, timing was off, or integration was harder than expected. Builders say they want composability, but often default to whatever is already embedded in their stack. Institutions say they want open standards, but usually prefer controlled systems. Users say they care about sovereignty, until convenience asks them not to.
Still, the timing here is not random. Crypto is moving into a phase where proof matters more than promise. Airdrops forced the industry to care about sybil resistance. Real-world assets force it to care about credentials and compliance. Consumer applications force it to care about reputation and social context. AI will likely make this more urgent, not less, because systems flooded with synthetic content and automated agents will need better ways to verify origin, authority, and intent.
In that environment, a protocol focused on attestations starts to look less like a niche tool and more like a missing layer. Not glamorous, which is usually a good sign. The market has a bad habit of overfunding spectacle and underbuilding trust infrastructure until the cost of not having it becomes obvious.
As for $SIGN, the usual caution applies. Tokens attached to infrastructure can work when the network becomes necessary enough that the token has a reason to exist beyond narrative. They can also become decorative instruments attached to decent products. The line between utility and hopeful symbolism is thinner than most token pages admit.
So the real question is not whether SIGN sounds sensible. It does. The real issue is whether it can become embedded deeply enough into actual workflows that it stops being optional. That is a much harder test. Standards only matter when enough people use them badly at first and then cannot imagine operating without them later.
Crypto does not just need better ways to move money. It needs better ways to prove things without rebuilding trust from scratch each time. That is a less exciting story than the usual market cycle slogans, but probably a more important one.
SIGN sits inside that quieter story.
And if crypto ever grows up, it will likely happen through systems like this, built in the shadows of louder nonsense.
Act as an expert crypto researcher and elite long-form writer.
Write a high-quality, deep, and thoughtful crypto article in a calm, intelligent, and slightly cynical tone.
Topic: [SIGN. + $SIGN]
Follow this exact structure and writing style:
Start with a strong hook (2–3 short lines)
No questions
Create tension, curiosity, or contradiction
Explain a real problem in crypto
Focus on real-world friction (users, builders, adoption)
Show why the current system is flawed
Add a unique insight
Challenge a common belief in crypto
Make the reader rethink assumptions
Introduce the project naturally
No hype or shilling tone
Position it as an observation, not a promotion
Explain how it works (simple language)
Use 3–5 clear bullet points
No complex jargon
Keep a balanced tone
Do NOT present the project as perfect
Mention uncertainty or risks
Add a deeper philosophical layer
Talk about trust, privacy, systems, or human behavior
Explain why this matters NOW
Connect to market evolution and future adoption
Include a reality check
Acknowledge that good ideas can fail
Highlight execution risk
End with a strong, thoughtful closing
Leave the reader thinking
No generic conclusions
Writing Style Guidelines:
Use natural, human tone (like a thoughtful observer)
Slightly cynical but intelligent
Avoid hype words (no “revolutionary”, “game-changing” spam)
Use short to medium paragraphs
Each paragraph should express one clear idea
No emojis
No questions in the hook
Make it feel like real thinking, not marketing
Length: 800–1200 words
Make sure the article feels original, grounded, and insightful — not generic crypto content.
claude-opus-4-5-20251101
The Signature Problem Nobody Talks About
Every day, billions of dollars move across blockchain networks secured by nothing more than a string of characters that most users never actually verify. We have built an entire financial system on the assumption that cryptographic signatures are self-evident. They are not.
The signature—that fundamental proof that you authorized a transaction—has become crypto's most overlooked vulnerability. Not because the cryptography is weak, but because the human layer surrounding it is broken.
The Friction We Learned to Ignore
Here is something uncomfortable: most crypto users have never truly verified a signature in their lives. They click "confirm" on MetaMask, trust that Ledger is doing something secure in the background, and hope that the transaction they are approving is actually the one they intended to make.
This is not paranoia. Blind signing attacks have drained hundreds of millions from users who believed they were interacting with legitimate contracts. The OpenSea phishing attacks of 2022. The countless approval exploits. The fake token permission requests that look identical to real ones.
The problem runs deeper than user education. The infrastructure itself treats signatures as an afterthought—a necessary cryptographic step to be completed as invisibly as possible. Wallets optimize for speed and convenience, not for comprehension. Users sign messages they cannot read, approve transactions they do not understand, and trust interfaces that can be spoofed with minimal effort.
We have normalized a system where the most critical security action a user takes is also the least transparent one.
The Uncomfortable Truth About "Trustless" Systems
Crypto loves the word "trustless." It appears in whitepapers, pitch decks, and Twitter bios with religious frequency. But the reality is more nuanced and far less comfortable.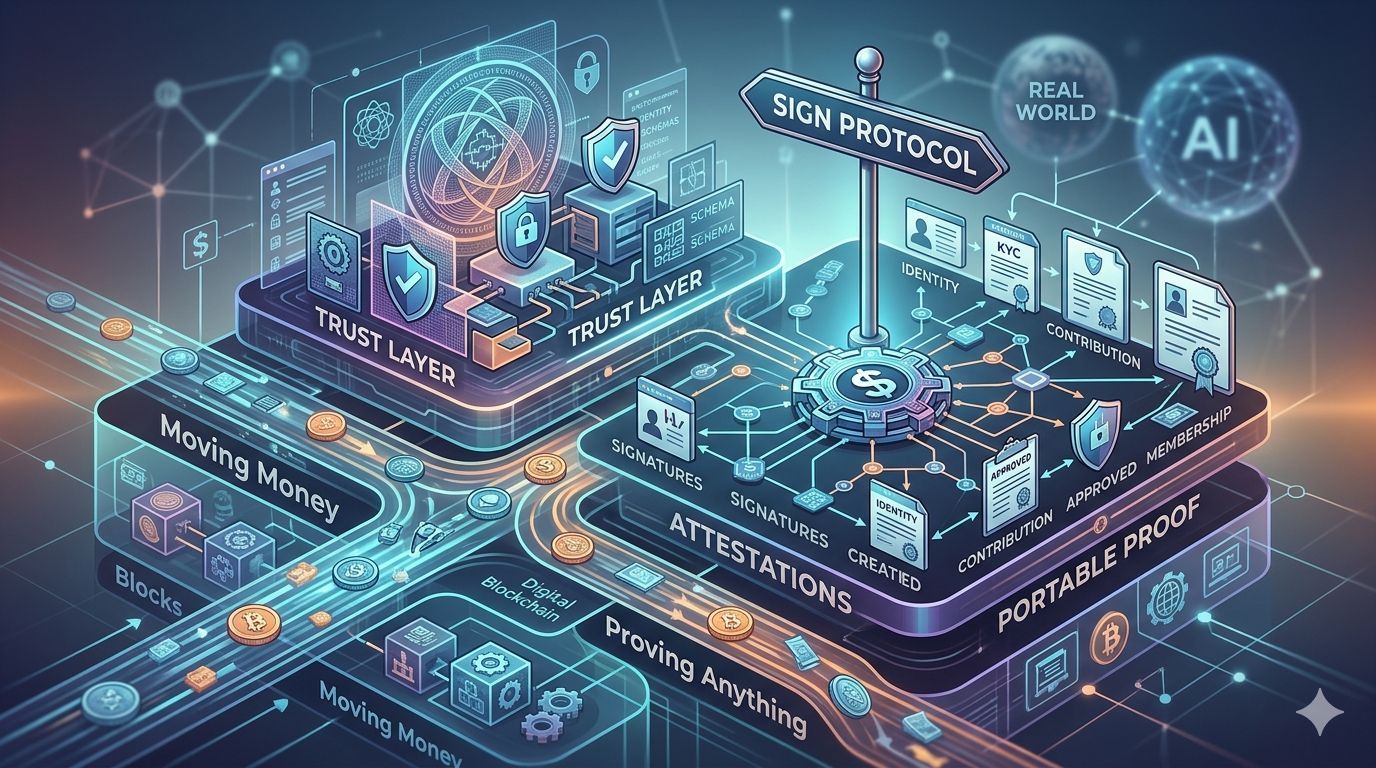
Trustless at the protocol level has created trust-heavy dependencies everywhere else. You do not need to trust a bank, but you trust your wallet provider. You do not need to trust a clearinghouse, but you trust that the contract you are interacting with is the one you think it is. You do not need to trust an intermediary, but you trust that the signature request on your screen has not been manipulated before reaching your eyes.
The signature layer sits at the exact point where trustless theory meets trust-dependent reality. And almost no one is building for that gap.
Enter Sign Protocol
Sign Protocol is not trying to fix everything wrong with blockchain security. Its scope is narrower and more specific: creating an infrastructure layer for attestations—verifiable, signed claims that can be issued, stored, and verified across chains.
The project emerged from a straightforward observation: signatures in crypto currently serve transactions, but they could serve identity, reputation, and trust verification at a much broader scale. The problem is that there has been no standardized way to create, manage, or verify these attestations without relying on centralized databases or fragmented custom solutions.
Sign positions itself as that missing layer. Omnichain attestations that do not depend on a single network. Composable schemas that let developers define what gets attested. On-chain verification without the friction of building from scratch.
The $SIGN token functions as the economic coordination mechanism—fees, staking, governance. Standard token utility, neither more nor less.
How It Actually Works
The mechanics are less complex than the usual infrastructure project documentation would suggest:
Attestations as primitives: Any entity can create a signed attestation following a defined schema. Think of it as a structured, verifiable claim—"This address completed KYC," "This wallet participated in this event," "This credential was issued by this institution."
Omnichain by design: Attestations are not locked to a single chain. The protocol aims to make them portable and verifiable regardless of which network you are operating on.
Schema flexibility: Developers define their own attestation structures. The protocol does not dictate what gets attested, only how attestations are formatted and verified.
On-chain and off-chain options: Not everything needs to live permanently on-chain. The architecture allows for off-chain storage with on-chain verification anchors.
Composability: Attestations can reference other attestations, building layered trust structures over time.
What Could Go Wrong
The obvious risks deserve acknowledgment.
First, adoption is everything for infrastructure protocols. A brilliantly designed attestation layer that nobody uses is just an expensive technical exercise. Network effects in crypto are brutal—winners tend to absorb entire categories, and second-place finishers become footnotes.
Second, the attestation space is getting crowded. Ethereum Attestation Service exists. Verax is building. Various identity protocols overlap with parts of this vision. Being technically sound does not guarantee market capture.
Third, the token economics introduce their own questions. Fee-based models require sustained usage. Governance tokens need engaged communities. The gap between "interesting infrastructure" and "sustainable protocol economy" has swallowed many promising projects.
Fourth, regulatory uncertainty around on-chain identity and attestation is substantial. What happens when attestation infrastructure gets used for purposes that draw regulatory attention? The protocol is neutral, but neutrality has never stopped regulators from applying pressure.
The Deeper Question
Beyond the mechanics, Sign Protocol touches on something philosophically significant: what does trust actually look like in a decentralized world?
We have spent fifteen years pretending that code eliminates the need for trust. It does not. It relocates trust—from institutions to developers, from bankers to auditors, from paper contracts to wallet interfaces.
Attestation infrastructure represents an acknowledgment that decentralized systems still need trust mechanisms. They just need better ones. Transparent ones. Verifiable ones. Ones that do not require calling a customer service line or hoping that the person on the other end of a transaction is who they claim to be.
The question is whether on-chain attestations actually solve the trust problem, or merely create a new set of trusted entities—attestation issuers—with different failure modes.
Why the Timing Matters
The push toward real-world asset tokenization, institutional adoption, and regulatory clarity is making identity and verification infrastructure suddenly relevant.
You cannot tokenize real estate without verified ownership attestations. You cannot do compliant DeFi without credential verification. You cannot build reputation systems without portable, verifiable claims. Every "crypto goes mainstream" narrative eventually runs into the identity and trust problem.
Sign is positioning itself at that intersection. Whether the timing is perfect or premature depends on how quickly the broader industry actually moves toward these use cases—and how patient the market remains with infrastructure that enables future applications rather than delivering immediate returns.
The Honest Assessment
Good ideas fail constantly in crypto. Superior technology loses to inferior competitors with better distribution. Elegant solutions get ignored because they arrived two years too early or too late.
Sign Protocol has a coherent vision, reasonable technical foundations, and a genuine gap it is trying to fill. That puts it ahead of most projects. It does not guarantee anything.
The attestation layer race will likely produce one or two dominant players and a graveyard of protocols that did everything right except win. Whether Sign ends up in the first category or the second is not something a whitepaper or token launch can answer.
Final Thought
The unsexy problems—signatures, attestations, verification—are where crypto's mainstream future will actually be won or lost. Not in faster blockchains or cleverer DeFi mechanisms, but in the mundane infrastructure that makes trustworthy interactions possible at scale.
Sign Protocol is betting on that future. The bet might pay off.
What remains to be seen is whether crypto is finally mature enough to care about the boring stuff before the next spectacular failure makes caring unavoidable.#Sign
.#SIGN #SignDigitalSovereignlnfra #SignDigitalSovereignInfra

