As blockchain technology matures, the conversation is shifting from transparency alone to a more balanced model that includes privacy as a core design principle. While public ledgers offer accountability, they often expose sensitive data in ways that limit real world adoption. This tension has led to the emergence of privacy focused infrastructures, where confidentiality and verifiability coexist. Within this evolving landscape, @MidnightNetwork is positioning itself as a protocol designed to address these structural limitations.
At the center of Midnight Network’s architecture is the concept of confidential smart contracts. Unlike traditional smart contracts that execute entirely in public view, these contracts allow certain inputs and outputs to remain private while still ensuring that execution is verifiable. This approach is particularly relevant for applications involving financial data, identity, or proprietary business logic, where full transparency may not be appropriate. By enabling computation over protected data, the network expands the range of viable blockchain use cases.
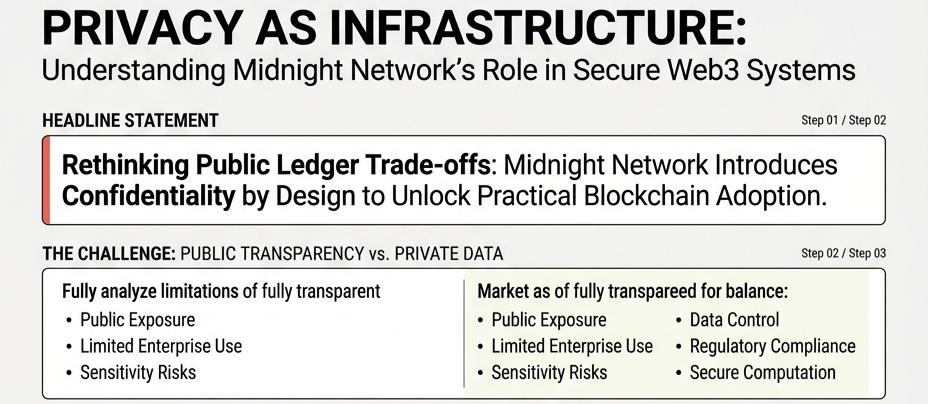
Another important component is its approach to data protection. In conventional blockchain systems, once data is published, it becomes permanently visible. Midnight Network introduces mechanisms that limit unnecessary data exposure, ensuring that sensitive information is shielded from public access while still contributing to the integrity of the network. This is achieved without compromising the trust assumptions that make distributed systems reliable.
Equally significant is the implementation of selective disclosure, which allows users and applications to reveal only the specific information required for a given interaction. Rather than sharing complete datasets, participants can provide proofs or partial views that satisfy verification requirements. This capability aligns closely with emerging regulatory expectations, where both transparency and privacy must be carefully balanced.
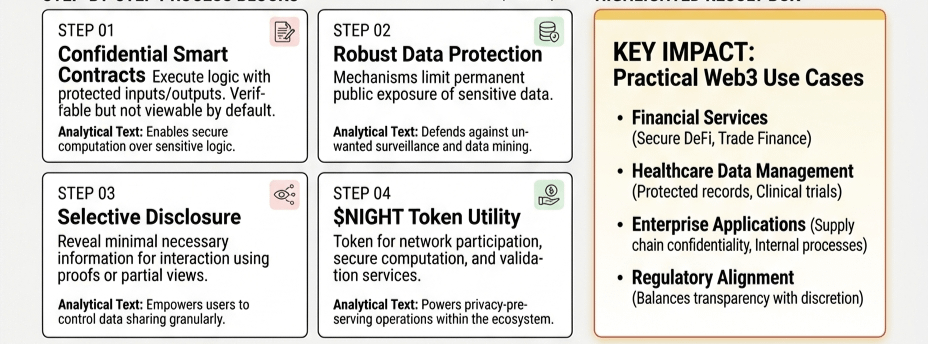
The role of $NIGHT within this ecosystem extends beyond a simple transactional token. It functions as a component of network participation, supporting operations that involve secure computation and validation. By embedding utility into privacy preserving processes, the token becomes part of a broader infrastructure that prioritizes controlled data access and secure execution.
From a practical standpoint, Midnight Network’s design opens pathways for sectors such as decentralized finance, healthcare data management, and enterprise applications areas where confidentiality is not optional but essential. The ability to handle sensitive information securely while maintaining decentralized verification could redefine how blockchain is integrated into real-world systems.
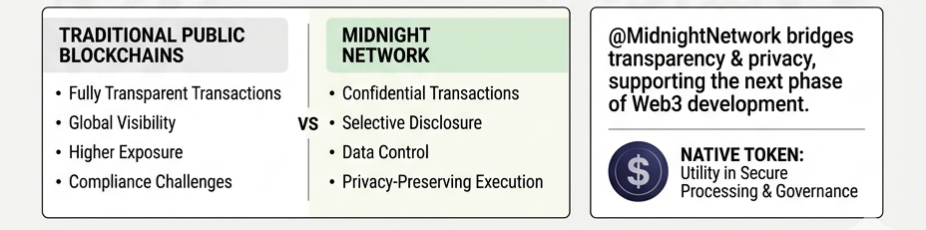
In conclusion, @MidnightNetwork reflects a growing recognition that privacy is not in opposition to transparency but rather a necessary complement to it. By advancing confidential smart contracts, robust data protection, and selective disclosure mechanisms, it contributes to a more nuanced and functional vision of Web3. As adoption progresses, infrastructure that can reconcile openness with discretion supported by frameworks like NIGHT token will likely play a defining role in the next phase of blockchain development.
@MidnightNetwork #night $NIGHT

