What keeps bothering me with Sign is how often people stop at “it verified” like that settles anything.
Sometimes that’s the problem.
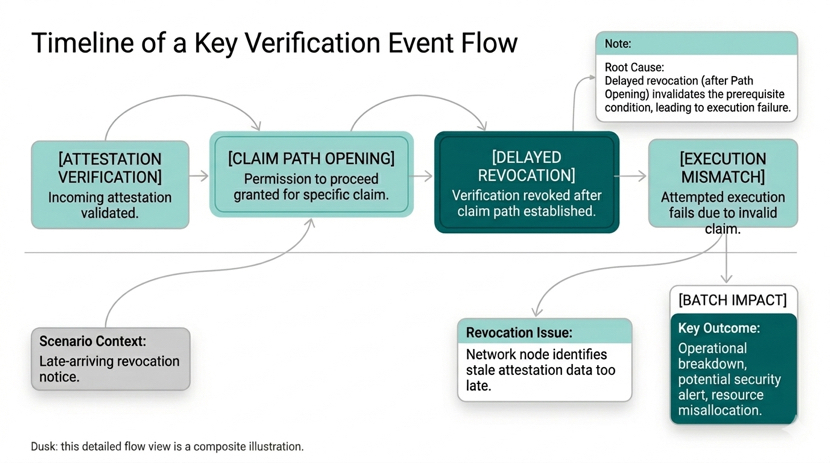
An attestation gets issued under a clean schema. The issuer has authority. Signature checks out. Status reads valid when the system queries it. SignScan has it indexed. TokenTable reads that state and opens the claim path.
Everything lines up.
That’s enough to let it move.
And then revocation lands after that.
Not fraud. Not broken credentials. Just timing.
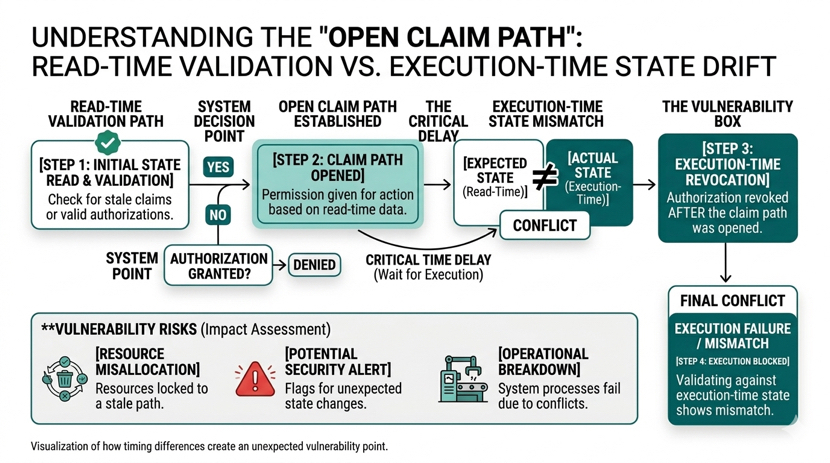
A valid attestation at read-time.
A stale eligibility state at execution-time.
That gap is small.
It’s enough.
Because the system already moved. Eligibility already flipped. The claim path is already open. And nothing in that flow forces a check strong enough to stop it once it starts.
So the protocol still looks correct.
While the outcome is already wrong.
A record can be valid when read and invalid when acted on. And once TokenTable is connected, that difference stops being technical. It becomes economic.
Money already moved.
That’s where most people get Sign wrong.
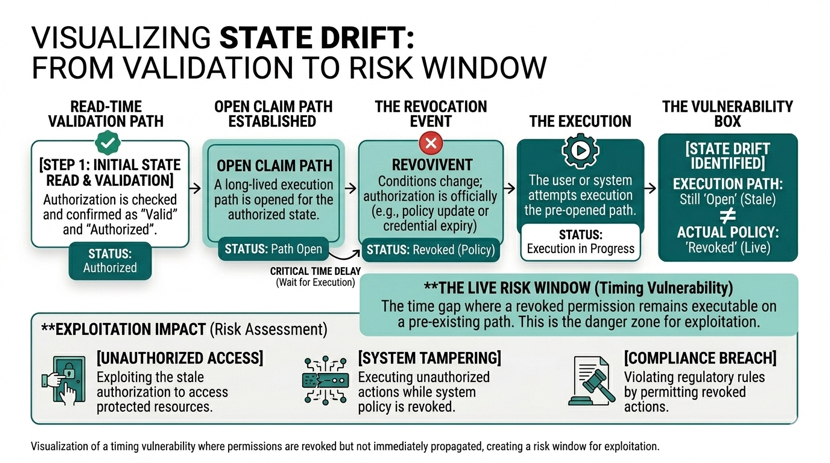
Revocation gets treated like cleanup. Something that fixes state after the fact.
It isn’t.
It’s one of the last control points that actually matters once eligibility touches distribution. And if it lands late, gets read late, or gets ignored at the wrong moment, then the system has already passed the point where it could have stopped anything.
No rollback. No hesitation. Just execution continuing on a state that no longer holds.
The primitives still look clean. Schema. Issuer. Signature. Status. Query. Done. That sequence feels tight, so teams start trusting it more than they should trust the administrative process behind it.
That’s where the compression happens.
One attested state starts carrying more consequence than it should. One check becomes “good enough” to move value.
And that’s where it breaks.
A wallet stays claimable longer than it should.
Another loses access based on a state that already changed.
Both outcomes pass through a system that technically worked.
That’s the uncomfortable part.
Verification didn’t fail.
Timing did.
And once that timing touches capital flows, especially in regions pushing toward coordinated digital infrastructure like the Middle East, being slightly late is the same as being wrong.
Because now revocation isn’t just a state update.
It’s financial control.
And if that control lands after the system already moved, then it wasn’t control at all.
Sign doesn’t pause and question that.
It executes based on what it saw.
And by the time someone asks why the claim path was still open, the only answer left is:
It verified when checked.
That just wasn’t enough.
#SignDigitalSovereignInfra $SIGN @SignOfficial
