A private transaction completes.
Moments later, another workflow shows the same pause.
The payload is secure. Proofs check out. Everything looks fine on paper.
But the rhythm isn’t quiet.
That’s the subtle version of Midnight that always catches my eye.
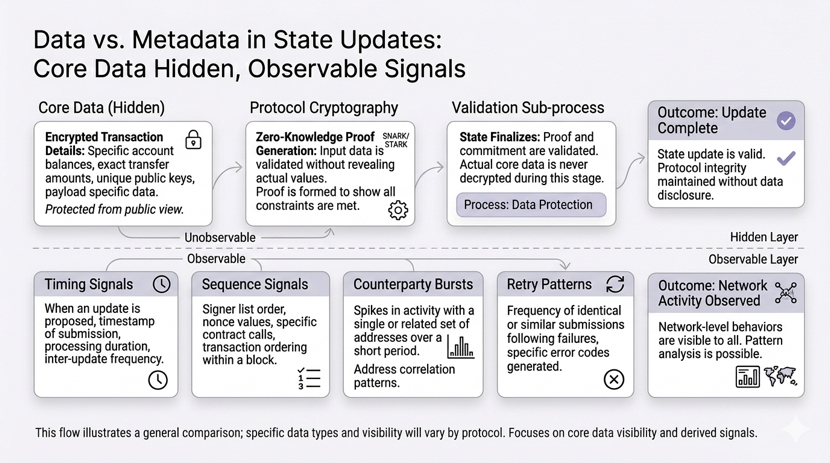
Not the polished privacy pitch. Not selective disclosure doing its neat work. The core data stays hidden, proofs verify, and technically, the system works perfectly.
The real challenge? The metadata, the traces, the tiny behavioral echoes that still leak out.
Timing. Patterns. Frequency of retries. Route choices. Counterparty bursts.
The core stays invisible. But the surrounding signals tell a story.
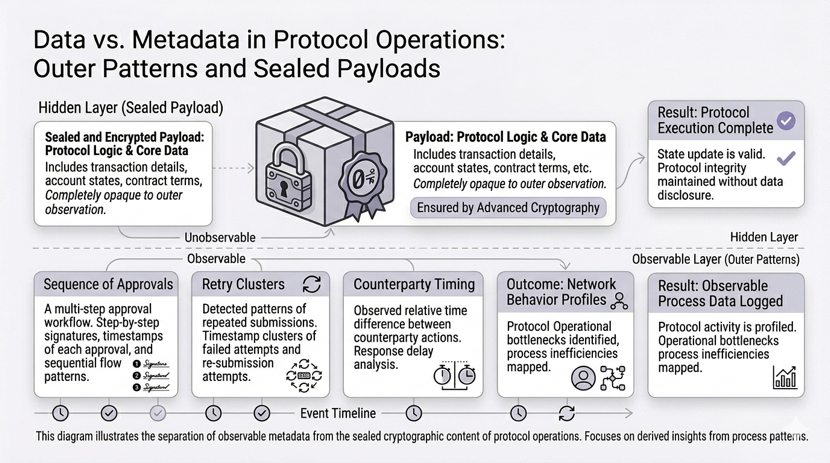
Think of a private treasury flow or internal payment system built on Midnight.
The ledger itself is sealed. Smart contract conditions execute privately. Thresholds validate without exposing every detail.
All of that works. Very Midnight. Very precise.
Now step back and look at the edges:
One approval path consistently adds a three-minute lag.
One review batch always triggers in the same sequence.
Certain counterparties light up just before the monthly reconciliation hits.
Retries cluster around the same type of event over and over.
Eventually, the hidden data isn’t needed to see the pattern.
The sequence, timing, and cadence are enough to reconstruct behavior.
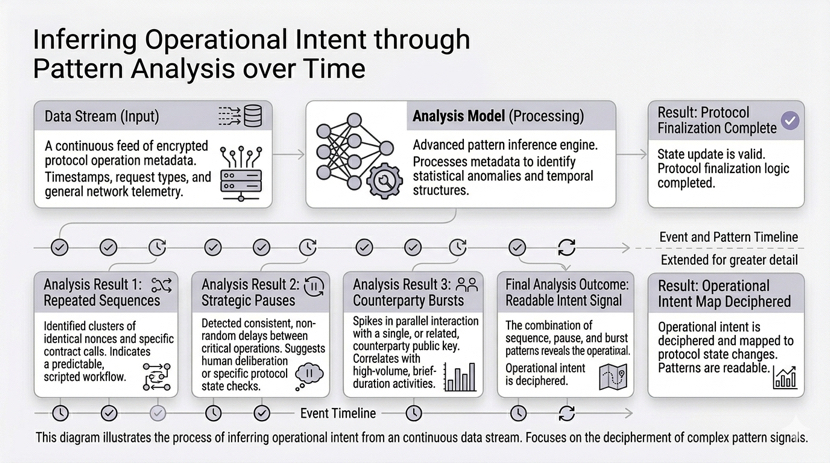
And here’s the thing: this isn’t just theoretical.
Traders notice. Analysts notice. Compliance notices. Even internal ops teams notice.
Hiding the value? Easy.
Hiding the identity? Possible.
Hiding the signal created by repetition and timing? That’s almost impossible.
The stronger the privacy in the core, the more attention people pay to the surrounding signals. The patterns become louder. And that’s where the narrative leaks.
Even a single counterparty cluster showing up at the same timestamp creates a rhythm that repeats across workflows.
Even retries that bunch around similar events tell someone patient enough what is happening under the hood.
Even the timing of approvals, the sequence of small packets, the cadence of review flows—everything becomes a hint.
It isn’t a flaw in Midnight. The proofs are solid. The data stays sealed.
But the story told by cadence, retries, sequence, and counterparty behavior doesn’t vanish.
Anyone patient enough can infer the system’s behavior without touching the private payload.
And the more adoption grows — private credit, treasury operations, identity-heavy onboarding — the more those patterns matter.
More volume creates more repetitions. More repetitions create more inferences.
Even perfectly private smart contracts can end up leaking enough to form a picture, quietly, through the metadata.
The real challenge isn’t keeping the data secret.
It’s managing what the system says about itself when nobody is watching the core directly.
The private layer works. The patterns don’t.
Even if everything technically “verifies,” someone watching the rhythm can build confidence, or doubt, without ever touching the payload.
The subtle signals end up shaping trust more than the private proof itself.
That’s the part most people ignore when they talk about privacy systems.
At scale, the metadata footprint grows. The cadence becomes a story. The pattern becomes predictable.
The private core may be perfect. The outer behavior still speaks.
And suddenly, privacy is not just a technical feature—it’s a story you can almost read without the proofs.
That’s what keeps me coming back to Midnight.
The hard problem is not hiding the data.
It’s managing the story the system tells about the data while keeping the proofs intact and the rest invisible.