@SignOfficial I keep coming back to the same conclusion on Sign Network: audits matter here, but verification matters even more. What Sign frames as S.I.G.N. is built around execution, identity, and evidence, with Sign Protocol serving as the shared layer for creating, retrieving, and verifying structured records. That framing changes how I read the project. I see a system trying to make trust inspectable. In Sign, schemas define what a claim should look like, attestations bind that claim to an issuer, and the record can be checked later instead of being accepted on faith.
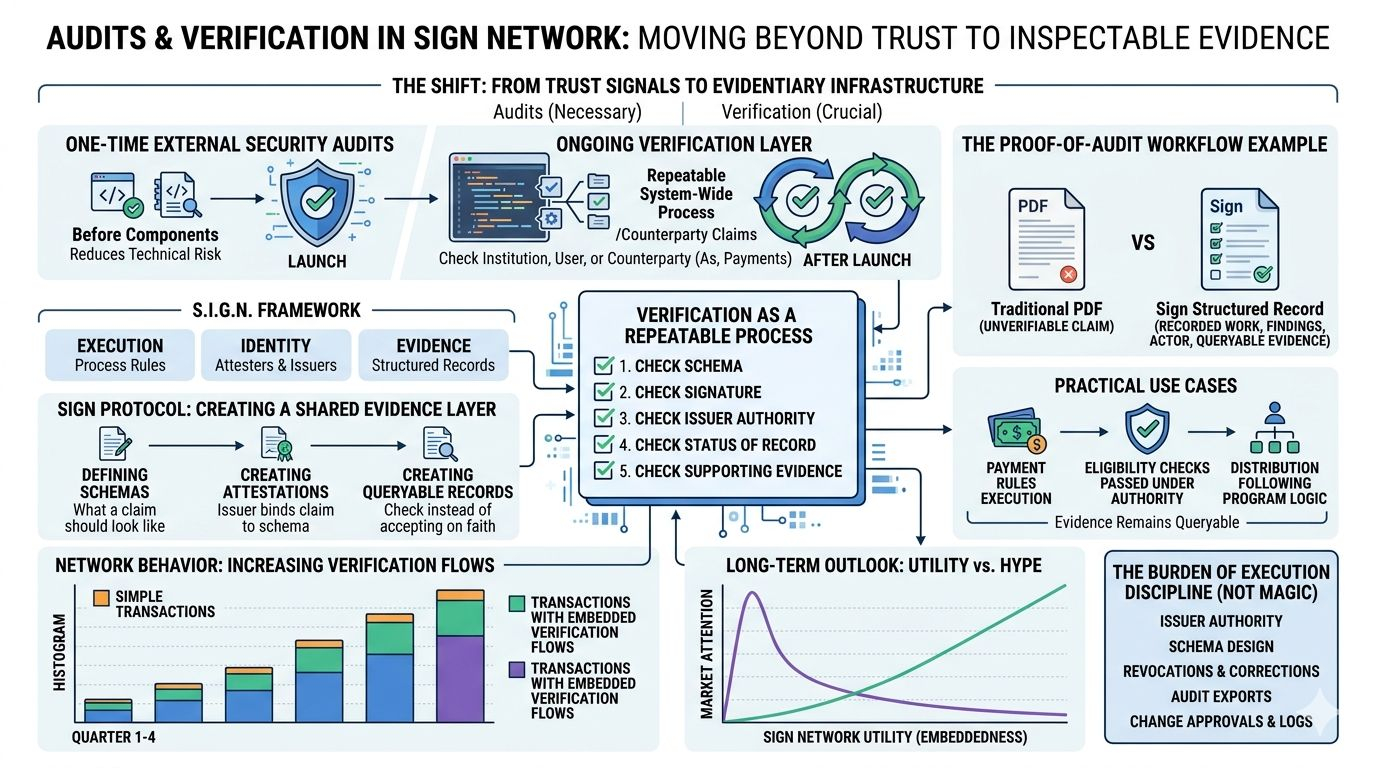
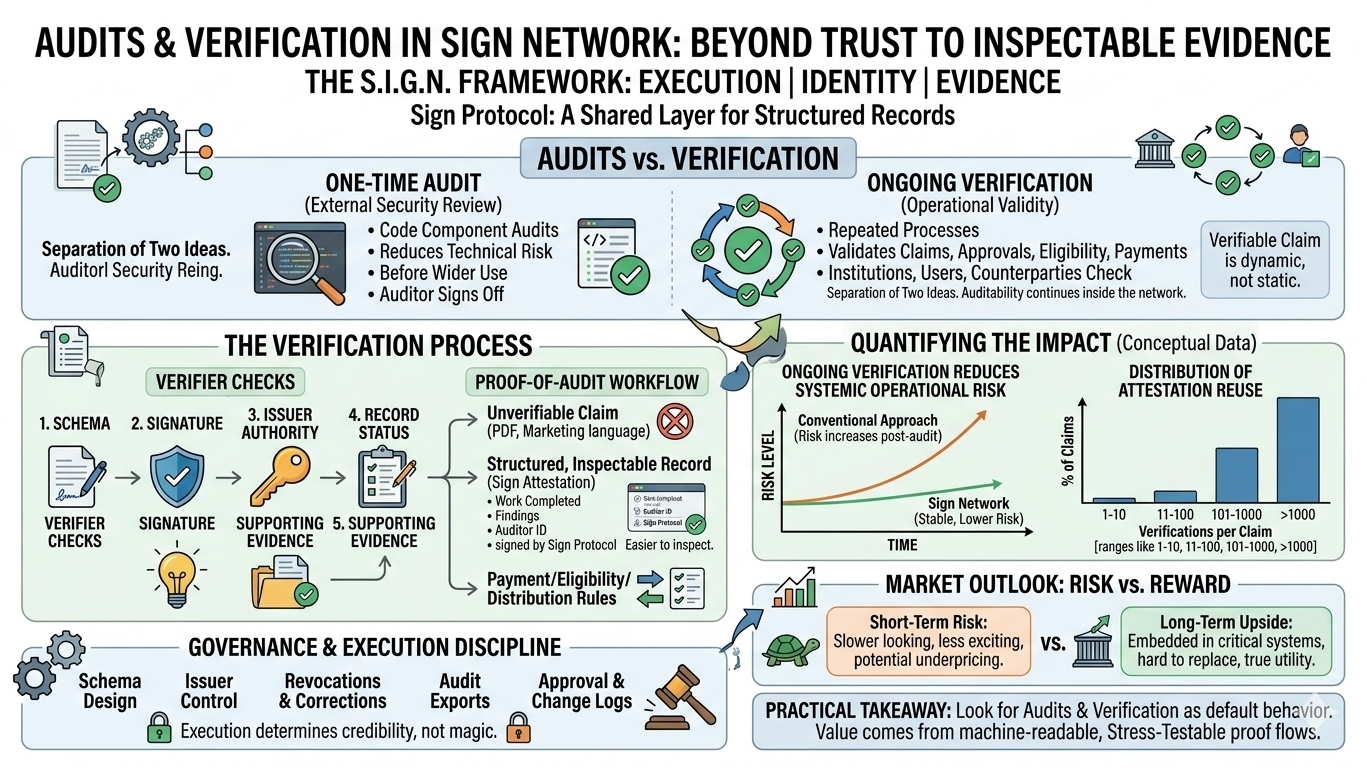
What matters is that Sign separates two ideas that many people blur together. The first is external security review, where code components are audited before wider use. The second is ongoing verification, where institutions, users, or counterparties keep checking whether a claim, approval, eligibility result, payment, or agreement is genuine and valid. That distinction is one of the strongest parts of the Sign thesis. A one-time audit can reduce technical risk, but it cannot replace a system that keeps producing evidence after launch. Sign’s materials point to audit reports and external review, but the deeper design choice is that auditability is meant to continue inside the network rather than end when an auditor signs off.
That is where I think the substance sits. Sign’s documentation describes verification as a repeatable process, not a vague trust signal. A verifier is meant to check the schema, the signature, the issuer’s authority, the status of the record, and the supporting evidence attached to it. A signed statement alone is never enough in systems that may govern money, credentials, approvals, or distribution rules. In my view, this is the part the market misses. Many people hear “attestation” and think of static proof. Sign is aiming at something broader: a reusable evidence layer where proof can be revisited and tested as conditions change.
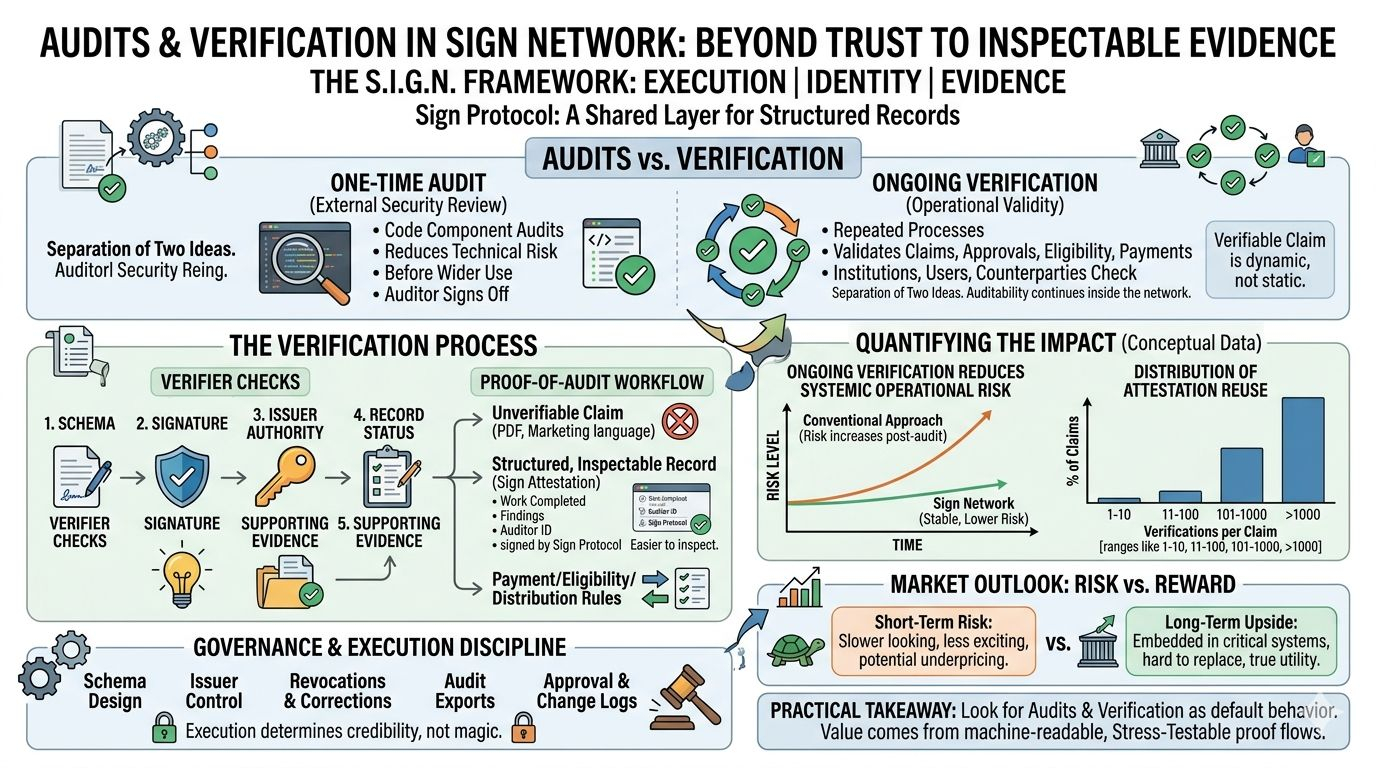
The clearest example is Sign’s proof-of-audit workflow. Instead of treating an audit as a PDF posted once and forgotten, Sign shows how a completed audit can become an attestation that records that the work happened, what the findings were, and who performed it. That matters because unverifiable audit claims are common, and a structured record is easier to inspect than marketing language. The same logic extends beyond security reviews. If a payment was executed under a ruleset, if an eligibility check passed under an authority, or if a distribution followed a version of program logic, Sign wants that evidence to remain queryable later. To me, that is where product utility begins to outweigh narrative.
I would not romanticize the model because verification is powerful but it is not magic. A signed attestation proves that a recognized issuer made a claim under a known schema; it does not automatically make a weak claim true. Sign’s governance material is clear about that. The burden sits in execution discipline: who is allowed to issue claims, how schemas are designed, how revocations and corrections are handled, how audit exports are produced, and how changes are approved and logged. Those are not minor details. They determine whether Sign becomes durable infrastructure or just elegant packaging around unreliable processes. That is why I see audits as necessary, but only verification tied to governance and evidence handling makes the model credible over time.
My practical takeaway is simple. If I were judging Sign, I would spend less time chasing attention and more time watching whether audits and verification become default behavior across the network. I would want repeated, machine-readable proof flows for completed audits, eligibility checks, approvals, and distribution records that can still be inspected under stress. The short-term risk is that verification-heavy infrastructure often looks slower and less exciting than consumer-facing products, so the market may underprice it or lose patience early. The long-term upside is clearer to me. If Sign becomes embedded in how claims are recorded, checked, and reconciled across important systems, its value will come from being hard to replace, not easy to hype. That is the sharpest way I know to understand what audits and verification really do in Sign Network.