To be honest, That gap is everywhere online.
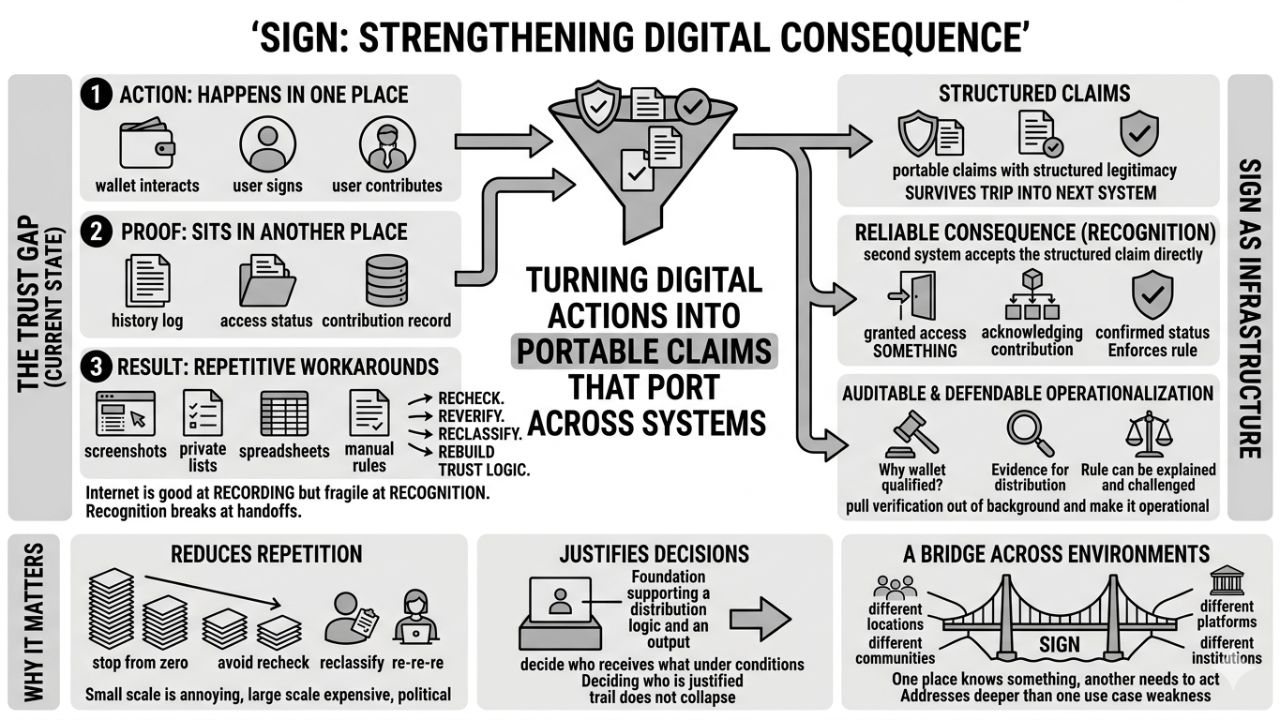
A person contributes to a network. A wallet proves some history. A user earns access somewhere. A community sets rules for who qualifies. An institution issues a credential. On paper, all of that sounds straightforward. Something happened, so the system should be able to recognize it and move forward. But that is not usually how it works. The action happens in one place, the proof sits in another, the decision gets made somewhere else, and the outcome depends on whether those pieces can be stitched together without too much confusion.
Most of the time, they cannot.
Or rather, they can, but only through workarounds. Manual review. Private lists. backend rules. exports. screenshots. spreadsheets. one-off scripts. People filling in the missing trust by hand. The internet is full of these little repair jobs. That is probably why I did not take this category seriously at first. Credential verification and token distribution sounded like one more attempt to tidy up a messy corner of the system. Useful, maybe, but not especially revealing.
Then after a while you notice that this is not a side problem.
It keeps showing up wherever digital systems try to move from record to consequence.
That is where things get interesting. Because the internet is actually very good at recording things. It can log activity forever. It can store data in absurd quantities. It can show that a wallet interacted, that a user signed, that an account exists, that an event happened. But recording is not the same as recognition. Recognition means another system can look at that fact and treat it as enough basis to do something. Grant access. distribute value. confirm status. acknowledge contribution. enforce a rule. And that second step is still much more fragile than people like to admit.
I think that is the angle from which @SignOfficial starts to make the most sense.
Not as a story about identity by itself. Not even mainly as a story about token mechanics. More as infrastructure for turning digital actions into portable claims that can survive the trip into another system. That sounds a bit abstract until you sit with it. Then it starts to feel very practical. A lot of the internet’s friction comes from the fact that actions do not travel well. They happen, but they do not carry enough structured legitimacy to matter elsewhere without being checked all over again.
You can usually tell when a system is missing a layer because people compensate with repetition.
That is what we do now. Recheck. reverify. reclassify. rebuild the same trust logic in slightly different forms depending on the platform, the chain, the institution, the campaign, the jurisdiction. A user may already have the right proof, but the receiving system still lacks a clean way to rely on it. So it starts from zero, or close to zero. At small scale, that is annoying. At larger scale, it becomes expensive, political, and difficult to defend.
Because once value gets attached, people start asking harder questions.
Why did this wallet qualify. Why was that one excluded. Who issued this credential. Why should it count here. What evidence supports the distribution. Can the rule be explained after the fact. Can it be audited. Can it be challenged. These are not edge questions. They are the actual questions that appear the moment systems stop being experimental and start carrying real consequence.
That is why token distribution, in this context, feels more serious than it first sounds. It is not just about sending assets. The sending part is often the easiest part. The real difficulty is justifying the send. Deciding who should receive what, under which conditions, with a trail that does not collapse the moment someone looks closely. That requirement pulls verification out of the background and makes it operational.
And that is probably why I keep reading SIGN as infrastructure rather than product.
Infrastructure is what people reach for when the same weakness keeps appearing across many environments. Different communities, same eligibility problem. Different platforms, same trust problem. Different institutions, same handoff problem. One place knows something. Another place needs to act on it. The bridge between those two is weaker than it should be. So a system that tries to strengthen that bridge is addressing something deeper than one use case.
Still, none of this is clean.
A verification layer is never just technical. The moment it influences who gets recognized or rewarded, it also starts shaping power. Someone defines what counts as valid proof. Someone becomes trusted to issue attestations. Someone gets excluded because their case does not fit the structure neatly enough. And if enough systems begin depending on the same rails, coordination gets easier but dependency also grows. That tension does not disappear just because the architecture is elegant.
So I do not look at $SIGN and see some final answer to online trust. That would be too neat. I see an attempt to make actions count more reliably after they happen. To reduce the amount of repeated interpretation that turns digital systems into administrative patchwork. To give proof enough structure that the next system does not have to pretend it is seeing the world for the first time.
That seems modest when written down like this.
But honestly, it touches something deep.
A lot of online systems do not fail because there is no activity. They fail because activity does not become consequence in a stable way. The record exists, but the recognition breaks. The eligibility is real, but the handoff is clumsy. The value can move, but the justification underneath it feels improvised. SIGN seems to be aimed right at that unstable middle.
And maybe that is why it stays with me.
Not because it promises to make trust simple.
Just because it starts from the fact that digital systems still struggle with a basic thing: letting what already happened carry enough weight to matter somewhere else.
#SignDigitalSovereignInfra
Άρθρο
What SIGN makes me think about most is the gap between action and recognition.
Αποποίηση ευθυνών: Περιλαμβάνει γνώμες τρίτων. Δεν είναι οικονομική συμβουλή. Ενδέχεται να περιλαμβάνει χορηγούμενο περιεχόμενο. Δείτε τους Όρους και προϋποθέσεις.
110
6.5k
Γίνετε κι εσείς μέλος των παγκοσμίων χρηστών κρυπτονομισμάτων στο Binance Square.
⚡️ Λάβετε τις πιο πρόσφατες και χρήσιμες πληροφορίες για τα κρυπτονομίσματα.
💬 Το εμπιστεύεται το μεγαλύτερο ανταλλακτήριο κρυπτονομισμάτων στον κόσμο.
👍 Ανακαλύψτε πραγματικά στοιχεία από επαληθευμένους δημιουργούς.
Διεύθυνση email/αριθμός τηλεφώνου
