Your protocol can pass every audit and still lose everything overnight.
Not from a bug in your smart contract. From a number someone fed it.
One manipulated price feed and your collateral math breaks, your liquidations misbehave, and your users eat the loss. That's the oracle problem. It's happened repeatedly and the damage is in the hundreds of millions.
Here's what's actually going on, and why it matters now more than ever.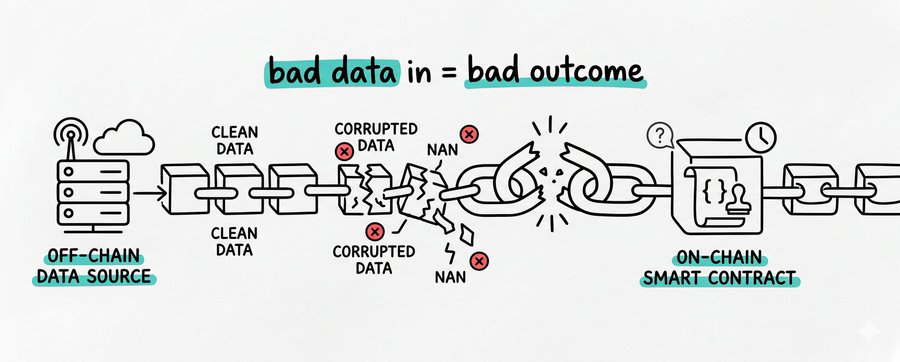
What oracles actually are
Smart contracts are closed systems by design.
They live entirely on-chain. They can't check a price on Binance. They can't call a bank to verify collateral. They can't read external data of any kind.
So you need a bridge: something that brings real-world data on-chain and hands it to the contract as truth.
That bridge is an oracle.
And here's where it gets uncomfortable. Most contracts have no way to verify whether the data they receive is accurate at the source. They can check that data arrived in an expected format. They can flag extreme deviations. But if the feed itself is corrupted upstream, those checks don't save you.
Garbage in, garbage execution.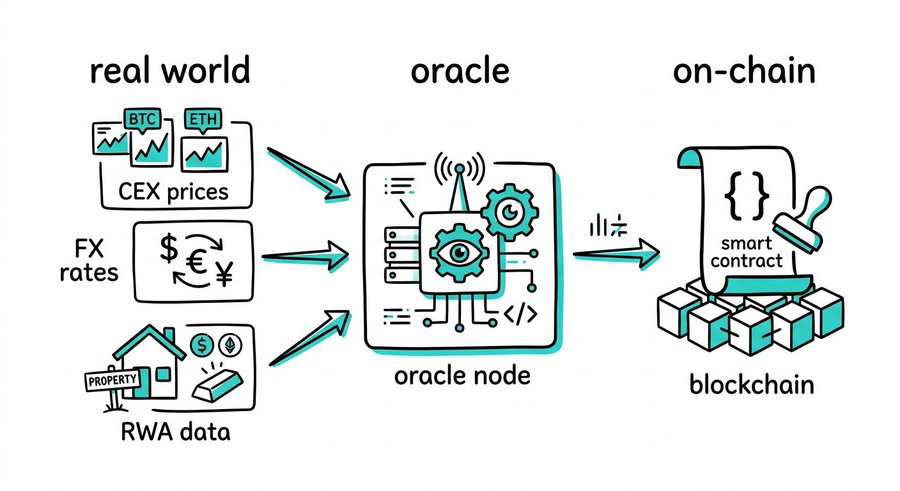
The exploit history is the thesis
The Mango Markets exploit in 2022: an attacker split $10M USDC across two accounts, manipulated the MNGO price feed through coordinated buying and selling, inflated their apparent collateral from $10M to over $400M using the distorted price, then borrowed and drained the protocol's remaining assets. $117M gone.
In 2024, price oracle manipulation ranked as the second most damaging attack vector in DeFi, accounting for $52 million in losses across 37 separate incidents, according to security research firm Three Sigma.
The April 2025 KiloEx exploit resulted in approximately $7 million in losses through the same class of vulnerability.
The smart contract code wasn't broken in any of these cases. The data feeding it was.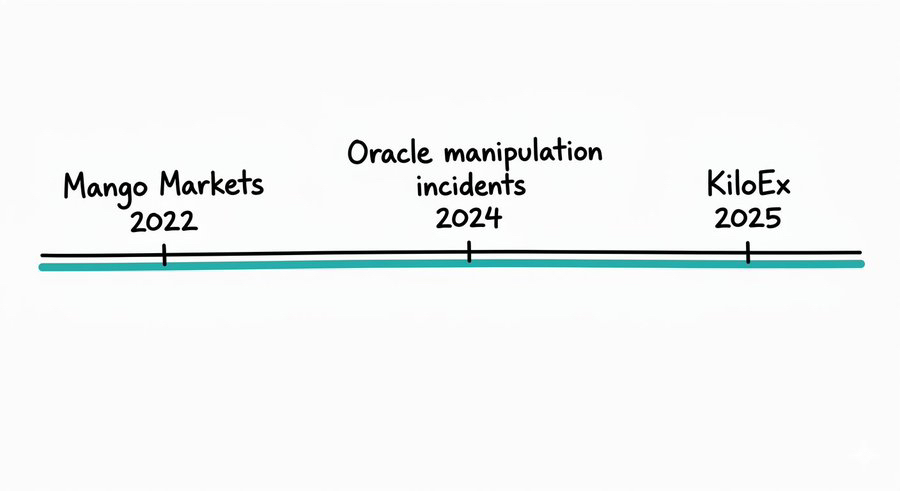
The structural problem that kept making this possible
After years of this, you'd expect every oracle to be transparent, auditable, and decentralized.
Most weren't.
Post-mortems from incidents including the ZKsync Venus Protocol attack in early 2025 and the Euler Finance ERC-4626 research published in January 2024 point to a consistent pattern: protocols taking on bad debt because oracle feeds lacked safeguards against manipulation, specifically around exchange rate oracles for yield-bearing assets where no upside cap or cross-chain verification existed.
The common thread across most oracle failures isn't exotic hacking. It's that data sourcing and aggregation happen off-chain, with limited visibility into methodology, and protocols have no way to independently verify what they're receiving or where it came from.
That's not a smart contract problem. It's an infrastructure problem.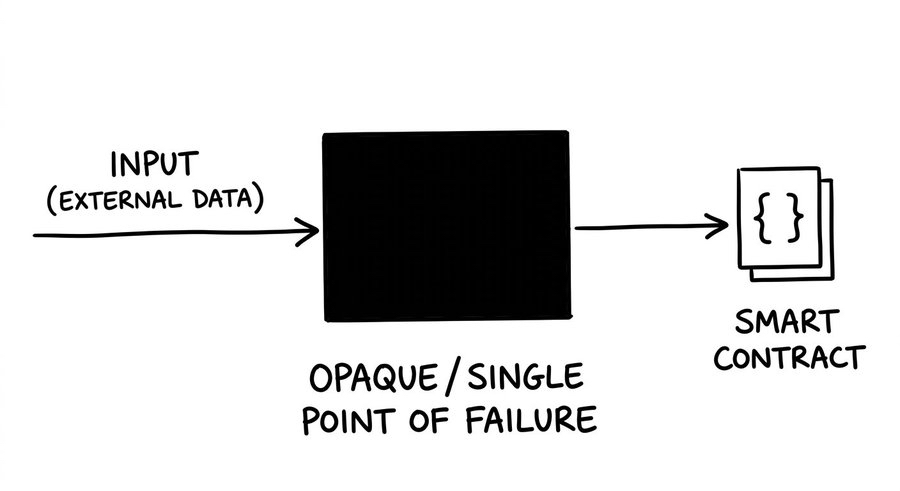
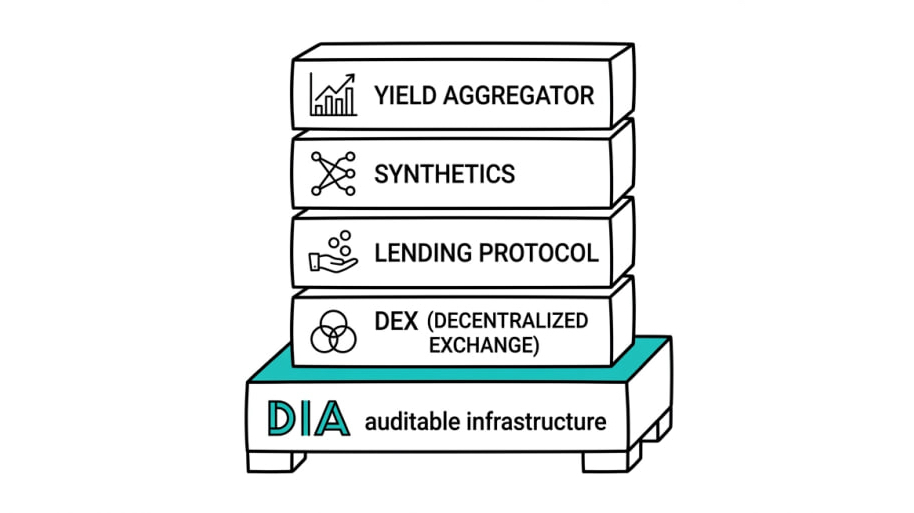
What DIA built instead
DIA's answer was to move the entire oracle pipeline on-chain.
In 2025, DIA completed the full rollout of DIA Lumina, with Lasernet (an Ethereum-based oracle rollup) as its settlement layer. The architecture works like this: independent feeder nodes collect raw trade data directly from CEXs and DEXs and compute source-level prices. That data is submitted to Lasernet, where Pods store it on-chain and Aggregators apply configurable rules to produce the final price. Every step of that process is on-chain and auditable.
What this means practically: you don't have to trust DIA's word that the data is clean. You can verify every computation yourself, trace every input back to its source, and audit the methodology without asking anyone for access.
That's a different trust model, not a marginal improvement on the existing one.
Note: Lasernet is an Ethereum rollup. Like all rollups at this stage of development, sequencer assumptions apply. DIA's decentralization claims should be read in that context, not as an absolute.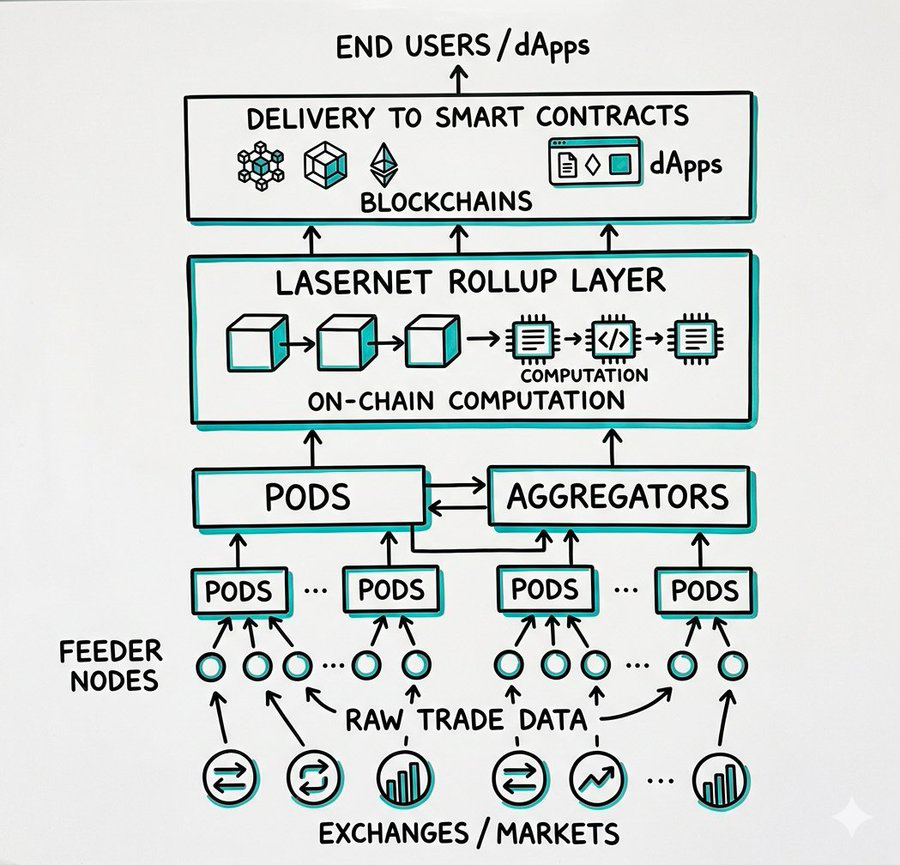
The RWA coverage question
The RWA narrative has moved past speculation. Tokenized T-bills, equities, FX rates, and commodities are live on-chain. They need pricing infrastructure that treats them differently from a memecoin.
A stock doesn't trade 24/7. A commodity has delivery contracts. An FX rate fluctuates on macroeconomic data. Generic crypto oracle methodology doesn't map cleanly onto these assets.
DIA launched xReal in 2025, a dedicated oracle suite for real-world asset applications. It delivers verifiable price feeds for over 1,000 RWAs including stocks, ETFs, FX rates, commodities, and macroeconomic data, powered by DIA Lumina's on-chain computation and auditable data sourcing.
The relevant question isn't coverage count. It's methodology. With DIA Lumina underneath xReal, the data sourcing and computation are on-chain and traceable. That matters differently for RWAs than for crypto assets because the counterparties in RWA DeFi are increasingly institutional, and they will ask.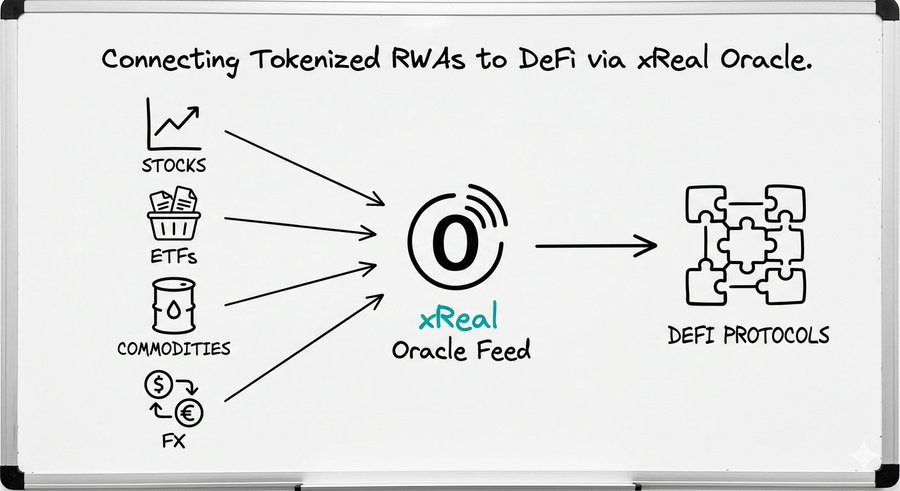
The actual coverage numbers, clearly stated
On the crypto-native side, DIA sources price data for over 3,000 digital assets from 90+ marketplaces across 45+ Layer 1 and Layer 2 blockchains. xReal adds 1,000+ real-world assets on top of that.
The more important point is customizability. As a builder you choose your data sources, your aggregation methodology, and your update triggers. You're not inheriting someone else's generic feed configured for a different asset profile.
For long-tail assets, newly launched tokens, LSTs, and niche DEX pairs, that matters considerably. A generic feed that doesn't reflect where your asset actually trades is a liability, not a service.
The ecosystem signal
In 2025, DIA ran an Oracle Grants Program across approximately 20 leading blockchains, offering up to one year of free oracle usage for builders integrating its feeds.
Free grants are a standard builder acquisition tactic; they don't by themselves prove product-market fit. What's worth watching is where the integrations landed: Ethereum L2s, Bitcoin L2s, and Polkadot ecosystems all saw increased dApp integrations with DIA through 2025 and into 2026.
Bitcoin L2 oracle demand is a specific signal. That space is building DeFi primitives largely from scratch, and the oracle layer is a foundational decision made early. Projects choosing DIA there are making a long-term infrastructure bet, not a promotional integration.
Oracles aren't where people spend their attention in crypto.
They don't generate token launch excitement, they don't trend during bull runs, and they don't get the CT spotlight until something goes wrong. Then suddenly everyone has a take.
But if you're building in DeFi or deploying capital into DeFi protocols, the oracle layer is one of the first things worth understanding. The attack surface is real, the losses are documented, and the infrastructure decisions protocols make now will determine what survives the next stress test.
DIA is building an oracle stack where the data pipeline is auditable by anyone, not just trusted from the top. Whether that becomes the standard or stays a niche approach is still an open question.
But the question matters. And not enough people are asking it.
What's your oracle due diligence checklist before depositing into a DeFi protocol?
Relevant Sources
https://www.certik.com/blog/oracle-wars-the-rise-of-price-manipulation-attacks
https://threesigma.xyz/blog/exploit/2024-defi-exploits-top-vulnerabilities
https://www.theblock.co/post/348785/analysis-of-700k-oracle-manipulation-exploit-highlights-vulnerabilities-in-defi-vaults
https://www.diadata.org/blog/post/2025-in-review-product-development/
https://www.diadata.org/docs/home
Disclosure: This article is educational and informational only. It does not constitute financial or investment advice. Always DYOR before interacting with any DeFi protocol.