Starting from a quiet assumption
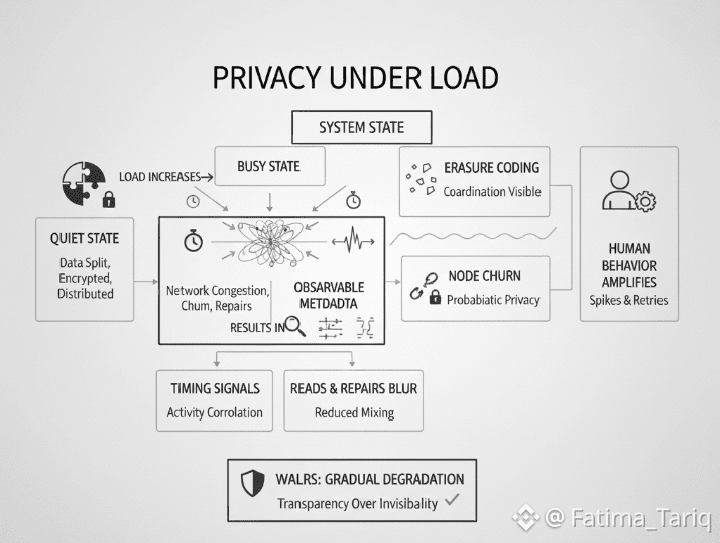
Privacy in decentralized storage is often described as a structural property. Data is split, encrypted, and distributed. No single operator sees the whole picture. In steady conditions, this framing is largely accurate. Fragmentation reduces custodial risk, and distribution limits centralized surveillance.The more difficult question is what happens when the system is busy.Load changes behavior. Networks congest, nodes churn, repairs accelerate, and users react. Under these conditions, privacy stops being an abstract guarantee and becomes an emergent property of timing, traffic patterns, and coordination. For protocols like Walrus, which rely on erasure coding and blob‑based storage, privacy under load is not about whether data remains encrypted. It is about what becomes observable when the system is forced to work harder than usual.This distinction matters because real systems spend much of their life operating under stress rather than ideal equilibrium.
Blobs, neutrality, and what the protocol cannot see
Walrus treats stored content as opaque blobs. This design avoids embedding meaning into the storage layer. The protocol does not know what a blob represents, who created it, or why it is accessed. From a privacy standpoint, this neutrality is a clear strength.However, content neutrality also limits contextual awareness. Walrus cannot distinguish between sensitive data and disposable data, or between routine access and urgent recovery. All blobs follow the same distribution, redundancy, and repair rules.When the system is lightly loaded, this uniformity simplifies reasoning about privacy. When the system is busy, it produces side effects. High‑value or frequently accessed blobs generate more reads. Reads trigger network activity. Network activity creates patterns. While the content remains hidden, the shape of demand becomes more visible.Privacy, in this context, depends not just on encryption, but on how well traffic patterns blend into background noise.
Erasure coding and the visibility of coordination
Erasure coding improves storage efficiency by breaking data into fragments and distributing them across many nodes. As long as enough fragments are available, the original blob can be reconstructed. This reduces the need for full replication and lowers storage overhead.The trade‑off is coordinationReconstruction requires fetching multiple fragments, often from different nodes. Under load, these requests become more frequent and more time‑sensitive. Repair operations add further coordination, as missing fragments must be regenerated and redistributed.Each of these steps is encrypted and permissionless, but not invisible. Observers cannot see what data is being reconstructed, but they can observe that reconstruction is happening, where traffic concentrates, and which nodes participate more frequently.As load increases, the amount of coordination required to maintain availability grows. With it, the surface area for metadata leakage expands—not through content exposure, but through activity correlation.
Churn turns privacy into a moving target
Node churn is normal in decentralized networks. Nodes go offline, rejoin, or change capacity. Walrus is designed with this reality in mind, continuously monitoring fragment availability and triggering repairs when thresholds are crossed.From a privacy perspective, churn complicates assumptions. When nodes leave unexpectedly, the system must react quickly. Repair traffic increases. Fragment redistribution becomes more urgent. These reactions are observable at the network level.Under sustained churn, certain nodes may become temporary hubs for repair coordination. They are not trusted authorities, but their elevated activity makes them more visible. Over time, repeated patterns can emerge, especially if the same nodes consistently provide higher uptime or bandwidth.Privacy here is probabilistic. No single event reveals meaningful information, but cumulative behavior under load can reduce anonymity sets.
Bandwidth contention and timing signals
Busy systems reveal themselves through delays.when user reads overlap with repair traffic, bandwidth contention emerges. Reads slow down. Clients retry. Retries increase request volume. Repair operations may be delayed, prompting further intervention.These feedback loops generate timing signals. An external observer cannot see what is being accessed, but can see when access spikes, when retries cluster, and when repairs accelerate. In aggregate, these signals can correlate with external events or application‑level usage patterns.This does not imply a privacy failure. It highlights a boundary. Walrus protects data at rest and in transit, but cannot fully mask system‑wide dynamics under load. Timing remains one of the hardest privacy problems in distributed systems.
Overlapping reads and repairs blur intent
One subtle challenge in Walrus is that reads and repairs look similar at the protocol level. Both involve fragment requests. Both consume bandwidth. Both are triggered by legitimate needs.Under light load, this overlap provides cover. Repair traffic blends into background activity. Under heavy load, the distinction matters. Reads are user‑driven and bursty. Repairs are system‑driven and persistent.As load increases, persistent repair traffic can dominate. This makes user reads more distinguishable by contrast, especially if they occur in short bursts. Privacy relies on mixing. When mixing weakens, inference becomes easier, even without access to content.This is a structural trade‑off. Improving availability under churn requires visible activity. Reducing visible activity risks data loss. Walrus prioritizes durability, accepting that privacy becomes more conditional under stress.
Human behavior amplifies metadata exposure
Technical systems do not operate in isolation. Users and operators respond to perceived performance issues in predictable ways.When reads stall, users refresh. When uploads time out, developers implement aggressive retry logic. When costs rise, operators adjust capacity. None of these actions are malicious. All of them increase variance in traffic patterns.Under load, these behaviors amplify signals. Bursty retries create identifiable spikes. Manual interventions introduce irregular timing. Operational shortcuts reduce uniformity across nodes.Walrus absorbs these behaviors without centralized control. This is a strength for decentralization, but it means privacy guarantees must account for human responses, not just protocol rules.
Decentralization slows intervention by design
In centralized systems, privacy incidents can be mitigated through rapid intervention. Traffic can be rerouted, throttled, or masked. In decentralized systems, coordination takes time.Walrus relies on protocol incentives and distributed decision‑making. This increases resistance to censorship and single‑point failure, but reduces responsiveness. Under extreme load, privacy degradation may persist longer simply because there is no authority to intervene quickly.This is not a flaw. It is a design choice. Privacy is protected structurally, not administratively. The cost is slower adaptation when conditions deviate sharply from expectations.
What Walrus gets right
Walrus does not oversell privacy. Its design acknowledges that availability, efficiency, and decentralization interact in complex ways. Encryption is treated as necessary but not sufficient. Repair is treated as a first‑class concern, not an afterthought.By avoiding application‑level assumptions, Walrus reduces the risk of policy leakage. By distributing fragments widely, it limits custodial exposure. By designing for churn, it avoids brittle privacy guarantees that collapse under real‑world conditions.These are meaningful strengths, especially when compared to systems that rely on static trust assumptions
Where limits become visible
Under sustained load, privacy in Walrus becomes conditional. Metadata exposure increases. Timing signals sharpen. Activity correlation becomes easier for sophisticated observers.These limits do not invalidate the system. They define its operating envelope. Developers building on Walrus must understand that privacy is strongest when load is well‑distributed and weakest during congestion and repair surges.Ignoring these conditions risks misaligned expectations.
A grounded conclusion
Privacy in decentralized storage is not an absolute state. It is a dynamic outcome shaped by protocol mechanics, system behavior, and human response. Walrus demonstrates how privacy can be preserved without central custody, but also how it becomes probabilistic under load.Evaluated honestly, Walrus offers credible privacy properties for blob storage, provided users and builders recognize that those properties degrade gracefully rather than catastrophically. Trust, in this context, comes from transparency about limits, not from claims of invisibility.Busy systems tell the truth about their design. Walrus tells that truth quietly, through behavior rather than promises.
